PDF - Complete Book (2.87 MB)
... CCIP, CCSP, the Cisco Arrow logo, the Cisco Powered Network mark, the Cisco Systems Verified logo, Cisco Unity, Follow Me Browsing, FormShare, iQ Breakthrough, iQ FastTrack, the iQ Logo, iQ Net Readiness Scorecard, Networking Academy, ScriptShare, SMARTnet, TransPath, and Voice LAN are trademarks of ...
... CCIP, CCSP, the Cisco Arrow logo, the Cisco Powered Network mark, the Cisco Systems Verified logo, Cisco Unity, Follow Me Browsing, FormShare, iQ Breakthrough, iQ FastTrack, the iQ Logo, iQ Net Readiness Scorecard, Networking Academy, ScriptShare, SMARTnet, TransPath, and Voice LAN are trademarks of ...
Wireless Design - Kenneth M. Chipps Ph.D. Home Page
... • The way to start any network design is to apply a top down approach that relates the business needs of the organization to the technical implementation of the network • Based on this systematic design approach a physical network is laid out on paper • The discussion here is the changes to this net ...
... • The way to start any network design is to apply a top down approach that relates the business needs of the organization to the technical implementation of the network • Based on this systematic design approach a physical network is laid out on paper • The discussion here is the changes to this net ...
Cisco Enhances per- IPSec Tunnel QoS, IOS Firewall Security for Unified
... Secures Neighbor Discovery Protocol (NDP) ...
... Secures Neighbor Discovery Protocol (NDP) ...
Fachbereich Informatik und Elektrotechnik
... Working Group 15: Wireless Personal Area Networks Synopsis: 802.15 focuses on the development of consensus standards for Personal Area Networks or short distance wireless networks. These WPANs address wireless networking of portable and mobile computing devices such as PCs, PDAs, peripherals, cell p ...
... Working Group 15: Wireless Personal Area Networks Synopsis: 802.15 focuses on the development of consensus standards for Personal Area Networks or short distance wireless networks. These WPANs address wireless networking of portable and mobile computing devices such as PCs, PDAs, peripherals, cell p ...
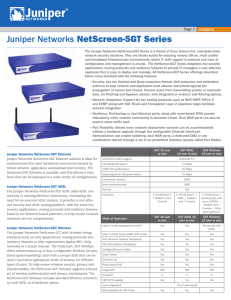
Juniper Networks NetScreen-5GT Series Datasheet
... The Juniper Networks NetScreen-5GT Series is a family of three feature-rich, enterprise-class network security solutions. They are ideally suited for securing remote offices, retail outlets and broadband telecommuter environments, where IT staff support is minimal and ease of configuration and manag ...
... The Juniper Networks NetScreen-5GT Series is a family of three feature-rich, enterprise-class network security solutions. They are ideally suited for securing remote offices, retail outlets and broadband telecommuter environments, where IT staff support is minimal and ease of configuration and manag ...
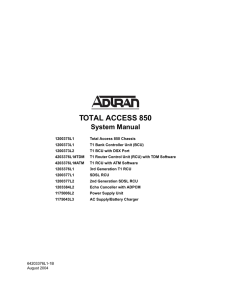
Total Access 850 System Manual
... telecommunications company. The equipment must also be installed using an acceptable method of connection. In some cases, the company's inside wiring associated with a single line individual service may be extended by means of a certified connector assembly (telephone extension cord). The customer s ...
... telecommunications company. The equipment must also be installed using an acceptable method of connection. In some cases, the company's inside wiring associated with a single line individual service may be extended by means of a certified connector assembly (telephone extension cord). The customer s ...
S9700 Series Terabit Routing Switches
... developed by Huawei to meet the demand for high-bandwidth access and Ethernet multi-service aggregation. Based on cutting-edge hardware and Huawei Versatile Routing Platform (VRP) software, the S5700 provides a large switching capacity and high-density GE ports to accommodate 10 Gbit/s upstream tra ...
... developed by Huawei to meet the demand for high-bandwidth access and Ethernet multi-service aggregation. Based on cutting-edge hardware and Huawei Versatile Routing Platform (VRP) software, the S5700 provides a large switching capacity and high-density GE ports to accommodate 10 Gbit/s upstream tra ...
Wiley Publishing - CCNA For Dummies [2000].
... Chapter 4: The Data Link Layer The sublayers of the Data Link layer.............................................................................................43 Controlling access to the network..................................................................................................45 Seg ...
... Chapter 4: The Data Link Layer The sublayers of the Data Link layer.............................................................................................43 Controlling access to the network..................................................................................................45 Seg ...
ConnectPort X Family User`s Guide
... Test the IP address configuration ...................................................................................................................52 Configuration through iDigi Manager Pro ............................................................................................................ ...
... Test the IP address configuration ...................................................................................................................52 Configuration through iDigi Manager Pro ............................................................................................................ ...
HP MSR900 Series
... lists, and aggregate policies Security Access control list (ACL): supports powerful ACLs for both IPv4 and IPv6; ACLs are used for filtering traffic to prevent unauthorized users from accessing the network, or for controlling network traffic to save resources; rules can either deny or permit traffic ...
... lists, and aggregate policies Security Access control list (ACL): supports powerful ACLs for both IPv4 and IPv6; ACLs are used for filtering traffic to prevent unauthorized users from accessing the network, or for controlling network traffic to save resources; rules can either deny or permit traffic ...
