Mobile Commerce: The Business of Time
... • Link manager protocol (LMP) is a Bluetooth layer that sets up ongoing link management with Bluetooth devices ...
... • Link manager protocol (LMP) is a Bluetooth layer that sets up ongoing link management with Bluetooth devices ...
Useful Tips for Reducing the Risk of Unauthorized Access
... This guide provides additional information related to the Canon Network Cameras, and in particular, steps you can take to enhance the secure operation of this device. This document will help you better understand how the device functions and will help you feel confident that it operates, stores or t ...
... This guide provides additional information related to the Canon Network Cameras, and in particular, steps you can take to enhance the secure operation of this device. This document will help you better understand how the device functions and will help you feel confident that it operates, stores or t ...
CE9 - aes journals
... A wireless ad hoc network is a collection of mobile nodes equipped with wireless transceivers that can work without any fixed networking infrastructure [1]. A node can transmit data packets to other nodes who are within its radio coverage range directly, and who are outside the range via multi-hop s ...
... A wireless ad hoc network is a collection of mobile nodes equipped with wireless transceivers that can work without any fixed networking infrastructure [1]. A node can transmit data packets to other nodes who are within its radio coverage range directly, and who are outside the range via multi-hop s ...
MJ-CV-1 - Snap Tech IT
... Supported and maintained PCs, monitors, laptops and printers. Installed and upgraded applications, antivirus, applied security updates, patches, service packs and drivers, added printers, configured desktops and migrated users/customers’ profile and data from old ones. Installed, configured, m ...
... Supported and maintained PCs, monitors, laptops and printers. Installed and upgraded applications, antivirus, applied security updates, patches, service packs and drivers, added printers, configured desktops and migrated users/customers’ profile and data from old ones. Installed, configured, m ...
ATmedia GmbH
... • Privately owned and independent German company • Development, production and distribution of high-speed network security products • Encryption products up to 10G with a BSI/NATO/EU approvals ...
... • Privately owned and independent German company • Development, production and distribution of high-speed network security products • Encryption products up to 10G with a BSI/NATO/EU approvals ...
Access Controller - Scoop Distribution
... Access Point Auto Discovery Access Point Auto IP Assignment Access Point Device Name Editing Access Point SSID Editing Access Point Client Limit Editing Access Point output power Editting Access Point Security Editting (None,WPA-PSK,WPA2-PSK) Access Point isolation Editting Access Point SSID isolati ...
... Access Point Auto Discovery Access Point Auto IP Assignment Access Point Device Name Editing Access Point SSID Editing Access Point Client Limit Editing Access Point output power Editting Access Point Security Editting (None,WPA-PSK,WPA2-PSK) Access Point isolation Editting Access Point SSID isolati ...
Support: Ticket, Process, and Expectations
... Be careful to not connect unless you are reasonably sure it is a legitimate WiFi (e.g., one that is provided by the business) Why is it safe to use BTOTS Web over a legitimate public or personal WiFi: BTOTS requires an secure (HTTPS) connection for you to work with it Communication with BTOTS Web ...
... Be careful to not connect unless you are reasonably sure it is a legitimate WiFi (e.g., one that is provided by the business) Why is it safe to use BTOTS Web over a legitimate public or personal WiFi: BTOTS requires an secure (HTTPS) connection for you to work with it Communication with BTOTS Web ...
11-Operating Systems Security
... – 70% of intrusion studied by 2009 could be prevented with 4 measures • Patch operating systems and applications using auto-update • Patch 3rd party applications • Restrict admin privileges to users who need them – Disable root on linux (only via sudoers groups users may gain root privileges) – Crea ...
... – 70% of intrusion studied by 2009 could be prevented with 4 measures • Patch operating systems and applications using auto-update • Patch 3rd party applications • Restrict admin privileges to users who need them – Disable root on linux (only via sudoers groups users may gain root privileges) – Crea ...
PDF
... Sensing Unit: Sensing units are usually composed of two subunits: sensors and analog to digital converters (ADCs). Sensor is a device which is used to translate physical phenomena to electrical signals. Processing Unit: The processing unit mainly provides intelligence to the sensor node. The process ...
... Sensing Unit: Sensing units are usually composed of two subunits: sensors and analog to digital converters (ADCs). Sensor is a device which is used to translate physical phenomena to electrical signals. Processing Unit: The processing unit mainly provides intelligence to the sensor node. The process ...
Linux+ Guide to Linux Certification
... • WPANs encompass technology that is designed for portable devices, typically PDAs, cell phones, and tablet or laptop computers at transmission speeds lower than the other types of networks • The IEEE 802.15 standards address wireless personal area networks • RFID is not a standard but is a technolo ...
... • WPANs encompass technology that is designed for portable devices, typically PDAs, cell phones, and tablet or laptop computers at transmission speeds lower than the other types of networks • The IEEE 802.15 standards address wireless personal area networks • RFID is not a standard but is a technolo ...
comp412p1
... • Topology: How the devices in the network (called nodes) are arranged – Star networks: A network that uses a host device connected directly to several other devices – Bus networks: A network consisting of a central cable to which all network devices are attached – Mesh networks: A network in which ...
... • Topology: How the devices in the network (called nodes) are arranged – Star networks: A network that uses a host device connected directly to several other devices – Bus networks: A network consisting of a central cable to which all network devices are attached – Mesh networks: A network in which ...
