Introduction
... – Other resources like: registers, files, alarms, related processes, and other information – A process is fundamentally a container that holds information for a program to run Intro To OS, Lecture 1 By Rana Umer ...
... – Other resources like: registers, files, alarms, related processes, and other information – A process is fundamentally a container that holds information for a program to run Intro To OS, Lecture 1 By Rana Umer ...
Operating System Concepts
... mapping is that a process's threads cannot simultaneously execute on multiple processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can notify a userlevel threading library of events (e.g., a thread has blocked or ...
... mapping is that a process's threads cannot simultaneously execute on multiple processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can notify a userlevel threading library of events (e.g., a thread has blocked or ...
Helios: Heterogeneous Multiprocessing with Satellite Kernels
... and code to coordinate communication between other kernels. All other traditional operating system drivers and services (e.g., a file system) execute as individual processes. The first satellite kernel to boot, called the coordinator kernel, discovers programmable devices and launches additional sat ...
... and code to coordinate communication between other kernels. All other traditional operating system drivers and services (e.g., a file system) execute as individual processes. The first satellite kernel to boot, called the coordinator kernel, discovers programmable devices and launches additional sat ...
file (1.5 MB, ppt)
... pretty easy to add support for a new peripheral). Unix includes a basic set of commands that allow the user to view/change the system resources (filesystem, processes, peripherals, etc.). ...
... pretty easy to add support for a new peripheral). Unix includes a basic set of commands that allow the user to view/change the system resources (filesystem, processes, peripherals, etc.). ...
ppt
... To use a disk to hold files, the operating system still needs to record its own data structures on the disk ...
... To use a disk to hold files, the operating system still needs to record its own data structures on the disk ...
Chapter 10: Mass-Storage Systems
... To use a disk to hold files, the operating system still needs to record its own data structures on the disk ...
... To use a disk to hold files, the operating system still needs to record its own data structures on the disk ...
Chapter 10: Mass-Storage Structure
... To use a disk to hold files, the operating system still needs to record its own data structures on the disk ...
... To use a disk to hold files, the operating system still needs to record its own data structures on the disk ...
Week_3 Operating system File
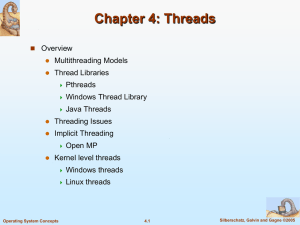
... A thread is a basic unit of CPU utilization; it comprises a thread ID, a program counter, a register set, and a stack. If a process has multiple threads of control, it can perform more than one task at a time. In certain situations, a single application may be required to perform several simil ...
... A thread is a basic unit of CPU utilization; it comprises a thread ID, a program counter, a register set, and a stack. If a process has multiple threads of control, it can perform more than one task at a time. In certain situations, a single application may be required to perform several simil ...
Midterm study guide
... One or more CPUs, device controllers connect through common bus providing access to shared memory ...
... One or more CPUs, device controllers connect through common bus providing access to shared memory ...
Virtual Ghost: Protecting Applications from Hostile Operating Systems
... Third, they require that all system call arguments must always be copied, even if the data being transferred is not security-sensitive, which is the common case in many applications. Fourth, these solutions do not provide any security benefits to the kernel itself; for example, control flow integrit ...
... Third, they require that all system call arguments must always be copied, even if the data being transferred is not security-sensitive, which is the common case in many applications. Fourth, these solutions do not provide any security benefits to the kernel itself; for example, control flow integrit ...
Threads
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the ...
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the ...
Before You Begin: Assign Information Classification
... Safe Mode – Starts Windows but only loads drivers for basic components, such as the keyboard and display. Safe Mode with Networking Support – Starts Windows identically to Safe Mode and also loads the drivers for network components. Safe Mode with Command Prompt – Starts Windows and loads the ...
