Network Working Group G. Bernstein Request for
... over heterogeneous equipment. Otherwise, the process can take days. Developing these tools for each new piece of equipment and each vendor is a significant burden on the service provider. A standardized interface for provisioning, such as GMPLS signaling, could significantly reduce or eliminate this ...
... over heterogeneous equipment. Otherwise, the process can take days. Developing these tools for each new piece of equipment and each vendor is a significant burden on the service provider. A standardized interface for provisioning, such as GMPLS signaling, could significantly reduce or eliminate this ...
ProSafe VPN Firewall 200 FVX538 Reference Manual
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
Cisco ASR 5x00 Packet Data Serving Node Administration Guide Version 15.0
... Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner ...
... Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner ...
PDF - Complete Book (2.44 MB)
... Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of t ...
... Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of t ...
trunk - Victoria College
... • Cisco created the proprietary VLAN Trunking Protocol (VTP) to solve operational problems in switched networks with VLANs – A domain may consist of several interconnected switches supporting multiple VLANs – To maintain connectivity within the VLANs, each VLAN must be manually configured on a switc ...
... • Cisco created the proprietary VLAN Trunking Protocol (VTP) to solve operational problems in switched networks with VLANs – A domain may consist of several interconnected switches supporting multiple VLANs – To maintain connectivity within the VLANs, each VLAN must be manually configured on a switc ...
Cisco Enhances per- IPSec Tunnel QoS, IOS Firewall Security for Unified
... Allows for stronger control on prefix advertisements ...
... Allows for stronger control on prefix advertisements ...
... such as client delay, server delay, network delay, transaction times, and connection status. This data can help you isolate application problems to the network or to the server. It can also help you quickly diagnose the root cause of the delay and thus resolve the problem while minimizing end-user i ...
TigerSwitch 10/100/1000 Management Guide
... The standard limited warranty can be upgraded to a Limited Lifetime* warranty by registering new products within 30 days of purchase from SMC or its Authorized Reseller. Registration can be accomplished via the enclosed product registration card or online via the SMC web site. Failure to register wi ...
... The standard limited warranty can be upgraded to a Limited Lifetime* warranty by registering new products within 30 days of purchase from SMC or its Authorized Reseller. Registration can be accomplished via the enclosed product registration card or online via the SMC web site. Failure to register wi ...
BACnet Middle East Journal
... building automation across all plant groups. In practice, however, the solutions encountered are vendor-specific islands with different communications protocols that can only be tied up to a central management system with great difficulty. These «old woes» of the sector are increasingly unaffordable ...
... building automation across all plant groups. In practice, however, the solutions encountered are vendor-specific islands with different communications protocols that can only be tied up to a central management system with great difficulty. These «old woes» of the sector are increasingly unaffordable ...
Observer - Optrics Engineering
... Network Instruments will (1) repair the product at no charge, using new or refurbished replacement parts, or (2) exchange the product with a product that is new or which has been manufactured from new or serviceable used parts and is at least functionally equivalent to the original product. A replac ...
... Network Instruments will (1) repair the product at no charge, using new or refurbished replacement parts, or (2) exchange the product with a product that is new or which has been manufactured from new or serviceable used parts and is at least functionally equivalent to the original product. A replac ...
6rd - Enabling IPv6 Customers on an IPv4
... Native dual-stack IPv4/IPv6 in the home or office Simple, stateless, automatic IPv6-in-IPv4 encap and decap functions IPv6 traffic automatically follows IPv4 Routing between CPE and BR BRs placed at IPv6 edge, addressed via anycast for load-balancing and resiliency Standardized in RFC ...
... Native dual-stack IPv4/IPv6 in the home or office Simple, stateless, automatic IPv6-in-IPv4 encap and decap functions IPv6 traffic automatically follows IPv4 Routing between CPE and BR BRs placed at IPv6 edge, addressed via anycast for load-balancing and resiliency Standardized in RFC ...
