Fast Variants of RSA
... able to interoperate with systems that are built for standard RSA; moreover, existing Certificate Authorities must be able to respond to a certificate request for a variant-RSA public key. The security of these variants is an open problem. We cannot show that an attack on any of these variants would ...
... able to interoperate with systems that are built for standard RSA; moreover, existing Certificate Authorities must be able to respond to a certificate request for a variant-RSA public key. The security of these variants is an open problem. We cannot show that an attack on any of these variants would ...
Cryptographic hashing - comp
... The main problem is that there is no special processing at the end of the hash function computation. Consider that Alice sends a message to Bob and wants to authenticate it by sending h(K||m), where K is a secret shared by Alice and Bob. Now an attacker can append text to m, and update the hash ...
... The main problem is that there is no special processing at the end of the hash function computation. Consider that Alice sends a message to Bob and wants to authenticate it by sending h(K||m), where K is a secret shared by Alice and Bob. Now an attacker can append text to m, and update the hash ...
Public-Key Cryptosystems from the Worst
... approximation factor for GapSVP is Õ(n/α), where (roughly speaking) α · q is the standard deviation of the Gaussian error distribution over Zq . More generally, our reduction implies that for moduli as small as (say) q ≥ n/α, search-LWE is at least as hard as classically approximating a novel varia ...
... approximation factor for GapSVP is Õ(n/α), where (roughly speaking) α · q is the standard deviation of the Gaussian error distribution over Zq . More generally, our reduction implies that for moduli as small as (say) q ≥ n/α, search-LWE is at least as hard as classically approximating a novel varia ...
Induction
... Mathematical induction proves a predicate is true for all integers greater than some number. ...
... Mathematical induction proves a predicate is true for all integers greater than some number. ...
TAKA_10v1_public-key cryptosystems bsed on CR
... The random choice of r, Pr[AskH]=O(qH/2t) in any case, qH=#(queries asked to the oracle H) and 0≦r<2t. G and H are seen like random oracles, the attacker has no chance to correctly guess b, during a real attack. ...
... The random choice of r, Pr[AskH]=O(qH/2t) in any case, qH=#(queries asked to the oracle H) and 0≦r<2t. G and H are seen like random oracles, the attacker has no chance to correctly guess b, during a real attack. ...
Organizations That Use TLS/SSL
... With all the recent stories about security breaches, you may be wondering what you can do to help secure your nonprofit or library's data and communications. Transport Layer Security (TLS) is a protocol (or set of guidelines) that can help you do this. If your organization stores or processes paymen ...
... With all the recent stories about security breaches, you may be wondering what you can do to help secure your nonprofit or library's data and communications. Transport Layer Security (TLS) is a protocol (or set of guidelines) that can help you do this. If your organization stores or processes paymen ...
Protecting the FPGA Design From Common Threats
... Though the definition of zeroization involves a clear plus verification that all data was cleared, most applications will benefit from a zeroization which clears all memory cells of the FPGA. The Cyclone III LS zeroization solution breaks out the clear function and the verification function to provi ...
... Though the definition of zeroization involves a clear plus verification that all data was cleared, most applications will benefit from a zeroization which clears all memory cells of the FPGA. The Cyclone III LS zeroization solution breaks out the clear function and the verification function to provi ...
Extended Hidden Number Problem and Its
... these known bits had to be consecutively placed on the position of either most or least significant bits or they had to occupy a block of bits somewhere in the middle of each nonce. An idea was given on how to overcome this restriction, based on a multidimensional diophantine approximation. Deeper in ...
... these known bits had to be consecutively placed on the position of either most or least significant bits or they had to occupy a block of bits somewhere in the middle of each nonce. An idea was given on how to overcome this restriction, based on a multidimensional diophantine approximation. Deeper in ...
Defense In Depth
... (DoS) attacks. A DoS attack is an attack on network resources to prevent users from getting to what they need. For instance, a smurf attack takes advantage of improperly configured routers on another network to fully consume a network’s bandwidth so legitimate users cannot access network resources. ...
... (DoS) attacks. A DoS attack is an attack on network resources to prevent users from getting to what they need. For instance, a smurf attack takes advantage of improperly configured routers on another network to fully consume a network’s bandwidth so legitimate users cannot access network resources. ...
SSABSA support materials
... Ref: A185579 (revised January 2013) © SACE Board of South Australia 2010 ...
... Ref: A185579 (revised January 2013) © SACE Board of South Australia 2010 ...
Chapter 9 - EECS People Web Server
... Network IDSs must match known and unknown attack strategies against their knowledge base to determine whether an attack has occurred These systems yield many more false-positive readings than do host-based IDSs, because they are attempting to read the network activity pattern to determine what i ...
... Network IDSs must match known and unknown attack strategies against their knowledge base to determine whether an attack has occurred These systems yield many more false-positive readings than do host-based IDSs, because they are attempting to read the network activity pattern to determine what i ...
CHAPTER 1 Networking Concepts
... A. Conventional Encryption Also referred to as symmetry encryption or single-key encryption A form of cryptosystem in which encryption and decryption are performed using the same key This encryption scheme has five ingredients Plaintext: Readable message or data Encryption Algorithm: Performs ...
... A. Conventional Encryption Also referred to as symmetry encryption or single-key encryption A form of cryptosystem in which encryption and decryption are performed using the same key This encryption scheme has five ingredients Plaintext: Readable message or data Encryption Algorithm: Performs ...
