Document
... Figure 15.1 The view of the Internet that IP software provides. Users and application programs treat the Internet like a single large network that allow arbitrary numbers of computers to communicate. ...
... Figure 15.1 The view of the Internet that IP software provides. Users and application programs treat the Internet like a single large network that allow arbitrary numbers of computers to communicate. ...
Reference Models - UT School of Information
... 1. Physical layer – not really part of this model, since TCP and IP deal with software; usually thought to refer to all hardware beneath the network layer. 2. Network or data link layer – defined by whatever the Internet Protocol will run over, e.g., a token-ring network. 3. Internet or network laye ...
... 1. Physical layer – not really part of this model, since TCP and IP deal with software; usually thought to refer to all hardware beneath the network layer. 2. Network or data link layer – defined by whatever the Internet Protocol will run over, e.g., a token-ring network. 3. Internet or network laye ...
Lecture18 - Philadelphia University
... WSN Architecture: • Nodes in the WSN are classified into two types according to their function: • Source node: It is any entity in the network that can provide information. It could be a sensor node, or an actuator node that provides feedback information about an operation. • Sink node: It is the ...
... WSN Architecture: • Nodes in the WSN are classified into two types according to their function: • Source node: It is any entity in the network that can provide information. It could be a sensor node, or an actuator node that provides feedback information about an operation. • Sink node: It is the ...
msb201073-sup
... (http://www.cytoscape.org/) which allows the import of SBML files (Level 2 Version 1) which was exported from CellDesigner 4.0.1 version of the maps. In order to compute the network properties, the Cytoscape plugin NetworkAnalyzer 2.6.1 (http://med.bioinf.mpiinf.mpg.de/netanalyzer/) were employed w ...
... (http://www.cytoscape.org/) which allows the import of SBML files (Level 2 Version 1) which was exported from CellDesigner 4.0.1 version of the maps. In order to compute the network properties, the Cytoscape plugin NetworkAnalyzer 2.6.1 (http://med.bioinf.mpiinf.mpg.de/netanalyzer/) were employed w ...
Introduction to Networking & telecommunications
... Large messages are broken into small pieces called packets (or frames) ...
... Large messages are broken into small pieces called packets (or frames) ...
E Education, the Internet, and the World Wide Web
... creation of a globally interconnected set of computers through which everyone quickly could access data and programs from any node, or place, in the world. In the early 1970s, a research project initiated by the United States Department of Defense investigated techniques and technologies to interlin ...
... creation of a globally interconnected set of computers through which everyone quickly could access data and programs from any node, or place, in the world. In the early 1970s, a research project initiated by the United States Department of Defense investigated techniques and technologies to interlin ...
Internet slides
... • No need to worry about retransmits • But still need to check that the file was written to the remote disk intact ...
... • No need to worry about retransmits • But still need to check that the file was written to the remote disk intact ...
Book Title - Computer Science
... Network interface card (NIC) Operating system that – Provides the connection between the computer and the network Inserted into a computer’s ...
... Network interface card (NIC) Operating system that – Provides the connection between the computer and the network Inserted into a computer’s ...
Westermo Group
... Cyber attacks are an increasing problem One UK utility reported that they are dealing with 8000 attacks a day! There is now a worm virus actively seeking and attacking PLC’s Most serious attacks or infections are from within i.e. the employees ...
... Cyber attacks are an increasing problem One UK utility reported that they are dealing with 8000 attacks a day! There is now a worm virus actively seeking and attacking PLC’s Most serious attacks or infections are from within i.e. the employees ...
Wireless Digital System and its application in EMI
... To carry an analog signal with 20MHz bandwidth, it needs too large bandwidth for carrier wave (why digital) To take the advantage of modern digital communication technology to overcome EMI in the field (why digital) ...
... To carry an analog signal with 20MHz bandwidth, it needs too large bandwidth for carrier wave (why digital) To take the advantage of modern digital communication technology to overcome EMI in the field (why digital) ...
Document - Oman College of Management & Technology
... signals from one part of a WAN to another, cause 0.5 to 5 sec delays. ...