MCT+Design+Options+and+Best+Practices+Guide+for+NetIron+
... Best Practice of Multicast for MCT • The (S, G) registry is synchronized to both MCT nodes. But only one MCT node in the pair forwards the multicast traffic to clients or uplink, not both. • Double amount of data traffic flows through ICL, ICL requires more bandwidth in the deployment of multicast ...
... Best Practice of Multicast for MCT • The (S, G) registry is synchronized to both MCT nodes. But only one MCT node in the pair forwards the multicast traffic to clients or uplink, not both. • Double amount of data traffic flows through ICL, ICL requires more bandwidth in the deployment of multicast ...
Software Configuration Guide, Cisco IOS 15.2(1)GC
... Using a Mobile Ad-hoc Network (MANET) for router-to-radio communications addresses the challenges faced when merging Internet Protocol (IP) routing with mobile radio communications. The Cisco solution for MANETs provides optimal performance by providing such capabilities as route selection based on ...
... Using a Mobile Ad-hoc Network (MANET) for router-to-radio communications addresses the challenges faced when merging Internet Protocol (IP) routing with mobile radio communications. The Cisco solution for MANETs provides optimal performance by providing such capabilities as route selection based on ...
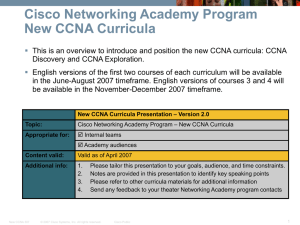
Presentation Title Size 30PT
... English versions of the first two courses of each curriculum will be available in the June-August 2007 timeframe. English versions of courses 3 and 4 will be available in the November-December 2007 timeframe. New CCNA Curricula Presentation – Version 2.0 ...
... English versions of the first two courses of each curriculum will be available in the June-August 2007 timeframe. English versions of courses 3 and 4 will be available in the November-December 2007 timeframe. New CCNA Curricula Presentation – Version 2.0 ...
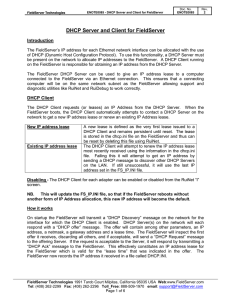
DHCP Server and Client for FieldServer
... have granted leases to clients, those clients will eventually get to a state to discover the new DHCP server(s) and will be given new leases. The leases would likely not have the same IP Addresses as the clients had from the FieldServer’s DHCP Server. The FieldServer DHCP Server gives out 5 minute I ...
... have granted leases to clients, those clients will eventually get to a state to discover the new DHCP server(s) and will be given new leases. The leases would likely not have the same IP Addresses as the clients had from the FieldServer’s DHCP Server. The FieldServer DHCP Server gives out 5 minute I ...
PDF
... configuration enables the Cisco MXE 3500 to connect to the LAN. You can then access the Cisco MXE 3500 Web UI and Windows desktop through its public IP address for additional configuration. ...
... configuration enables the Cisco MXE 3500 to connect to the LAN. You can then access the Cisco MXE 3500 Web UI and Windows desktop through its public IP address for additional configuration. ...
8 Security
... The present document has not been subject to any approval process by the 3GPP Organisational Partners and shall not be implemented. This Specification is provided for future development work within 3GPP only. The Organisational Partners accept no liability for any use of this Specification. Specific ...
... The present document has not been subject to any approval process by the 3GPP Organisational Partners and shall not be implemented. This Specification is provided for future development work within 3GPP only. The Organisational Partners accept no liability for any use of this Specification. Specific ...
TS 133 107
... print versions of the present document shall not be modified without the prior written authorization of ETSI. In case of any existing or perceived difference in contents between such versions and/or in print, the only prevailing document is the print of the Portable Document Format (PDF) version kep ...
