Device Management System
... form the fabric of our network and allows for transport of application data through the Aeris operations center to your host application environment. Tools and information are provided for managing your devices on the Company network: online device management and web services. Online device manageme ...
... form the fabric of our network and allows for transport of application data through the Aeris operations center to your host application environment. Tools and information are provided for managing your devices on the Company network: online device management and web services. Online device manageme ...
MSS485 Installation Guide
... For termination in two-wire mode, set switch 4 to the On position and switch 5 to the Off position. For termination in four-wire mode, set both switches to the On position. To disable termination, set both switches to the Off position. C. Switches 6 and 7 control RX (receive) biasing. Biasing makes ...
... For termination in two-wire mode, set switch 4 to the On position and switch 5 to the Off position. For termination in four-wire mode, set both switches to the On position. To disable termination, set both switches to the Off position. C. Switches 6 and 7 control RX (receive) biasing. Biasing makes ...
Presentation Title Size 30PT
... ** Student passes CCNA Discovery 4 or Exploration 4 final from the first attempt with 75% or higher they are eligible either the two or one exam offer, but not both 26 ...
... ** Student passes CCNA Discovery 4 or Exploration 4 final from the first attempt with 75% or higher they are eligible either the two or one exam offer, but not both 26 ...
IP Networks Curriculum
... Understanding Voice over IP™ ....................................................................................................................................................... 88 Understanding IMS for All-IP Networks™ ............................................................................. ...
... Understanding Voice over IP™ ....................................................................................................................................................... 88 Understanding IMS for All-IP Networks™ ............................................................................. ...
2. HBR Overview - Computer Science, Columbia University
... application above it. On the other hand, if the mobility solution were to be implemented at a higher layer, e.g. separately by each application, it might be argued that this would be inefficient. However, this may not apply if a widely used application layer protocol were to be able to handle mobili ...
... application above it. On the other hand, if the mobility solution were to be implemented at a higher layer, e.g. separately by each application, it might be argued that this would be inefficient. However, this may not apply if a widely used application layer protocol were to be able to handle mobili ...
CT-500S ADSL Router User`s Manual
... The ADSL Router utilizes an ADI chipset to meet the specific needs of multiple users at small/home offices and remote /branch offices. It provides one 10/100 BaseT Ethernet port to connect to a LAN. It can access the Internet; Corporate LAN; or Video on demand, over one ordinary telephone line; at s ...
... The ADSL Router utilizes an ADI chipset to meet the specific needs of multiple users at small/home offices and remote /branch offices. It provides one 10/100 BaseT Ethernet port to connect to a LAN. It can access the Internet; Corporate LAN; or Video on demand, over one ordinary telephone line; at s ...
Product Manual - KORE Telematics
... personnel so that they can quickly install BlueVue on multiple computers using, for example, a batch operation. Please refer to the “BlueVue User Guide” for more information. ...
... personnel so that they can quickly install BlueVue on multiple computers using, for example, a batch operation. Please refer to the “BlueVue User Guide” for more information. ...
Introduction to VLANs
... Both 802.1Q and ISL do “Explicit tagging.” 802.1Q uses an “internal tagging process” that modifies the existing Ethernet frame with the VLAN ID. This allows 802.1Q frames to work on both access and trunk links as it appears to be a standard Ethernet frame. ISL uses external tagging process, where th ...
... Both 802.1Q and ISL do “Explicit tagging.” 802.1Q uses an “internal tagging process” that modifies the existing Ethernet frame with the VLAN ID. This allows 802.1Q frames to work on both access and trunk links as it appears to be a standard Ethernet frame. ISL uses external tagging process, where th ...
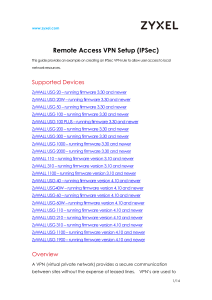
Remote Access VPN Setup (IPSec)
... not supported by the IPSec standard. Because broadcasts are not supported by the IPSec VPN standard we cannot guarantee that using hostnames instead of IP’s will work. A work around for this limitation of the IPSec standard would be to use a WINS server. ...
