Advanced Networking: Network Address Translation (NAT)
... device to avoid inconsistent assignments to pieces of the same packet • End-to-end connectivity: – NAT destroys universal end-to-end reachability of hosts on the Internet – A host in the public Internet often cannot initiate communication to a host in a private network – The problem is worse, when t ...
... device to avoid inconsistent assignments to pieces of the same packet • End-to-end connectivity: – NAT destroys universal end-to-end reachability of hosts on the Internet – A host in the public Internet often cannot initiate communication to a host in a private network – The problem is worse, when t ...
NPort 6000 Series User`s Manual
... part of MOXA. MOXA provides this document “as is,” without warranty of any kind, either expressed or implied, including, but not limited to, its particular purpose. MOXA reserves the right to make improvements and/or changes to this manual, or to the products and/or the programs described in this ma ...
... part of MOXA. MOXA provides this document “as is,” without warranty of any kind, either expressed or implied, including, but not limited to, its particular purpose. MOXA reserves the right to make improvements and/or changes to this manual, or to the products and/or the programs described in this ma ...
Reference Manual for the Model RP614 Web Safe Router
... part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiate radio frequency energy and, if not installed and used in accordance with the instructions, may cause harmfu ...
... part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiate radio frequency energy and, if not installed and used in accordance with the instructions, may cause harmfu ...
Multicasting
... • If a leaf network contains no members for a given group the router connecting that network to the rest of the internet does not forward on the network • RPM is called a broadcast and prune strategy because a router broadcasts until it receives information that allows it to prune a path •Also known ...
... • If a leaf network contains no members for a given group the router connecting that network to the rest of the internet does not forward on the network • RPM is called a broadcast and prune strategy because a router broadcasts until it receives information that allows it to prune a path •Also known ...
CCENT/CCNA ICND1 100-105 Official
... always great to work with Chris, even though I’m jealous of his office setup. This book has more moving parts than most, and Chris’s part of the work happened on a challenging timeline. Thanks, Chris, for the many late-night hours working through the different elements, and especially for keeping us ...
... always great to work with Chris, even though I’m jealous of his office setup. This book has more moving parts than most, and Chris’s part of the work happened on a challenging timeline. Thanks, Chris, for the many late-night hours working through the different elements, and especially for keeping us ...
the document - Support
... This document describes the NE5000E in terms of its product positioning and features, architecture, technical specifications, supported FPICs, link features, service features, usage scenarios, and operation and maintenance. ...
... This document describes the NE5000E in terms of its product positioning and features, architecture, technical specifications, supported FPICs, link features, service features, usage scenarios, and operation and maintenance. ...
Quality of Service in mobile ad hoc networks: a
... a cost-effective and cheaper way to share information among many mobile hosts. The unique characteristics of an ad hoc network differentiate it from other classes of networks. The mobile devices are connected through wireless links that may have several effects such as fading, environmental, obstacl ...
... a cost-effective and cheaper way to share information among many mobile hosts. The unique characteristics of an ad hoc network differentiate it from other classes of networks. The mobile devices are connected through wireless links that may have several effects such as fading, environmental, obstacl ...
NAT - Hong Kong University of Science and Technology
... far as outside word is concerned: no need to be allocated range of addresses from ISP: - just one IP address is used for all devices can change addresses of devices in local network without notifying outside world can change ISP without changing addresses of devices in local network devices ...
... far as outside word is concerned: no need to be allocated range of addresses from ISP: - just one IP address is used for all devices can change addresses of devices in local network without notifying outside world can change ISP without changing addresses of devices in local network devices ...
HMC 840 Connectivity Security White Paper
... Note: For DS8000, the private LAN and the HMC(s) are inside the machine. In this setup the HMC connects through the client-provided Internet connection by the default route. When using this type of configuration on the Power HMC, the client can optionally use a second network card to physically sep ...
... Note: For DS8000, the private LAN and the HMC(s) are inside the machine. In this setup the HMC connects through the client-provided Internet connection by the default route. When using this type of configuration on the Power HMC, the client can optionally use a second network card to physically sep ...
ip-shiv2004-routing-I
... consistent while the rest may be inconsistent. Large networks => inconsistency is a scalability issue. Consistency can be achieved in two ways: Fully distributed approach: a consistency criterion or invariant across the states of adjacent nodes Signaled approach: the signaling protocol sets up ...
... consistent while the rest may be inconsistent. Large networks => inconsistency is a scalability issue. Consistency can be achieved in two ways: Fully distributed approach: a consistency criterion or invariant across the states of adjacent nodes Signaled approach: the signaling protocol sets up ...
ccna4-mod1-ScalingIPAddress
... • NAT is designed to conserve IP addresses and enable networks to use ...
... • NAT is designed to conserve IP addresses and enable networks to use ...
Resilient Overlay Networks Abstract MIT Laboratory for Computer Science
... fault-tolerance needs, do not often require such a large address block, and cannot effectively multi-home. One alternative may be “provider-based addressing,” where an organization gets addresses from multiple providers, but this requires handling two distinct sets of addresses on its hosts. It is u ...