... Safe Mode – Starts Windows but only loads drivers for basic components, such as the keyboard and display. Safe Mode with Networking Support – Starts Windows identically to Safe Mode and also loads the drivers for network components. Safe Mode with Command Prompt – Starts Windows and loads the ...
A Survey of Multiprocessor Operating System Kernels (DRAFT)
... times, and scalability is limited in that the shared global bus imposes limits on the maximum number of processors and memory modules it can accommodate. A NUMA architecture addresses the scalability problem by attaching local memory to each processor. Processors directly access local memory and com ...
... times, and scalability is limited in that the shared global bus imposes limits on the maximum number of processors and memory modules it can accommodate. A NUMA architecture addresses the scalability problem by attaching local memory to each processor. Processors directly access local memory and com ...
Demise of CPM
... only use "standard" IBM-compatable soft-sectored floppy disks. They had a different, incompatible flavor of floppy. At this point, most ordinary programmers would simply have changed the operating system to use the different format and sold it, but Gary Kildall had a better idea. What he did was sep ...
... only use "standard" IBM-compatable soft-sectored floppy disks. They had a different, incompatible flavor of floppy. At this point, most ordinary programmers would simply have changed the operating system to use the different format and sold it, but Gary Kildall had a better idea. What he did was sep ...
History and Demise of CPM
... only use "standard" IBM-compatable soft-sectored floppy disks. They had a different, incompatible flavor of floppy. At this point, most ordinary programmers would simply have changed the operating system to use the different format and sold it, but Gary Kildall had a better idea. What he did was sep ...
... only use "standard" IBM-compatable soft-sectored floppy disks. They had a different, incompatible flavor of floppy. At this point, most ordinary programmers would simply have changed the operating system to use the different format and sold it, but Gary Kildall had a better idea. What he did was sep ...
Chapter 10: Mass-Storage Systems
... ■ To use a disk to hold files, the operating system still needs to record its ...
... ■ To use a disk to hold files, the operating system still needs to record its ...
Synchronization Part-I - McMaster Computing and Software
... Therefore, bounded waiting is satisfied, and a process will enter its critical section after at most one entry by the other process (bounded waiting). ...
... Therefore, bounded waiting is satisfied, and a process will enter its critical section after at most one entry by the other process (bounded waiting). ...
1- intro to rts
... admit a process from "new" into "ready". It uses the loader to do this. • The CPU scheduler or short-term scheduler decides to dispatch a process from "ready" into "running". This requires a context switch (more on that later.) • The CPU scheduler also decides to remove a process from "running" to " ...
... admit a process from "new" into "ready". It uses the loader to do this. • The CPU scheduler or short-term scheduler decides to dispatch a process from "ready" into "running". This requires a context switch (more on that later.) • The CPU scheduler also decides to remove a process from "running" to " ...
Document
... • system-config-securitylevel utility – Alters /etc/sysconfig/system-config-securitylevel file – Based on firewall selections ...
... • system-config-securitylevel utility – Alters /etc/sysconfig/system-config-securitylevel file – Based on firewall selections ...
Install the Operating System
... Windows Advanced Startup Options menu, which allows you to select how to boot Windows. Safe Mode – Starts Windows but only loads drivers for basic components, such as the keyboard and display. Safe Mode with Networking Support – Starts Windows identically to Safe Mode and also loads the drivers ...
... Windows Advanced Startup Options menu, which allows you to select how to boot Windows. Safe Mode – Starts Windows but only loads drivers for basic components, such as the keyboard and display. Safe Mode with Networking Support – Starts Windows identically to Safe Mode and also loads the drivers ...
Chapter 4
... Synchronous signals: e.g. signals delivered to the same process that performed the operation causing the signal. For example, division by ...
... Synchronous signals: e.g. signals delivered to the same process that performed the operation causing the signal. For example, division by ...
slides
... Multithreading Models (cont’d) In multithreaded kernels (i.e., most current OSs), mapping from ...
... Multithreading Models (cont’d) In multithreaded kernels (i.e., most current OSs), mapping from ...