... not supported by the IPSec standard. Because broadcasts are not supported by the IPSec VPN standard we cannot guarantee that using hostnames instead of IP’s will work. A work around for this limitation of the IPSec standard would be to use a WINS server. ...
Computer Networking : Principles, Protocols and Practice
... information about a given topic is sometimes only a few clicks away. Websites such as wikipedia provide lots of information on various topics and students often consult them. Unfortunately, the organisation of the information on these websites is not well suited to allow students to learn from them. ...
... information about a given topic is sometimes only a few clicks away. Websites such as wikipedia provide lots of information on various topics and students often consult them. Unfortunately, the organisation of the information on these websites is not well suited to allow students to learn from them. ...
! T encor etworks
... comment, not an executable line. We will make the line an executable command, and we will assign the BANDIT’s IP address. To modify the line, do the following: a While the listing is displayed, type m to modify a line. ❖ The following prompt is displayed. ...
... comment, not an executable line. We will make the line an executable command, and we will assign the BANDIT’s IP address. To modify the line, do the following: a While the listing is displayed, type m to modify a line. ❖ The following prompt is displayed. ...
Computer Networks and Internets
... Printed in the United States of America. This publication is protected by Copyright and permission should be obtained from the publisher prior to any prohibited reproduction, storage in a retrieval system, or transmission in any form or by any means, electronic, mechanical, photocopying, recording, ...
... Printed in the United States of America. This publication is protected by Copyright and permission should be obtained from the publisher prior to any prohibited reproduction, storage in a retrieval system, or transmission in any form or by any means, electronic, mechanical, photocopying, recording, ...
Optical transmission technology
... even over large distances. At the end of the line opto/electro converters transform the optical signal back into a SAT-IF signal (see figure below). ...
... even over large distances. At the end of the line opto/electro converters transform the optical signal back into a SAT-IF signal (see figure below). ...
Powerpoint Slides - Suraj @ LUMS
... For example, ingress needs to know how much bandwidth is left on links The information is propagated by means of routing protocols and their extensions ...
... For example, ingress needs to know how much bandwidth is left on links The information is propagated by means of routing protocols and their extensions ...
Investigation on Material Dispersion as a Function of Pressure and
... communications. On the contrary, material dispersion limits how much data can be sent, as the pulses will overlap and information will be lost. Ongoing research is attempting to reduce the effects of material dispersion. In optics, the Sellmeier equation is an empirical relationship between refracti ...
... communications. On the contrary, material dispersion limits how much data can be sent, as the pulses will overlap and information will be lost. Ongoing research is attempting to reduce the effects of material dispersion. In optics, the Sellmeier equation is an empirical relationship between refracti ...
User Guide Linksys E-Series Routers
... How to find your network on the Internet . . . . . . . . . . . . . How to clone a MAC address . . . . . . . . . . . . . . . . . . . . . . How to connect to your corporate office using a VPN . . . . . . How to optimize your router for gaming and voice . . . ...
... How to find your network on the Internet . . . . . . . . . . . . . How to clone a MAC address . . . . . . . . . . . . . . . . . . . . . . How to connect to your corporate office using a VPN . . . . . . How to optimize your router for gaming and voice . . . ...
Trading Structure for Randomness in Wireless Opportunistic Routing
... Figure 2: Multicast Example. Instead of retransmitting all four packets, the source can transmit two linear combinations, e.g., p1 + p2 + p3 + p4 and p1 + 2p2 + 3p3 + 4p4 . These two coded packets allow all three destinations to retrieve the four original packets, saving the source 2 transmissions. ...
... Figure 2: Multicast Example. Instead of retransmitting all four packets, the source can transmit two linear combinations, e.g., p1 + p2 + p3 + p4 and p1 + 2p2 + 3p3 + 4p4 . These two coded packets allow all three destinations to retrieve the four original packets, saving the source 2 transmissions. ...
