Network Security Overview
... availability, which are basic factors in information security. • Information security protects valuable information from unauthorized access, modification and distribution. • The CIA triad guides information security efforts to ensure success. • There are instances when one of the goals of the CIA t ...
... availability, which are basic factors in information security. • Information security protects valuable information from unauthorized access, modification and distribution. • The CIA triad guides information security efforts to ensure success. • There are instances when one of the goals of the CIA t ...
Chapter 15 Operating System Security
... completely remove all components of a package should an attacker succeed in gaining some access to a system, disabled software could be re-enabled and used to further compromise a system it is better for security if unwanted software is not installed, and thus not available for use at all ...
... completely remove all components of a package should an attacker succeed in gaining some access to a system, disabled software could be re-enabled and used to further compromise a system it is better for security if unwanted software is not installed, and thus not available for use at all ...
... completely remove all components of a package should an attacker succeed in gaining some access to a system, disabled software could be re-enabled and used to further compromise a system it is better for security if unwanted software is not installed, and thus not available for use at all ...
Document
... effects on your organization. 2. Security topology covers four primary areas of concern (design goals, security zones, technologies, and business requirements). Describe each area including key topics in each area. 3. Discuss software threats classified as malicious code on page 81 of your text. ...
... effects on your organization. 2. Security topology covers four primary areas of concern (design goals, security zones, technologies, and business requirements). Describe each area including key topics in each area. 3. Discuss software threats classified as malicious code on page 81 of your text. ...
Essentials of Business Information Systems Chapter 7 Securing
... • Internet vulnerabilities • Network open to anyone • Size of Internet means abuses can have wide impact • Use of fixed Internet addresses with permanent connections to Internet eases identification by ...
... • Internet vulnerabilities • Network open to anyone • Size of Internet means abuses can have wide impact • Use of fixed Internet addresses with permanent connections to Internet eases identification by ...
William Stallings, Cryptography and Network Security 3/e
... relative simplicity, it is easier to check such modifications for security flaws. • Each proxy is independent of other proxies on the bastion host—a problem with one will not affect the others. • A proxy generally performs no disk access other than to read its initial configuration file. This makes ...
... relative simplicity, it is easier to check such modifications for security flaws. • Each proxy is independent of other proxies on the bastion host—a problem with one will not affect the others. • A proxy generally performs no disk access other than to read its initial configuration file. This makes ...
Identify Security Risks and Threats
... Create and configure an IP Security policy that contains IPSec port filters that will be used to lock down unnecessary ports on an IIS server View IPSec port filter properties ...
... Create and configure an IP Security policy that contains IPSec port filters that will be used to lock down unnecessary ports on an IIS server View IPSec port filter properties ...
Architecting High-Security Systems for Multilateral
... separated sessions. In fact it enables the user to securely access multiple, differently classified networks from within a single system. Nonetheless, the separation of those networks is maintained at all times. As different networks are not necessarily under control of one single organisation, our ...
... separated sessions. In fact it enables the user to securely access multiple, differently classified networks from within a single system. Nonetheless, the separation of those networks is maintained at all times. As different networks are not necessarily under control of one single organisation, our ...
Threat Briefing - (AFCEA) Ottawa Chapter
... cloud computing present new and complex security questions that can lead to huge vulnerabilities if not addressed properly. Network boundaries are becoming more blurred. Computing services such as data storage and document management are being provided via the web or ‘Internet Cloud’. If that wasn’t ...
... cloud computing present new and complex security questions that can lead to huge vulnerabilities if not addressed properly. Network boundaries are becoming more blurred. Computing services such as data storage and document management are being provided via the web or ‘Internet Cloud’. If that wasn’t ...
Chapter 1
... Penetration may not necessarily be by the most obvious means, nor via the one we have the most defense against. Consider all the means of penetration Checked repeated times Don’t underestimate the attacker/think like an attacker Strengthening one thin might weaken another ...
... Penetration may not necessarily be by the most obvious means, nor via the one we have the most defense against. Consider all the means of penetration Checked repeated times Don’t underestimate the attacker/think like an attacker Strengthening one thin might weaken another ...
Chapter 1
... Penetration may not necessarily be by the most obvious means, nor via the one we have the most defense against. Consider all the means of penetration Checked repeated times Don’t underestimate the attacker/think like an attacker Strengthening one thin might weaken another ...
... Penetration may not necessarily be by the most obvious means, nor via the one we have the most defense against. Consider all the means of penetration Checked repeated times Don’t underestimate the attacker/think like an attacker Strengthening one thin might weaken another ...
Support: Ticket, Process, and Expectations
... Great approach for home computers as it provides a location for all work files to be placed in an encrypted "drive" and when the computer isn't being used for work purposes, it is simply not connected and is thus protected from anyone else accessing the files. ...
... Great approach for home computers as it provides a location for all work files to be placed in an encrypted "drive" and when the computer isn't being used for work purposes, it is simply not connected and is thus protected from anyone else accessing the files. ...
How does it get written up?
