Security Technology-I
... • Frequently installed on a dedicated computer; also known as a proxy server • Since proxy server is often placed in unsecured area of the network (e.g., DMZ), it is exposed to higher levels of risk from less trusted networks • Additional filtering routers can be implemented behind the proxy server, ...
... • Frequently installed on a dedicated computer; also known as a proxy server • Since proxy server is often placed in unsecured area of the network (e.g., DMZ), it is exposed to higher levels of risk from less trusted networks • Additional filtering routers can be implemented behind the proxy server, ...
muhammad usman
... WiMAX / OFC Field Engineer in Wateen Telecom Ltd. (A company by Abu Dhabi Group in Pakistan) Duration: Jan 2008 to Aug 2009 The responsibilities were: As WiMAX RAN engineer in operation and maintenance department and look after more than 60 BTS sites. Wateen using equipment of Motorola (BTS Equipm ...
... WiMAX / OFC Field Engineer in Wateen Telecom Ltd. (A company by Abu Dhabi Group in Pakistan) Duration: Jan 2008 to Aug 2009 The responsibilities were: As WiMAX RAN engineer in operation and maintenance department and look after more than 60 BTS sites. Wateen using equipment of Motorola (BTS Equipm ...
pdf
... Authorized licensed use limited to: Old Dominion University. Downloaded on October 12, 2008 at 16:56 from IEEE Xplore. Restrictions apply. ...
... Authorized licensed use limited to: Old Dominion University. Downloaded on October 12, 2008 at 16:56 from IEEE Xplore. Restrictions apply. ...
Chapter 05
... It can be an expensive process though. ◦ In 2006 an EAL4 rating takes 2 years and $350,000 for a product. ...
... It can be an expensive process though. ◦ In 2006 an EAL4 rating takes 2 years and $350,000 for a product. ...
Ethernet Types Media Max segment length Connector
... regenerating clear signals Can handle multiple frame forwarding/filtering simultaneously. May offer VLAN (Virtual LAN) features Can support full-deplex mode Switch works in layer 2. ...
... regenerating clear signals Can handle multiple frame forwarding/filtering simultaneously. May offer VLAN (Virtual LAN) features Can support full-deplex mode Switch works in layer 2. ...
Cisco Discovery 1 Module 03 Quiz Picture Descriptions
... the IP phone? (Choose two.) The diagram depicts an IP telephone connected to a switch. Also connected to the switch are two computers, directly connected to pne of the computers is a standalone printer. ...
... the IP phone? (Choose two.) The diagram depicts an IP telephone connected to a switch. Also connected to the switch are two computers, directly connected to pne of the computers is a standalone printer. ...
cvfeb2016_cloud - Edwin Hernandez, PhD
... Research Assistant, University of Florida, Gainesville, FL, Jan’00 – Aug ’02 Experience: I investigated the effects of handoff and network mobility at different vehicular speeds. I used Mobile network simulation and emulation were important tools to study MobileIP and Layer-2/3 mobility protocols. I ...
... Research Assistant, University of Florida, Gainesville, FL, Jan’00 – Aug ’02 Experience: I investigated the effects of handoff and network mobility at different vehicular speeds. I used Mobile network simulation and emulation were important tools to study MobileIP and Layer-2/3 mobility protocols. I ...
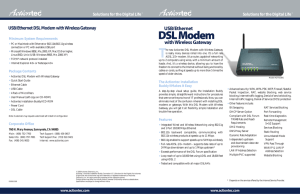
USB/Ethernet DSL Modem With Wireless Gateway
... header is prepended to the (Ethernet) frame • VC multiplexing, in which a null two byte header is prepended to the frame. Default is LLC encapsulation; VC multiplexing can be configured using console command or WEB ...
... header is prepended to the (Ethernet) frame • VC multiplexing, in which a null two byte header is prepended to the frame. Default is LLC encapsulation; VC multiplexing can be configured using console command or WEB ...
SAC Conference Tutorial
... LAN-based Systems » Call setup via LAN call processing server » Call path between all peripherals via LAN ...
... LAN-based Systems » Call setup via LAN call processing server » Call path between all peripherals via LAN ...
UoD_CISCO Networking Academy
... advanced functionality. By the end of this course, participants will be able to configure and troubleshoot routers and switches and resolve common issues with OSPF, EIGRP, and STP in both IPv4 and IPv6 networks. Participants will also develop the knowledge and skills needed to implement a WLAN in a ...
... advanced functionality. By the end of this course, participants will be able to configure and troubleshoot routers and switches and resolve common issues with OSPF, EIGRP, and STP in both IPv4 and IPv6 networks. Participants will also develop the knowledge and skills needed to implement a WLAN in a ...
Bit9
... successful breaches of corporate networks required only the most basic techniques. Hacking tools are easily acquired from the Internet, including tools that "crack" passwords in minutes. But consider this: a vast majority of hacks are stunningly simple to deflect with 4 simple steps ...
... successful breaches of corporate networks required only the most basic techniques. Hacking tools are easily acquired from the Internet, including tools that "crack" passwords in minutes. But consider this: a vast majority of hacks are stunningly simple to deflect with 4 simple steps ...
