Cisco CCNA Study Guide
... A LAN is generally a high-speed network that covers a small geographic area, usually contained within a single building or campus. A LAN is usually under the administrative control of a single organization. Ethernet is the most common LAN technology. A WAN can be defined one of two ways. The book de ...
... A LAN is generally a high-speed network that covers a small geographic area, usually contained within a single building or campus. A LAN is usually under the administrative control of a single organization. Ethernet is the most common LAN technology. A WAN can be defined one of two ways. The book de ...
iptables-1-updated
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
Cisco Catalyst 2960-S and 2960 Series Switches with
... addresses primary IT and business challenges to help create a truly borderless experience by bringing interactions closer to the employee and customer. Borderless experience is only possible with intelligent network elements designed and architected to meet the needs of a global workspace. Cisco Net ...
... addresses primary IT and business challenges to help create a truly borderless experience by bringing interactions closer to the employee and customer. Borderless experience is only possible with intelligent network elements designed and architected to meet the needs of a global workspace. Cisco Net ...
Unix System Administration
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
Dave`s AusNOG 02 talk - Locator/ID Separation Protocol
... the DFZ, and points the prefix at the ETR doing the translation; standard NAT stuff here… • The translating ETR is configured as follows: – ip lisp etr – ip lisp database-mapping 153.16.10.0/24 128.223.156.134 priority 1 weight 100 – ip lisp translate inside 153.16.10.5 outside ...
... the DFZ, and points the prefix at the ETR doing the translation; standard NAT stuff here… • The translating ETR is configured as follows: – ip lisp etr – ip lisp database-mapping 153.16.10.0/24 128.223.156.134 priority 1 weight 100 – ip lisp translate inside 153.16.10.5 outside ...
ESBC Administrator`s Guide
... GETTING STARTED WITH THE ESBC .............................................................................................13 ...
... GETTING STARTED WITH THE ESBC .............................................................................................13 ...
Hack Attacks Revealed
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
Hack Attacks Revealed
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
N450 WiFi Cable Modem Router N450/CG2000Dv2 User Manual
... The modem router lets you access your network anywhere within the operating range of your wireless network. However, the operating distance or range of your wireless connection can vary significantly depending on the physical placement of your modem router. For example, the thickness and number of w ...
... The modem router lets you access your network anywhere within the operating range of your wireless network. However, the operating distance or range of your wireless connection can vary significantly depending on the physical placement of your modem router. For example, the thickness and number of w ...
Flex System Fabric CN4093 10Gb Converged
... RADIUS Authentication Features in IBM Networking OS . Switch User Accounts . . . . . . . . . . . . . . . RADIUS Attributes for IBM Networking OS User Privileges ...
... RADIUS Authentication Features in IBM Networking OS . Switch User Accounts . . . . . . . . . . . . . . . RADIUS Attributes for IBM Networking OS User Privileges ...
Diapositive 1
... 100G deployment: green field Green field deployment: new WDM network based on 100G only High capacity backbone network Capacity per fiber pair increases by a factor 10 compared to 10G design ...
... 100G deployment: green field Green field deployment: new WDM network based on 100G only High capacity backbone network Capacity per fiber pair increases by a factor 10 compared to 10G design ...
APNIC Tutorial: IPv6 Essentials
... discovery process [Path MTU Discovery] to determine most optimum MTU size before creating end to end session • In this discovery process, the source IPv6 device attempts to send a packet at the size specified by the upper IP layers [i.e TCP/Application]. • If the device receives an ICMP packet to ...
... discovery process [Path MTU Discovery] to determine most optimum MTU size before creating end to end session • In this discovery process, the source IPv6 device attempts to send a packet at the size specified by the upper IP layers [i.e TCP/Application]. • If the device receives an ICMP packet to ...
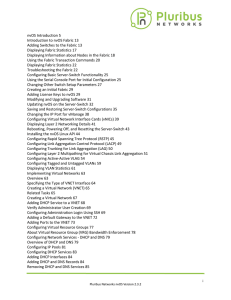
nvOS Introduction 5 Introduction to nvOS Fabric
... Pluribus Netvisor uses the concept of Fabric-Cluster to describe the interconnectivity of devices into a single logical network. The concept of a virtual network (VNET) describes is a “slice” of resources that apply to a single entity with assigned resources within the fabric. The VNET contains serv ...
... Pluribus Netvisor uses the concept of Fabric-Cluster to describe the interconnectivity of devices into a single logical network. The concept of a virtual network (VNET) describes is a “slice” of resources that apply to a single entity with assigned resources within the fabric. The VNET contains serv ...
Juniper / Cisco Interoperability Cookbook
... This configuration guide is intended for any network architect, administrator, or engineer who needs to interconnect Juniper and Cisco Ethernet switches. This document assumes familiarity with basic Ethernet and TCP/IP networking concepts, as well as at least limited experience with the Juniper and ...
... This configuration guide is intended for any network architect, administrator, or engineer who needs to interconnect Juniper and Cisco Ethernet switches. This document assumes familiarity with basic Ethernet and TCP/IP networking concepts, as well as at least limited experience with the Juniper and ...