NETWORKING LAB -
... The fundamental difference between a router and a Layer 3 switch is that Layer 3 switches have optimized hardware to pass data as fast as Layer 2 switches, yet they make decisions on how to transmit traffic at Layer 3, just like a router. Within the LAN environment, a Layer 3 switch is usually faste ...
... The fundamental difference between a router and a Layer 3 switch is that Layer 3 switches have optimized hardware to pass data as fast as Layer 2 switches, yet they make decisions on how to transmit traffic at Layer 3, just like a router. Within the LAN environment, a Layer 3 switch is usually faste ...
networkworld - Sift Security
... As soon as a customer installs the Sift Security software (on premises or on AWS using commodity hardware), the platform begins to ingest data from whatever sources are pointed to it. These can be existing logs or custom or proprietary logs. Since Sift Security's software isn't priced according to d ...
... As soon as a customer installs the Sift Security software (on premises or on AWS using commodity hardware), the platform begins to ingest data from whatever sources are pointed to it. These can be existing logs or custom or proprietary logs. Since Sift Security's software isn't priced according to d ...
Web Server Administration
... A proxy server delivers content on behalf of a user or server application Proxy servers need to understand the protocol of the application that they proxy such as HTTP or FTP Forward proxy servers isolate users from the Internet ...
... A proxy server delivers content on behalf of a user or server application Proxy servers need to understand the protocol of the application that they proxy such as HTTP or FTP Forward proxy servers isolate users from the Internet ...
Linux OS Concepts
... or from a private network. Firewalls can be implemented in both hardware and software, or a combination of both. Firewalls are frequently used to prevent unauthorized Internet users from accessing private networks connected to the Internet, especially intranets. All messages entering or leaving the ...
... or from a private network. Firewalls can be implemented in both hardware and software, or a combination of both. Firewalls are frequently used to prevent unauthorized Internet users from accessing private networks connected to the Internet, especially intranets. All messages entering or leaving the ...
researchtalk2004
... only send to nearest base station hop-by-hop, not end-to-end reliability short packets, very low overhead ...
... only send to nearest base station hop-by-hop, not end-to-end reliability short packets, very low overhead ...
Cyber Security in Evolving Enterprise
... • BotNet Detection and Mitigation • Tight Access Control to Identify Sources of Malware ...
... • BotNet Detection and Mitigation • Tight Access Control to Identify Sources of Malware ...
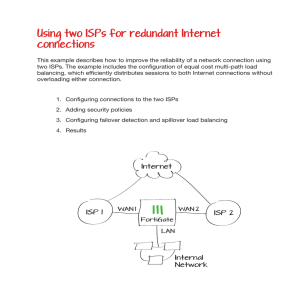
Using two ISPs for redundant Internet connections
... This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without overloading either connection. ...
... This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without overloading either connection. ...
Wireless Networks
... host: must associate with an AP scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication [Chapter 8] will typically run DHCP to get IP address in AP’s ...
... host: must associate with an AP scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication [Chapter 8] will typically run DHCP to get IP address in AP’s ...
(FIPS) 140-2 - Aviat Networks
... • Mandates identity-based authentication, tamper evidence, etc) • Level 3 and 4: VERY STRONG • Must be pick-resistant, tamper-proof. Adds large cost and complexity to product to ...
... • Mandates identity-based authentication, tamper evidence, etc) • Level 3 and 4: VERY STRONG • Must be pick-resistant, tamper-proof. Adds large cost and complexity to product to ...
Chapter 5
... An extremely weak form of wireless network security is to turn off the broadcast of the SSID. While to the average user there does not appear to be a network in use, a network protected in this way is still easily accessed by crackers using the appropriate tools. Other forms of encryption and authen ...
... An extremely weak form of wireless network security is to turn off the broadcast of the SSID. While to the average user there does not appear to be a network in use, a network protected in this way is still easily accessed by crackers using the appropriate tools. Other forms of encryption and authen ...
Chapter03-1 |
... Band (Ptcl, World Call, Wateen) technologies often link together a wired PAN. While wireless PANs typically use Bluetooth or sometimes infrared connections. Bluetooth PANs are also called piconets. Personal area networks generally cover a range of less than 10 meters. ...
... Band (Ptcl, World Call, Wateen) technologies often link together a wired PAN. While wireless PANs typically use Bluetooth or sometimes infrared connections. Bluetooth PANs are also called piconets. Personal area networks generally cover a range of less than 10 meters. ...
CMPE 155 - University of California, Santa Cruz
... Observations Service-specific filtering based on client using non-privileged port to contact privileged server port. FTP uses 2 TCP connections: one for control and another for data. ...
... Observations Service-specific filtering based on client using non-privileged port to contact privileged server port. FTP uses 2 TCP connections: one for control and another for data. ...
Cisco RV110W Wireless
... The Cisco RV110W Wireless-N VPN Firewall provides simple, affordable, highly secure, business-class connectivity to the Internet for small offices/home offices and remote workers. The Cisco RV110W combines wired and wireless connectivity for small offices and remote workers with a highspeed, 802.11n ...
... The Cisco RV110W Wireless-N VPN Firewall provides simple, affordable, highly secure, business-class connectivity to the Internet for small offices/home offices and remote workers. The Cisco RV110W combines wired and wireless connectivity for small offices and remote workers with a highspeed, 802.11n ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.