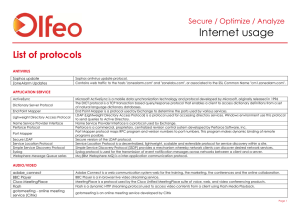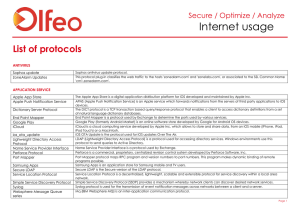
Protocols List
... The real-time transport Control protocol RTP allows monitoring of the data delivery in a manner scalable to large multicast networks, and to provide minimal control and identification functionality. RTP is the real-time transport protocol used to transmit real-time data, such as audio, video or simu ...
... The real-time transport Control protocol RTP allows monitoring of the data delivery in a manner scalable to large multicast networks, and to provide minimal control and identification functionality. RTP is the real-time transport protocol used to transmit real-time data, such as audio, video or simu ...
NOTE - Surveillance System, Security Cameras, CCTV Articles
... Configure Specific Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Planning for Your Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Example: A LAN Requiring Three Pinholes . . . . . . . . . . . . . . . . . 70 Pinhole Configuration Procedure . . . . . . ...
... Configure Specific Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Planning for Your Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Example: A LAN Requiring Three Pinholes . . . . . . . . . . . . . . . . . 70 Pinhole Configuration Procedure . . . . . . ...
Internet usage
... The real-time transport Control protocol RTP allows monitoring of the data delivery in a manner scalable to large multicast networks, and to provide minimal control and identification functionality. RTP is the real-time transport protocol used to transmit real-time data, such as audio, video or simu ...
... The real-time transport Control protocol RTP allows monitoring of the data delivery in a manner scalable to large multicast networks, and to provide minimal control and identification functionality. RTP is the real-time transport protocol used to transmit real-time data, such as audio, video or simu ...
Netopia Software User Guide V7
... Configure the IPMaps Feature . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83 FAQs for the IPMaps Feature . . . . . . . . . . . . . . . . . . . . . . . . . . . 83 What are IPMaps and how are they used? . . . . . . . . . . . . . . . . . 83 What types of servers are supported by IPMaps? ...
... Configure the IPMaps Feature . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83 FAQs for the IPMaps Feature . . . . . . . . . . . . . . . . . . . . . . . . . . . 83 What are IPMaps and how are they used? . . . . . . . . . . . . . . . . . 83 What types of servers are supported by IPMaps? ...
Reference Manual for the MR814v2 Cable/DSL Wireless Router
... Advanced Configuration of the Router Configuring for Port Forwarding to Local Servers ..........................................................6-1 Adding a Custom Service .........................................................................................6-2 Editing or Deleting a Port Forwardi ...
... Advanced Configuration of the Router Configuring for Port Forwarding to Local Servers ..........................................................6-1 Adding a Custom Service .........................................................................................6-2 Editing or Deleting a Port Forwardi ...
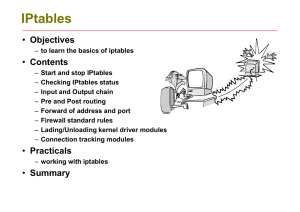
iptables-1-updated
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
Introduction to IPv6 protocol
... Anycast Addresses (RFC 3513) • «Anycast addresses allow a packet to be routed to one of a number of different nodes all responding to the same address » • «Anycast addresses are taken from the unicast address spaces (of any scope) and are not syntactically distinguishable from unicast addresses … i ...
... Anycast Addresses (RFC 3513) • «Anycast addresses allow a packet to be routed to one of a number of different nodes all responding to the same address » • «Anycast addresses are taken from the unicast address spaces (of any scope) and are not syntactically distinguishable from unicast addresses … i ...
TCPware for OpenVMS Network Control Utility
... Use is subject to license terms which appear in the file named ISC-LICENSE that should have accompanied this file when you received it. If a file named ISC-LICENSE did not accompany this file, or you are not sure the one you have is correct, you may obtain an applicable copy of the license at: http: ...
... Use is subject to license terms which appear in the file named ISC-LICENSE that should have accompanied this file when you received it. If a file named ISC-LICENSE did not accompany this file, or you are not sure the one you have is correct, you may obtain an applicable copy of the license at: http: ...
Unix System Administration
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
PHysical laYer protocol
... • Ethernet is well suited to applications where a local communication medium must carry sporadic, occasionally heavy traffic at high peak data rates. ...
... • Ethernet is well suited to applications where a local communication medium must carry sporadic, occasionally heavy traffic at high peak data rates. ...
Magnum Network Software – DX
... As to equipment proposed and furnished by GarrettCom, GarrettCom shall defend any suit or proceeding brought against purchaser so far as based on a claim that said equipment constitutes an infringement of any patent of the United States, if notified promptly in writing and given authority, informati ...
... As to equipment proposed and furnished by GarrettCom, GarrettCom shall defend any suit or proceeding brought against purchaser so far as based on a claim that said equipment constitutes an infringement of any patent of the United States, if notified promptly in writing and given authority, informati ...
