CCNA cheat sheet - Internetwork Training
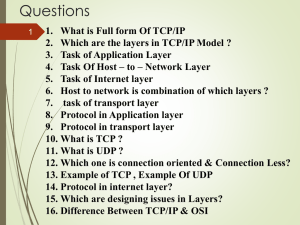
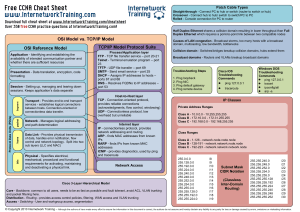
... Application - Identifying and establishing the availability of intended communication partner and whether there are sufficient resources Presentation - Data translation, encryption, code formatting ...
... Application - Identifying and establishing the availability of intended communication partner and whether there are sufficient resources Presentation - Data translation, encryption, code formatting ...
Backbone: the main connecting cable that runs from one end of the
... protocol- is a convention or standard that controls or enables the connection, communication, and data transfer between two computing endpoints. In its simplest form, a protocol can be defined as the rules governing the syntax, semantics, and synchronization of communication. Protocols may be implem ...
... protocol- is a convention or standard that controls or enables the connection, communication, and data transfer between two computing endpoints. In its simplest form, a protocol can be defined as the rules governing the syntax, semantics, and synchronization of communication. Protocols may be implem ...
2 - UTRGV Faculty Web
... computer transmits the final packet • When a packet arrives – The packet passes up through the protocol layers – A given layer performs processing and passes the packet up to the next layer – The application receives the message that was sent ...
... computer transmits the final packet • When a packet arrives – The packet passes up through the protocol layers – A given layer performs processing and passes the packet up to the next layer – The application receives the message that was sent ...
Telecommunication
... If there are only 2 users on the network, it’s not very useful; if there are 200 it’s much more useful. So the Internet with millions of computers is incredibly useful. ...
... If there are only 2 users on the network, it’s not very useful; if there are 200 it’s much more useful. So the Internet with millions of computers is incredibly useful. ...
Word 2000 - UCLA.edu
... sends an acknowledgement. If not, the receiver discards the packet. The sender basically waits for the acknowledgement for a while. If the acknowledgement does not arrive, the sender will retransmit the message. If two senders try to send at the same time, both messages would get garbled, and both m ...
... sends an acknowledgement. If not, the receiver discards the packet. The sender basically waits for the acknowledgement for a while. If the acknowledgement does not arrive, the sender will retransmit the message. If two senders try to send at the same time, both messages would get garbled, and both m ...
PPT - 清華大學資訊工程學系
... – If the channel is busy, it waits another random period. After waiting, if the channel is silent, it sends data immediately. ...
... – If the channel is busy, it waits another random period. After waiting, if the channel is silent, it sends data immediately. ...
Chapter 12 Summary: The Internet and How It Works
... The Internet began as a research network funded by the U.S. Defense Department in 1969. ...
... The Internet began as a research network funded by the U.S. Defense Department in 1969. ...
Language Support for Concurrency
... • The promise of distributed systems: – Higher availability: one machine goes down, use another – Better durability: store data in multiple locations – More security: each piece easier to make secure ...
... • The promise of distributed systems: – Higher availability: one machine goes down, use another – Better durability: store data in multiple locations – More security: each piece easier to make secure ...
IGERTPoster2009
... 2Department of Neuroscience, Department of Physiology and Cellular Biophysics, Columbia University ...
... 2Department of Neuroscience, Department of Physiology and Cellular Biophysics, Columbia University ...
Network Environments
... units (commonly referred to as nodes) are connected. Common topologies: ...
... units (commonly referred to as nodes) are connected. Common topologies: ...
426Introduction
... Used analog transmission system Requires setting up a connection before transfer of information can take place (called “circuit switching”) ...
... Used analog transmission system Requires setting up a connection before transfer of information can take place (called “circuit switching”) ...
Basic Network Concepts
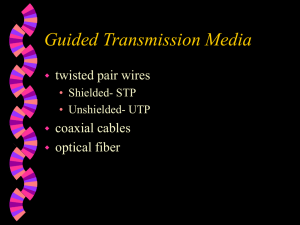
... computers and other devices that can send data to and receive data from each other. • A network is often connected by wires. • However, wireless networks transmit data through infrared light and microwaves. ...
