TS 102 470-1
... specific field of broadcasting and related fields. Since 1995 the JTC Broadcast became a tripartite body by including in the Memorandum of Understanding also CENELEC, which is responsible for the standardization of radio and television receivers. The EBU is a professional association of broadcasting ...
... specific field of broadcasting and related fields. Since 1995 the JTC Broadcast became a tripartite body by including in the Memorandum of Understanding also CENELEC, which is responsible for the standardization of radio and television receivers. The EBU is a professional association of broadcasting ...
Multicasting
... (DR), is a router that agrees to cache copies of the data and process acknowledgements from routers and hosts further down the forwarding tree. If a retransmission is need it is taken from the routers cache. This occurs when the host or router send a NACK. The NACK will propogate up the tree until a ...
... (DR), is a router that agrees to cache copies of the data and process acknowledgements from routers and hosts further down the forwarding tree. If a retransmission is need it is taken from the routers cache. This occurs when the host or router send a NACK. The NACK will propogate up the tree until a ...
Routing Theory Part 2
... Network Discovery with Split Horizon - First Round of Updates RTB’s routing update sent out serial 0 to RTA Includes the network 10.1.3.0/24 which RTA can reach via 10.1.2.2. Split horizon: Does not include the 10.1.2.0/24 network. Split horizon blocks the 10.1.2.0/24 update from being sent to R ...
... Network Discovery with Split Horizon - First Round of Updates RTB’s routing update sent out serial 0 to RTA Includes the network 10.1.3.0/24 which RTA can reach via 10.1.2.2. Split horizon: Does not include the 10.1.2.0/24 network. Split horizon blocks the 10.1.2.0/24 update from being sent to R ...
Cisco Industrial Ethernet 3000 Layer 2/Layer 3 Series Switches Data
... ● IEEE 802.1x with VLAN assignment, guest VLAN, and voice VLAN allows dynamic port-based security, providing user authentication. ● Port-based ACLs for Layer 2 interfaces allow application of security policies on individual switch ports. ● MAC address filtering prevents the forwarding of any type of ...
... ● IEEE 802.1x with VLAN assignment, guest VLAN, and voice VLAN allows dynamic port-based security, providing user authentication. ● Port-based ACLs for Layer 2 interfaces allow application of security policies on individual switch ports. ● MAC address filtering prevents the forwarding of any type of ...
Release Notes for Catalyst 3850 Series Switch, Cisco IOS XE
... attribute information present in the redirect URL to send the login page based on the AP location or SSID or the client mac address. The commands to configure this feature are given below: ...
... attribute information present in the redirect URL to send the login page based on the AP location or SSID or the client mac address. The commands to configure this feature are given below: ...
Lenovo Network Application Guide for Lenovo Cloud Network
... © Copyright Lenovo 2016 Portions © Copyright IBM Corporation 2014. LIMITED AND RESTRICTED RIGHTS NOTICE: If data or software is delivered pursuant a General Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Len ...
... © Copyright Lenovo 2016 Portions © Copyright IBM Corporation 2014. LIMITED AND RESTRICTED RIGHTS NOTICE: If data or software is delivered pursuant a General Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Len ...
PDF - Complete Book (2.54 MB)
... gateway for the device. You can also use this command to transfer a Cisco software image to a device when the device is in boot mode. In boot mode, IP routing is not enabled on the device. Unlike the ip default-gateway command, the ip default-network command can be used when IP routing is enabled on ...
... gateway for the device. You can also use this command to transfer a Cisco software image to a device when the device is in boot mode. In boot mode, IP routing is not enabled on the device. Unlike the ip default-gateway command, the ip default-network command can be used when IP routing is enabled on ...
Overlay Network
... • An overlay socket (OL Socket) is an endpoint for communication in an overlay network • An overlay socket provides application programs an interface for communications over an overlay network • The application programming interface (API) of an OL Socket offers applications the ability to • create o ...
... • An overlay socket (OL Socket) is an endpoint for communication in an overlay network • An overlay socket provides application programs an interface for communications over an overlay network • The application programming interface (API) of an OL Socket offers applications the ability to • create o ...
