Clavister Virtual Core
... We strive to make things easy to understand and easy to use. This includes everything from hardware design to security management. We build highly customizable enterprise-grade firewalls, and despite the inherent complexity, we make an effort of making it easy to use. For example, our highly acclaim ...
... We strive to make things easy to understand and easy to use. This includes everything from hardware design to security management. We build highly customizable enterprise-grade firewalls, and despite the inherent complexity, we make an effort of making it easy to use. For example, our highly acclaim ...
PaperCut Konica Minolta Standard UI Embedded Manual
... “PKI Settings” subsection, please ignore this section and refer to Appendix A instead for configuration of older devices. Create a new certificate following these steps. (Even if a certificate is already shown in the “Device Certificate List”, this certificate may not be usable for SSL. Please delet ...
... “PKI Settings” subsection, please ignore this section and refer to Appendix A instead for configuration of older devices. Create a new certificate following these steps. (Even if a certificate is already shown in the “Device Certificate List”, this certificate may not be usable for SSL. Please delet ...
BSG 8ew 1.0 Solution Guide
... network and involve several components. The components involved in the architecture are the Communication Servers (CS2000), Media Gateways, Signaling Gateways, and CPE devices. They are interconnected through the Managed IP network that can be viewed as a core network that is managed by the service ...
... network and involve several components. The components involved in the architecture are the Communication Servers (CS2000), Media Gateways, Signaling Gateways, and CPE devices. They are interconnected through the Managed IP network that can be viewed as a core network that is managed by the service ...
MEF Global Interconnect Briefing
... • Intention – These MEF reference presentations are intended to give general overviews of the MEF work and have been approved by the MEF Marketing Committee – Further details on the topic are to be found in related specifications, technical overviews, white papers in the MEF public site Information ...
... • Intention – These MEF reference presentations are intended to give general overviews of the MEF work and have been approved by the MEF Marketing Committee – Further details on the topic are to be found in related specifications, technical overviews, white papers in the MEF public site Information ...
JTC 1 Security and Privacy
... SC 27 is an internationally recognized centre of information and IT security standards expertise serving the needs of business sectors as well as governments. Its work covers the development of standards for the protection of information and ICT. This includes requirements, methods, techniques and g ...
... SC 27 is an internationally recognized centre of information and IT security standards expertise serving the needs of business sectors as well as governments. Its work covers the development of standards for the protection of information and ICT. This includes requirements, methods, techniques and g ...
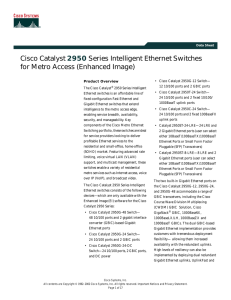
Cisco Catalyst 2950 Series Intelligent Ethernet
... To implement QoS, first, the Cisco Catalyst 2950 Series switches identify traffic flows, or packet groups, and classify or reclassify these groups using either the Differentiated Services Code Point (DSCP) field or the 802.1p class-of-service (CoS) field, or both. Classification and reclassification ...
... To implement QoS, first, the Cisco Catalyst 2950 Series switches identify traffic flows, or packet groups, and classify or reclassify these groups using either the Differentiated Services Code Point (DSCP) field or the 802.1p class-of-service (CoS) field, or both. Classification and reclassification ...
Solaris 10 - Center for Internet Security
... for any software Product that is not already in the form of source code; (ii) distribute, redistribute, encumber, sell, rent, lease, lend, sublicense, or otherwise transfer or exploit rights to any Product or any component of a Product; (iii) post any Product or any component of a Product on any web ...
... for any software Product that is not already in the form of source code; (ii) distribute, redistribute, encumber, sell, rent, lease, lend, sublicense, or otherwise transfer or exploit rights to any Product or any component of a Product; (iii) post any Product or any component of a Product on any web ...
ISA Server Product Guide
... network connectivity are managed independently, and that they sometimes even conflict with each other. This could result in incorrect business decisions or sub-optimal resource allocation. For example, if users complain about slow Internet connectivity, the person responsible for caching may invest ...
... network connectivity are managed independently, and that they sometimes even conflict with each other. This could result in incorrect business decisions or sub-optimal resource allocation. For example, if users complain about slow Internet connectivity, the person responsible for caching may invest ...
TDC 563-98-301/302, Spring 2002 2-14 TDC 563-98
... •Database Description: When a router just came up, it cannot wait for all link state packets. Neighbors will send it a database description (not the full database but like an outline). From this, the router can then ask for information it does not have. Describes the contents of the topological data ...
... •Database Description: When a router just came up, it cannot wait for all link state packets. Neighbors will send it a database description (not the full database but like an outline). From this, the router can then ask for information it does not have. Describes the contents of the topological data ...
(IP) routers
... sustainable network by functioning as a shared backup router. • Current commercial routers was not virtualized but implemented as a proprietary hardware and software. ...
... sustainable network by functioning as a shared backup router. • Current commercial routers was not virtualized but implemented as a proprietary hardware and software. ...
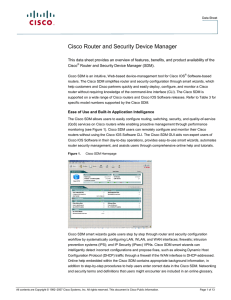
Cloud and Network Services
... SDM offers advanced configuration tools to quickly configure and fine-tune router security features, allowing network professionals to review the commands generated by the Cisco SDM before delivering the configuration changes to the router. The Cisco SDM helps administrators configure and monitor ro ...
