CATAPAN Global Brochure
... The CATAPAN Global Key Management System (KMS) is a unique off-the-shelf solution for full sovereign key generation and management. The KMS allows customers to control their own cryptographic keys for the CATAPAN Global devices. Full control of this process guarantees the sovereign capability of the ...
... The CATAPAN Global Key Management System (KMS) is a unique off-the-shelf solution for full sovereign key generation and management. The KMS allows customers to control their own cryptographic keys for the CATAPAN Global devices. Full control of this process guarantees the sovereign capability of the ...
Decision Support System
... and stored in the rule database of the SIEM. • Correlator engine is a software component that allows to detect specific attacks signatures (security event sequences) within the event flow received. ...
... and stored in the rule database of the SIEM. • Correlator engine is a software component that allows to detect specific attacks signatures (security event sequences) within the event flow received. ...
Unix Network Security - LSU Computer Science
... authorized person should be able to access the information. Integrity is being sure that information has not been changed while processing or communicating. Availability is obtaining resources only to authorized clients. Confidentiality, availability and integrity are the basic term and point to dif ...
... authorized person should be able to access the information. Integrity is being sure that information has not been changed while processing or communicating. Availability is obtaining resources only to authorized clients. Confidentiality, availability and integrity are the basic term and point to dif ...
Building an in-depth defense with Vectra and sandbox security
... Botnet monetization occurs when the attacker controls a host for the purposes of making money through internal activities such as Bitcoin mining or external activities such as advertising click fraud. The presence of botnet monetization behavior indicates this is not a targeted attack and allows an ...
... Botnet monetization occurs when the attacker controls a host for the purposes of making money through internal activities such as Bitcoin mining or external activities such as advertising click fraud. The presence of botnet monetization behavior indicates this is not a targeted attack and allows an ...
William Stallings, Cryptography and Network Security 3/e
... Trusted Computer Systems • information security is increasingly important • have varying degrees of sensitivity of information – eg. military info classifications: confidential, secret etc ...
... Trusted Computer Systems • information security is increasingly important • have varying degrees of sensitivity of information – eg. military info classifications: confidential, secret etc ...
2015/16 Cyber Security Survey Results
... This work is licensed under the Creative Commons Attribution 3.0 Australia Licence (CCBY 3.0). This licence allows you to copy, distribute and adapt this work, provided you attribute the work and do not suggest that APRA endorses you or your work. To view a full copy of the terms of this licence, vi ...
... This work is licensed under the Creative Commons Attribution 3.0 Australia Licence (CCBY 3.0). This licence allows you to copy, distribute and adapt this work, provided you attribute the work and do not suggest that APRA endorses you or your work. To view a full copy of the terms of this licence, vi ...
Hacking, Security, and Information War
... 1. What are some of the positives about TOR, the Dark Web, and Bitcoin (in general, for libraries)? 1. What are some of the negatives about TOR, the Dark Web, and Bitcoin (in general, for libraries)? 1. Should these technologies be regulated (eliminated)? Is it possible to regulate/eliminate these t ...
... 1. What are some of the positives about TOR, the Dark Web, and Bitcoin (in general, for libraries)? 1. What are some of the negatives about TOR, the Dark Web, and Bitcoin (in general, for libraries)? 1. Should these technologies be regulated (eliminated)? Is it possible to regulate/eliminate these t ...
Essentials of Security
... Benefits of Investing in Security Reduced downtime and costs associated with non-availability of systems and applications ...
... Benefits of Investing in Security Reduced downtime and costs associated with non-availability of systems and applications ...
Cyber Solutions for NEI 08-09 Whitepaper 119 KB
... Security Services and Solutions GE provides security consulting services to asset owners and operators in the nuclear sector. We also provide technical solutions designed and tested for the industrial controls environment. Our solutions are built with security in mind, and are readily integrated int ...
... Security Services and Solutions GE provides security consulting services to asset owners and operators in the nuclear sector. We also provide technical solutions designed and tested for the industrial controls environment. Our solutions are built with security in mind, and are readily integrated int ...