HP TCP/IP Services for OpenVMS Management Command Reference
... UNIX® is a registered trademark of The Open Group. The information contained herein is subject to change without notice. The only warranties for HP products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as co ...
... UNIX® is a registered trademark of The Open Group. The information contained herein is subject to change without notice. The only warranties for HP products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as co ...
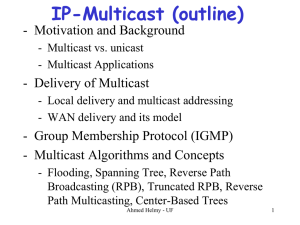
Multicast Routing
... • Advantages over RPM, in terms of scalability: – A router maintains state information for each group, not for each (source, group) pair. – Multicast packets only flow down branches leading to members (not periodically broadcast). – Only join state is kept on-tree ...
... • Advantages over RPM, in terms of scalability: – A router maintains state information for each group, not for each (source, group) pair. – Multicast packets only flow down branches leading to members (not periodically broadcast). – Only join state is kept on-tree ...
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 202-10099-01, April 2005
... NETGEAR is a trademark of Netgear, Inc. Microsoft, Windows, and Windows NT are registered trademarks of Microsoft Corporation. Other brand and product names are registered trademarks or trademarks of their respective holders. Statement of Conditions In the interest of improving internal design, oper ...
... NETGEAR is a trademark of Netgear, Inc. Microsoft, Windows, and Windows NT are registered trademarks of Microsoft Corporation. Other brand and product names are registered trademarks or trademarks of their respective holders. Statement of Conditions In the interest of improving internal design, oper ...
VoIP
... if PDU lost, still have most of every original VOIP PDU no redundancy overhead, but increases playout delay ...
... if PDU lost, still have most of every original VOIP PDU no redundancy overhead, but increases playout delay ...
Sniffer University 1-3
... Troubleshooting with the Sniffer Portable Network Analyzer Ethernet Network Analysis & Troubleshooting (10, 100, 1000 Mbps) WAN Network Analysis and Troubleshooting Sniffer Portable Switch Expert Analysis & Troubleshooting ATM Network Analysis and Troubleshooting Wireless LAN Analysis and Troublesho ...
... Troubleshooting with the Sniffer Portable Network Analyzer Ethernet Network Analysis & Troubleshooting (10, 100, 1000 Mbps) WAN Network Analysis and Troubleshooting Sniffer Portable Switch Expert Analysis & Troubleshooting ATM Network Analysis and Troubleshooting Wireless LAN Analysis and Troublesho ...
Unix System Administration
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
Overlay Network
... Overlay ID • An overlay network is uniquely identified by an overlay identifier (Overlay ID) – The overlay ID should be a globally unique identifier, e.g., IP address + timestamp: “128.143.71.29:997831668759” – No assumption on specific format of overlay ID – Uniqueness is not enforced ...
... Overlay ID • An overlay network is uniquely identified by an overlay identifier (Overlay ID) – The overlay ID should be a globally unique identifier, e.g., IP address + timestamp: “128.143.71.29:997831668759” – No assumption on specific format of overlay ID – Uniqueness is not enforced ...
2509, 2510, 2511, 2512 User Guide
... The console terminal is used to provide basic and emergency local system access. The auxiliary port is used to provide basic and emergency remote system access. The access server uses a 68-pin connector and breakout cable, which provides 8 RJ-45 ports on each cable. These ports use RJ-45-to-DB-25 ad ...
... The console terminal is used to provide basic and emergency local system access. The auxiliary port is used to provide basic and emergency remote system access. The access server uses a 68-pin connector and breakout cable, which provides 8 RJ-45 ports on each cable. These ports use RJ-45-to-DB-25 ad ...
A Comparative Study of Multicast Protocols: Top, Bottom, or In the
... referred to as service nodes) besides end hosts in order to facilitate the management of group membership and multicast delivery structures. Comparatively, these two approaches are much easier to deploy than IP multicast. On the other hand, however, they sacrifice the efficiency of multicast, since ...
... referred to as service nodes) besides end hosts in order to facilitate the management of group membership and multicast delivery structures. Comparatively, these two approaches are much easier to deploy than IP multicast. On the other hand, however, they sacrifice the efficiency of multicast, since ...
Internet protocol suite

The Internet protocol suite is the computer networking model and set of communications protocols used on the Internet and similar computer networks. It is commonly known as TCP/IP, because among many protocols, the Transmission Control Protocol (TCP) and the Internet Protocol (IP) is the accepted and most widely used protocol in Internet. Often also called the Internet model, it was originally also known as the DoD model, because the development of the networking model was funded by DARPA, an agency of the United States Department of Defense.TCP/IP provides end-to-end connectivity specifying how data should be packetized, addressed, transmitted, routed and received at the destination. This functionality is organized into four abstraction layers which are used to sort all related protocols according to the scope of networking involved. From lowest to highest, the layers are the link layer, containing communication technologies for a single network segment (link); the internet layer, connecting hosts across independent networks, thus establishing internetworking; the transport layer handling host-to-host communication; and the application layer, which provides process-to-process application data exchange.The TCP/IP model and related protocol models are maintained by the Internet Engineering Task Force (IETF).