ppt
... – For each source system, record latest timestamp covered during previous extraction cycle ...
... – For each source system, record latest timestamp covered during previous extraction cycle ...
Advanced Data Structure
... • Use boolean array with 232 cells • 4GB memory already • Even O(1) checking... Too much memory required ...
... • Use boolean array with 232 cells • 4GB memory already • Even O(1) checking... Too much memory required ...
Data Structures for NLP
... Value* get_value(char* key) { int code=get_hash_code(key); Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
... Value* get_value(char* key) { int code=get_hash_code(key); Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
Text Processing in Linux A Tutorial for CSE 562/662 (NLP)
... Value* get_value(char* key) { int code=get_hash_code(key); Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
... Value* get_value(char* key) { int code=get_hash_code(key); Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
DB Support for SW - Department of Computer Engineering
... Benefits: Saving subject and predicate only once Short query time Simple structure ...
... Benefits: Saving subject and predicate only once Short query time Simple structure ...
Distributed Hash Tables: An Overview
... Exports a DHT interface Stores an object only at a node whose ID is closest to the object ID In addition to main routing table ...
... Exports a DHT interface Stores an object only at a node whose ID is closest to the object ID In addition to main routing table ...
Distributed Hash Tables
... Exports a DHT interface Stores an object only at a node whose ID is closest to the object ID In addition to main routing table ...
... Exports a DHT interface Stores an object only at a node whose ID is closest to the object ID In addition to main routing table ...
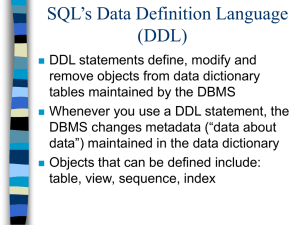
DDL : Tables
... Objects are defined using the CREATE statement Some objects can be modified using the ALTER statement Objects are removed using the DROP statement Oracle’s data dictionary views such as USER_OBJECTS, USER_TABLES, USER_CONSTRAINTS, USER_COLUMNS, USER_SEQUENCES, USER_INDEXES can be queried using SELEC ...
... Objects are defined using the CREATE statement Some objects can be modified using the ALTER statement Objects are removed using the DROP statement Oracle’s data dictionary views such as USER_OBJECTS, USER_TABLES, USER_CONSTRAINTS, USER_COLUMNS, USER_SEQUENCES, USER_INDEXES can be queried using SELEC ...
22C:21 Lecture Notes Running time of Binary Search
... that the program took to run. Instead, we mean a quantity that is a function of the input size. For example, if the input to a function foo is an array of length n, then we would like to figure out how long foo takes to complete as a function of n. We will see many examples of this throughout the se ...
... that the program took to run. Instead, we mean a quantity that is a function of the input size. For example, if the input to a function foo is an array of length n, then we would like to figure out how long foo takes to complete as a function of n. We will see many examples of this throughout the se ...
Fast and compact hash tables for integer keys
... use of a stash can greatly improve the failure probability bounds of insertion, and given knowledge of the total number of keys inserted, only a constant amount of additional space is required (Kirsch et al. 2008). Additional variants of cuckoo hashing include one that is engineered for use in hardw ...
... use of a stash can greatly improve the failure probability bounds of insertion, and given knowledge of the total number of keys inserted, only a constant amount of additional space is required (Kirsch et al. 2008). Additional variants of cuckoo hashing include one that is engineered for use in hardw ...
table
... A record in one table (a parent table) is related to one and only one record in a second table (a child table). A record in a second table (the child table) is related to one and only one record in the first table (the parent table). We create a 1:1 relationship by copying the primary key of a paren ...
... A record in one table (a parent table) is related to one and only one record in a second table (a child table). A record in a second table (the child table) is related to one and only one record in the first table (the parent table). We create a 1:1 relationship by copying the primary key of a paren ...
Lock-Free Resizeable Concurrent Tries
... the updated bitmap and the new key entry in the array, and then do a CAS in the entry within the C2 array that points to C1. The change is then done atomically. However, this approach does not work. Assume that another thread T2 decides to insert a key below the node C2 at the time when T1 is creati ...
... the updated bitmap and the new key entry in the array, and then do a CAS in the entry within the C2 array that points to C1. The change is then done atomically. However, this approach does not work. Assume that another thread T2 decides to insert a key below the node C2 at the time when T1 is creati ...
Q: What is Data Structure?
... will work ) as the hashed value or key. Radix transformation: Where the value or key is digital, the number base (or radix) can be changed resulting in a different sequence of digits. (For example, a decimal numbered key could be transformed into a hexadecimal numbered key.) High-order digits could ...
... will work ) as the hashed value or key. Radix transformation: Where the value or key is digital, the number base (or radix) can be changed resulting in a different sequence of digits. (For example, a decimal numbered key could be transformed into a hexadecimal numbered key.) High-order digits could ...
Midterm
... Number of equality tests to insert N keys into an empty linear probing hash table of size 2N . ...
... Number of equality tests to insert N keys into an empty linear probing hash table of size 2N . ...
Relational Database Design
... one customer, but each customer may place many orders, there is a many-toone relationship between orders and ...
... one customer, but each customer may place many orders, there is a many-toone relationship between orders and ...
