TCP/IP Network Administration - U
... Abstract Syntax Notation One (ASN.1) : 11.9. Simple Network Management Protocol access control : 12.5. Access Control levels of : 9.1.2.1. The share command services to place under, listed : 12.5.1. wrapper software for : 12.5. Access Control ACKD command, in POP : 3.4.2. Post Office Protocol Acknow ...
... Abstract Syntax Notation One (ASN.1) : 11.9. Simple Network Management Protocol access control : 12.5. Access Control levels of : 9.1.2.1. The share command services to place under, listed : 12.5.1. wrapper software for : 12.5. Access Control ACKD command, in POP : 3.4.2. Post Office Protocol Acknow ...
Implementation of IS-IS Routing Protocol for IP versions 4 and 6
... System (IS-IS) routing protocol. This thesis was done for the ICEFIN Research Laboratory at Tampere University of Technology, Institute of Communications Engineering. IS-IS was standardized by International Organization for Standardization (ISO) and was originally intended to be used with Connection ...
... System (IS-IS) routing protocol. This thesis was done for the ICEFIN Research Laboratory at Tampere University of Technology, Institute of Communications Engineering. IS-IS was standardized by International Organization for Standardization (ISO) and was originally intended to be used with Connection ...
http://www.gratisexam.com/
... MAC addresses as MAC addresses are not present until the PDU becomes a frame. QUESTION 38 You are the Cisco administrator for your company. A new branch office is opening and you are selecting the necessary hardware to support the network. There will be two groups of computers, each organized by dep ...
... MAC addresses as MAC addresses are not present until the PDU becomes a frame. QUESTION 38 You are the Cisco administrator for your company. A new branch office is opening and you are selecting the necessary hardware to support the network. There will be two groups of computers, each organized by dep ...
Scap: Stream-Oriented Network Traffic Capture and
... to reason about higher-level entities and constructs such as TCP flows, HTTP headers, SQL arguments, email messages, and so on, while traffic capture frameworks still operate at the lowest possible level: they provide the raw—possibly duplicate, out-of-order, or overlapping—and in some cases even ir ...
... to reason about higher-level entities and constructs such as TCP flows, HTTP headers, SQL arguments, email messages, and so on, while traffic capture frameworks still operate at the lowest possible level: they provide the raw—possibly duplicate, out-of-order, or overlapping—and in some cases even ir ...
MIS 5211.001 Week 5 Site:
... https://www.govtechworks.com/military-battles-to-man-itsgrowing-cyber-force/#gs.BUzyl30 http://www.ehackingnews.com/2015/09/security-bug-allowshackers-to-take.html http://krebsonsecurity.com/2013/06/the-value-of-a-hackedemail-account/ ...
... https://www.govtechworks.com/military-battles-to-man-itsgrowing-cyber-force/#gs.BUzyl30 http://www.ehackingnews.com/2015/09/security-bug-allowshackers-to-take.html http://krebsonsecurity.com/2013/06/the-value-of-a-hackedemail-account/ ...
Serial Server Installation Guide
... This equipment has been tested and found to comply with the limits for a Class A digital device pursuant to Part 15 of FCC Rules. These limits are designed to provide reasonable protection against such interference when operating in a commercial environment. This equipment generates, uses, and can r ...
... This equipment has been tested and found to comply with the limits for a Class A digital device pursuant to Part 15 of FCC Rules. These limits are designed to provide reasonable protection against such interference when operating in a commercial environment. This equipment generates, uses, and can r ...
Thwarting E-mail Spam Laundering - Computer Science
... to the anonymous characteristic of a proxy and the availability of a large number of spam proxies. The IP address of a spammer is obfuscated by a spam proxy during the protocol transformation, which hinders the tracking of real spam origins. According to Composite Blocking List (CBL) [CBL 2007], whi ...
