Tema 1: Tecnologías de red. - GRC
... Documents cost SFr, but can get three freebies for each email address ...
... Documents cost SFr, but can get three freebies for each email address ...
VCAT/LCAS in a Nutshell - Grotto Networking Home
... does not overlap or conflict with GMPLS' routing or signaling functionality for the establishment of component links or entire VCAT groups. LCAS instead is used to control whether a particular component signal is actually put into service carrying traffic for the VCAT group. Although we are used to ...
... does not overlap or conflict with GMPLS' routing or signaling functionality for the establishment of component links or entire VCAT groups. LCAS instead is used to control whether a particular component signal is actually put into service carrying traffic for the VCAT group. Although we are used to ...
tymserve™ 2100ld
... is critical for accurate time stamps, operational logs, and security applications. Many complex data processing tasks are dependent upon precise event sequences that are, in turn, dependent upon each sequence having a correct time tag. By using something other than a dedicated time server, problems ...
... is critical for accurate time stamps, operational logs, and security applications. Many complex data processing tasks are dependent upon precise event sequences that are, in turn, dependent upon each sequence having a correct time tag. By using something other than a dedicated time server, problems ...
A Survey of BGP Security Issues and Solutions
... messages they send to each other would not be seen by any other party. However, Charlie could eavesdrop on the message stream between Alice and Bob, in an attempt to learn policy and routing information from the two parties. While this information is not necessarily sensitive, many service providers ...
... messages they send to each other would not be seen by any other party. However, Charlie could eavesdrop on the message stream between Alice and Bob, in an attempt to learn policy and routing information from the two parties. While this information is not necessarily sensitive, many service providers ...
Efficient Data Transfer Protocols for Big Data
... The current state-of-the-art for bulk transfer of large scientific data sets is to use tools such as Globus Online / GridFTP that securely move data using parallel TCP streams. Using these tools on properly tuned hosts, where there are no network impediments such as an under-powered firewall applian ...
... The current state-of-the-art for bulk transfer of large scientific data sets is to use tools such as Globus Online / GridFTP that securely move data using parallel TCP streams. Using these tools on properly tuned hosts, where there are no network impediments such as an under-powered firewall applian ...
Chapter 1
... • Helps stabilize routing information and helps prevent routing loops. (Much more later!). Once a route is marked as unreachable, it must stay in holddown long enough for all routers in the topology to learn about the Chapter 4 CCNA2-39 unreachable network. By default, the holddown timer is set for ...
... • Helps stabilize routing information and helps prevent routing loops. (Much more later!). Once a route is marked as unreachable, it must stay in holddown long enough for all routers in the topology to learn about the Chapter 4 CCNA2-39 unreachable network. By default, the holddown timer is set for ...
Broadband Reference Guide
... K-12 education to have 1Gb per 1,000 students; however, students also need the affordable access and connectivity outside of the school day. “Homework” today requires access to online information at home and thus the ability for students and families to have affordable broadband that meets the FCC r ...
... K-12 education to have 1Gb per 1,000 students; however, students also need the affordable access and connectivity outside of the school day. “Homework” today requires access to online information at home and thus the ability for students and families to have affordable broadband that meets the FCC r ...
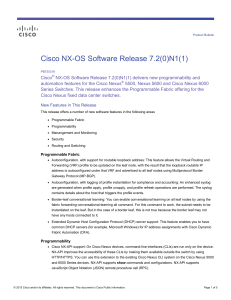
PDF
... fabric forwarding conversational-learning all command. For this command to work, the subnet needs to be instantiated on the leaf. But in the case of a border leaf, this is not true because the border leaf may not have any hosts connected to it. ...
... fabric forwarding conversational-learning all command. For this command to work, the subnet needs to be instantiated on the leaf. But in the case of a border leaf, this is not true because the border leaf may not have any hosts connected to it. ...
TCP operations
... data. For applications TCP provides a standard way of accessing remote computers on unreliable internetwork. This reliability is provided by adding services on top of IP. IP is connectionless and does not guarantee delivery of packets. The reliability of TCP is achieved by retransmitting data, which ...
... data. For applications TCP provides a standard way of accessing remote computers on unreliable internetwork. This reliability is provided by adding services on top of IP. IP is connectionless and does not guarantee delivery of packets. The reliability of TCP is achieved by retransmitting data, which ...
abstract - Douglas Reeves
... involved in routing packets to the destination peer. Hence, there needs to be a mechanism to maintain the authenticity, confidentiality and integrity of messages. There has been some work on avoiding attacks that prevent correct message delivery in P2P networks [14]. • Peer Authentication: Since the ...
... involved in routing packets to the destination peer. Hence, there needs to be a mechanism to maintain the authenticity, confidentiality and integrity of messages. There has been some work on avoiding attacks that prevent correct message delivery in P2P networks [14]. • Peer Authentication: Since the ...
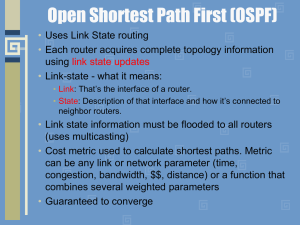
computer networks
... Each router must do the following: 1. Discover its neighbors, learn their network address. 2. Measure the delay or cost to each of its neighbors. 3. Construct a packet telling all it has just learned. 4. Send this packet to all other routers. 5. Compute the shortest path to every other router. ...