... fault-tolerance needs, do not often require such a large address block, and cannot effectively multi-home. One alternative may be “provider-based addressing,” where an organization gets addresses from multiple providers, but this requires handling two distinct sets of addresses on its hosts. It is u ...
wireless mesh networks
... If a probing node embeds the information of nw from all its neighbors to the probe packet Then each of its neighbors can derive the packet delivery ratio from the neighbor to the probing node With the delivery ratio at both forward and reverse directions, denoted by df and dr, respectively, ET ...
... If a probing node embeds the information of nw from all its neighbors to the probe packet Then each of its neighbors can derive the packet delivery ratio from the neighbor to the probing node With the delivery ratio at both forward and reverse directions, denoted by df and dr, respectively, ET ...
here - BITS Embryo
... – Initiator executes “SendTargets” command after establishing the session • This is the only command supported for a Discovery session ...
... – Initiator executes “SendTargets” command after establishing the session • This is the only command supported for a Discovery session ...
Implementation of IPv6 ToS over ATM Network
... called “IPv6 ToS Mapping” is also added to the source. This new attribute allows the user to select the ATM service category to map IPv6’s ToS. At simulation time, depending on the user’s selection, SVC’s of the specified ATM service category will be set up before packets are generated. For example, ...
... called “IPv6 ToS Mapping” is also added to the source. This new attribute allows the user to select the ATM service category to map IPv6’s ToS. At simulation time, depending on the user’s selection, SVC’s of the specified ATM service category will be set up before packets are generated. For example, ...
Reorder Density (RD): A Formal, Comprehensive Metric for Packet Reordering
... possibly to increased congestion [4]. Approaches for mitigating the impact of out-oforder packet delivery on TCP performance include adjusting ‘dupthresh’ parameter, i.e., the number of duplicate ACKs to be allowed before classifying a following nonacknowledged packet as lost [19]. In delay sensitiv ...
... possibly to increased congestion [4]. Approaches for mitigating the impact of out-oforder packet delivery on TCP performance include adjusting ‘dupthresh’ parameter, i.e., the number of duplicate ACKs to be allowed before classifying a following nonacknowledged packet as lost [19]. In delay sensitiv ...
DSL-504T ADSL Router User’s Guide
... shall be to replace the non-conforming Software (or defective media) with software that substantially conforms to D-Link’s functional specifications for the Software or to refund at D-Link’s sole discretion. Except as otherwise agreed by D-Link in writing, the replacement Software is provided only t ...
... shall be to replace the non-conforming Software (or defective media) with software that substantially conforms to D-Link’s functional specifications for the Software or to refund at D-Link’s sole discretion. Except as otherwise agreed by D-Link in writing, the replacement Software is provided only t ...
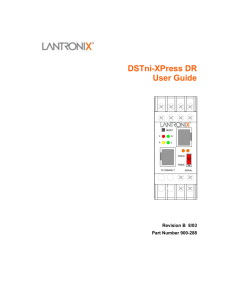
DSTni-XPress DR User Guide
... Attention: This product has been designed to comply with the limits for a Class A digital device pursuant to Part 15 of FCC Rules. These limits are designed to provide reasonable protection against such interference when operating in a commercial environment. This equipment generates, uses, and can ...
... Attention: This product has been designed to comply with the limits for a Class A digital device pursuant to Part 15 of FCC Rules. These limits are designed to provide reasonable protection against such interference when operating in a commercial environment. This equipment generates, uses, and can ...
Class Power Points Gaz on Firewalls for Chapter #10
... • NAT is designed to conserve IP addresses and enable networks to use ...
... • NAT is designed to conserve IP addresses and enable networks to use ...
ss7 structure - Home - KSU Faculty Member websites
... signaling and controlling switches and databases (intelligence) ...
... signaling and controlling switches and databases (intelligence) ...
Raven and PinPoint GPRS User Guide
... GSM network. GPRS gives packet-switched access over GSM to external data networks with high peak transfer capacity. The main objective of GPRS is to offer access to standard data networks such as TCP/IP. GPRS is a non-voice service designed specifically for transmitting data. It breaks data messages ...
... GSM network. GPRS gives packet-switched access over GSM to external data networks with high peak transfer capacity. The main objective of GPRS is to offer access to standard data networks such as TCP/IP. GPRS is a non-voice service designed specifically for transmitting data. It breaks data messages ...
Internet protocol suite

The Internet protocol suite is the computer networking model and set of communications protocols used on the Internet and similar computer networks. It is commonly known as TCP/IP, because among many protocols, the Transmission Control Protocol (TCP) and the Internet Protocol (IP) is the accepted and most widely used protocol in Internet. Often also called the Internet model, it was originally also known as the DoD model, because the development of the networking model was funded by DARPA, an agency of the United States Department of Defense.TCP/IP provides end-to-end connectivity specifying how data should be packetized, addressed, transmitted, routed and received at the destination. This functionality is organized into four abstraction layers which are used to sort all related protocols according to the scope of networking involved. From lowest to highest, the layers are the link layer, containing communication technologies for a single network segment (link); the internet layer, connecting hosts across independent networks, thus establishing internetworking; the transport layer handling host-to-host communication; and the application layer, which provides process-to-process application data exchange.The TCP/IP model and related protocol models are maintained by the Internet Engineering Task Force (IETF).