Introduction to IPv6
... java.net, Class InetAddress. This class represents an Internet Protocol (IP) address. An IP address is either a 32-bit or 128-bit unsigned number used by IP, a lower-level protocol on which protocols like UDP and TCP are built. And subClasses: Inet4Addres, Inet6Address ...
... java.net, Class InetAddress. This class represents an Internet Protocol (IP) address. An IP address is either a 32-bit or 128-bit unsigned number used by IP, a lower-level protocol on which protocols like UDP and TCP are built. And subClasses: Inet4Addres, Inet6Address ...
What are Sockets?
... – Used for Interprocess communication. The Client-Server model – Most interprocess communication uses client-server model – Client & Server are two processes that wants to communicate with each other – The Client process connects to the Server process, to make a request for information/services own ...
... – Used for Interprocess communication. The Client-Server model – Most interprocess communication uses client-server model – Client & Server are two processes that wants to communicate with each other – The Client process connects to the Server process, to make a request for information/services own ...
Dia 1
... • A global, publicly accessible, series of interconnected computer networks (made up of hosts and clients) using the packet-switched Internet Protocol • Consists of millions of small network domains • ICANN, the Internet Corporation for Assigned Names and Numbers – Unique identifiers, domain names, ...
... • A global, publicly accessible, series of interconnected computer networks (made up of hosts and clients) using the packet-switched Internet Protocol • Consists of millions of small network domains • ICANN, the Internet Corporation for Assigned Names and Numbers – Unique identifiers, domain names, ...
6 Multi-layer Recovery Strategy in Resilient Packet
... There are few steps to recover from failure by RPR layer, which include the indication of a failure (or significant signal degradation) and the final wrapping or steering of the ring. The RPR complete recovery time is the time required by the network to return to a steady state after a failure has o ...
... There are few steps to recover from failure by RPR layer, which include the indication of a failure (or significant signal degradation) and the final wrapping or steering of the ring. The RPR complete recovery time is the time required by the network to return to a steady state after a failure has o ...
Secure and Distributed Multicast Address Allocation on IPv6 Networks M. L. Slaviero
... C.1 Creating an Unix Domain Socket with Credential Passing . . . 146 C.2 Receiving Unix Domain Message with Credential Passing . . . 147 ...
... C.1 Creating an Unix Domain Socket with Credential Passing . . . 146 C.2 Receiving Unix Domain Message with Credential Passing . . . 147 ...
Multicast Basic Concept
... Multicast Basic Concepts • Multicasting has been designed to fit into the Internet as seamlessly as possible. • Most of the work is done by routers and should be transparent to application programmers. • An application simply sends datagram packets multicast IP address. The router makes sure that t ...
... Multicast Basic Concepts • Multicasting has been designed to fit into the Internet as seamlessly as possible. • Most of the work is done by routers and should be transparent to application programmers. • An application simply sends datagram packets multicast IP address. The router makes sure that t ...
Slides
... - Look for users to connect to a high number of systems Especially useful if you isolate events into periods of time - User A connected to N number of systems in T minutes ...
... - Look for users to connect to a high number of systems Especially useful if you isolate events into periods of time - User A connected to N number of systems in T minutes ...
A Reference Implementation Architecture for Deploying a Highly
... routing protocols or applications which type of connection is used. For this paper, the z/VM Linux guests used VSWITCH and HiperSockets connections, but not direct OSA-Express connections. Our z/OS LPARs used HiperSockets and direct OSA-Express connections (but not VSWITCH, because they were not run ...
... routing protocols or applications which type of connection is used. For this paper, the z/VM Linux guests used VSWITCH and HiperSockets connections, but not direct OSA-Express connections. Our z/OS LPARs used HiperSockets and direct OSA-Express connections (but not VSWITCH, because they were not run ...