... to the anonymous characteristic of a proxy and the availability of a large number of spam proxies. The IP address of a spammer is obfuscated by a spam proxy during the protocol transformation, which hinders the tracking of real spam origins. According to Composite Blocking List (CBL) [CBL 2007], whi ...
Netgear WGU624 Manual - FTP Directory Listing
... device intended for home and office use in EU and EFTA member states. In some EU / EFTA member states some restrictions may apply. Please contact local spectrum management authorities for further details before putting this device into operation. Marking by the above symbol indicates compliance with ...
... device intended for home and office use in EU and EFTA member states. In some EU / EFTA member states some restrictions may apply. Please contact local spectrum management authorities for further details before putting this device into operation. Marking by the above symbol indicates compliance with ...
HP MSR2000 Router Series data sheet
... VXLAN is an IP-based network, using the “MAC in UDP” package of Layer VPN technology. VXLAN can be based on an existing ISP or enterprise IP networks for decentralized physical site provides Layer 2 communication, and can provide service isolation for different tenants • Virtual Private LAN Service ...
... VXLAN is an IP-based network, using the “MAC in UDP” package of Layer VPN technology. VXLAN can be based on an existing ISP or enterprise IP networks for decentralized physical site provides Layer 2 communication, and can provide service isolation for different tenants • Virtual Private LAN Service ...
Multicast Over Wireless Networks
... Reliable Multicast in Multi-Access Wireless LANs Comparison of the three protocols: A successful RTS-CTS exchange, DBP and PBP would take longer than LBP. The buffer requirements in DBP is higher both at the base-station and receivers. A problem with DBP and PBP is the choice of right param ...
... Reliable Multicast in Multi-Access Wireless LANs Comparison of the three protocols: A successful RTS-CTS exchange, DBP and PBP would take longer than LBP. The buffer requirements in DBP is higher both at the base-station and receivers. A problem with DBP and PBP is the choice of right param ...
IPv6 and Transition Mechanisms
... – BIS (Bump in the Stack) - At the Transport Layer – BIA (Bump in the API) - At the Application Layer IPv6 Transition Mechanisms - 6DISS Workshop - 5 March 2006 ...
... – BIS (Bump in the Stack) - At the Transport Layer – BIA (Bump in the API) - At the Application Layer IPv6 Transition Mechanisms - 6DISS Workshop - 5 March 2006 ...
The OAM Jigsaw Puzzle
... The acronym "OAM" has had different meanings and has been used in different contexts. The most widely used meaning is Operations, Administration, and Maintenance, referring to detection and diagnosis of link failures in a communication network. OAM has existed for a while, dating back to traditional ...
... The acronym "OAM" has had different meanings and has been used in different contexts. The most widely used meaning is Operations, Administration, and Maintenance, referring to detection and diagnosis of link failures in a communication network. OAM has existed for a while, dating back to traditional ...
Chapter 1 - Introduction
... – describes the format of packets that are sent across the Internet – discusses the key concepts of datagram encapsulation, forwarding, and fragmentation and reassembly ...
... – describes the format of packets that are sent across the Internet – discusses the key concepts of datagram encapsulation, forwarding, and fragmentation and reassembly ...
cis185-ROUTE-lecture6-BGP-Part1
... AS 65500 would then be considered a transit AS (an ISP) Not a very undesirable situation Careful BGP configuration is required to avoid this situation. ...
... AS 65500 would then be considered a transit AS (an ISP) Not a very undesirable situation Careful BGP configuration is required to avoid this situation. ...
Compaq TCP/IP Services for OpenVMS Management
... COMPAQ, VAX, VMS, and the Compaq logo Registered in U.S. Patent and Trademark Office. OpenVMS, PATHWORKS, and Tru64 are trademarks of Compaq Information Technologies Group, L.P. in the United States and other countries. All other product names mentioned herein may be trademarks of their respective c ...
... COMPAQ, VAX, VMS, and the Compaq logo Registered in U.S. Patent and Trademark Office. OpenVMS, PATHWORKS, and Tru64 are trademarks of Compaq Information Technologies Group, L.P. in the United States and other countries. All other product names mentioned herein may be trademarks of their respective c ...
