Computer Networks (CSC 345)
... email message finds its way to the receiver) • Reliability and recovery: guarantee end-to-end delivery • Traffic management: monitoring and policing the network! Regulate traffic ...
... email message finds its way to the receiver) • Reliability and recovery: guarantee end-to-end delivery • Traffic management: monitoring and policing the network! Regulate traffic ...
Chapter 9
... layers into one layer – TCP/IP appears simpler because it has fewer layers – TCP/IP transport layer using UDP does not always guarantee reliable delivery of packets as the transport layer in the OSI model does ...
... layers into one layer – TCP/IP appears simpler because it has fewer layers – TCP/IP transport layer using UDP does not always guarantee reliable delivery of packets as the transport layer in the OSI model does ...
Abstract - PG Embedded systems
... In telecommunication, information theory, and coding theory, forward error correction (FEC) or channel coding is a technique used for controlling errors in data transmission over unreliable or noisy communication channels. The central idea is the sender encodes their message in a redundant way by us ...
... In telecommunication, information theory, and coding theory, forward error correction (FEC) or channel coding is a technique used for controlling errors in data transmission over unreliable or noisy communication channels. The central idea is the sender encodes their message in a redundant way by us ...
No Slide Title - comp
... • Two most common network APIs: Sockets and X/Open Transport Interface (XTI), a slight modification of AT&T’s Transport Layer Interface (TLI). • The APIs allows programmers to easily make “connections” with another application process, without knowing how the underlying network ...
... • Two most common network APIs: Sockets and X/Open Transport Interface (XTI), a slight modification of AT&T’s Transport Layer Interface (TLI). • The APIs allows programmers to easily make “connections” with another application process, without knowing how the underlying network ...
Network Device Security Options
... Description of Ricoh Network Security Options available for MFP and Printer Products Network Port Security (ability to close unused network ports) Typically, network-enabled systems from all office equipment vendors are shipped to the customer with all the network ports “open,” making it as easy a ...
... Description of Ricoh Network Security Options available for MFP and Printer Products Network Port Security (ability to close unused network ports) Typically, network-enabled systems from all office equipment vendors are shipped to the customer with all the network ports “open,” making it as easy a ...
CPE 400: Computer Communication Networks
... Upon completion of the course, students will be able to: 1. Analyze OSI model and TCP/IP protocol architecture using network analysis tools (1.1, 1.3, 1.4, 1.5, 1.8, 1.10, 1.11) [1,2]. 2. Design and analyze data communication and data networking protocols (1.1, 1.3, ...
... Upon completion of the course, students will be able to: 1. Analyze OSI model and TCP/IP protocol architecture using network analysis tools (1.1, 1.3, 1.4, 1.5, 1.8, 1.10, 1.11) [1,2]. 2. Design and analyze data communication and data networking protocols (1.1, 1.3, ...
Document
... To do this, the router needs to have a Dynamic Host Configuration Protocol (DHCP) ability. DHCP assigns each device in the lower level LAN a specific IP address where it can be reached. This assignment is periodically checked by sending Address Resolution Protocol (ARP) packets. These packets make s ...
... To do this, the router needs to have a Dynamic Host Configuration Protocol (DHCP) ability. DHCP assigns each device in the lower level LAN a specific IP address where it can be reached. This assignment is periodically checked by sending Address Resolution Protocol (ARP) packets. These packets make s ...
that enables communication and transmission of data between
... precisely in April 1969 saw the release of the first RFC (Request for Comments) document, which launches a series of technical publications about the Internet. In the early 1970 the ARPANET grew to connect research institutes and laboratories ...
... precisely in April 1969 saw the release of the first RFC (Request for Comments) document, which launches a series of technical publications about the Internet. In the early 1970 the ARPANET grew to connect research institutes and laboratories ...
Zen and the Art of the Internet
... ◦ Packet-switching networks are more efficient if some amount of delay is acceptable. ...
... ◦ Packet-switching networks are more efficient if some amount of delay is acceptable. ...
Document
... To understand the flow of information on the Internet To understand the levels of activity in network traffic flow To understand the basis for vulnerabilities To understand the basis for security tools and how they work ...
... To understand the flow of information on the Internet To understand the levels of activity in network traffic flow To understand the basis for vulnerabilities To understand the basis for security tools and how they work ...
Chapter 1 - UniMAP Portal
... • Internet evolved from ARPANET – first operational packet network – applied to tactical radio & satellite nets also – had a need for interoperability – lead to standardized TCP/IP protocols ...
... • Internet evolved from ARPANET – first operational packet network – applied to tactical radio & satellite nets also – had a need for interoperability – lead to standardized TCP/IP protocols ...
IRIS Project
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
ppt in chapter 11
... plus firewall devices. Internal routers provide additional security to the network by screening traffic to various parts of the protected corporate network, and they do this using access lists. You can see where each of these types of devices are found in Figure below. ...