TRANSITION FROM IPv4 TO IPv6 LAHTI UNIVERSITY OF APPLIED
... and network researchers who have an interest in the network communication and would like to join the community of IPv6. Therefore, with the topic “Transition from IPv4 to IPv6: The best method for large enterprise networks”, we will have two main parts: the theoretical and the practical. For the fir ...
... and network researchers who have an interest in the network communication and would like to join the community of IPv6. Therefore, with the topic “Transition from IPv4 to IPv6: The best method for large enterprise networks”, we will have two main parts: the theoretical and the practical. For the fir ...
Layer 2 WAN Technology Design Guide - August 2014
... Service providers implement these Ethernet services by using a variety of methods. MPLS networks support both Ethernet over MPLS (EoMPLS) and Virtual Private LAN Service (VPLS). You can use other network technologies, such as Ethernet switches in various topologies, to provide Ethernet Layer 2 WAN ...
... Service providers implement these Ethernet services by using a variety of methods. MPLS networks support both Ethernet over MPLS (EoMPLS) and Virtual Private LAN Service (VPLS). You can use other network technologies, such as Ethernet switches in various topologies, to provide Ethernet Layer 2 WAN ...
CCNPv5 Module 5 Lesson 10
... authentication, a NTP access group can be created and a basic IP ACL applied to it To control access to NTP services, use the ntp access-group command in global configuration mode The access group options are scanned in the following order, from least restrictive to most restrictive: 1. peer: Allows ...
... authentication, a NTP access group can be created and a basic IP ACL applied to it To control access to NTP services, use the ntp access-group command in global configuration mode The access group options are scanned in the following order, from least restrictive to most restrictive: 1. peer: Allows ...
Top-Down Network Design
... Priscilla Oppenheimer has been developing data communications and networking systems since 1980 when she earned her master’s degree in information science from the University of Michigan. After many years as a software developer, she became a technical instructor and training developer and has taugh ...
... Priscilla Oppenheimer has been developing data communications and networking systems since 1980 when she earned her master’s degree in information science from the University of Michigan. After many years as a software developer, she became a technical instructor and training developer and has taugh ...
TCP/IP Tutorial and Technical Overview
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1989, 1998. All rights reserved. Note to U.S. Government User ...
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1989, 1998. All rights reserved. Note to U.S. Government User ...
Reference Manual for the Model RP614 Web Safe Router
... Federal Communications Commission (FCC) Compliance Notice: Radio Frequency Notice This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interfer ...
... Federal Communications Commission (FCC) Compliance Notice: Radio Frequency Notice This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interfer ...
Point-to-Point Protocol (PPP)
... The first phase of LCP operation is link establishment. This phase must complete successfully, before any Network layer packets can be exchanged. During link establishment, the LCP opens the connection and negotiates the configuration parameters. The link establishment process starts with the initia ...
... The first phase of LCP operation is link establishment. This phase must complete successfully, before any Network layer packets can be exchanged. During link establishment, the LCP opens the connection and negotiates the configuration parameters. The link establishment process starts with the initia ...
Xerox Secure Access EIP2 Manual
... NOTE: The FujiXerox devices available in the Asia-Pacific region do not support EIP. These devices can instead make use of the Network Accounting features to control access to the copier. See the PaperCut Xerox Network Accounting Embedded manual for information. NOTE*: The 57xx series mentioned abov ...
... NOTE: The FujiXerox devices available in the Asia-Pacific region do not support EIP. These devices can instead make use of the Network Accounting features to control access to the copier. See the PaperCut Xerox Network Accounting Embedded manual for information. NOTE*: The 57xx series mentioned abov ...
IMTC H.323 Forum Launch
... were designed in such a way that both media and call control were handled by the ...
... were designed in such a way that both media and call control were handled by the ...
Attack Detection and Defense Mechanisms
... The terms and conditions for using this software are described in the software license contained in the acknowledgment to your purchase order or, to the extent applicable, to any reseller agreement or end-user purchase agreement executed between you and Juniper Networks. By using this software, you ...
... The terms and conditions for using this software are described in the software license contained in the acknowledgment to your purchase order or, to the extent applicable, to any reseller agreement or end-user purchase agreement executed between you and Juniper Networks. By using this software, you ...
NAT - Hong Kong University of Science and Technology
... isolates organization’s internal net from open Internet, protect the local network from being accessed by unauthorized sources ...
... isolates organization’s internal net from open Internet, protect the local network from being accessed by unauthorized sources ...
Model FVL328 ProSafe High-Speed VPN Firewall Reference
... This equipment is in the second category (information equipment to be used in a residential area or an adjacent area thereto), and conforms to the standards set by the Voluntary Control Council for Interference by Data Processing Equipment and Electronic Office Machines, aimed at preventing radio in ...
... This equipment is in the second category (information equipment to be used in a residential area or an adjacent area thereto), and conforms to the standards set by the Voluntary Control Council for Interference by Data Processing Equipment and Electronic Office Machines, aimed at preventing radio in ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.



![Wiley Publishing - CCNA For Dummies [2000].](http://s1.studyres.com/store/data/008049680_1-a9b72081a3d6e4abe69a6bd824c30e5a-300x300.png)