Configuring QSFP+ Ports . . . . . . . . . . . . . . . . . . . . . . . 152
... © Copyright Lenovo 2015 Portions © Copyright IBM Corporation 2014. LIMITED AND RESTRICTED RIGHTS NOTICE: If data or software is delivered pursuant a General Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Len ...
... © Copyright Lenovo 2015 Portions © Copyright IBM Corporation 2014. LIMITED AND RESTRICTED RIGHTS NOTICE: If data or software is delivered pursuant a General Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Len ...
N150 Wireless ADSL2+ Modem Router DGN1000 User
... service providers, lets you block unsafe Internet content and applications, and protects the devices (PCs, gaming consoles, and so on) that you connect to your home network. If you have not already set up your new router using the installation guide that comes in the box, this chapter walks you thro ...
... service providers, lets you block unsafe Internet content and applications, and protects the devices (PCs, gaming consoles, and so on) that you connect to your home network. If you have not already set up your new router using the installation guide that comes in the box, this chapter walks you thro ...
Unix System Administration
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
... • Source and stateful routing and failover functions Route traffic more efficiant and faster than regular IP routers. ...
LevelOne
... network printing solutions for various common network operating systems such as Windows 98SE/ME/2000/XP, NetWare, Unix/Linux and MAC OS, etc. With the help of Installation Wizard, you can easily and instantly complete the settings for the printing environment, and start enjoying the fantastic featur ...
... network printing solutions for various common network operating systems such as Windows 98SE/ME/2000/XP, NetWare, Unix/Linux and MAC OS, etc. With the help of Installation Wizard, you can easily and instantly complete the settings for the printing environment, and start enjoying the fantastic featur ...
User Manual
... Part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiate radio frequency energy, and may cause harmful interference to radio communications if it is not installed a ...
... Part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiate radio frequency energy, and may cause harmful interference to radio communications if it is not installed a ...
TDMoIP : IPR
... equivalence class - set of entities sharing common characteristics that can be considered equivalent for some purpose Theorem (from set theory) - any equality relation (e.g. common features) divides all entities into non-overlapping equivalence classes any forwarding algorithm need only consider d ...
... equivalence class - set of entities sharing common characteristics that can be considered equivalent for some purpose Theorem (from set theory) - any equality relation (e.g. common features) divides all entities into non-overlapping equivalence classes any forwarding algorithm need only consider d ...
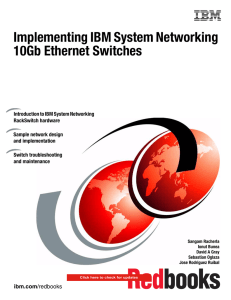
Implementing IBM System Networking 10Gb
... 4.2 Administration interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4.2.1 Console, Telnet, and Secure Shell (SSH). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4.2.2 Browser-Based interface. . . . . . . . . . . . . . . . . . . . . ...
... 4.2 Administration interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4.2.1 Console, Telnet, and Secure Shell (SSH). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4.2.2 Browser-Based interface. . . . . . . . . . . . . . . . . . . . . ...
1854_fQCC Help Screens
... NetWare®, and Macintosh OS X operating systems. Multiple operating system support allows control of heterogeneous environments. The QConvergeConsole web interface runs on the two most recent versions of commonly used web browsers, including Apple Safari, Mozilla Firefox, Google Chrome, and Microsoft ...
... NetWare®, and Macintosh OS X operating systems. Multiple operating system support allows control of heterogeneous environments. The QConvergeConsole web interface runs on the two most recent versions of commonly used web browsers, including Apple Safari, Mozilla Firefox, Google Chrome, and Microsoft ...
N150 Wireless ADSL2+ Modem Router DGN1000 User Manual 350 East Plumeria Drive
... service providers, lets you block unsafe Internet content and applications, and protects the devices (PCs, gaming consoles, and so on) that you connect to your home network. If you have not already set up your new router using the installation guide that comes in the box, this chapter walks you thro ...
... service providers, lets you block unsafe Internet content and applications, and protects the devices (PCs, gaming consoles, and so on) that you connect to your home network. If you have not already set up your new router using the installation guide that comes in the box, this chapter walks you thro ...
ATM Management Interface (AMI) Manual
... ForeRunnerLE, ForeThought, ForeView, PowerHub, and CellPath are trademarks of FORE Systems, Inc. All other brands or product names are trademarks or registered trademarks of their respective holders. U.S. Government Restricted Rights. If you are licensing the Software on behalf of the U.S. Governmen ...
... ForeRunnerLE, ForeThought, ForeView, PowerHub, and CellPath are trademarks of FORE Systems, Inc. All other brands or product names are trademarks or registered trademarks of their respective holders. U.S. Government Restricted Rights. If you are licensing the Software on behalf of the U.S. Governmen ...
david-meyer-lisp-network-grow-ietf72-2008
... – The ALT typically runs over GRE tunnels, but we also have it running over native and .1q ethernet encapsulations ...
... – The ALT typically runs over GRE tunnels, but we also have it running over native and .1q ethernet encapsulations ...