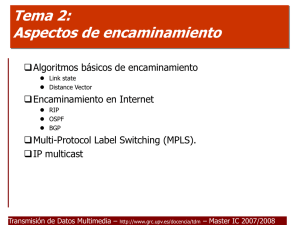
computer networks
... Each router must do the following: 1. Discover its neighbors, learn their network address. 2. Measure the delay or cost to each of its neighbors. 3. Construct a packet telling all it has just learned. 4. Send this packet to all other routers. 5. Compute the shortest path to every other router. ...
... Each router must do the following: 1. Discover its neighbors, learn their network address. 2. Measure the delay or cost to each of its neighbors. 3. Construct a packet telling all it has just learned. 4. Send this packet to all other routers. 5. Compute the shortest path to every other router. ...
TSHOOT Chapter 9 - Faculty Website Directory
... Securing the Control Plane: Overview – Cont. It is important to know which control plane security features have been implemented in the network and on which devices. Misconfiguration can cause the operation of a control plane protocol between devices to fail. Ask the following questions to he ...
... Securing the Control Plane: Overview – Cont. It is important to know which control plane security features have been implemented in the network and on which devices. Misconfiguration can cause the operation of a control plane protocol between devices to fail. Ask the following questions to he ...
Sample Title Slide Standard Template
... – A network’s security controls may not be ready for IPv6 • Or may not be configured properly (e.g. not applying a firewall rule to IPv6 as well as IPv4) ...
... – A network’s security controls may not be ready for IPv6 • Or may not be configured properly (e.g. not applying a firewall rule to IPv6 as well as IPv4) ...
Wireless Access Point Router with 4-Port Switch
... over Ethernet” or PPPoE. PPPoE is similar to a dial-up connection but does not have a phone number to dial into, and PPPoE is a dedicated high-speed connection. PPPoE also will provide the Router with a dynamic IP address to establish a connection to the Internet. DHCP (Dynamic Host Configuration Pr ...
... over Ethernet” or PPPoE. PPPoE is similar to a dial-up connection but does not have a phone number to dial into, and PPPoE is a dedicated high-speed connection. PPPoE also will provide the Router with a dynamic IP address to establish a connection to the Internet. DHCP (Dynamic Host Configuration Pr ...
ppt
... • IP anycast is simple reuse of existing protocols – Multiple instances of a service share same IP address – Each instance announces IP address / prefix in BGP / IGP – Routing infrastructure directs packets to nearest instance of the service • Can use same selection criteria as installing routes in ...
... • IP anycast is simple reuse of existing protocols – Multiple instances of a service share same IP address – Each instance announces IP address / prefix in BGP / IGP – Routing infrastructure directs packets to nearest instance of the service • Can use same selection criteria as installing routes in ...
Brocade VDX 6940 Switch data sheet
... securely, and in a scalable manner on a pertenant basis. Traditional VLANs can be used for this purpose up to a point, but limitations on VLAN ID scale and the complexity of configuring large numbers of VLANs restrict their usefulness in larger data centers. The VCS Virtual Fabric feature of Brocade ...
... securely, and in a scalable manner on a pertenant basis. Traditional VLANs can be used for this purpose up to a point, but limitations on VLAN ID scale and the complexity of configuring large numbers of VLANs restrict their usefulness in larger data centers. The VCS Virtual Fabric feature of Brocade ...
Reputation based Trust in Service-Oriented Network Environments by
... Our decisions are based on our estimation of how trustworthy a person is or how reliable a service is. Consequently, there has been a rise in trust systems that model human trust in a virtual or computing environment. These trust systems or trust models help to bridge the gap of human feelings and i ...
... Our decisions are based on our estimation of how trustworthy a person is or how reliable a service is. Consequently, there has been a rise in trust systems that model human trust in a virtual or computing environment. These trust systems or trust models help to bridge the gap of human feelings and i ...
Host-to-host congestion control for TCP
... proposed solutions focus on a variety of problems, starting with the basic problem of eliminating the phenomenon of congestion collapse, and also include the problems of effectively using the available network resources in different types of environments (wired, wireless, high-speed, long-delay, etc ...