... SDM offers advanced configuration tools to quickly configure and fine-tune router security features, allowing network professionals to review the commands generated by the Cisco SDM before delivering the configuration changes to the router. The Cisco SDM helps administrators configure and monitor ro ...
cis185-ROUTE-lecture2-EIGRP-Part2
... A switched WAN technology Virtual circuits (VCs) are created by a Service Provider (SP) Multiple logical VCs to be multiplexed over a single physical interface. Typically PVCs identified by a locally significant data link connection ...
... A switched WAN technology Virtual circuits (VCs) are created by a Service Provider (SP) Multiple logical VCs to be multiplexed over a single physical interface. Typically PVCs identified by a locally significant data link connection ...
Technical Presentation
... SIP Protocol is an Application Layer Protocol Network Address Translation (NAT) resides at the Transport Layer (TCP/IP) NAT will not change the SIP addressing within the TCP/UDP datagram Firewalls are a NATing device and BLOCK all Incoming SIP Traffic to the LAN Any NAT device, either Far End (remot ...
... SIP Protocol is an Application Layer Protocol Network Address Translation (NAT) resides at the Transport Layer (TCP/IP) NAT will not change the SIP addressing within the TCP/UDP datagram Firewalls are a NATing device and BLOCK all Incoming SIP Traffic to the LAN Any NAT device, either Far End (remot ...
Ingate Firewall & SIParator Training
... SIP Protocol is an Application Layer Protocol Network Address Translation (NAT) resides at the Transport Layer (TCP/IP) NAT will not change the SIP addressing within the TCP/UDP datagram Firewalls are a NATing device and BLOCK all Incoming SIP Traffic to the LAN Any NAT device, either Far End (remot ...
... SIP Protocol is an Application Layer Protocol Network Address Translation (NAT) resides at the Transport Layer (TCP/IP) NAT will not change the SIP addressing within the TCP/UDP datagram Firewalls are a NATing device and BLOCK all Incoming SIP Traffic to the LAN Any NAT device, either Far End (remot ...
Recent Advances in Computer Networking including ATM
... ! Ethernet was and is cheaper than 10 one-Mbps links. ! No FDDI if it is 10 times as expensive as Ethernet. 10/100 Ethernet adapters = $50 over 10 Mbps ...
... ! Ethernet was and is cheaper than 10 one-Mbps links. ! No FDDI if it is 10 times as expensive as Ethernet. 10/100 Ethernet adapters = $50 over 10 Mbps ...
Cisco TrustSec How-To Guide: Segmenting Clients and Servers in
... Virtual server - physical server segmentation using SGFW (Figure 2). For this use case, we will deny all network traffic between the engineering server connected to the Cisco Nexus 7000 distribution switch and the virtual servers hosted behind the Cisco Nexus 7000 end-of-row switch. While SGFW is th ...
... Virtual server - physical server segmentation using SGFW (Figure 2). For this use case, we will deny all network traffic between the engineering server connected to the Cisco Nexus 7000 distribution switch and the virtual servers hosted behind the Cisco Nexus 7000 end-of-row switch. While SGFW is th ...
Document
... • Other two routers are drop routers connected to client devices. • Two connections from the network port at the ingress service router to two drop ports, one in each of the drop routers. Client device sends 50% of the traffic on one of these drop interfaces and 50% on the other (it is attached to b ...
... • Other two routers are drop routers connected to client devices. • Two connections from the network port at the ingress service router to two drop ports, one in each of the drop routers. Client device sends 50% of the traffic on one of these drop interfaces and 50% on the other (it is attached to b ...
2014-06 WLAN 9100 Learning_Bytes
... apply QoS to applications directly at the Network Edge This reduces network load and ensures ...
... apply QoS to applications directly at the Network Edge This reduces network load and ensures ...
6LoWPAN: The Wireless Embedded Internet
... For details of our global editorial offices, for customer services and for information about how to apply for permission to reuse the copyright material in this book please see our website at www.wiley.com. The right of the author to be identified as the author of this work has been asserted in acco ...
... For details of our global editorial offices, for customer services and for information about how to apply for permission to reuse the copyright material in this book please see our website at www.wiley.com. The right of the author to be identified as the author of this work has been asserted in acco ...
BACnet in China
... • BACnet’s advantage is that the same protocol can operate at multiple levels ― from the field, to the automation and up to the enterprise • At the automation level there are operator workstations, building controllers and advanced application controllers running BACnet/IP • At the field level there ...
... • BACnet’s advantage is that the same protocol can operate at multiple levels ― from the field, to the automation and up to the enterprise • At the automation level there are operator workstations, building controllers and advanced application controllers running BACnet/IP • At the field level there ...
ppt
... – Is a router tracking each attached peer? – Should clients respond immediately to membership queries? – What if local networks are layer-two switched? ...
... – Is a router tracking each attached peer? – Should clients respond immediately to membership queries? – What if local networks are layer-two switched? ...
Tsunami 8000 Series (Point-to-point and Point-to
... The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to refer to, endorse, or promote the products or for any other purpose related to the products without prior written permission. For written permission, please contact [email protected]. This software is provided by the OpenSS ...
... The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to refer to, endorse, or promote the products or for any other purpose related to the products without prior written permission. For written permission, please contact [email protected]. This software is provided by the OpenSS ...
Chapter16-PresentationDistilled
... organization. It turns out that more than three quarters of external actors are affiliated with organized crime or nation states. • Partner actors are affiliated with an organization that you partner or work with. Quite often partners are granted some access to each other’s systems (to place orders, ...
... organization. It turns out that more than three quarters of external actors are affiliated with organized crime or nation states. • Partner actors are affiliated with an organization that you partner or work with. Quite often partners are granted some access to each other’s systems (to place orders, ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.