Introducing the Specifications of the MEF
... – Over the same “shared” MEN access/backbone links. – Allow certain traffic be delivered with strict SLAs (Service Level Agreements), – Allow other traffic to be delivered best efforts. • Critical SLA Service Attributes – Bandwidth Profile – Service Performance • Allows bandwidth to exceed commitmen ...
... – Over the same “shared” MEN access/backbone links. – Allow certain traffic be delivered with strict SLAs (Service Level Agreements), – Allow other traffic to be delivered best efforts. • Critical SLA Service Attributes – Bandwidth Profile – Service Performance • Allows bandwidth to exceed commitmen ...
Stateless Addr. Autoconfiguration
... An address for a set of interfaces (in a given scope) that typically belong to different nodes. IPv6 multicast addresses are used instead of broadcast addresses in IPv4. ...
... An address for a set of interfaces (in a given scope) that typically belong to different nodes. IPv6 multicast addresses are used instead of broadcast addresses in IPv4. ...
Alcatel-Lucent Interior Routing Protocols and High
... Different subnet masks per network Routing protocols must advertise the subnet mask with updates. High-order bits are not reusable. Routing decisions are made based on the longest match. A more efficient use of IP addressing than basic subnetting Requires a good understanding of subnetti ...
... Different subnet masks per network Routing protocols must advertise the subnet mask with updates. High-order bits are not reusable. Routing decisions are made based on the longest match. A more efficient use of IP addressing than basic subnetting Requires a good understanding of subnetti ...
Alcatel-Lucent Interior Routing Protocols and High
... Different subnet masks per network Routing protocols must advertise the subnet mask with updates. High-order bits are not reusable. Routing decisions are made based on the longest match. A more efficient use of IP addressing than basic subnetting Requires a good understanding of subnetti ...
... Different subnet masks per network Routing protocols must advertise the subnet mask with updates. High-order bits are not reusable. Routing decisions are made based on the longest match. A more efficient use of IP addressing than basic subnetting Requires a good understanding of subnetti ...
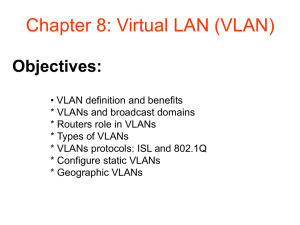
Chapter 8: Virtual LAN (VLAN)
... All workstations and servers used by a particular workgroup share the same VLAN, regardless of the physical connection or location. ...
... All workstations and servers used by a particular workgroup share the same VLAN, regardless of the physical connection or location. ...
TL1 History - ManageEngine
... SNMP has emerged as a popular protocol for managing data centric NEs. Like CMIP, SNMP is a machine-to-machine language. SNMP as the name implies is based on simple get-set messaging. With this simplicity comes lack of sophisticated operations capabilities. SNMP dominates the IP domain and is popular ...
... SNMP has emerged as a popular protocol for managing data centric NEs. Like CMIP, SNMP is a machine-to-machine language. SNMP as the name implies is based on simple get-set messaging. With this simplicity comes lack of sophisticated operations capabilities. SNMP dominates the IP domain and is popular ...
ICMP.pptx
... quench message Ideally, such a message should be sent before a router is forced to drop packets Senders reduce transmission rate upon receipt of a source quench message ...
... quench message Ideally, such a message should be sent before a router is forced to drop packets Senders reduce transmission rate upon receipt of a source quench message ...
IPv6 and Transition Mechanisms
... – BIS (Bump in the Stack) - At the Transport Layer – BIA (Bump in the API) - At the Application Layer IPv6 Transition Mechanisms - 6DISS Workshop - 5 March 2006 ...
... – BIS (Bump in the Stack) - At the Transport Layer – BIA (Bump in the API) - At the Application Layer IPv6 Transition Mechanisms - 6DISS Workshop - 5 March 2006 ...
FRITZ!WLAN USB Stick AC 860
... FRITZ!WLAN USB Stick AC 860 at a Glance The FRITZ!WLAN USB Stick connects your computer with a FRITZ!Box or another wireless access point via wireless LAN. The wireless connection provides the computer with access to the Internet. The FRITZ!WLAN USB Stick can also connect your computer directly with ...
... FRITZ!WLAN USB Stick AC 860 at a Glance The FRITZ!WLAN USB Stick connects your computer with a FRITZ!Box or another wireless access point via wireless LAN. The wireless connection provides the computer with access to the Internet. The FRITZ!WLAN USB Stick can also connect your computer directly with ...
Wireless Application Development Issues
... This document begins by profiling the key players in the wireless world. The issues facing these players help set the stage for discussions and recommendations that follow. Next we describe the paging infrastructure in some detail. Many application developers are prone to believe that the infrastruc ...
... This document begins by profiling the key players in the wireless world. The issues facing these players help set the stage for discussions and recommendations that follow. Next we describe the paging infrastructure in some detail. Many application developers are prone to believe that the infrastruc ...
3346 Software User Guide V6.3
... Copyright © 2003 Netopia, Inc. All rights reserved, Printed in the USA. The information in this document is subject to change without notice. The statements, configurations, technical data, and recommendations in this document are believed to be accurate and reliable, but are presented without expre ...
... Copyright © 2003 Netopia, Inc. All rights reserved, Printed in the USA. The information in this document is subject to change without notice. The statements, configurations, technical data, and recommendations in this document are believed to be accurate and reliable, but are presented without expre ...
Cisco IP SLA`s
... • Service Provider needs visibility in the Customer Edge, in order to commit to SLAs • Enterprise will verify SP SLAs by using access router edge to edge measurements Enterprise may provide restricted Simple Network Management Protocol (SNMP) (RTT, Latency, QoS) visibility into Access router for Ser ...