Datasäkerhet/Data security EDA625 – Lect2 CRYPTOGRAPHY
... strong collision resistance: it is infeasable to find x,x’ such that h(x)=h(x’) ...
... strong collision resistance: it is infeasable to find x,x’ such that h(x)=h(x’) ...
Joshua White - Everis Inc.
... Joshua White Director of CyOON Research and Development “Cyber Operations for Optical Networks” [email protected] Everis Inc http://www.EverisInc.com ...
... Joshua White Director of CyOON Research and Development “Cyber Operations for Optical Networks” [email protected] Everis Inc http://www.EverisInc.com ...
CIS 5357 - FSU Computer Science
... If b’ = b, the attacker wins. If every attacker has only a negligible probability of success, we say that the scheme is secure under chosen-plaintext attacks. ...
... If b’ = b, the attacker wins. If every attacker has only a negligible probability of success, we say that the scheme is secure under chosen-plaintext attacks. ...
CSIT560 Project Presentation
... standard is becoming the international standard for VPN. IPSec has created a secure means for interoperable security, which guarantees that encrypted information is protected on its way from one network to another, while also allowing partner companies to link their respective VPNs together, even ...
... standard is becoming the international standard for VPN. IPSec has created a secure means for interoperable security, which guarantees that encrypted information is protected on its way from one network to another, while also allowing partner companies to link their respective VPNs together, even ...
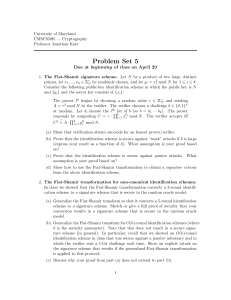
pdf
... key is N, e, y and the secret key is x for which x e = y). Prove that this is indeed a secure identity-based scheme when H is a random oracle. More formally, show that an adversary who obtains the secret keys for users ID 1 , . . . , ID` cannot forge a signature for a user ID 0 6∈ {ID1 , . . . , ID` ...
... key is N, e, y and the secret key is x for which x e = y). Prove that this is indeed a secure identity-based scheme when H is a random oracle. More formally, show that an adversary who obtains the secret keys for users ID 1 , . . . , ID` cannot forge a signature for a user ID 0 6∈ {ID1 , . . . , ID` ...
22C:19 Discrete Math
... study in pure mathematics. However, in modern times, number theory is very important in the area of security. Encryption algorithms heavily depend on modular arithmetic, and our ability to deal with large integers. We need appropriate techniques to deal with such algorithms. ...
... study in pure mathematics. However, in modern times, number theory is very important in the area of security. Encryption algorithms heavily depend on modular arithmetic, and our ability to deal with large integers. We need appropriate techniques to deal with such algorithms. ...
Notes
... We have already looked at the analysis of fixed point iterations in 1D; here, the analysis is not much different. Subtract the fixed point equation x = x + Â−1 (b − Ax), and we find e(k+1) = (I − Â−1 A)e(k) . Taking norms, we find that the rate of convergence of the iteration depends on kI − Â−1 ...
... We have already looked at the analysis of fixed point iterations in 1D; here, the analysis is not much different. Subtract the fixed point equation x = x + Â−1 (b − Ax), and we find e(k+1) = (I − Â−1 A)e(k) . Taking norms, we find that the rate of convergence of the iteration depends on kI − Â−1 ...
Computer Security and Penetration Testing Chapter 11 Denial
... – Z axis =Voluntary or involuntary, on the part of the systems administrator ...
... – Z axis =Voluntary or involuntary, on the part of the systems administrator ...
Cryptanalysis of Shieh-Lin-Yang
... The message m is first signed by an initiator U1, and then is sent separately to all signer. Finally,U1 is responsible for combining these individual signature into a multisignature. ...
... The message m is first signed by an initiator U1, and then is sent separately to all signer. Finally,U1 is responsible for combining these individual signature into a multisignature. ...
Number Theory: Applications
... Open Hashing (aka separate chaining) – each hash address is the head of a linked list. When collisions occur, the new key is appended to the end of the list. Closed Hashing (aka open addressing) – when collisions occur, we attempt to hash the item into an adjacent hash address. This is known as line ...
... Open Hashing (aka separate chaining) – each hash address is the head of a linked list. When collisions occur, the new key is appended to the end of the list. Closed Hashing (aka open addressing) – when collisions occur, we attempt to hash the item into an adjacent hash address. This is known as line ...
Cryptanalysis

Cryptanalysis (from the Greek kryptós, ""hidden"", and analýein, ""to loosen"" or ""to untie"") is the study of analyzing information systems in order to study the hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown.In addition to mathematical analysis of cryptographic algorithms, cryptanalysis includes the study of side-channel attacks that do not target weaknesses in the cryptographic algorithms themselves, but instead exploit weaknesses in their implementation.Even though the goal has been the same, the methods and techniques of cryptanalysis have changed drastically through the history of cryptography, adapting to increasing cryptographic complexity, ranging from the pen-and-paper methods of the past, through machines like the British Bombes and Colossus computers at Bletchley Park in World War II, to the mathematically advanced computerized schemes of the present. Methods for breaking modern cryptosystems often involve solving carefully constructed problems in pure mathematics, the best-known being integer factorization.