Chapter6
... • Using subinterfaces for inter-VLAN routing results in a less complex physical configuration (less cables) than using separate physical interfaces. • On the other hand, using subinterfaces with a trunk port results in a more complex software configuration, which can be difficult to troubleshoot. • ...
... • Using subinterfaces for inter-VLAN routing results in a less complex physical configuration (less cables) than using separate physical interfaces. • On the other hand, using subinterfaces with a trunk port results in a more complex software configuration, which can be difficult to troubleshoot. • ...
Summit X460 Data Sheet
... the proprietary Netflow. The technology is a complimentary protocol to sFlow. IPFIX gathers information about network flows through the switch and sends the information to an external collector. Summit X460 includes hardware support to keep track of the flow records. ...
... the proprietary Netflow. The technology is a complimentary protocol to sFlow. IPFIX gathers information about network flows through the switch and sends the information to an external collector. Summit X460 includes hardware support to keep track of the flow records. ...
Xerox Network Accounting Manual
... authenticate users or release print jobs). To provide an additional level of security, PaperCut may be configured to only allow device connections from a restricted range of network addresses. This ensures that only approved devices are connected to the PaperCut server. By default PaperCut will allo ...
... authenticate users or release print jobs). To provide an additional level of security, PaperCut may be configured to only allow device connections from a restricted range of network addresses. This ensures that only approved devices are connected to the PaperCut server. By default PaperCut will allo ...
Optical link module
... secure operation of plants, solutions, machines, equipment and/or networks. They are important components in a holistic industrial security concept. With this in mind, Siemens’ products and solutions undergo continuous development. Siemens recommends strongly that you regularly check for product upd ...
... secure operation of plants, solutions, machines, equipment and/or networks. They are important components in a holistic industrial security concept. With this in mind, Siemens’ products and solutions undergo continuous development. Siemens recommends strongly that you regularly check for product upd ...
Chapter 17
... – The low order bit of the high-order octet distinguishes unicast (0) from multicast(1) addresses • In dotted hexadecimal: 01.00.00.00.00.0016 – Device driver software can reconfigure a device to allow it to recognize one or more multicast addresses ...
... – The low order bit of the high-order octet distinguishes unicast (0) from multicast(1) addresses • In dotted hexadecimal: 01.00.00.00.00.0016 – Device driver software can reconfigure a device to allow it to recognize one or more multicast addresses ...
Routing protocols for wireless networks
... 2. Sender S broadcasts a RREQ to all its neighbors, each node receiving RREQ forwards RREQ to its neighbors. *Sequence numbers help to avoid the possibility of forwarding the same packet more than once. 3. An intermediate node (not the destination) may also send a RouteReply (RREP) packet provided t ...
... 2. Sender S broadcasts a RREQ to all its neighbors, each node receiving RREQ forwards RREQ to its neighbors. *Sequence numbers help to avoid the possibility of forwarding the same packet more than once. 3. An intermediate node (not the destination) may also send a RouteReply (RREP) packet provided t ...
Before You Begin: Assign Information Classification
... users, applications, and data—and escalating user expectations Simplify management and reduce TCO--computing, energy, and maintenance costs Maintain the university’s reputation for leading-edge computing to attract students, faculty, and research. Seamlessly integrate applications, network, an ...
... users, applications, and data—and escalating user expectations Simplify management and reduce TCO--computing, energy, and maintenance costs Maintain the university’s reputation for leading-edge computing to attract students, faculty, and research. Seamlessly integrate applications, network, an ...
ccna1-mod10-Routing
... which a physical path is obtained for and dedicated to a single connection between two end-points in the network for the duration of the connection. – This type of communication between sender and receiver is known as connectionless (rather than dedicated). – Most traffic over the Internet uses pack ...
... which a physical path is obtained for and dedicated to a single connection between two end-points in the network for the duration of the connection. – This type of communication between sender and receiver is known as connectionless (rather than dedicated). – Most traffic over the Internet uses pack ...