... Each router must do the following: 1. Discover its neighbors, learn their network address. 2. Measure the delay or cost to each of its neighbors. 3. Construct a packet telling all it has just learned. 4. Send this packet to all other routers. 5. Compute the shortest path to every other router. ...
Broadband Router with built-in ADSL Modem
... Party Line Service is subject to state tariffs. When programming and/or making test calls to emergency numbers: • Remain on the line and briefly explain to the dispatcher the reason for the call. • Perform such activities in off-peak hours such as early morning or late evenings. The Telephone Consum ...
... Party Line Service is subject to state tariffs. When programming and/or making test calls to emergency numbers: • Remain on the line and briefly explain to the dispatcher the reason for the call. • Perform such activities in off-peak hours such as early morning or late evenings. The Telephone Consum ...
Hacking Wireless Networks
... uses the Orthogonal Frequency Division Multiplexing (OFDM) encoding class. The maximum speed supported by the 802.11a standard is 54Mbps. 802.11b: 802.11b is an amendment to the IEEE 802.11 specification that extended the throughput up to 11 Mbit/s using the same 2.4 GHz band. This specification und ...
... uses the Orthogonal Frequency Division Multiplexing (OFDM) encoding class. The maximum speed supported by the 802.11a standard is 54Mbps. 802.11b: 802.11b is an amendment to the IEEE 802.11 specification that extended the throughput up to 11 Mbit/s using the same 2.4 GHz band. This specification und ...
Cisco Nexus 1000V Series Switches
... The Cisco Nexus 1000V Series provides a common management model for both physical and virtual network infrastructures through Cisco VN-Link technology, which includes policy-based virtual machine connectivity, mobility of virtual machine security and network properties, and a non-disruptive operatio ...
... The Cisco Nexus 1000V Series provides a common management model for both physical and virtual network infrastructures through Cisco VN-Link technology, which includes policy-based virtual machine connectivity, mobility of virtual machine security and network properties, and a non-disruptive operatio ...
Arctic networking properties
... communicating parties must know each other's public keys in order to be able to authenticate ...
... communicating parties must know each other's public keys in order to be able to authenticate ...
Experiment Manual
... Experiment 3: Simulate a three node point-to-point network with the links connected as follows: n0 n2, n1 n2 and n2 n3. Apply TCP agent between n0-n3 and UDP between n1-n3. Apply relevant applications over TCP and UDP agents changing the parameter and determine the number of packets sent by TC ...
... Experiment 3: Simulate a three node point-to-point network with the links connected as follows: n0 n2, n1 n2 and n2 n3. Apply TCP agent between n0-n3 and UDP between n1-n3. Apply relevant applications over TCP and UDP agents changing the parameter and determine the number of packets sent by TC ...
The CELTIC Office Workplan
... – Bind HIP transport protocol (e.g IPsec ESP beet mode) with EPC bearers to provide appropriate QoS for different application classes. – Issues with introducing HIP on 3GPP-access networks ...
... – Bind HIP transport protocol (e.g IPsec ESP beet mode) with EPC bearers to provide appropriate QoS for different application classes. – Issues with introducing HIP on 3GPP-access networks ...
The Internet and Its Uses
... released a document summarizing the Ten Most Critical Internet Security Vulnerabilities. Since that time, thousands of organizations rely on this list to prioritize their efforts so they can close the most dangerous holes first. The threat landscape is very dynamic, which in turn makes it necessary ...
... released a document summarizing the Ten Most Critical Internet Security Vulnerabilities. Since that time, thousands of organizations rely on this list to prioritize their efforts so they can close the most dangerous holes first. The threat landscape is very dynamic, which in turn makes it necessary ...
View PDF - Allied Telesis
... platforms. For information about how to install the adapters as well as procedures to install and configure the related software, see the Gigabit Ethernet Network Adapters Installation Guide (part number 613-000049). The Preface contains the following sections: ...
... platforms. For information about how to install the adapters as well as procedures to install and configure the related software, see the Gigabit Ethernet Network Adapters Installation Guide (part number 613-000049). The Preface contains the following sections: ...
pptx - Department of Computer Science
... User public keys are certified by login server at login. ...
... User public keys are certified by login server at login. ...
Which three statements regarding IP multicast addresses are
... Lack of congestion control may result in overall network degradation as the popularity of UDP-based multicast applications grow. Best effort delivery may result in heavy drops on voice applications, which will cause jerky, missed speech patterns that can make the content unintelligible when the drop ...
... Lack of congestion control may result in overall network degradation as the popularity of UDP-based multicast applications grow. Best effort delivery may result in heavy drops on voice applications, which will cause jerky, missed speech patterns that can make the content unintelligible when the drop ...
NetApp CN1610 Switch Administrator`s Guide
... The CN1610 switch supports router advertisement as an integral part of IPv6. Numerous options are available, including stateless/stateful address configuration, router and address lifetimes, and neighbor discovery timer control. The switch also supports Ethernet and tunnel interfaces. For Ethernet, ...
... The CN1610 switch supports router advertisement as an integral part of IPv6. Numerous options are available, including stateless/stateful address configuration, router and address lifetimes, and neighbor discovery timer control. The switch also supports Ethernet and tunnel interfaces. For Ethernet, ...