Network Working Group G. Bernstein Request for
... The CCAMP Working Group of the IETF has the goal of extending MPLS [1] protocols to support multiple network layers and new services. This extended MPLS, which was initially known as Multi-Protocol Lambda Switching, is now better referred to as Generalized MPLS (or GMPLS). The GMPLS effort is, in ef ...
... The CCAMP Working Group of the IETF has the goal of extending MPLS [1] protocols to support multiple network layers and new services. This extended MPLS, which was initially known as Multi-Protocol Lambda Switching, is now better referred to as Generalized MPLS (or GMPLS). The GMPLS effort is, in ef ...
TDMoIP : IPR
... if message destination address does not match receiver’s address message ignored (except in promiscuous mode) if message destination address matches receiver’s address message processed ...
... if message destination address does not match receiver’s address message ignored (except in promiscuous mode) if message destination address matches receiver’s address message processed ...
IPv6 (modified version)
... The prefix list includes the prefixes that have been recently learned from router advertisements. The router list includes the IPv6 addresses of all routers from which advertisements have recently been received. ...
... The prefix list includes the prefixes that have been recently learned from router advertisements. The router list includes the IPv6 addresses of all routers from which advertisements have recently been received. ...
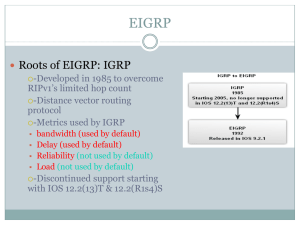
EIGRP
... information, such as a new link or a link becoming unavailable cause a routing update to occur. –EIGRP routing updates are still vectors of distances transmitted to directly connected neighbors. ...
... information, such as a new link or a link becoming unavailable cause a routing update to occur. –EIGRP routing updates are still vectors of distances transmitted to directly connected neighbors. ...
Total Access 850 System Manual
... Industry Canada Compliance Information The Industry Canada Certification label identifies certified equipment. This certification means that the equipment meets certain telecommunications network protective, operational, and safety requirements. The Department of Commerce does not guarantee the equi ...
... Industry Canada Compliance Information The Industry Canada Certification label identifies certified equipment. This certification means that the equipment meets certain telecommunications network protective, operational, and safety requirements. The Department of Commerce does not guarantee the equi ...
MSS485 Installation Guide
... terminal protocol, supported on most UNIX systems, is an easyto-use interface that creates terminal connections to any network host supporting Telnet. Rlogin is a protocol that allows users to initiate a TCP/IP login session. UDP (User Datagram Protocol) is a connectionless protocol that results in ...
... terminal protocol, supported on most UNIX systems, is an easyto-use interface that creates terminal connections to any network host supporting Telnet. Rlogin is a protocol that allows users to initiate a TCP/IP login session. UDP (User Datagram Protocol) is a connectionless protocol that results in ...
Internet protocol suite

The Internet protocol suite is the computer networking model and set of communications protocols used on the Internet and similar computer networks. It is commonly known as TCP/IP, because among many protocols, the Transmission Control Protocol (TCP) and the Internet Protocol (IP) is the accepted and most widely used protocol in Internet. Often also called the Internet model, it was originally also known as the DoD model, because the development of the networking model was funded by DARPA, an agency of the United States Department of Defense.TCP/IP provides end-to-end connectivity specifying how data should be packetized, addressed, transmitted, routed and received at the destination. This functionality is organized into four abstraction layers which are used to sort all related protocols according to the scope of networking involved. From lowest to highest, the layers are the link layer, containing communication technologies for a single network segment (link); the internet layer, connecting hosts across independent networks, thus establishing internetworking; the transport layer handling host-to-host communication; and the application layer, which provides process-to-process application data exchange.The TCP/IP model and related protocol models are maintained by the Internet Engineering Task Force (IETF).