Chapter 5 - College of Business Administration
... take appropriate actions). Concepts like extranets, collaborative commerce, intranets support this idea. Higher quality management decisions (access to more information in a timely manner) Declining geographical barriers Declining temporal barriers (software development, time-based competition) ...
... take appropriate actions). Concepts like extranets, collaborative commerce, intranets support this idea. Higher quality management decisions (access to more information in a timely manner) Declining geographical barriers Declining temporal barriers (software development, time-based competition) ...
Lecture 3a
... • A network of networks, joining many government, university and private computers together and providing an infrastructure for the use of E-mail, bulletin boards, file archives, hypertext documents, databases and other computational resources • The vast collection of computer networks which form an ...
... • A network of networks, joining many government, university and private computers together and providing an infrastructure for the use of E-mail, bulletin boards, file archives, hypertext documents, databases and other computational resources • The vast collection of computer networks which form an ...
Technology and Convergence Looking Back and Looking
... Consumer perspective: freedom to use broadband to access content, applications and devices of their choice Company perspective: broadband networks may not “discriminate” in favor of their own or affiliated content, applications or devices ...
... Consumer perspective: freedom to use broadband to access content, applications and devices of their choice Company perspective: broadband networks may not “discriminate” in favor of their own or affiliated content, applications or devices ...
1_Oct16_2015 - users.cs.umn.edu
... information systems (e.g. reconstructions). – Uses OD Matrix to model simulated trips. – Trip Simulation: • Assign vehicles initially to (one of k) shortest path (s). ...
... information systems (e.g. reconstructions). – Uses OD Matrix to model simulated trips. – Trip Simulation: • Assign vehicles initially to (one of k) shortest path (s). ...
Adam Arvay IGVA 1 Opening the black box of connectionist nets
... transformation correctly through a series of learning trials. There are many different ways to set up an artificial neural network along with many different learning algorithms but all neural networks have the same goal, to transform an input into the appropriate output. The details of how the netwo ...
... transformation correctly through a series of learning trials. There are many different ways to set up an artificial neural network along with many different learning algorithms but all neural networks have the same goal, to transform an input into the appropriate output. The details of how the netwo ...
Interacting Network Elements: Chaos and Congestion Propagation
... and Communication Networks Laboratory1 Eötvös University H-1117 Budapest, Pázmány P. s. 1/A, Hungary ...
... and Communication Networks Laboratory1 Eötvös University H-1117 Budapest, Pázmány P. s. 1/A, Hungary ...
Convergence
... • Internet Protocol does not save a path in the network for the entire duration of the call • During pauses and silences, conversations from multiple sources are transmitted over shared facilities • These variable lengths of data are called packets ...
... • Internet Protocol does not save a path in the network for the entire duration of the call • During pauses and silences, conversations from multiple sources are transmitted over shared facilities • These variable lengths of data are called packets ...
Internet - CCIT34VC
... • print servers, accepts print jobs over the network faster than a printer; workstation gets on with other tasks whilst printing is done • Database server; hold d/bases and allows them to be used by many users • web servers, connected to internet and serve webpages to viewers • Domain name servers, ...
... • print servers, accepts print jobs over the network faster than a printer; workstation gets on with other tasks whilst printing is done • Database server; hold d/bases and allows them to be used by many users • web servers, connected to internet and serve webpages to viewers • Domain name servers, ...
Lecture 2 - Networking Devices
... Routers differ from bridges in several respects. First, bridging occurs at the data link layer or layer 2,while routing occurs at the network layer or layer 3 of the OSI model. Second, bridges use physical or MAC addresses to make data forwarding decisions. Routers use a different addressing schem ...
... Routers differ from bridges in several respects. First, bridging occurs at the data link layer or layer 2,while routing occurs at the network layer or layer 3 of the OSI model. Second, bridges use physical or MAC addresses to make data forwarding decisions. Routers use a different addressing schem ...
Introduction to Communications and Networks
... Typically between cities and countries Technology: Circuit Switch, Packet Switch, Frame Relay, ATM Examples: ...
... Typically between cities and countries Technology: Circuit Switch, Packet Switch, Frame Relay, ATM Examples: ...
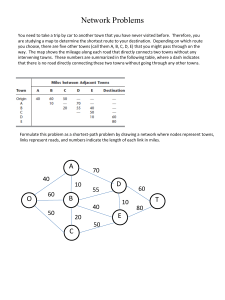
Hwk 5 Soln
... are studying a map to determine the shortest route to your destination. Depending on which route you choose, there are five other towns (call them A, B, C, D, E) that you might pass through on the way. The map shows the mileage along each road that directly connects two towns without any intervening ...
... are studying a map to determine the shortest route to your destination. Depending on which route you choose, there are five other towns (call them A, B, C, D, E) that you might pass through on the way. The map shows the mileage along each road that directly connects two towns without any intervening ...
Computer Networks - Texas State Department of Computer Science
... connected by telecommunication links. The individual computers are called nodes or hosts. The nodes are connected by some method of carrying digitized signals. Wires (coax, Cat5) Light (fiber optic) Microwaves Radio Waves Protocol An agreed upon language that computers use to communi ...
... connected by telecommunication links. The individual computers are called nodes or hosts. The nodes are connected by some method of carrying digitized signals. Wires (coax, Cat5) Light (fiber optic) Microwaves Radio Waves Protocol An agreed upon language that computers use to communi ...
Computer Networks - Texas State Department of Computer Science
... Maintains connection Checks identity of client Commonly used for sending e-mail Post Office Protocol (POP3) Common protocol for internet e-mail clients such as Eudora, Outlook Express, etc. Commonly used for checking e-mail, but not for sending E-mail stored on a mail server and the cl ...
... Maintains connection Checks identity of client Commonly used for sending e-mail Post Office Protocol (POP3) Common protocol for internet e-mail clients such as Eudora, Outlook Express, etc. Commonly used for checking e-mail, but not for sending E-mail stored on a mail server and the cl ...
Networks
... What advantages do networks have? - increase productivity - workers can share information easily without printing, copying, telephoning, or posting. ...
... What advantages do networks have? - increase productivity - workers can share information easily without printing, copying, telephoning, or posting. ...
How the internet works
... The nature of the Internet changed abruptly in 1992, when the U.S. government began pulling out of network management, and commercial entities offered Internet access to the general public for the first time. This change in focus marked the beginning of the Internet's astonishing expansion. ...
... The nature of the Internet changed abruptly in 1992, when the U.S. government began pulling out of network management, and commercial entities offered Internet access to the general public for the first time. This change in focus marked the beginning of the Internet's astonishing expansion. ...
Should SIP be modified for per call billing?
... Service checks user authentication, relays to “Phone-x” Phone-x completes the call, bills service Service bills user. ...
... Service checks user authentication, relays to “Phone-x” Phone-x completes the call, bills service Service bills user. ...



![[slides] Introduction](http://s1.studyres.com/store/data/000071965_1-ad3bfbc03953cb954fa70b8bdbbdb4bb-300x300.png)