TCP Congestion Control
... was far worse than I was generally seeing. In some sense, I felt we were lucky that the really bad stuff hit just where Van was there to see it. ...
... was far worse than I was generally seeing. In some sense, I felt we were lucky that the really bad stuff hit just where Van was there to see it. ...
IEEE Report Jul 99 - IEEE Communications Society
... Speaker: Khaled Amer: President and founder of AmerNet Focus on architecture analysis and performance modeling for communications and networking chips and systems ...
... Speaker: Khaled Amer: President and founder of AmerNet Focus on architecture analysis and performance modeling for communications and networking chips and systems ...
Exploration CCNA4 - College of DuPage
... customer’s link at all times. If the CIR of the customer is less than the local access rate, the customer and provider agree on whether bursting above the CIR is allowed. If the local access rate is T1 or 1.544 Mbps, and the CIR is 768 Kbps, half of the potential bandwidth (as determined by the ...
... customer’s link at all times. If the CIR of the customer is less than the local access rate, the customer and provider agree on whether bursting above the CIR is allowed. If the local access rate is T1 or 1.544 Mbps, and the CIR is 768 Kbps, half of the potential bandwidth (as determined by the ...
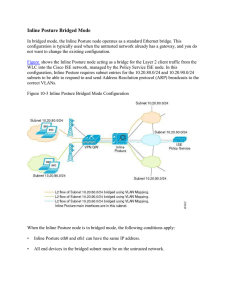
15360608-Inline Posture Bridged Mode
... Consider the following when configuring filters: • As typically implemented, Inline Posture enforces authentication requirements on endpoints that attempt to access the network. Device and subnet filters are used to validate or deny WLC and VPN devices. • For certain devices, you may want to bypass ...
... Consider the following when configuring filters: • As typically implemented, Inline Posture enforces authentication requirements on endpoints that attempt to access the network. Device and subnet filters are used to validate or deny WLC and VPN devices. • For certain devices, you may want to bypass ...
ProLiant Essentials Intelligent Networking Pack Windows Edition
... NOTE: For use with a single server. Contains one license with a unique license activation key and documentation ProLiant Essentials Intelligent Networking Pack, Flexible License NOTE: For use with multiple servers (minimum of 5). This part number allows you to specify the license quantity. When orde ...
... NOTE: For use with a single server. Contains one license with a unique license activation key and documentation ProLiant Essentials Intelligent Networking Pack, Flexible License NOTE: For use with multiple servers (minimum of 5). This part number allows you to specify the license quantity. When orde ...
ZigBee: Home Wireless Control Made Simple
... Freescale Semiconductor Confidential and Proprietary Information. Freescale™ and the Freescale logo are trademarks of Freescale Semiconductor, Inc. All other product or service names are the property of their respective owners. © Freescale Semiconductor, Inc. 2005. ...
... Freescale Semiconductor Confidential and Proprietary Information. Freescale™ and the Freescale logo are trademarks of Freescale Semiconductor, Inc. All other product or service names are the property of their respective owners. © Freescale Semiconductor, Inc. 2005. ...
Networks and Network Security - Nicolas T. COURTOIS` research in
... – leased line between offices would be expensive. – use the Internet: very cheap BUT dangerous/insecure ...
... – leased line between offices would be expensive. – use the Internet: very cheap BUT dangerous/insecure ...
DSL-504T ADSL Router User’s Guide
... product in question has not been returned to a D-Link office, then a proof of purchase (such as a copy of the dated purchase invoice) must be provided when requesting warranty service. The term "purchase" in this software warranty refers to the purchase transaction and resulting license to use such ...
... product in question has not been returned to a D-Link office, then a proof of purchase (such as a copy of the dated purchase invoice) must be provided when requesting warranty service. The term "purchase" in this software warranty refers to the purchase transaction and resulting license to use such ...
Seahorse XFp Analyzer User Guide
... The XFp Analyzer uses optical detection technology to measure extremely low levels of fluorescent emission from analyte sensors. Therefore, although the instrument has been designed to shield room light, excessive light (such as direct sunlight) should be avoided. ...
... The XFp Analyzer uses optical detection technology to measure extremely low levels of fluorescent emission from analyte sensors. Therefore, although the instrument has been designed to shield room light, excessive light (such as direct sunlight) should be avoided. ...
Smart Gird Energy Training Coalition
... from a power source to an electrical load across an air gap, without interconnecting cords. • Attracting a wide range of applications, from low-power toothbrush to high-power electric vehicles, because of its convenience and better user experience. • Many leading smartphone manufacturers, such as Sa ...
... from a power source to an electrical load across an air gap, without interconnecting cords. • Attracting a wide range of applications, from low-power toothbrush to high-power electric vehicles, because of its convenience and better user experience. • Many leading smartphone manufacturers, such as Sa ...
Demystifying Layer 2 and Layer 3 VPNs
... 4.2.16 Less Vulnerable to Internet-Borne Security Threats .......................................................................................................................................................... 35 4.2.17 Multi-Homing for WAN Redundancy.............................................. ...
... 4.2.16 Less Vulnerable to Internet-Borne Security Threats .......................................................................................................................................................... 35 4.2.17 Multi-Homing for WAN Redundancy.............................................. ...
PPT
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
Wireless Sniffing With Wireshark
... Before we start wireless sniffing using Wireshark, it is helpful to understand the different operating modes supported by wireless cards. Most wireless users only use their wireless cards as a station to an AP. In managed mode, the wireless card and driver software rely on a local AP to provide conn ...