3rd Edition, Chapter 5
... Multiple access problem Point-to-point link and switched media no problem Broadcast links? Network arbitration Give everyone a fixed time/freq slot? • Ok for fixed bandwidth (e.g., voice) • What if traffic is bursty? ...
... Multiple access problem Point-to-point link and switched media no problem Broadcast links? Network arbitration Give everyone a fixed time/freq slot? • Ok for fixed bandwidth (e.g., voice) • What if traffic is bursty? ...
ARRIS Router Setup - Web GUI User’s Guide Standard 1.2 May 2012
... Except as specifically required for use of the Software and Service and subject to the Agreement, reproduction in any manner whatsoever without the express written permission of ARRIS Group, Inc. is strictly forbidden. For more information, contact ARRIS. ARRIS disclaims rights to any third party co ...
... Except as specifically required for use of the Software and Service and subject to the Agreement, reproduction in any manner whatsoever without the express written permission of ARRIS Group, Inc. is strictly forbidden. For more information, contact ARRIS. ARRIS disclaims rights to any third party co ...
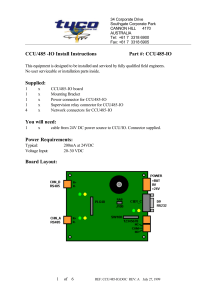
485-CCU HUB - Tyco Safety Products ANZ
... BINARY address. Note that the address of the board can be configured in software, in which case the address jumpers are ignored. See Appendix B for a complete list of address numbers and corresponding jumper positions. ...
... BINARY address. Note that the address of the board can be configured in software, in which case the address jumpers are ignored. See Appendix B for a complete list of address numbers and corresponding jumper positions. ...
KillerBee: Practical ZigBee Exploitation Framework or "Hacking the
... devices must have key stored in flash • When device boots, key is moved to RAM • Leverage device to retrieve encryption key, access network or decrypt all traffic This is not unlike WPA2-PSK networks, where each device has knowledge of the key. A compromised device is a compromised network. No key r ...
... devices must have key stored in flash • When device boots, key is moved to RAM • Leverage device to retrieve encryption key, access network or decrypt all traffic This is not unlike WPA2-PSK networks, where each device has knowledge of the key. A compromised device is a compromised network. No key r ...
... communication. Different from traditional PSTN, it has several advantages including cost saving, flexibility, and better voice quality. These properties have led to growing demand for development of better VoIP services. Furthermore, recent research works [4][5][6][7] on VoIP design have attained mo ...
Game Theory application to Networking Research: Part IV.
... X: strategy of “overlay” traffic allocation on logical links Y: strategy of “underlay” traffic allocation on physical links : Cost of “overlay” ...
... X: strategy of “overlay” traffic allocation on logical links Y: strategy of “underlay” traffic allocation on physical links : Cost of “overlay” ...
USB/IP - a Peripheral Bus Extension for Device Sharing
... the existing abstraction layer to forward device requests) usually only support the same operating system and cannot interoperate with other operating systems which do not have such an abstraction layer. Furthermore, the interoperability sometimes conflicts with the above first issue; the abstractio ...
... the existing abstraction layer to forward device requests) usually only support the same operating system and cannot interoperate with other operating systems which do not have such an abstraction layer. Furthermore, the interoperability sometimes conflicts with the above first issue; the abstractio ...
69 Kyung Hee University Router Link LSA 70 Kyung Hee University
... 1. The shortest distance and the cost between a node and itself is initialized to 0 2. The shortest distance between a node and any other node is set to infinity. The cost between a node and any other node should be given. 3. The algorithm repeat until there is no more change in the shortest distanc ...
... 1. The shortest distance and the cost between a node and itself is initialized to 0 2. The shortest distance between a node and any other node is set to infinity. The cost between a node and any other node should be given. 3. The algorithm repeat until there is no more change in the shortest distanc ...