... print versions of the present document shall not be modified without the prior written authorization of ETSI. In case of any existing or perceived difference in contents between such versions and/or in print, the only prevailing document is the print of the Portable Document Format (PDF) version kep ...
Cisco ASR 5500 System Administration Guide Version 15.0
... Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner ...
... Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner ...
Title Subtitle - Aalborg Universitet
... — one in each or single label in combined field, negotiated by LDP • Further fields in stack are encoded with ‘shim’ header in PPP/LAN format — must be at least one, with bottom label distinguished with ‘explicit NULL’ • TTL is carried in top label in stack, as a proxy for ATM header (that lacks TTL ...
... — one in each or single label in combined field, negotiated by LDP • Further fields in stack are encoded with ‘shim’ header in PPP/LAN format — must be at least one, with bottom label distinguished with ‘explicit NULL’ • TTL is carried in top label in stack, as a proxy for ATM header (that lacks TTL ...
Chapter 12 PowerPoint
... When Kerberos or public key authentication cannot be used When testing a new IPSec filter, to ensure that authentication problems are not causing the SA's failure When establishing an IPSec SA between two hosts and the association will only be between the two hosts When the preshared key is set to b ...
... When Kerberos or public key authentication cannot be used When testing a new IPSec filter, to ensure that authentication problems are not causing the SA's failure When establishing an IPSec SA between two hosts and the association will only be between the two hosts When the preshared key is set to b ...
PDF - Complete Book (655.0 KB)
... Configuration Guides, Command References, and Supplementary Resources Table 1 lists, in alphabetical order, Cisco IOS and Cisco IOS XE software configuration guides and command references, including brief descriptions of the contents of the documents. The Cisco IOS command references are comprehensi ...
... Configuration Guides, Command References, and Supplementary Resources Table 1 lists, in alphabetical order, Cisco IOS and Cisco IOS XE software configuration guides and command references, including brief descriptions of the contents of the documents. The Cisco IOS command references are comprehensi ...
Seahorse XFp Analyzer User Guide
... Safe operation of the XFp Analyzer requires that all covers be securely attached and plate tray door is closed. This also prevents heat loss and system cooling, which can affect data quality. The door opens automatically when the tray is extended, allowing the operator to insert or remove the assay ...
... Safe operation of the XFp Analyzer requires that all covers be securely attached and plate tray door is closed. This also prevents heat loss and system cooling, which can affect data quality. The door opens automatically when the tray is extended, allowing the operator to insert or remove the assay ...
BSCI Module 2 Lesson 1
... routing updates must have the same autonomous system number. Router(config-router)# network network-number [wildcard-mask] ...
... routing updates must have the same autonomous system number. Router(config-router)# network network-number [wildcard-mask] ...
Intel® Pro Wireless Display (Pro WiDi) Implementation Guide
... secure and manageable. A solution built for a home environment often lacks the security and management needed in an enterprise. The security features include enhancements that are enabled by default and can be further customized specific to an environment. Preventing bridging between an infrastructu ...
... secure and manageable. A solution built for a home environment often lacks the security and management needed in an enterprise. The security features include enhancements that are enabled by default and can be further customized specific to an environment. Preventing bridging between an infrastructu ...
Wake-on-LAN
Wake-on-LAN (WoL) is an Ethernet or Token ring computer networking standard that allows a computer to be turned on or awakened by a network message.The message is usually sent by a program executed on another computer on the same local area network. It is also possible to initiate the message from another network by using subnet directed broadcasts or a WOL gateway service. Equivalent terms include wake on WAN, remote wake-up, power on by LAN, power up by LAN, resume by LAN, resume on LAN and wake up on LAN. In case the computer being awakened is communicating via Wi-Fi, a supplementary standard called Wake on Wireless LAN (WoWLAN) must be employed.The WOL and WoWLAN standards are often supplemented by vendors to provide protocol-transparent on-demand services, for example in the Apple Bonjour wake-on-demand (Sleep Proxy) feature.