... machine, according to player’s preferences: the server has acopy of all the «approved» games so the casino can «push» the game (including graphics andbuttons) on to the machines without having to send a technician out to replace the EEPROM.It also offers players a way to play the games they want at ...
Introduction
... Confidentiality can be achieved through Encryption: Transform data to a meaningless unit for transmission and storage. Show it correctly to intended users Access control: Control who can claim access to Authentication: Determining identity of person claiming access ...
... Confidentiality can be achieved through Encryption: Transform data to a meaningless unit for transmission and storage. Show it correctly to intended users Access control: Control who can claim access to Authentication: Determining identity of person claiming access ...
Intro_part2
... Delay in Packet-Switched Networks 3/4 •Transmission delay versus Propagation delay The transmission delay the amount of time required for the network entity to push out the packet function of the packet's length and the transmission rate of the link has nothing to do with the distance between t ...
... Delay in Packet-Switched Networks 3/4 •Transmission delay versus Propagation delay The transmission delay the amount of time required for the network entity to push out the packet function of the packet's length and the transmission rate of the link has nothing to do with the distance between t ...
Networking
... A server is a program (or collection of programs) that provide some service, e.g., file service, name service, … The server may exist on one or more nodes. A client is a program that uses the service. A client first binds to the server, I.e., locates it in the network and establishes a connection. T ...
... A server is a program (or collection of programs) that provide some service, e.g., file service, name service, … The server may exist on one or more nodes. A client is a program that uses the service. A client first binds to the server, I.e., locates it in the network and establishes a connection. T ...
HP WX5000 Access Controller Series
... The HP WX5000 Access Controller Series features large capacity, high reliability, and rich services, and offers strong wired and wireless data processing capacity. The WX5000 series provides refined user control and management, a comprehensive RF management and security mechanism, fast roaming, stro ...
... The HP WX5000 Access Controller Series features large capacity, high reliability, and rich services, and offers strong wired and wireless data processing capacity. The WX5000 series provides refined user control and management, a comprehensive RF management and security mechanism, fast roaming, stro ...
3G and 4G - Web Services Overview
... Predominantly voice- data as Converged data and VoIP add-on Wide area Cell based Hybrid – integration of Wireless Lan (WiFi), Blue ...
... Predominantly voice- data as Converged data and VoIP add-on Wide area Cell based Hybrid – integration of Wireless Lan (WiFi), Blue ...
Oracle9i Security
... environments by defining the protocol for interaction between provisioning service components and agents representing provisioned services. ...
... environments by defining the protocol for interaction between provisioning service components and agents representing provisioned services. ...
Privacy enhancing protocols for wireless networks
... In this thesis some privacy aspects of different wireless networks are investigated. These networks are radio frequency identification systems, vehicular ad hoc networks, and wireless sensor networks. At first, private authentication methods are proposed and analyzed for low cost identification systems. ...
... In this thesis some privacy aspects of different wireless networks are investigated. These networks are radio frequency identification systems, vehicular ad hoc networks, and wireless sensor networks. At first, private authentication methods are proposed and analyzed for low cost identification systems. ...
CIS484-FIREWALL
... through file sharing (like Kazaa or Gnucleus) or through direct download of a malicious program. Firewalls can't prevent this - only a good anti-virus software program can. ...
... through file sharing (like Kazaa or Gnucleus) or through direct download of a malicious program. Firewalls can't prevent this - only a good anti-virus software program can. ...
The Fast Lane to VoIP
... engineering, manufacturing and customer support is conducted right here in the United States. REDCOM lives up to the traditions of American quality and service by building products that last a lifetime, and we provide ongoing support for everything we’ve ever sold. You don’t have to look far to find ...
... engineering, manufacturing and customer support is conducted right here in the United States. REDCOM lives up to the traditions of American quality and service by building products that last a lifetime, and we provide ongoing support for everything we’ve ever sold. You don’t have to look far to find ...
Detail Comparison of Network Simulators
... research[1]. In 1996-‘97, NS2 was initiated and licensed for use under General Public License (GNU). It provides support for both wired and wireless simulation of functions and protocols such as TCP, UDP etc. NS2 was developed from the ideology of REAL simulator[19]. NS2 is one of the popular simula ...
... research[1]. In 1996-‘97, NS2 was initiated and licensed for use under General Public License (GNU). It provides support for both wired and wireless simulation of functions and protocols such as TCP, UDP etc. NS2 was developed from the ideology of REAL simulator[19]. NS2 is one of the popular simula ...
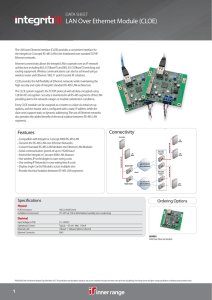
LAN Over Ethernet Module (CLOE)
... the Integriti (or Concept) RS-485 LAN to be distributed over standard TCP/IP Ethernet networks. Ethernet connectivity allows the Integriti LAN to operate over an IP network architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also ...