... • Service Provider needs visibility in the Customer Edge, in order to commit to SLAs • Enterprise will verify SP SLAs by using access router edge to edge measurements Enterprise may provide restricted Simple Network Management Protocol (SNMP) (RTT, Latency, QoS) visibility into Access router for Ser ...
Compatible Systems Reference Guides
... program which is located in the Network Management/CompatiView/Windows directory on the CD-ROM. The program will install CompatiView and its associated files on the drive you specify. System Requirements for Windows CompatiView for Windows requires a 486 machine or faster, running Microsoft Windows ...
... program which is located in the Network Management/CompatiView/Windows directory on the CD-ROM. The program will install CompatiView and its associated files on the drive you specify. System Requirements for Windows CompatiView for Windows requires a 486 machine or faster, running Microsoft Windows ...
Multi-Area OSPF
... • Type 1 LSAs are referred to as the router link entries • Type 2 LSAs are referred to as the network link entries and are flooded by a DR • Type 3 LSAs are referred to as the summary link entries and are created and propagated by ...
... • Type 1 LSAs are referred to as the router link entries • Type 2 LSAs are referred to as the network link entries and are flooded by a DR • Type 3 LSAs are referred to as the summary link entries and are created and propagated by ...
DSL-504T ADSL Router User’s Guide
... product in question has not been returned to a D-Link office, then a proof of purchase (such as a copy of the dated purchase invoice) must be provided when requesting warranty service. The term "purchase" in this software warranty refers to the purchase transaction and resulting license to use such ...
... product in question has not been returned to a D-Link office, then a proof of purchase (such as a copy of the dated purchase invoice) must be provided when requesting warranty service. The term "purchase" in this software warranty refers to the purchase transaction and resulting license to use such ...
BSG 8ew 1.0 Solution Guide
... network and involve several components. The components involved in the architecture are the Communication Servers (CS2000), Media Gateways, Signaling Gateways, and CPE devices. They are interconnected through the Managed IP network that can be viewed as a core network that is managed by the service ...
... network and involve several components. The components involved in the architecture are the Communication Servers (CS2000), Media Gateways, Signaling Gateways, and CPE devices. They are interconnected through the Managed IP network that can be viewed as a core network that is managed by the service ...
Reference Manual for the MR814v2 Cable/DSL Wireless Router
... Advanced Configuration of the Router Configuring for Port Forwarding to Local Servers ..........................................................6-1 Adding a Custom Service .........................................................................................6-2 Editing or Deleting a Port Forwardi ...
... Advanced Configuration of the Router Configuring for Port Forwarding to Local Servers ..........................................................6-1 Adding a Custom Service .........................................................................................6-2 Editing or Deleting a Port Forwardi ...
ns-3 tutorial
... ## Set up some default values for the simulation. Use the Bind() ## technique to tell the system what subclass of Queue to use, ## and what the queue limit is ## The below Bind command tells the queue factory which class to ## instantiate, when the queue factory is invoked in the topology code ns.De ...
... ## Set up some default values for the simulation. Use the Bind() ## technique to tell the system what subclass of Queue to use, ## and what the queue limit is ## The below Bind command tells the queue factory which class to ## instantiate, when the queue factory is invoked in the topology code ns.De ...
“Computers in Communication” by Gordon Brebner
... The recommended way to use the book is to read the five parts in this order, that is, to read the book from beginning to end. Forward and backward cross-references in the text have been designed to be optimal for a sequential reader. However, some readers might want to vary the order, either because ...
... The recommended way to use the book is to read the five parts in this order, that is, to read the book from beginning to end. Forward and backward cross-references in the text have been designed to be optimal for a sequential reader. However, some readers might want to vary the order, either because ...
ccna3-mod4-SwitchingConcept
... • Listens to the network’s shared media to see if any other users on “on the line” by trying to sense a neutral electrical signal or carrier. • If no transmission is sensed, then multiple access allows anyone onto the media without any further permission required. • If two PCs detect a neutral signa ...
... • Listens to the network’s shared media to see if any other users on “on the line” by trying to sense a neutral electrical signal or carrier. • If no transmission is sensed, then multiple access allows anyone onto the media without any further permission required. • If two PCs detect a neutral signa ...
Deploying the Dell Force10 MXL into a Cisco Nexus Network
... Uplink configuration for the MXL will generally be done in one of two ways in a Cisco Nexus network environment: running PVST with discreet LAGs connected to separate top-of-rack switches as covered in Trunk Port Uplink Configuration with Per-VLAN Spanning Tree and running PVST with a single LAG con ...
... Uplink configuration for the MXL will generally be done in one of two ways in a Cisco Nexus network environment: running PVST with discreet LAGs connected to separate top-of-rack switches as covered in Trunk Port Uplink Configuration with Per-VLAN Spanning Tree and running PVST with a single LAG con ...
TCP Fairness Issues
... and receivers. – ECN-compliant TCP senders initiate their congestion avoidance algorithm after receiving marked ACK packets from the TCP receiver – A RED extension that marks packets to signal congestion ...
... and receivers. – ECN-compliant TCP senders initiate their congestion avoidance algorithm after receiving marked ACK packets from the TCP receiver – A RED extension that marks packets to signal congestion ...
User Guide Linksys E-Series Routers
... How to optimize your router for gaming and voice . . . . . . . . How to remotely change your router settings . . . . . . . . . . . How to enable Voice over IP on your network . . . . . . . . . . . How to configure UPnP . . . . . . . . . . . . . . . . . . ...
... How to optimize your router for gaming and voice . . . . . . . . How to remotely change your router settings . . . . . . . . . . . How to enable Voice over IP on your network . . . . . . . . . . . How to configure UPnP . . . . . . . . . . . . . . . . . . ...