... plus firewall devices. Internal routers provide additional security to the network by screening traffic to various parts of the protected corporate network, and they do this using access lists. You can see where each of these types of devices are found in Figure below. ...
document
... • Replaces conventional remote login programs (sftp, sshd) • Supports multiple encryption algorithms • High-end security algorithms to detect identity spoofing • Authentication through RSA or DSA key pairs ...
... • Replaces conventional remote login programs (sftp, sshd) • Supports multiple encryption algorithms • High-end security algorithms to detect identity spoofing • Authentication through RSA or DSA key pairs ...
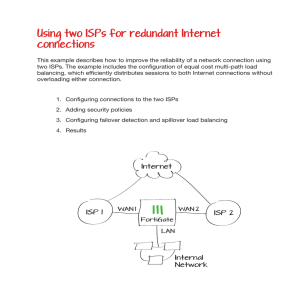
Using two ISPs for redundant Internet connections
... This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without overloading either connection. ...
... This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without overloading either connection. ...
Computer Networks - Texas State Department of Computer Science
... On a cable modem in your house… To download a music file of some sort To download a 3GB movie in MP4 format ...
... On a cable modem in your house… To download a music file of some sort To download a 3GB movie in MP4 format ...
eHealth Network Monitoring
... verify compliance with service level agreements (SLAs) Prevent outages and ensure availability by identifying which resources are at risk of failure Manage servers supporting network services, such as firewalls, DNS, and DHCP servers, on Windows and UNIX platforms Perform continuous, active te ...
... verify compliance with service level agreements (SLAs) Prevent outages and ensure availability by identifying which resources are at risk of failure Manage servers supporting network services, such as firewalls, DNS, and DHCP servers, on Windows and UNIX platforms Perform continuous, active te ...
Communications and networking history and background Internet
... voice calls need only a narrow bandwidth channel a call uses a dedicated circuit, with long setup and hold times telephone number is a unique identifier fixed routing for a specific call parallel signaling network; data separated from control simple user interface: all intelligence inside network gu ...
... voice calls need only a narrow bandwidth channel a call uses a dedicated circuit, with long setup and hold times telephone number is a unique identifier fixed routing for a specific call parallel signaling network; data separated from control simple user interface: all intelligence inside network gu ...
PowerPoint XP
... A receiver acknowledges if a packet is received properly A sender resends the same message after not hearing the acknowledgment for some time (a timeout period) ...
... A receiver acknowledges if a packet is received properly A sender resends the same message after not hearing the acknowledgment for some time (a timeout period) ...
INTRODUCTION TO INFORMATION SYSTEMS TECHNOLOGY
... Internet Telephony Uses Voice-over Internet Protocol (VoIP) Can use your computer to make phone calls Software connects computers via the Internet and transmits voice data Savings comes from eliminating toll charges ...
... Internet Telephony Uses Voice-over Internet Protocol (VoIP) Can use your computer to make phone calls Software connects computers via the Internet and transmits voice data Savings comes from eliminating toll charges ...
STATE UNIVERSITY OF NEW YORK COLLEGE OF TECHNOLOGY CANTON, NEW YORK
... ACTIVITY: 2 hours lecture and 2 hours laboratory per week H. CATALOG DESCRIPTION: This course will cover topics include: Network topologies and connectivity devices, TCP/IP protocol suite and internet protocol addressing, networks and sub-networks, network-layer protocols, internet control message ...
... ACTIVITY: 2 hours lecture and 2 hours laboratory per week H. CATALOG DESCRIPTION: This course will cover topics include: Network topologies and connectivity devices, TCP/IP protocol suite and internet protocol addressing, networks and sub-networks, network-layer protocols, internet control message ...
Chapter 20 - William Stallings, Data and Computer Communications
... level D will be delivered Traffic offered at service level E will be allotted twice the bandwidth of traffic delivered at service level F Traffic with drop precedence X has a higher probability of delivery than traffic with drop precedence Y ...
... level D will be delivered Traffic offered at service level E will be allotted twice the bandwidth of traffic delivered at service level F Traffic with drop precedence X has a higher probability of delivery than traffic with drop precedence Y ...
Kuliah Komunikasi Data
... Project 802, to set standards to enable intercommunication among equipment from a variety of manufacturers. Project 802 is a way of specifying functions of the physical layer and the data link layer of major LAN protocols. ...
... Project 802, to set standards to enable intercommunication among equipment from a variety of manufacturers. Project 802 is a way of specifying functions of the physical layer and the data link layer of major LAN protocols. ...
Presentation
... share. It also has installa4ons in Sri Lanka, Maldives, Belfast and Dubai. In most of these hotels Microsense has provided the network infrastructure and is also maintaining and managing the opera ...
... share. It also has installa4ons in Sri Lanka, Maldives, Belfast and Dubai. In most of these hotels Microsense has provided the network infrastructure and is also maintaining and managing the opera ...