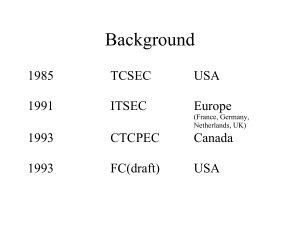
Common Criteria
... classes of network and system attacks, interoperability and compatibility with the defense-in-depth strategy, and IA solutions that should be considered to counter attacks. 5.2.21. Acquire IA solutions that have been evaluated using the Common Criteria Evaluation and Validation Scheme based on the N ...
... classes of network and system attacks, interoperability and compatibility with the defense-in-depth strategy, and IA solutions that should be considered to counter attacks. 5.2.21. Acquire IA solutions that have been evaluated using the Common Criteria Evaluation and Validation Scheme based on the N ...
Principals of Information Security, Fourth Edition
... enforcement agencies with broader latitude in order to combat terrorism-related activities • USA PATRIOT Improvement and Reauthorization Act: Made permanent fourteen of the sixteen expanded powers of the Department of Homeland Security and the FBI in investigating terrorist activity • Computer Secur ...
... enforcement agencies with broader latitude in order to combat terrorism-related activities • USA PATRIOT Improvement and Reauthorization Act: Made permanent fourteen of the sixteen expanded powers of the Department of Homeland Security and the FBI in investigating terrorist activity • Computer Secur ...
Guide to Security - Cal Poly Pomona Foundation, Inc.
... – Record held by the anti-virus package that helps identify known viruses when they attempt to strike – Can prompt users to periodically collect new data ...
... – Record held by the anti-virus package that helps identify known viruses when they attempt to strike – Can prompt users to periodically collect new data ...
Jaden Terry CIS 280 Final Network Security From browsing the
... viruses etc. According to Wikipedia, a hacker is defined as, “Someone who seeks and exploits weaknesses in a computer system or computer network.” Some evil hackers may insert a virus or malware that could make a computer unusable. From hackers and viruses, to network privacy, the security of our ne ...
... viruses etc. According to Wikipedia, a hacker is defined as, “Someone who seeks and exploits weaknesses in a computer system or computer network.” Some evil hackers may insert a virus or malware that could make a computer unusable. From hackers and viruses, to network privacy, the security of our ne ...
PCI Compliance - Aug 2009 - Commonwealth Business Travel
... the following individual data elements may be retained subsequent to transaction authorization: Cardholder Account Number Cardholder Name ...
... the following individual data elements may be retained subsequent to transaction authorization: Cardholder Account Number Cardholder Name ...
AccessControlSimulation
... systems used to process tax and financial information did not fully prevent access by unauthorized users or excessive levels of access for authorized users. ...
... systems used to process tax and financial information did not fully prevent access by unauthorized users or excessive levels of access for authorized users. ...
IBM Security QRadar Incident Forensics
... terms and conditions of the agreements under which they are provided. The client is responsible for ensuring compliance with laws and regulations applicable to it. IBM does not provide legal advice or represent or warrant that its services or products will ensure that the client is in compliance w ...
... terms and conditions of the agreements under which they are provided. The client is responsible for ensuring compliance with laws and regulations applicable to it. IBM does not provide legal advice or represent or warrant that its services or products will ensure that the client is in compliance w ...
Ch10aProtectionMechanisms
... • Trace – A process by which the organization attempts to determine the identity of someone discovered in unauthorized areas of the network or systems ...
... • Trace – A process by which the organization attempts to determine the identity of someone discovered in unauthorized areas of the network or systems ...
Digital Billboard Security Guidelines
... something you are. Some current implementations include the use of a password with one of the following second methods: a hardware token generator, a service that sends a code to your mobile phone, or a biometric device to read fingerprints. Patch Management: A process (manual or automated) to apply ...
... something you are. Some current implementations include the use of a password with one of the following second methods: a hardware token generator, a service that sends a code to your mobile phone, or a biometric device to read fingerprints. Patch Management: A process (manual or automated) to apply ...