IPSec (IP Security)
... encrypted messages (with key from Phase1) second set of shared secret keys Phase1-SA is used to setup IPSec SAs usually (at least)two unidirectional IPSec SAs Phase2 repeated to change keys, Phase1-SA remains ...
... encrypted messages (with key from Phase1) second set of shared secret keys Phase1-SA is used to setup IPSec SAs usually (at least)two unidirectional IPSec SAs Phase2 repeated to change keys, Phase1-SA remains ...
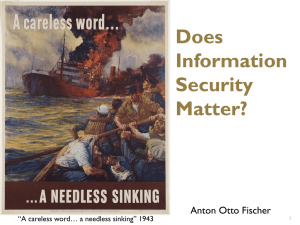
Slide 1
... identification, performance data, geo-spatial and netspatial information, control plane information, and extended service content. Available Network Flow Information ...
... identification, performance data, geo-spatial and netspatial information, control plane information, and extended service content. Available Network Flow Information ...
RF-LAMBDA
... The information contained herein is believed to be reliable. RF‐Lambda makes no warranties regarding the information contained herein. RF‐ Lambda assumes no responsibility or liability whatsoever for any of the information contained herein. RF‐Lambda assumes no responsibility or liability whatsoever ...
... The information contained herein is believed to be reliable. RF‐Lambda makes no warranties regarding the information contained herein. RF‐ Lambda assumes no responsibility or liability whatsoever for any of the information contained herein. RF‐Lambda assumes no responsibility or liability whatsoever ...
Privacy Policy - Cummings Flavel McCormack
... of this policy. Upon such contact we undertake to respond within 30 days. Keeping your personal information secure We will take all reasonable steps to protect your personal information held by us from misuse, loss, interference and from unauthorized access, modification or disclosure. Our security ...
... of this policy. Upon such contact we undertake to respond within 30 days. Keeping your personal information secure We will take all reasonable steps to protect your personal information held by us from misuse, loss, interference and from unauthorized access, modification or disclosure. Our security ...
Unix Network Security - LSU Computer Science
... Prevention of unauthorized disclosure of information. • Integrity Prevention of unauthorized modifications of information. • Availability Prevention of unauthorized withholding of information or resources Confidentiality is keeping your data or communication secret to others. Only authorized person ...
... Prevention of unauthorized disclosure of information. • Integrity Prevention of unauthorized modifications of information. • Availability Prevention of unauthorized withholding of information or resources Confidentiality is keeping your data or communication secret to others. Only authorized person ...
Text Based Information Retrieval H02C8A H02C8B
... retrieved when users web search Clustering: finding Retrieval: finding Ranking: deciding similar documents good documents to of the relevant which so they can be answer users’ documents are the retrieved together or queries best stored on same servers ...
... retrieved when users web search Clustering: finding Retrieval: finding Ranking: deciding similar documents good documents to of the relevant which so they can be answer users’ documents are the retrieved together or queries best stored on same servers ...
CLOUDS ON THE INFORMATION HORIZON:
... (PII) is subject to many restrictions worldwide. Transferring this information to a SaaS provider may violate some countries’ laws. PII is not the only issue. Country restrictions vary, but information potentially subject to privacy, location, and other restrictions can include financial data, intel ...
... (PII) is subject to many restrictions worldwide. Transferring this information to a SaaS provider may violate some countries’ laws. PII is not the only issue. Country restrictions vary, but information potentially subject to privacy, location, and other restrictions can include financial data, intel ...
RF-LAMBDA
... The information contained herein is believed to be reliable. RF‐Lambda makes no warranties regarding the information contained herein. RF‐ Lambda assumes no responsibility or liability whatsoever for any of the information contained herein. RF‐Lambda assumes no responsibility or liability whatsoever ...
... The information contained herein is believed to be reliable. RF‐Lambda makes no warranties regarding the information contained herein. RF‐ Lambda assumes no responsibility or liability whatsoever for any of the information contained herein. RF‐Lambda assumes no responsibility or liability whatsoever ...
L16_Security
... a transferred file are subject to these threats encryption masks the contents of what is transferred so even if obtained by someone, they would be unable to extract information ...
... a transferred file are subject to these threats encryption masks the contents of what is transferred so even if obtained by someone, they would be unable to extract information ...
TrendMicro Titanium - A New Concept in Security by Ira Wilsker
... This lack of frequent signature file updating may have been an acute disadvantage with earlier security products, where failure to update frequently would leave the computer ...
... This lack of frequent signature file updating may have been an acute disadvantage with earlier security products, where failure to update frequently would leave the computer ...
Chapter 3 - Cal State LA - Instructional Web Server
... Strategic Management Support • Covered many c-level positions in Chapter 2 for IT • 2 others in information management • Data administration – function that plans for, oversees the development of, and monitors the information resource • Database administration – function responsible for the more te ...
... Strategic Management Support • Covered many c-level positions in Chapter 2 for IT • 2 others in information management • Data administration – function that plans for, oversees the development of, and monitors the information resource • Database administration – function responsible for the more te ...
