CCNA - Cisco Certified Network Associate
... review questionnaires within the course. The goal of the reviews is to provide a mechanism to reinforce the material covered during the course rather than simply testing how much a student has taken in on the first pass. Live equipment, including Cisco 2500 and 2600 routers and 1900 switches, serve ...
... review questionnaires within the course. The goal of the reviews is to provide a mechanism to reinforce the material covered during the course rather than simply testing how much a student has taken in on the first pass. Live equipment, including Cisco 2500 and 2600 routers and 1900 switches, serve ...
automatically trigger packet capture from solarwinds® network
... it to any security or monitoring appliance. This approach provides efficient access to asymmetric traffic across large heterogeneous networks. The NTO filters out traffic, which does not need analysis, prior to consuming resources on monitoring appliances. The NTO can share traffic from a network ac ...
... it to any security or monitoring appliance. This approach provides efficient access to asymmetric traffic across large heterogeneous networks. The NTO filters out traffic, which does not need analysis, prior to consuming resources on monitoring appliances. The NTO can share traffic from a network ac ...
Speed Up Incident Response with Actionable Forensic Analytics
... were notified by external entities after it was already too late to save the reputation of the company. Security breaches can have a devastating impact on any company. For example, in the Target breach alone, 40 million credit/debit card data records and 70 million total data records were stolen in ...
... were notified by external entities after it was already too late to save the reputation of the company. Security breaches can have a devastating impact on any company. For example, in the Target breach alone, 40 million credit/debit card data records and 70 million total data records were stolen in ...
646-203 Cisco Cisco Sales Expert Visit: http://www.pass4sureofficial
... and leased lines in a single platform, allowing service providers to offer multiple types of services to end users without having to maintain multiple edge devices? A. 3600 Series B. 7600 Series C. 10000 Series D. 15000 Series Answer: C QUESTION 8 Which benefit does storage networking provide? ...
... and leased lines in a single platform, allowing service providers to offer multiple types of services to end users without having to maintain multiple edge devices? A. 3600 Series B. 7600 Series C. 10000 Series D. 15000 Series Answer: C QUESTION 8 Which benefit does storage networking provide? ...
Pass4sure 646
... and leased lines in a single platform, allowing service providers to offer multiple types of services to end users without having to maintain multiple edge devices? A. 3600 Series B. 7600 Series C. 10000 Series D. 15000 Series Answer: C QUESTION 8 Which benefit does storage networking provide? ...
... and leased lines in a single platform, allowing service providers to offer multiple types of services to end users without having to maintain multiple edge devices? A. 3600 Series B. 7600 Series C. 10000 Series D. 15000 Series Answer: C QUESTION 8 Which benefit does storage networking provide? ...
User Guide
... Installing the HG659 on an Ethernet Broadband Network In some communities, network service providers use Ethernet interfaces as Internet interfaces. On this network, your PC is directly connected to the Internet through the Ethernet interface provided by the network service provider. If you have sub ...
... Installing the HG659 on an Ethernet Broadband Network In some communities, network service providers use Ethernet interfaces as Internet interfaces. On this network, your PC is directly connected to the Internet through the Ethernet interface provided by the network service provider. If you have sub ...
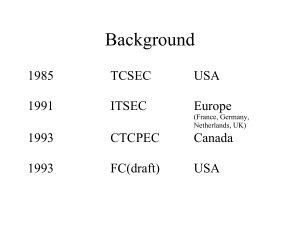
Common Criteria
... classes of network and system attacks, interoperability and compatibility with the defense-in-depth strategy, and IA solutions that should be considered to counter attacks. 5.2.21. Acquire IA solutions that have been evaluated using the Common Criteria Evaluation and Validation Scheme based on the N ...
... classes of network and system attacks, interoperability and compatibility with the defense-in-depth strategy, and IA solutions that should be considered to counter attacks. 5.2.21. Acquire IA solutions that have been evaluated using the Common Criteria Evaluation and Validation Scheme based on the N ...
Develop Security Framework - NSW Department of Education
... Reconnaissance is where a potential threat checks out a system for vulnerable points to enter. If successful, denial of service or data manipulation can result. Reconnaissance is also known as information gathering. The intruder may ping sweep the target network for live IP addresses. Next, a port s ...
... Reconnaissance is where a potential threat checks out a system for vulnerable points to enter. If successful, denial of service or data manipulation can result. Reconnaissance is also known as information gathering. The intruder may ping sweep the target network for live IP addresses. Next, a port s ...
Review For Final - Eastern Illinois University
... and WordProcessings. The Network administrator assigns user Lee to the group Outer. The administrator assigns Outer the access rights R, S, and T in Directory Applications. (Don’t worry about the meaning of R, S, and T. They are simply types of rights.) The administrator assigns Outer the access rig ...
... and WordProcessings. The Network administrator assigns user Lee to the group Outer. The administrator assigns Outer the access rights R, S, and T in Directory Applications. (Don’t worry about the meaning of R, S, and T. They are simply types of rights.) The administrator assigns Outer the access rig ...
Training
... Random Access - like a meeting without a chairperson - collisions can occur but the protocol does something to address this. ...
... Random Access - like a meeting without a chairperson - collisions can occur but the protocol does something to address this. ...
address - Information Services and Technology
... • Wireless communications compelling Easy, low-cost deployment Mobility & roaming: Access information anywhere Supports personal devices ...
... • Wireless communications compelling Easy, low-cost deployment Mobility & roaming: Access information anywhere Supports personal devices ...
hosts
... • NIC encapsulates source & dest. MAC • Host that receives frame reads dest. MAC – If it contains its own MAC, it will process it – If not, it ignores it ...