... signals from one part of a WAN to another, cause 0.5 to 5 sec delays. ...
Lecture 29 - Electrical and Computer Engineering
... Copyright 1999, S.D. Personick. All Rights Reserved. ...
... Copyright 1999, S.D. Personick. All Rights Reserved. ...
A geneset score is assigned a p-value by comparing it
... walk through the condition-specific, protein-protein interaction network as follows: 1. Initialize the geneset with a randomly selected node in the interaction network, with equal probability of selection for all nodes. 2. Determine the neighbors of the current subgraph in the interaction network. 3 ...
... walk through the condition-specific, protein-protein interaction network as follows: 1. Initialize the geneset with a randomly selected node in the interaction network, with equal probability of selection for all nodes. 2. Determine the neighbors of the current subgraph in the interaction network. 3 ...
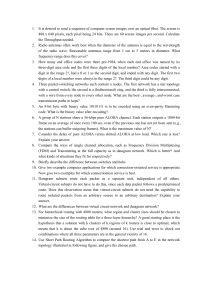
1 It is desired to send a sequence of computer screen images over
... 1. It is desired to send a sequence of computer screen images over an optical fiber. The screen is 480 x 640 pixels, each pixel being 24 bits. There are 60 screen images per second. Calculate the Throughput needed. 2. Radio antennas often work best when the diameter of the antenna is equal to the wa ...
... 1. It is desired to send a sequence of computer screen images over an optical fiber. The screen is 480 x 640 pixels, each pixel being 24 bits. There are 60 screen images per second. Calculate the Throughput needed. 2. Radio antennas often work best when the diameter of the antenna is equal to the wa ...
Article: Water and wireless: The new match in Analytical Instrumentation
... topology in which every wireless device on the network acts as a router for nearby devices. All devices work together seamlessly to identify and use the most efficient communication path for each message which ensures high data transmission reliability and network availability. The network dynamical ...
... topology in which every wireless device on the network acts as a router for nearby devices. All devices work together seamlessly to identify and use the most efficient communication path for each message which ensures high data transmission reliability and network availability. The network dynamical ...
The final will be 1-2:50 PM on Wednesday, December 13... closed-book and closed-note, except for three sheets of paper with...
... The final will be 1-2:50 PM on Wednesday, December 13 in ITT 322. The test will be closed-book and closed-note, except for three sheets of paper with notes. About 70% of the Final will focus on the material since the last test, and about 30% will focus on tests 1 and 2 material. Chapter 8. OS Suppor ...
... The final will be 1-2:50 PM on Wednesday, December 13 in ITT 322. The test will be closed-book and closed-note, except for three sheets of paper with notes. About 70% of the Final will focus on the material since the last test, and about 30% will focus on tests 1 and 2 material. Chapter 8. OS Suppor ...
15-441 Socket Programming
... – Vast majority of Internet usage is data retrieval and service access. – Users care about the content and are oblivious to location. They are often oblivious as to delivery time: • Fetching headlines from CNN, videos from YouTube, TV from Tivo • Accessing a bank account at www.bank.com. ...
... – Vast majority of Internet usage is data retrieval and service access. – Users care about the content and are oblivious to location. They are often oblivious as to delivery time: • Fetching headlines from CNN, videos from YouTube, TV from Tivo • Accessing a bank account at www.bank.com. ...
tutorial 1 - Portal UniMAP
... way around? The first computer networks grew from the need to economically utilize mainframe computers. Since the mainframe was at one location and the computer users could be anywhere in the world, a large geographical network was necessary to provide access to the mainframe. LANs came about later ...
... way around? The first computer networks grew from the need to economically utilize mainframe computers. Since the mainframe was at one location and the computer users could be anywhere in the world, a large geographical network was necessary to provide access to the mainframe. LANs came about later ...
Chapter 1 Introduction
... Example: company uses MAN to connect the LANs in a city Owned by private company or by a public company (telephone company) ...
... Example: company uses MAN to connect the LANs in a city Owned by private company or by a public company (telephone company) ...