Review of Researches in Controller Area Networks Evolution and
... advanced serial communication protocol which effectively supports distributed realtime control. Ideally, CAN is suitable in application requiring a large number of short messages with high reliability in rugged environment. These characteristics along with many others, allows wide opportunity in dev ...
... advanced serial communication protocol which effectively supports distributed realtime control. Ideally, CAN is suitable in application requiring a large number of short messages with high reliability in rugged environment. These characteristics along with many others, allows wide opportunity in dev ...
Week_Three_Network_ppt - Computing Sciences
... • When considering protocol behavior, what is the difference between relative network utilization and absolute network utilization? • Why should you characterize the logical structure of an internetwork and not just the physical structure? • What architectural and environmental factors should you co ...
... • When considering protocol behavior, what is the difference between relative network utilization and absolute network utilization? • Why should you characterize the logical structure of an internetwork and not just the physical structure? • What architectural and environmental factors should you co ...
Tutorial on QoS In WLAN
... than EDCA. • Combines the advantages of PCF and DCF. • Coordinates the traffic in any fashion (not just round- robin). ...
... than EDCA. • Combines the advantages of PCF and DCF. • Coordinates the traffic in any fashion (not just round- robin). ...
wireless network fixed network
... primitive caching (often disabled, dynamic objects) security problems (using SSL/TLS with proxies) ...
... primitive caching (often disabled, dynamic objects) security problems (using SSL/TLS with proxies) ...
Acceptable Use Policy for Technology
... a. Connecting a personal device to the RACS network provides access to filtered Internet and access to the student portal which allows access to web-based RACS resources. Access to the Internet will be filtered according to school policy. b. The preferred personal device is a netbook or laptop as th ...
... a. Connecting a personal device to the RACS network provides access to filtered Internet and access to the student portal which allows access to web-based RACS resources. Access to the Internet will be filtered according to school policy. b. The preferred personal device is a netbook or laptop as th ...
45.3% of employees are aware that their workplace can be
... ■ Device used to communicate business emails: Desktop PC provided by company (46.1%); Laptop PC provided by company (37.9%); Personal smartphone (13.6%). ■ In terms of security policies in the workplace, 60.7% said “yes, we have security policies”, 31.3% said “no, we do not have policies”, and 8.0% ...
... ■ Device used to communicate business emails: Desktop PC provided by company (46.1%); Laptop PC provided by company (37.9%); Personal smartphone (13.6%). ■ In terms of security policies in the workplace, 60.7% said “yes, we have security policies”, 31.3% said “no, we do not have policies”, and 8.0% ...
Wireless Mesh Networks Challenges and Opportunities
... Nodes can use a control channel to coordinate and the rest to exchange data. In some conditions can be very efficient. However the control channel can be: an unacceptable ...
... Nodes can use a control channel to coordinate and the rest to exchange data. In some conditions can be very efficient. However the control channel can be: an unacceptable ...
Wireless Communication Systems
... not suitable for sensor networks. First of all, power management is a “pervasive” issue in the overall design of a sensor network. Sensor networks utilize on-board batteries with limited energy that cannot be replenished in most ...
... not suitable for sensor networks. First of all, power management is a “pervasive” issue in the overall design of a sensor network. Sensor networks utilize on-board batteries with limited energy that cannot be replenished in most ...
Lecture 8 - Bhecker.com
... • Digital signature: A digital code attached to an electronically transmitted message that is used to verify the origin and contents of a message • Digital certificates: Data files used to establish the identity of users and electronic assets for protection of online transactions • Public Key Infras ...
... • Digital signature: A digital code attached to an electronically transmitted message that is used to verify the origin and contents of a message • Digital certificates: Data files used to establish the identity of users and electronic assets for protection of online transactions • Public Key Infras ...
Presentation Prepared By: Raghda Zahran
... Firewalls and network security mechanisms Intrusion detection systems Security configuration settings Anti-viral software Smart cards ...
... Firewalls and network security mechanisms Intrusion detection systems Security configuration settings Anti-viral software Smart cards ...
Assets, Threats and Vulnerabilities: Discovery and
... entire networks in a non-intrusive mode. Under direct control of the user, this process automatically scans the network, using standard protocols to find and label all devices, such as computers, routers, firewalls and printers. Expert 4.1 also identifies operating systems, active services, and soft ...
... entire networks in a non-intrusive mode. Under direct control of the user, this process automatically scans the network, using standard protocols to find and label all devices, such as computers, routers, firewalls and printers. Expert 4.1 also identifies operating systems, active services, and soft ...
Windows Server 2012 Network Setup For TCP/IP
... Windows Server 2012 Network Setup For TCP/IP For offices NOT using Patterson branded hardware, we recommend a professional trained in installation and maintenance of a Windows Server 2012 system be employed to set up machines running a Windows Server 2012. TCP/IP network setup is required on Windows ...
... Windows Server 2012 Network Setup For TCP/IP For offices NOT using Patterson branded hardware, we recommend a professional trained in installation and maintenance of a Windows Server 2012 system be employed to set up machines running a Windows Server 2012. TCP/IP network setup is required on Windows ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.