CIS 100 Emerge Terms: Exam #3 Bluetooth: enables digital devices
... Cloud Computing: delivers a variety of computing resources from the Internet as a service for free or for a fee, to relieve users from the burden of installing, maintaining, and securing those resources themselves. Cloud Services include computing services provided over the Internet in three categor ...
... Cloud Computing: delivers a variety of computing resources from the Internet as a service for free or for a fee, to relieve users from the burden of installing, maintaining, and securing those resources themselves. Cloud Services include computing services provided over the Internet in three categor ...
PowerPoint - 6S Global
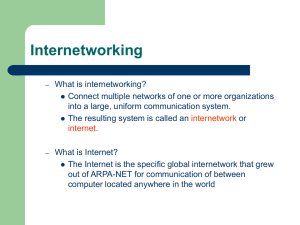
... When the network devices are connected to each other over the Internet, they do not get connected automatically ...
... When the network devices are connected to each other over the Internet, they do not get connected automatically ...
ppt - Carnegie Mellon School of Computer Science
... Different chunks for geographical addressing, the IPv4 address space, Perhaps help clean up the routing tables - just use one huge chunk per ISP and one huge chunk per customer. ...
... Different chunks for geographical addressing, the IPv4 address space, Perhaps help clean up the routing tables - just use one huge chunk per ISP and one huge chunk per customer. ...
Week-10.3-2
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
No Slide Title - Ed Lazowska
... Using TCP/IP and lower layers, we can get multipacket messages delivered reliably from address space A on machine B to address space C on machine D, where machines B and D are many heterogeneous network hops apart, without knowing any of the ...
... Using TCP/IP and lower layers, we can get multipacket messages delivered reliably from address space A on machine B to address space C on machine D, where machines B and D are many heterogeneous network hops apart, without knowing any of the ...
presentation source
... IPFWADM (Firewall) • Manages Permit/Deny Firewall Access Lists • Controls which networks are allowed to IP Masquerade • Deny access to all other networks. ...
... IPFWADM (Firewall) • Manages Permit/Deny Firewall Access Lists • Controls which networks are allowed to IP Masquerade • Deny access to all other networks. ...
Document
... • IP network addresses must be unique, or the Internet will not be stable • The Internet Network Information Centre (InterNIC) was originally responsible for issuing Internet network addresses • Today, the Internet Assigned Number Authority (IANA) issues network addresses to Information Service Prov ...
... • IP network addresses must be unique, or the Internet will not be stable • The Internet Network Information Centre (InterNIC) was originally responsible for issuing Internet network addresses • Today, the Internet Assigned Number Authority (IANA) issues network addresses to Information Service Prov ...
Session2
... MAC Address- Media Access Control address is a unique identifier assigned to most network adapters or network interface cards (NICs) by the manufacturer… ...
... MAC Address- Media Access Control address is a unique identifier assigned to most network adapters or network interface cards (NICs) by the manufacturer… ...
Computer network
... Types of Networks • Various configurations, called topologies, have been used to administer LANs – Ring topology A configuration that connects all nodes in a closed loop on which messages travel in ...
... Types of Networks • Various configurations, called topologies, have been used to administer LANs – Ring topology A configuration that connects all nodes in a closed loop on which messages travel in ...
Networks Local area network
... it makes sense for them all to be connected. • In this way the office can have a single printer and all ten people can print to it. • In a similar way other devices such as ...
... it makes sense for them all to be connected. • In this way the office can have a single printer and all ten people can print to it. • In a similar way other devices such as ...
Document - Oman College of Management & Technology
... checksum are compared. Mismatch means there is transmission errors occurred. ...
... checksum are compared. Mismatch means there is transmission errors occurred. ...
Understanding the Internet`s Underlying Architecture
... Hubs: Link groups of computers together Bridges: Link Local Area Networks (LAN) Gateways: Similar to bridges but translate data from one type to another Repeaters: Amplify data signals for long distance transmission Routers: Transmit data packets between two different networks ...
... Hubs: Link groups of computers together Bridges: Link Local Area Networks (LAN) Gateways: Similar to bridges but translate data from one type to another Repeaters: Amplify data signals for long distance transmission Routers: Transmit data packets between two different networks ...
Document
... • To improve the efficiency of transferring information over a shared communication line, messages are divided into fixedsized, numbered packets • Network devices called routers are used to direct packets between networks Figure 15.4 Messages sent by packet switching ...
... • To improve the efficiency of transferring information over a shared communication line, messages are divided into fixedsized, numbered packets • Network devices called routers are used to direct packets between networks Figure 15.4 Messages sent by packet switching ...
The Internet and Security
... Specialized for filtering without routing duties Usually easier to configure, have auditing, logging, auditing Can use for privacy to hide internal network addresses Many firewalls can maintain state, i.e. maintain virtual sessions for UDP and close port when connection closes • Some firewalls can l ...
... Specialized for filtering without routing duties Usually easier to configure, have auditing, logging, auditing Can use for privacy to hide internal network addresses Many firewalls can maintain state, i.e. maintain virtual sessions for UDP and close port when connection closes • Some firewalls can l ...
Review of IP protocol
... echo and echo reply timestamp and timestamp reply address mask request and reply ...
... echo and echo reply timestamp and timestamp reply address mask request and reply ...
Chapter 13
... – No longer supported by Microsoft • XP does not install NetBEUI by default, but the protocol can be added from the installation CD. ...
... – No longer supported by Microsoft • XP does not install NetBEUI by default, but the protocol can be added from the installation CD. ...
ITS CSS Desktop Support
... Nodes within a network are assigned an IP address. IP acts as a transport layer for other network protocols (ICMP, TCP, UDP) ...
... Nodes within a network are assigned an IP address. IP acts as a transport layer for other network protocols (ICMP, TCP, UDP) ...
Network hunt - Barefoot Computing
... together so they can ‘talk’ to each other by exchanging data. The data travels along the cables which come out of this device. ...
... together so they can ‘talk’ to each other by exchanging data. The data travels along the cables which come out of this device. ...
04The Internet - Computer Science
... A characteristic of a heterarchical network is that it is a robust network. If some nodes are removed, data can still be sent between nodes Q10: Hierarchical networks do not lend themselves to robustness. Why? ...
... A characteristic of a heterarchical network is that it is a robust network. If some nodes are removed, data can still be sent between nodes Q10: Hierarchical networks do not lend themselves to robustness. Why? ...
SOHO Network Administration
... system will search that network for a DHCP server. When the program finds such device, your computer will request a temporary IP address from the DHCP server. The IP address is loaned to you while you are connected to the LAN. When you disconnect, that IP address becomes available, and the DHCP serv ...
... system will search that network for a DHCP server. When the program finds such device, your computer will request a temporary IP address from the DHCP server. The IP address is loaned to you while you are connected to the LAN. When you disconnect, that IP address becomes available, and the DHCP serv ...
Kuliah Komunikasi Data
... specifying functions of the physical layer and the data link layer of major LAN protocols. ...
... specifying functions of the physical layer and the data link layer of major LAN protocols. ...