... Before we start wireless sniffing using Wireshark, it is helpful to understand the different operating modes supported by wireless cards. Most wireless users only use their wireless cards as a station to an AP. In managed mode, the wireless card and driver software rely on a local AP to provide conn ...
Vipersat CDM-570/570L
... IMPORTANT NOTE: The information contained in this document supersedes all previously published information regarding this product. Product specifications are subject to change without prior notice. Comtech reserves the right to revise this publication at any time without obligation to provide notifi ...
... IMPORTANT NOTE: The information contained in this document supersedes all previously published information regarding this product. Product specifications are subject to change without prior notice. Comtech reserves the right to revise this publication at any time without obligation to provide notifi ...
Contents - Heliodyne
... through port 9999. Some network security settings will not allow communication through port 9999 or communications to the IP address 67.221.235.20. In this case, you must disable the security settings in your router that restrict these actions. Some networks must be intentionally set to allow commun ...
... through port 9999. Some network security settings will not allow communication through port 9999 or communications to the IP address 67.221.235.20. In this case, you must disable the security settings in your router that restrict these actions. Some networks must be intentionally set to allow commun ...
D1.1: Functional Architecture Definition and Top Level
... Engineering (TE) tools for the Internet. The TEQUILA system should provide both quantitative and qualitative service guarantees through planning, dimensioning and dynamic control of traffic management techniques based on DiffServ. The DiffServ architecture has been conceived from the beginning to pr ...
... Engineering (TE) tools for the Internet. The TEQUILA system should provide both quantitative and qualitative service guarantees through planning, dimensioning and dynamic control of traffic management techniques based on DiffServ. The DiffServ architecture has been conceived from the beginning to pr ...
Exede WiFi Modem User Guide
... The Exede WiFi Modem contains a WiFi wireless LAN radio transmitter and accordingly has been certified as compliant with 47 CFR Part 15 of the FCC Rules for intentional radiators. Products that contain a radio transmitter operating under 47 CFR Part 15 are labeled with FCC ID and FCC logo. The m ...
... The Exede WiFi Modem contains a WiFi wireless LAN radio transmitter and accordingly has been certified as compliant with 47 CFR Part 15 of the FCC Rules for intentional radiators. Products that contain a radio transmitter operating under 47 CFR Part 15 are labeled with FCC ID and FCC logo. The m ...
Layer 2 WAN Technology Design Guide - August 2014
... performance and reliability. Although most of the applications and services that the remote-site worker uses are centrally located, the WAN design must provide the workforce with a common resource-access experience, regardless of location. Major market drivers for Layer 2 WAN services include surgin ...
... performance and reliability. Although most of the applications and services that the remote-site worker uses are centrally located, the WAN design must provide the workforce with a common resource-access experience, regardless of location. Major market drivers for Layer 2 WAN services include surgin ...
Cisco PIX 535 Security Appliance
... Additional integrated event management and inventory solutions are also available as part of the CiscoWorks VMS network management suite. The integrated Cisco PIX Device Manager provides an intuitive, Web-based management interface for remotely configuring, monitoring, and troubleshooting a Cisco PI ...
... Additional integrated event management and inventory solutions are also available as part of the CiscoWorks VMS network management suite. The integrated Cisco PIX Device Manager provides an intuitive, Web-based management interface for remotely configuring, monitoring, and troubleshooting a Cisco PI ...
PPT
... sender despite transmission errors and out-of-order delivery on the wireless link. If wireless link delay-bandwidth product less than 4 packets: simple (TCP-unaware) link level retransmission scheme can suffice. ...
... sender despite transmission errors and out-of-order delivery on the wireless link. If wireless link delay-bandwidth product less than 4 packets: simple (TCP-unaware) link level retransmission scheme can suffice. ...
Cisco IP SLA`s
... IP SLA for Voice over IP • VoIP may be difficult to deploy when the network behavior is not well understood Cisco IOS IP SLAs will verify network readiness and QoS Measure critical performance for VoIP deployment Real time warning of network performance degradation IP SLA is universally available a ...
... IP SLA for Voice over IP • VoIP may be difficult to deploy when the network behavior is not well understood Cisco IOS IP SLAs will verify network readiness and QoS Measure critical performance for VoIP deployment Real time warning of network performance degradation IP SLA is universally available a ...
Part I: Introduction - Department of Computer Science and Technology
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
Link Layer
... Random Access Protocols r When node has packet to send m transmit at full channel data rate R. m no a priori coordination among nodes r two or more transmitting nodes ➜ “collision”, r random access MAC protocol specifies: m how to detect collisions m how to recover from collisions (e.g., via delaye ...
... Random Access Protocols r When node has packet to send m transmit at full channel data rate R. m no a priori coordination among nodes r two or more transmitting nodes ➜ “collision”, r random access MAC protocol specifies: m how to detect collisions m how to recover from collisions (e.g., via delaye ...
OSPFN - Named Data Networking (NDN)
... Forwarding Information Base (FIB) using the names carried in the messages. Although FIBs can be manually configured, such manipulation is time-consuming and error-prone. For the NDN testbed and, more importantly, future NDN deployment, we need a routing protocol that would calculate routes to name p ...
... Forwarding Information Base (FIB) using the names carried in the messages. Although FIBs can be manually configured, such manipulation is time-consuming and error-prone. For the NDN testbed and, more importantly, future NDN deployment, we need a routing protocol that would calculate routes to name p ...