Chromecast Deployment Guide, Release 7.6 Introduction
... A Chromecast device receiving the request with the Search Target responds by sending a unicast UDP packet to the client. The UDP packet contains the LOCATION header, which has an absolute http URL for the uPNP description of the Chromecast device. The UDP packet also contains the Search Target sent ...
... A Chromecast device receiving the request with the Search Target responds by sending a unicast UDP packet to the client. The UDP packet contains the LOCATION header, which has an absolute http URL for the uPNP description of the Chromecast device. The UDP packet also contains the Search Target sent ...
XP Utilites
... commands into Device Driver Interface (DDI) commands sent to printer Printer interface driver—means of allowing Windows XP to interact with printer (provides "Printers and Faxes" applet Characterization data file—provides information to driver about make and model of printer, and its features ...
... commands into Device Driver Interface (DDI) commands sent to printer Printer interface driver—means of allowing Windows XP to interact with printer (provides "Printers and Faxes" applet Characterization data file—provides information to driver about make and model of printer, and its features ...
Neutering Ettercap
... IP DHCP Snooping only allows authentic DHCP servers to be able to reply to transactions. Rogue servers that send replies to DHCP request will have the reply packet dropped by the switch and a log message will be generated. The DHCP Transaction will still be visible to all host on the LAN segment, bu ...
... IP DHCP Snooping only allows authentic DHCP servers to be able to reply to transactions. Rogue servers that send replies to DHCP request will have the reply packet dropped by the switch and a log message will be generated. The DHCP Transaction will still be visible to all host on the LAN segment, bu ...
NION CobraNet Hardware Manual Version 1.7.1.0 July 23, 2014
... commercial audio and communications applications. The product features an internal processing core supported by a wide range of features, including a scalable I/O architecture. A range of plug-in cards is available that allow audio input and output, plus advanced features like echo cancellation. Aud ...
... commercial audio and communications applications. The product features an internal processing core supported by a wide range of features, including a scalable I/O architecture. A range of plug-in cards is available that allow audio input and output, plus advanced features like echo cancellation. Aud ...
IPv6 based NGN
... • A Next Generation Networks (NGN) is a packet-based network able to provide Telecommunication Services to users and able to make use of multiple broadband, QoS-enabled transport technologies and in which service-related functions are independent of the underlying transportrelated technologies. ...
... • A Next Generation Networks (NGN) is a packet-based network able to provide Telecommunication Services to users and able to make use of multiple broadband, QoS-enabled transport technologies and in which service-related functions are independent of the underlying transportrelated technologies. ...
A Review of 6LoWPAN Routing Protocols
... However, beyond the Mesh Header, additional routing information is needed to be appended appropriately with the headers to achieve a full routing functionality. Therefore, additional routing header is needed to be encapsulated in the packet. There have been a few developments on routing protocols fo ...
... However, beyond the Mesh Header, additional routing information is needed to be appended appropriately with the headers to achieve a full routing functionality. Therefore, additional routing header is needed to be encapsulated in the packet. There have been a few developments on routing protocols fo ...
Towards Automated Dynamic Analysis for Linux
... exploit succeeds by monitoring events from our instrumented kernel. These passes helped us detect 14 previously unknown vulnerabilities, which were automatically confirmed to affect 69 firmware images, based on proof-of-concept exploits that we developed (see §V-B). We further demonstrate the flexib ...
... exploit succeeds by monitoring events from our instrumented kernel. These passes helped us detect 14 previously unknown vulnerabilities, which were automatically confirmed to affect 69 firmware images, based on proof-of-concept exploits that we developed (see §V-B). We further demonstrate the flexib ...
J045055560
... the development and organizes of definite project execution. Network diagram play a vital role in formative project-completion time. In general a project will consist of a number of performance and some performance can be started, only after ultimate some other behavior. There may be some behavior w ...
... the development and organizes of definite project execution. Network diagram play a vital role in formative project-completion time. In general a project will consist of a number of performance and some performance can be started, only after ultimate some other behavior. There may be some behavior w ...