... computers and other devices that can send data to and receive data from each other. • A network is often connected by wires. • However, wireless networks transmit data through infrared light and microwaves. ...
Introduction to Networks
... protocols versus the Internet protocols are no longer relevant. – ISO protocols are largely ignored. – An implementation of the TCP/IP protocol suite was bundled with the Unix operating system. – The ISO/ITU culture has always been to specify first and implement later. – In 1988, the NIST approved a ...
... protocols versus the Internet protocols are no longer relevant. – ISO protocols are largely ignored. – An implementation of the TCP/IP protocol suite was bundled with the Unix operating system. – The ISO/ITU culture has always been to specify first and implement later. – In 1988, the NIST approved a ...
Introduction - Jigar Pandya
... DCEs are carrier-owned internetworking devices. The purpose of DCE equipment is to provide clocking and switching services in a network, which are the devices that actually transmit data through the WAN. ...
... DCEs are carrier-owned internetworking devices. The purpose of DCE equipment is to provide clocking and switching services in a network, which are the devices that actually transmit data through the WAN. ...
The Internet and the World Wide Web Basics
... servers explains why people in Paraguay may be able to access the site while people in Portugal cannot since it has not reached their DNS servers. One of the advantages of this technology is that you can find out who is looking at your site. Most hosting services log the IP address of the users that ...
... servers explains why people in Paraguay may be able to access the site while people in Portugal cannot since it has not reached their DNS servers. One of the advantages of this technology is that you can find out who is looking at your site. Most hosting services log the IP address of the users that ...
Introduction to Distributed Systems & Networking
... Physical Layer: electrical details of bits on the wire Data Link: sending “frames” of bits and error detection Network Layer:” routing packets to the destination Transport Layer: reliable transmission of messages, disassembly/assembly, ordering, retransmission of lost packets • Session Layer; really ...
... Physical Layer: electrical details of bits on the wire Data Link: sending “frames” of bits and error detection Network Layer:” routing packets to the destination Transport Layer: reliable transmission of messages, disassembly/assembly, ordering, retransmission of lost packets • Session Layer; really ...
Solution
... lane then 1from the second, then 1 from the first, and so on). WFQ: ticket counter at airport providing service to 2 people from first class and 1 from economy, and again 2 from first class, and so on. 9. What are some of the difficulties associated with the Intserv model and per-flow reservation of ...
... lane then 1from the second, then 1 from the first, and so on). WFQ: ticket counter at airport providing service to 2 people from first class and 1 from economy, and again 2 from first class, and so on. 9. What are some of the difficulties associated with the Intserv model and per-flow reservation of ...
NP_ch01
... The Internet can accommodate arbitrary, heterogeneous network Data rates keep increasing Protocols and applications keep evolving System design is expensive, and implementation and testing take too long Special-purpose hardware designed for one system cannot be reused ...
... The Internet can accommodate arbitrary, heterogeneous network Data rates keep increasing Protocols and applications keep evolving System design is expensive, and implementation and testing take too long Special-purpose hardware designed for one system cannot be reused ...
classful addressing - E Learning UPN Veteran Yogyakarta
... • Addresses beginning with 01111111, or 127 decimal, are reserved for loopback and for internal testing on a local machine; [You can test this: you should always be able to ping 127.0.0.1, which points to yourself] ...
... • Addresses beginning with 01111111, or 127 decimal, are reserved for loopback and for internal testing on a local machine; [You can test this: you should always be able to ping 127.0.0.1, which points to yourself] ...
Certification Exercise 2
... 8. Which network device provides public to private network security and may use Network Address Translation (NAT)? a) Hub b) Bridge c) Switch d) Firewall 9. Which device connects multiple computers to create a single logical network segment? a) Hub b) NIC c) Router d) Bridge 10. Devices on a Token ...
... 8. Which network device provides public to private network security and may use Network Address Translation (NAT)? a) Hub b) Bridge c) Switch d) Firewall 9. Which device connects multiple computers to create a single logical network segment? a) Hub b) NIC c) Router d) Bridge 10. Devices on a Token ...