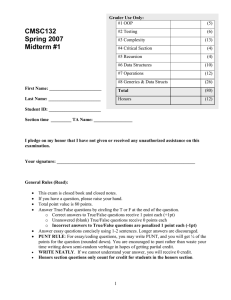
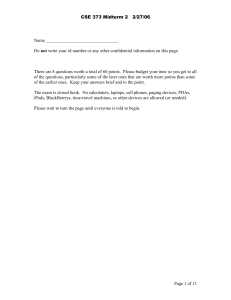
Problem 1 (20 points) General Questions about topics covered in class
... If you have a question, please raise your hand. Total point value is 80 points. Answer True/False questions by circling the T or F at the end of the question. o Correct answers to True/False questions receive 1 point each (+1pt) o Unanswered (blank) True/False questions receive 0 points each o Incor ...
... If you have a question, please raise your hand. Total point value is 80 points. Answer True/False questions by circling the T or F at the end of the question. o Correct answers to True/False questions receive 1 point each (+1pt) o Unanswered (blank) True/False questions receive 0 points each o Incor ...
Advanced Data Structures
... • Suppose we need to store values between 0 and 99, but only have an array with 10 cells • We can map the values [0,99] to [0,9] by taking modulo 10. The result is the “Hash Value” • Adding, finding and removing an element are O(1) • It is even possible to map the strings to integers, e.g. “ATE” to ...
... • Suppose we need to store values between 0 and 99, but only have an array with 10 cells • We can map the values [0,99] to [0,9] by taking modulo 10. The result is the “Hash Value” • Adding, finding and removing an element are O(1) • It is even possible to map the strings to integers, e.g. “ATE” to ...
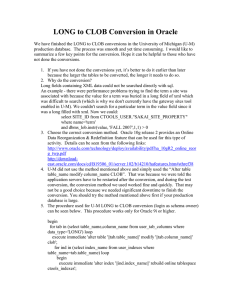
We have finished the LONG to CLOB conversions in University of
... tablesapaces). The backup will also need more spaces. 9. The conversions needed temporary space to hold the data during the conversion. During the conversion process, Oracle needs space to hold intermediate data that have been converted before all the data have been converted. 10. The operation gene ...
... tablesapaces). The backup will also need more spaces. 9. The conversions needed temporary space to hold the data during the conversion. During the conversion process, Oracle needs space to hold intermediate data that have been converted before all the data have been converted. 10. The operation gene ...
Unit-2
... • When existing software doesn't do what you want, you can write your own programs. • We are going to create a simple login system using PHP code on our pages, and a MySQL database to store our user’s information. ...
... • When existing software doesn't do what you want, you can write your own programs. • We are going to create a simple login system using PHP code on our pages, and a MySQL database to store our user’s information. ...
Mid-term exam
... Give (at least) the intermediate result after every iteration of the for-loop. (b) Explain why the worst-case time complexity of insertion sort is in O(n2 ). Exercise 3. (8 points) This exercise is concerned with singly linked lists. (a) For a singly linked list we have an operation first that gives ...
... Give (at least) the intermediate result after every iteration of the for-loop. (b) Explain why the worst-case time complexity of insertion sort is in O(n2 ). Exercise 3. (8 points) This exercise is concerned with singly linked lists. (a) For a singly linked list we have an operation first that gives ...
Organic Chemistry
... Summary: IUPAC Rules for Alkane Nomenclature 1. Find and name the longest continuous carbon chain. This is called the parent chain. 2. Number the chain consecutively, starting at the end nearest an attached group (substituent). 3. Identify and name groups attached to this chain. 4. Designate the lo ...
... Summary: IUPAC Rules for Alkane Nomenclature 1. Find and name the longest continuous carbon chain. This is called the parent chain. 2. Number the chain consecutively, starting at the end nearest an attached group (substituent). 3. Identify and name groups attached to this chain. 4. Designate the lo ...
Using Hash Based Apriori Algorithm to Reduce the Candidate 2
... Data mining is having a vital role in many of the applications like market-basket analysis, in biotechnology field etc. In data mining, frequent itemsets plays an important role which is used to identify the correlations among the fields of database. Association rules are used to identify relationsh ...
... Data mining is having a vital role in many of the applications like market-basket analysis, in biotechnology field etc. In data mining, frequent itemsets plays an important role which is used to identify the correlations among the fields of database. Association rules are used to identify relationsh ...
Name
... Assuming that variable x is initialized to point to the node labeled x in the left diagram above, write a sequence of assignment statements to perform this rotation. You do not need to write a complete method, and you do not need to worry about keeping track of the colors of the nodes. Just write a ...
... Assuming that variable x is initialized to point to the node labeled x in the left diagram above, write a sequence of assignment statements to perform this rotation. You do not need to write a complete method, and you do not need to worry about keeping track of the colors of the nodes. Just write a ...
Rainbow table
A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes. Tables are usually used in recovering a plaintext password up to a certain length consisting of a limited set of characters. It is a practical example of a space/time trade-off, using less computer processing time and more storage than a brute-force attack which calculates a hash on every attempt, but more processing time and less storage than a simple lookup table with one entry per hash. Use of a key derivation function that employs a salt makes this attack infeasible.Rainbow tables are an application of an earlier, simpler algorithm by Martin Hellman.