... • NIC encapsulates source & dest. MAC • Host that receives frame reads dest. MAC – If it contains its own MAC, it will process it – If not, it ignores it ...
IPSec
... IPSec is an abbreviation for IP security, which is used to transfer data securely over unprotected networks like “Internet”. It acts at the networks layer and is part of IPv6. The protocol/process is as follows : Sender encrypts packets before sending them on the network. Receiver authenti ...
... IPSec is an abbreviation for IP security, which is used to transfer data securely over unprotected networks like “Internet”. It acts at the networks layer and is part of IPv6. The protocol/process is as follows : Sender encrypts packets before sending them on the network. Receiver authenti ...
Slide 1
... (fake) source address. – To hide the identity of the attacker. – If the address is used by a real host, the host whose address was spoofed will receive the SYN/ACK packet from the target. Since the host never initiated a connection, it will send a RST packet to the target to refuse a connection. The ...
... (fake) source address. – To hide the identity of the attacker. – If the address is used by a real host, the host whose address was spoofed will receive the SYN/ACK packet from the target. Since the host never initiated a connection, it will send a RST packet to the target to refuse a connection. The ...
Diapositiva 1 - MEGAFRIO S.A
... The firewalls must be disabled The proxy server must be disabled To access in the pCOWeb configuration: admin & fadmin ...
... The firewalls must be disabled The proxy server must be disabled To access in the pCOWeb configuration: admin & fadmin ...
Cryptanalysis of Stream Cipher
... No security reduction but easy to analyze Not resistant to nonce reuse No incremental tags Flexible implementation sizes: 128/256 Performance: speed/size ...
... No security reduction but easy to analyze Not resistant to nonce reuse No incremental tags Flexible implementation sizes: 128/256 Performance: speed/size ...
New York Comic Con Exhibitor Network Planning Guide
... Wireless: Connect to “Javits-Fast” if you’re using the facility Wi-Fi (you can pay by the day or week). If you set up your own Wi-Fi, make sure you connect to the 5 GHz link, not the 2.4 GHz radio. Demos on 2.4 GHz Wi-Fi will experience much more interference. Routers and wireless gear: For large bo ...
... Wireless: Connect to “Javits-Fast” if you’re using the facility Wi-Fi (you can pay by the day or week). If you set up your own Wi-Fi, make sure you connect to the 5 GHz link, not the 2.4 GHz radio. Demos on 2.4 GHz Wi-Fi will experience much more interference. Routers and wireless gear: For large bo ...
MF10 3G Wireless Router
... Connecting the external power ................................................................................... 14 Switching on your device............................................................................................ 14 Power supply................................................... ...
... Connecting the external power ................................................................................... 14 Switching on your device............................................................................................ 14 Power supply................................................... ...
Key To Personal Information Security
... (LAN) or Internet run many services that listen at well-known and not so well known ports • By port scanning, the attacker finds which ports are available (i.e., what service might be listing to a port) • A port scan consists of sending a message to each port, one at a time • The kind of response re ...
... (LAN) or Internet run many services that listen at well-known and not so well known ports • By port scanning, the attacker finds which ports are available (i.e., what service might be listing to a port) • A port scan consists of sending a message to each port, one at a time • The kind of response re ...
Using GSS API For Securing Web Services
... • We want to be security mechanism independent • We want to be interoperable with existing Web-based authentication systems • We want to provide Identity delegation, endto-end security, mutual authentication • We want to be transport independent • We want to be able to identify individual services r ...
... • We want to be security mechanism independent • We want to be interoperable with existing Web-based authentication systems • We want to provide Identity delegation, endto-end security, mutual authentication • We want to be transport independent • We want to be able to identify individual services r ...
Mobile Communications
... • The demand for mobile communication creates the need for integration of wireless networks into existing fixed networks: • local area networks: standardization of IEEE 802.11 • Internet: Mobile IP extension of the internet protocol IP • wide area networks: e.g., internetworking of GSM and ISDN, VoI ...
... • The demand for mobile communication creates the need for integration of wireless networks into existing fixed networks: • local area networks: standardization of IEEE 802.11 • Internet: Mobile IP extension of the internet protocol IP • wide area networks: e.g., internetworking of GSM and ISDN, VoI ...
9 chapter communications and networks
... instant messaging, internet telephone and electronic commerce. Connectivity: is a concept related to using computer networks to link people and resources. ( you can connect your microcomputer by telephone or other telecommunication link to other computers). ...
... instant messaging, internet telephone and electronic commerce. Connectivity: is a concept related to using computer networks to link people and resources. ( you can connect your microcomputer by telephone or other telecommunication link to other computers). ...
Cradlepoint Solutions Power YESCO Digital Signage Networks
... operations that rely on network connections are assigned their own static IP addresses run by the Cradlepoint. 4G speeds allow surveillance cameras to stream video to monitor the sign’s operations and for security purposes. YESCO also uses Enterprise Cloud Manager, Cradlepoint’s remote management ap ...
... operations that rely on network connections are assigned their own static IP addresses run by the Cradlepoint. 4G speeds allow surveillance cameras to stream video to monitor the sign’s operations and for security purposes. YESCO also uses Enterprise Cloud Manager, Cradlepoint’s remote management ap ...
With the help of this diagram, try to describe the function of these
... Bridges can also partition a large network into two smaller ones and connect two LANs that are nearby each other. A router is a special computer that directs communicating messages when several networks are connected ...
... Bridges can also partition a large network into two smaller ones and connect two LANs that are nearby each other. A router is a special computer that directs communicating messages when several networks are connected ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.