... How can it be exploited For an attack or exploit, what sort of damage does it do • Any forensics: logs or other evidence of exploitation ...
... How can it be exploited For an attack or exploit, what sort of damage does it do • Any forensics: logs or other evidence of exploitation ...
Bandura® Releases REACT™ Software to Integrate Internal
... ST. LOUIS (MARCH 24, 2015) – Bandura, LLC, manufacturer of the U.S. Defense‐tested PoliWall cyber security technology, today introduced the REACT™ software product that allows customers to integrate real‐time threat information from their own network into the PoliWall® security appliance, providin ...
... ST. LOUIS (MARCH 24, 2015) – Bandura, LLC, manufacturer of the U.S. Defense‐tested PoliWall cyber security technology, today introduced the REACT™ software product that allows customers to integrate real‐time threat information from their own network into the PoliWall® security appliance, providin ...
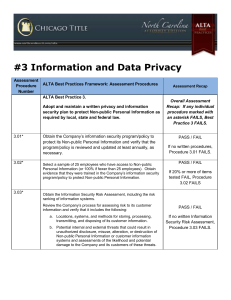
ALTA Assessment Procedures
... a. Obtain and review change management procedures when technology and business function changes are made. ...
... a. Obtain and review change management procedures when technology and business function changes are made. ...
Information Security Incident Management
... with a risk assessment to established the required security controls needed to adequately manage information security risks within the business processes • Used in conjunction with BS7799, it also establish documentation, revision, communication, training, auditing and continuous improvement require ...
... with a risk assessment to established the required security controls needed to adequately manage information security risks within the business processes • Used in conjunction with BS7799, it also establish documentation, revision, communication, training, auditing and continuous improvement require ...
About EICTA - Baltic IT&T Review
... Intruders gained access to VISA computer network in the U.K. and later demanded ransom for data obtained in the virtual break-in; company received a ransom demand of £10 million. (Apr’01) A system administrator, angered by his diminished role in a thriving defense manufacturing firm whose computer n ...
... Intruders gained access to VISA computer network in the U.K. and later demanded ransom for data obtained in the virtual break-in; company received a ransom demand of £10 million. (Apr’01) A system administrator, angered by his diminished role in a thriving defense manufacturing firm whose computer n ...
security threats: a guide for small and medium
... passwords may not be changed (especially if not documented) thus leaving a backdoor for the exemployee. A startup company called JournalSpace 4 was caught with no backups when their former system administrator decided to wipe out the main database. This proved to be disastrous for the company which ...
... passwords may not be changed (especially if not documented) thus leaving a backdoor for the exemployee. A startup company called JournalSpace 4 was caught with no backups when their former system administrator decided to wipe out the main database. This proved to be disastrous for the company which ...
pdNickname Site License
... I. This Site License grants to the Licensee the right to install the licensed version of pdNickname (hereinafter, ‘information’) on all computers in the same building within a single company or organization. Separate Site Licenses must be purchased for each building the information is used in. II. T ...
... I. This Site License grants to the Licensee the right to install the licensed version of pdNickname (hereinafter, ‘information’) on all computers in the same building within a single company or organization. Separate Site Licenses must be purchased for each building the information is used in. II. T ...
Introduction to Access PowerPoint
... organized by name, date created, link to the document/project or digital image of the student work •Create a database information and images on a historical event (World War I) that includes significant battles, leaders, documents, places, etc. ...
... organized by name, date created, link to the document/project or digital image of the student work •Create a database information and images on a historical event (World War I) that includes significant battles, leaders, documents, places, etc. ...
Chapter 19
... 802.11i Architecture • Authentication: protocol used to define an exchange between a user and an AS • Access control: function that enforces the use of the authentication function, routes messages properly and facilitates key exchange. • Privacy with message integrity: MAC-level data are encrypted ...
... 802.11i Architecture • Authentication: protocol used to define an exchange between a user and an AS • Access control: function that enforces the use of the authentication function, routes messages properly and facilitates key exchange. • Privacy with message integrity: MAC-level data are encrypted ...
Chapter 1 THE INFORMATION AGE IN WHICH YOU LIVE Changing
... o Companies need information about their employees to run their business effectively o As of March 2005, 60% of employers monitored employee e-mails o 70% of Web traffic occurs during work hours o 78% of employers reported abuse o 60% employees admitted abuse ...
... o Companies need information about their employees to run their business effectively o As of March 2005, 60% of employers monitored employee e-mails o 70% of Web traffic occurs during work hours o 78% of employers reported abuse o 60% employees admitted abuse ...
Resume - OPResume.com
... Provided troubleshooting via telephone and in-person to 1550 internal and external customers, including the installation and configuration of software, password resets and first-line diagnosis/troubleshooting for computer hardware and software problems. Implemented an organization’s computer informa ...
... Provided troubleshooting via telephone and in-person to 1550 internal and external customers, including the installation and configuration of software, password resets and first-line diagnosis/troubleshooting for computer hardware and software problems. Implemented an organization’s computer informa ...