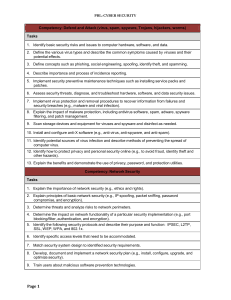
Competency: Defend and Attack (virus, spam, spyware - FBLA-PBL
... Computer Network Software Operations, Computer Applications, Information Technology Fundamentals, and Computer Information Systems Competency-Based Tasks/Competency Lists. 2009-2010. Virginia Department of Education. Richmond, VA. Computer Business Applications and Network Administration. 2001. Care ...
... Computer Network Software Operations, Computer Applications, Information Technology Fundamentals, and Computer Information Systems Competency-Based Tasks/Competency Lists. 2009-2010. Virginia Department of Education. Richmond, VA. Computer Business Applications and Network Administration. 2001. Care ...
evesecures9
... January 2009, Heartland Payment Systems – Malicious software on payment processing network ...
... January 2009, Heartland Payment Systems – Malicious software on payment processing network ...
BILL ANALYSIS
... security. This fragmented network security approach can lead to overlapping and redundant state assets on one hand which cost more money than necessary, and a lack of security features on the other hand where monetary resources are lacking. A recent report by the Department of Information Resources ...
... security. This fragmented network security approach can lead to overlapping and redundant state assets on one hand which cost more money than necessary, and a lack of security features on the other hand where monetary resources are lacking. A recent report by the Department of Information Resources ...
Information Assurance Presentation
... Overflows occur when a program tries to store more data than the allocated memory can hold. The extra data slops over into the adjacent memory area, overwriting what was already there, including data or instructions. Malicious hackers have become proficient at leveraging such overflows to introduc ...
... Overflows occur when a program tries to store more data than the allocated memory can hold. The extra data slops over into the adjacent memory area, overwriting what was already there, including data or instructions. Malicious hackers have become proficient at leveraging such overflows to introduc ...
Slide 1
... Project Agency (ARPA) of the U.S. government in 1969 and was known as ARPAnet. It was designed to enable U.S. military leaders to stay in contact in case of a nuclear war. The protocol used in ARPAnet was called Network Control Protocol (NCP). The protocol had too many limitations and was not robust ...
... Project Agency (ARPA) of the U.S. government in 1969 and was known as ARPAnet. It was designed to enable U.S. military leaders to stay in contact in case of a nuclear war. The protocol used in ARPAnet was called Network Control Protocol (NCP). The protocol had too many limitations and was not robust ...
Powerpoint Slides
... Public key encryption scheme can also handle the problem of privacy. Sender uses the receiver’s public key to encode the message. Receiver uses it’s private key to decode the message. Messages can be encoded twice to authenticate the sender and to enforce privacy. First with the sender’s private ...
... Public key encryption scheme can also handle the problem of privacy. Sender uses the receiver’s public key to encode the message. Receiver uses it’s private key to decode the message. Messages can be encoded twice to authenticate the sender and to enforce privacy. First with the sender’s private ...
Ethics in Information Technology
... – Are updated with encrypted data every time the card is used – Used widely in Europe – Not widely used in the U.S. ...
... – Are updated with encrypted data every time the card is used – Used widely in Europe – Not widely used in the U.S. ...
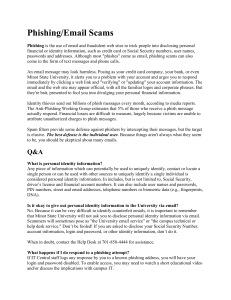
Phishing/Email Scams - Minot State University
... that Minot State University will not ask you to disclose personal identity information via email. Scammers will sometimes pose as "the University email service" or "the campus technical or help desk service." Don’t be fooled! If you are asked to disclose your Social Security Number, account informat ...
... that Minot State University will not ask you to disclose personal identity information via email. Scammers will sometimes pose as "the University email service" or "the campus technical or help desk service." Don’t be fooled! If you are asked to disclose your Social Security Number, account informat ...
RF-LAMBDA
... The information contained herein is believed to be reliable. RF‐Lambda makes no warranties regarding the information contained herein. RF‐ Lambda assumes no responsibility or liability whatsoever for any of the information contained herein. RF‐Lambda assumes no responsibility or liability whatsoever ...
... The information contained herein is believed to be reliable. RF‐Lambda makes no warranties regarding the information contained herein. RF‐ Lambda assumes no responsibility or liability whatsoever for any of the information contained herein. RF‐Lambda assumes no responsibility or liability whatsoever ...
Key To Personal Information Security
... • Provides a type of firewall by hiding internal IP addresses for external or untrusted users • Expands the number of internal IP addresses available to an organization • No possibility of conflict with IP addresses used by other companies and organizations ...
... • Provides a type of firewall by hiding internal IP addresses for external or untrusted users • Expands the number of internal IP addresses available to an organization • No possibility of conflict with IP addresses used by other companies and organizations ...
computer security - GH Raisoni Polytechnic, Nagpur
... only those individuals who have the Authority can view a piece of information. 2. Authentication: Authentication deals with the desire to ensure that an individual is who they claim to be. The need for this in an online transaction is obvious. 3. Integrity: Integrity is a related concept but deals w ...
... only those individuals who have the Authority can view a piece of information. 2. Authentication: Authentication deals with the desire to ensure that an individual is who they claim to be. The need for this in an online transaction is obvious. 3. Integrity: Integrity is a related concept but deals w ...