Chapter 8: Virtual LAN (VLAN)
... This header information designates the VLAN membership of each packet. The packet is then forwarded to the appropriate switches or routers based on the VLAN identifier and MAC address. Upon reaching the destination node (Switch) the VLAN ID is removed from the packet by the adjacent switch and forwa ...
... This header information designates the VLAN membership of each packet. The packet is then forwarded to the appropriate switches or routers based on the VLAN identifier and MAC address. Upon reaching the destination node (Switch) the VLAN ID is removed from the packet by the adjacent switch and forwa ...
Chapter11 (Unicast Routing Protocols)
... 1. The shortest distance and the cost between a node and itself is initialized to 0 2. The shortest distance between a node and any other node is set to infinity. The cost between a node and any other node should be given. 3. The algorithm repeat until there is no more change in the shortest distanc ...
... 1. The shortest distance and the cost between a node and itself is initialized to 0 2. The shortest distance between a node and any other node is set to infinity. The cost between a node and any other node should be given. 3. The algorithm repeat until there is no more change in the shortest distanc ...
D3.2 Traffic Models
... aggregate level. Section 5.1 presents a comparison between daily profiles of the different networks along with an interesting analysis of the average traffic rate per active user in the Spanish CMTS network. Section 5.2 summarizes the findings (presented in D3.1) of the relationship between the upli ...
... aggregate level. Section 5.1 presents a comparison between daily profiles of the different networks along with an interesting analysis of the average traffic rate per active user in the Spanish CMTS network. Section 5.2 summarizes the findings (presented in D3.1) of the relationship between the upli ...
Serial over Ethernet Device Server User`s Manual
... devices. It provides a convenient and economical solution not only to protect your current hardware investment, but also to ensure future network expandability. With Serial over Ethernet Server, users can centralize serial devices and distribute the management hosts at the same time. Serial over Eth ...
... devices. It provides a convenient and economical solution not only to protect your current hardware investment, but also to ensure future network expandability. With Serial over Ethernet Server, users can centralize serial devices and distribute the management hosts at the same time. Serial over Eth ...
Hyper Converged 250 System for VMware vSphere Installation Guide
... The information contained herein is subject to change without notice. The only warranties for Hewlett Packard Enterprise products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional wa ...
... The information contained herein is subject to change without notice. The only warranties for Hewlett Packard Enterprise products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional wa ...
TCP Proxy
... Single TCP Connection over Bluetooth • Possible Reasons for throughput jumps – Traffic in low-bandwidth direction • Packet Scheduler has to send more data • Adjusting to „more symmetric“ bandwidth • Flow Control on Baseband ...
... Single TCP Connection over Bluetooth • Possible Reasons for throughput jumps – Traffic in low-bandwidth direction • Packet Scheduler has to send more data • Adjusting to „more symmetric“ bandwidth • Flow Control on Baseband ...
Intelligent Environments
... carrier uses the zero-voltage crossing point of the 60Hz AC sine wave on the cycle’s positive or negative transition Synchronized receivers accept the carrier at each zero-crossing point X10 uses two zero crossings to transmit a binary digit so as to reduce errors Intelligent Environments ...
... carrier uses the zero-voltage crossing point of the 60Hz AC sine wave on the cycle’s positive or negative transition Synchronized receivers accept the carrier at each zero-crossing point X10 uses two zero crossings to transmit a binary digit so as to reduce errors Intelligent Environments ...
This chapter covers the following topics: • Characteristics of roaming
... basic interoperability. The fact that the algorithms are left to vendor implementation provide vendors an opportunity to differentiate themselves by creating new and better performing algorithms than their competitors. Roaming algorithms become a vendor’s “secret sauce,” and as a result are kept con ...
... basic interoperability. The fact that the algorithms are left to vendor implementation provide vendors an opportunity to differentiate themselves by creating new and better performing algorithms than their competitors. Roaming algorithms become a vendor’s “secret sauce,” and as a result are kept con ...