Nortel Networks L2/3 Ethernet Switch Module for
... This information was developed for products and services offered in the U.S.A. IBM may not offer the products, services, or features discussed in this document in other countries. Consult your local IBM representative for information on the products and services currently available in your area. Any ...
... This information was developed for products and services offered in the U.S.A. IBM may not offer the products, services, or features discussed in this document in other countries. Consult your local IBM representative for information on the products and services currently available in your area. Any ...
Observer - Optrics Engineering
... Network Instruments will (1) repair the product at no charge, using new or refurbished replacement parts, or (2) exchange the product with a product that is new or which has been manufactured from new or serviceable used parts and is at least functionally equivalent to the original product. A replac ...
... Network Instruments will (1) repair the product at no charge, using new or refurbished replacement parts, or (2) exchange the product with a product that is new or which has been manufactured from new or serviceable used parts and is at least functionally equivalent to the original product. A replac ...
PDF - This Chapter (378.0 KB)
... router hostname, the router uses the factory-assigned default hostname “Router.” Do not expect capitalization and lower casing to be preserved in the hostname. Uppercase and lowercase characters are treated as identical by many Internet software applications. It may seem appropriate to capitalize a ...
... router hostname, the router uses the factory-assigned default hostname “Router.” Do not expect capitalization and lower casing to be preserved in the hostname. Uppercase and lowercase characters are treated as identical by many Internet software applications. It may seem appropriate to capitalize a ...
PPT source - IIT Bombay
... Spread spectrum technology Problem of radio transmission: frequency dependent fading can wipe out narrow band signals for duration of the interference Solution: spread the narrow band signal into a broad band signal using a special code - protection against narrow band interference ...
... Spread spectrum technology Problem of radio transmission: frequency dependent fading can wipe out narrow band signals for duration of the interference Solution: spread the narrow band signal into a broad band signal using a special code - protection against narrow band interference ...
21-05-0298-01-0000-Section5-Draft1
... service adaptation to varying quality of service, battery life conservation, and network discovery and link selection. In a system containing heterogeneous network interfaces of 802 types and cellular 3GPP, 3GPP2 types, the Media Independent Handover Function can help the L3MP to implement effective ...
... service adaptation to varying quality of service, battery life conservation, and network discovery and link selection. In a system containing heterogeneous network interfaces of 802 types and cellular 3GPP, 3GPP2 types, the Media Independent Handover Function can help the L3MP to implement effective ...
Apuntes seguridad Redes Avanzadas 0708
... mainly as a result of service provider policies and network limitations. Only in the context of intradomain multicast [8] the Sparse Mode (SM) [7] and the SSM variant of PIM (PIM-SM and PIMSSM, respectively) have been deployed. The problem for inter domain multicast deployment is similar to that of ...
... mainly as a result of service provider policies and network limitations. Only in the context of intradomain multicast [8] the Sparse Mode (SM) [7] and the SSM variant of PIM (PIM-SM and PIMSSM, respectively) have been deployed. The problem for inter domain multicast deployment is similar to that of ...
Implementing IPv6 in a Production Network
... multicast address is delivered to every interface in a group. The IPv6 difference is that, instead of annoying every single host on the segment with broadcast blather. Only hosts who are members of the multicast group receive the multicast packets. IPv6 multicast is routable, and routers will not fo ...
... multicast address is delivered to every interface in a group. The IPv6 difference is that, instead of annoying every single host on the segment with broadcast blather. Only hosts who are members of the multicast group receive the multicast packets. IPv6 multicast is routable, and routers will not fo ...
Wireless Networking Technologies
... Time and frequency multiplex Combination of both methods A channel gets a certain frequency band for a certain amount of time k1 k2 k3 k4 k5 k6 Example: GSM Advantages: c – better protection against tapping – protection against frequency selective interference – higher data rates compar ...
... Time and frequency multiplex Combination of both methods A channel gets a certain frequency band for a certain amount of time k1 k2 k3 k4 k5 k6 Example: GSM Advantages: c – better protection against tapping – protection against frequency selective interference – higher data rates compar ...