... the Integriti (or Concept) RS-485 LAN to be distributed over standard TCP/IP Ethernet networks. Ethernet connectivity allows the Integriti LAN to operate over an IP network architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... management using MA and SA was also adopted to minimize the handoff delay in the WLAN-CDMA Cellular interconnection architecture based on IP. In the handoff algorithm they use the number of continuous beacon signals whose signal strength from the WLAN falls below the predefined threshold value. In s ...
... management using MA and SA was also adopted to minimize the handoff delay in the WLAN-CDMA Cellular interconnection architecture based on IP. In the handoff algorithm they use the number of continuous beacon signals whose signal strength from the WLAN falls below the predefined threshold value. In s ...
Cookie file
... Continue despite loss of networks or gateways Support multiple types of communication service Accommodate a variety of networks Permit distributed management of Internet resources Cost effective Host attachment should be easy Resource accountability ...
... Continue despite loss of networks or gateways Support multiple types of communication service Accommodate a variety of networks Permit distributed management of Internet resources Cost effective Host attachment should be easy Resource accountability ...
PPT
... What is a protocol, what is layering? Protocols Protocol layers and their service models Network structure - edge: applications and some services Network structure - core: ...
... What is a protocol, what is layering? Protocols Protocol layers and their service models Network structure - edge: applications and some services Network structure - core: ...
18-07-0026-00 - IEEE 802 LAN/MAN Standards Committee
... connections, VoIP, instant messaging and on- line multiplayer gaming. The IMT Advanced systems shall provide the mobile user with an "always-on" experience while also taking into account and providing features needed to preserve battery life. The connectivity from the mobile terminal to the base sta ...
... connections, VoIP, instant messaging and on- line multiplayer gaming. The IMT Advanced systems shall provide the mobile user with an "always-on" experience while also taking into account and providing features needed to preserve battery life. The connectivity from the mobile terminal to the base sta ...
18-07-0026-00 - IEEE 802 LAN/MAN Standards Committee
... [QoS is an important factor especially for applications sensitive to delay and jitter which are currently supported by circuit switched networks.] IMT-Advanced systems shall support a flexible set of QoS classes and their respective configuration (e.g., by the system operator), enabling an optimal m ...
... [QoS is an important factor especially for applications sensitive to delay and jitter which are currently supported by circuit switched networks.] IMT-Advanced systems shall support a flexible set of QoS classes and their respective configuration (e.g., by the system operator), enabling an optimal m ...
Chapter 6 slides, Computer Networking, 3rd edition
... - Replace a single high power base station with several lower power base stations, each covering a smaller geographical area, a ‘cell’. - Each of the base stations is allocated a number of channels (portion of the overall system channels) 6: Wireless and Mobile Networks ...
... - Replace a single high power base station with several lower power base stations, each covering a smaller geographical area, a ‘cell’. - Each of the base stations is allocated a number of channels (portion of the overall system channels) 6: Wireless and Mobile Networks ...
Security+ Guide to Network Security Fundamentals, Fourth Edition
... Security+ Guide to Network Security Fundamentals, Fourth Edition ...
... Security+ Guide to Network Security Fundamentals, Fourth Edition ...
An Embedded Dynamic Security Networking
... network, but the algorithm is complex and the real-time performance is very poor, which can not be well used in the rapid dynamic networking. Jiao Xian-long has proposed a wireless ad-hoc network coding method with heuristic algorithm, using basic thoughts of the greedy collection configuration heur ...
... network, but the algorithm is complex and the real-time performance is very poor, which can not be well used in the rapid dynamic networking. Jiao Xian-long has proposed a wireless ad-hoc network coding method with heuristic algorithm, using basic thoughts of the greedy collection configuration heur ...
Class notes - Center For Information Management, Integration and
... – Dial-up access, Leased circuits, Cable modem, DSL technologies,Wireless access ...
... – Dial-up access, Leased circuits, Cable modem, DSL technologies,Wireless access ...
CG21532537
... application, it is passed down to the cache layer. To send the request message to the next hop, the cache layer wraps the original request message with a new destination address, which is the next hop to reach the data server (real destination). Here, we assume that the cache layer can access the ro ...
... application, it is passed down to the cache layer. To send the request message to the next hop, the cache layer wraps the original request message with a new destination address, which is the next hop to reach the data server (real destination). Here, we assume that the cache layer can access the ro ...
module 3 Cyberpatriot Powerpoint
... • Complexity ranges from simple devices to enterprise networks • Much less expensive than wired solutions • Wireless LAN (WLAN) – Wireless client: system with wireless capability – Access point (AP): device that connects different wireless stations Module 03: 66 ...
... • Complexity ranges from simple devices to enterprise networks • Much less expensive than wired solutions • Wireless LAN (WLAN) – Wireless client: system with wireless capability – Access point (AP): device that connects different wireless stations Module 03: 66 ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.