... proposed solutions focus on a variety of problems, starting with the basic problem of eliminating the phenomenon of congestion collapse, and also include the problems of effectively using the available network resources in different types of environments (wired, wireless, high-speed, long-delay, etc ...
CN 2015 1-2 - DSpace
... It is used in WANs to interconnect LANs and for mission critical networks like those used by banks and ...
... It is used in WANs to interconnect LANs and for mission critical networks like those used by banks and ...
Alcatel-Lucent Interior Routing Protocols and High
... Alcatel-Lucent Interior Routing Protocols and High Availability ...
... Alcatel-Lucent Interior Routing Protocols and High Availability ...
NETGEAR Wireless Router Setup Manual
... DHCP Configuration of TCP/IP in Windows XP, 2000, or NT4 ............................. C-10 DHCP Configuration of TCP/IP in Windows XP ................................................... C-10 DHCP Configuration of TCP/IP in Windows 2000 ................................................ C-12 DHCP Conf ...
... DHCP Configuration of TCP/IP in Windows XP, 2000, or NT4 ............................. C-10 DHCP Configuration of TCP/IP in Windows XP ................................................... C-10 DHCP Configuration of TCP/IP in Windows 2000 ................................................ C-12 DHCP Conf ...
Alcatel-Lucent Interior Routing Protocols and High
... Alcatel-Lucent Interior Routing Protocols and High Availability ...
... Alcatel-Lucent Interior Routing Protocols and High Availability ...
EPL-Router sorgt für Transparenz und Durchgängigkeit
... Ethernet-Powerlink-segment. The second port is the interface to an IPnetwork, the so-called generic or legacy Ethernet. On the Ethernet Powerlinkside the Ethernet Powerlink-Router acts like any other Ethernet Powerlinkparticipant and has the communication profile for a Controlled Node (CN) implement ...
... Ethernet-Powerlink-segment. The second port is the interface to an IPnetwork, the so-called generic or legacy Ethernet. On the Ethernet Powerlinkside the Ethernet Powerlink-Router acts like any other Ethernet Powerlinkparticipant and has the communication profile for a Controlled Node (CN) implement ...
Tema 1: Tecnologías LAN. - GRC
... Voice & Data convergence on a single network infrastructure. Continual increase in number of users. Demand for higher connection speeds. Increase in traffic volumes. Ever-increasing number of ISP networks. ...
... Voice & Data convergence on a single network infrastructure. Continual increase in number of users. Demand for higher connection speeds. Increase in traffic volumes. Ever-increasing number of ISP networks. ...
Mobile Communications
... global, seamless operation low power for battery use no special permissions or licenses needed to use the LAN robust transmission technology simplified spontaneous cooperation at meetings easy to use for everyone, simple management protection of investment in wired networks security (no one should b ...
... global, seamless operation low power for battery use no special permissions or licenses needed to use the LAN robust transmission technology simplified spontaneous cooperation at meetings easy to use for everyone, simple management protection of investment in wired networks security (no one should b ...
Internet protocol suite

The Internet protocol suite is the computer networking model and set of communications protocols used on the Internet and similar computer networks. It is commonly known as TCP/IP, because among many protocols, the Transmission Control Protocol (TCP) and the Internet Protocol (IP) is the accepted and most widely used protocol in Internet. Often also called the Internet model, it was originally also known as the DoD model, because the development of the networking model was funded by DARPA, an agency of the United States Department of Defense.TCP/IP provides end-to-end connectivity specifying how data should be packetized, addressed, transmitted, routed and received at the destination. This functionality is organized into four abstraction layers which are used to sort all related protocols according to the scope of networking involved. From lowest to highest, the layers are the link layer, containing communication technologies for a single network segment (link); the internet layer, connecting hosts across independent networks, thus establishing internetworking; the transport layer handling host-to-host communication; and the application layer, which provides process-to-process application data exchange.The TCP/IP model and related protocol models are maintained by the Internet Engineering Task Force (IETF).