IBM BladeCenter iSCSI SAN Solution
... © Copyright International Business Machines Corporation 2006. All rights reserved. Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule ...
... © Copyright International Business Machines Corporation 2006. All rights reserved. Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule ...
Dynamics of Hot-Potato Routing in IP Networks
... making performance dependent on the routing behavior in multiple domains. In the large ASes at the core of the Internet, routers forward packets based on information from both the intradomain and interdomain routing protocols. These networks use the Border Gateway Protocol (BGP) [1] to exchange rout ...
... making performance dependent on the routing behavior in multiple domains. In the large ASes at the core of the Internet, routers forward packets based on information from both the intradomain and interdomain routing protocols. These networks use the Border Gateway Protocol (BGP) [1] to exchange rout ...
20070227-P2PSIP
... SIP is already ready for P2P with little changes Uses symmetric, direct client-to-client communication Intelligence resides mostly on the network border in the user agents The proxies and the registrar only perform lookup and routing All that user agents lack to build a P2P network is lookup ...
... SIP is already ready for P2P with little changes Uses symmetric, direct client-to-client communication Intelligence resides mostly on the network border in the user agents The proxies and the registrar only perform lookup and routing All that user agents lack to build a P2P network is lookup ...
BIG-IP Global Traffic Manager | F5 Datasheet
... Disaster recovery/business continuity planning In addition to performing comprehensive site availability checks, you can define the conditions for shifting all traffic to a backup data center, failing over an entire site, or controlling only the affected applications. ...
... Disaster recovery/business continuity planning In addition to performing comprehensive site availability checks, you can define the conditions for shifting all traffic to a backup data center, failing over an entire site, or controlling only the affected applications. ...
Total Access 850 System Manual
... ( ) I have responsibility for the operation and maintenance of the terminal equipment to be connected to 1.544 Mbps and/or ________ subrate digital services. The terminal equipment to be connected complies with Part 68 of the FCC rules except for the encoded analog content and billing protection spe ...
... ( ) I have responsibility for the operation and maintenance of the terminal equipment to be connected to 1.544 Mbps and/or ________ subrate digital services. The terminal equipment to be connected complies with Part 68 of the FCC rules except for the encoded analog content and billing protection spe ...
PDF
... 802.1x MAC Auth Bypass (Including MAB with voice VLAN): The 802.1x protocol has three entities: client (supplicant), authenticator, and authentication server. Typically, the host PC runs the supplicant software and tries to authenticate itself by sending its credentials to the authenticator, which i ...
... 802.1x MAC Auth Bypass (Including MAB with voice VLAN): The 802.1x protocol has three entities: client (supplicant), authenticator, and authentication server. Typically, the host PC runs the supplicant software and tries to authenticate itself by sending its credentials to the authenticator, which i ...
Multicast - Virginia Tech
... •A host running an application that has joined 225.0.1.1 Ethernet address 01:00:5E:00:01:01. Packet will be discarded by perfect filtering in IP layer •A host running an application that has joined some multicast group which the Ethernet address produces the same hash value as 01:00:5E:00:01:01. P ...
... •A host running an application that has joined 225.0.1.1 Ethernet address 01:00:5E:00:01:01. Packet will be discarded by perfect filtering in IP layer •A host running an application that has joined some multicast group which the Ethernet address produces the same hash value as 01:00:5E:00:01:01. P ...
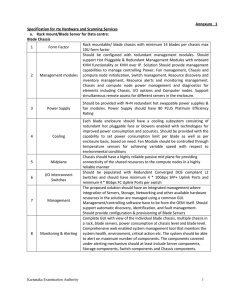
Annexure 1
... 1 client network and across all the controllers in the cluster. SAN: The backend SAN storage should be provided with dual controllers in Active-Active mode. Each controller should be with Single/Dual CPU 4-cores or above. The controller pair should not be more than 2U form factor. The controller pai ...
... 1 client network and across all the controllers in the cluster. SAN: The backend SAN storage should be provided with dual controllers in Active-Active mode. Each controller should be with Single/Dual CPU 4-cores or above. The controller pair should not be more than 2U form factor. The controller pai ...