CHAPTER 1 Networking Concepts
... Encryption: Renders data indecipherable to any unauthorized users that might be able to examine packets of data traffic Authorization: Screens users according to user IDs and passwords and determines by examining Access Control Lists (ACLs) whether a given user is authorized to access requested file ...
... Encryption: Renders data indecipherable to any unauthorized users that might be able to examine packets of data traffic Authorization: Screens users according to user IDs and passwords and determines by examining Access Control Lists (ACLs) whether a given user is authorized to access requested file ...
IEEE PROJECTS 2011 DOTNET | IEEE 2011 / 2012 PROJECTS
... Correlation in Cognitive Radio Network Privacy in VoIP Networks: Flow Analysis Attacks and Defense Privacy Preserving Collaborative Enforcement of Firewall Policies in Virtual Private Networks ProgME: Towards Programmable Network Measurement Quasi-Kautz Digraphs for Peer-to-Peer Networks. Research o ...
... Correlation in Cognitive Radio Network Privacy in VoIP Networks: Flow Analysis Attacks and Defense Privacy Preserving Collaborative Enforcement of Firewall Policies in Virtual Private Networks ProgME: Towards Programmable Network Measurement Quasi-Kautz Digraphs for Peer-to-Peer Networks. Research o ...
circuit-level gateway
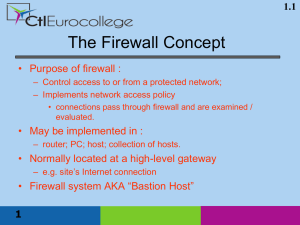
... prevent denial of service attacks: – SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections. prevent illegal modification/access of internal data. – e.g., attacker replaces CIA’s homepage with something else allow only authorized access to inside netw ...
... prevent denial of service attacks: – SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections. prevent illegal modification/access of internal data. – e.g., attacker replaces CIA’s homepage with something else allow only authorized access to inside netw ...
Security services at various protocols levels
... which are best supplied by application layer security solutions – since true non-repudiation requires that the user knows what is signed when it is signed – something that is easier to ensure when only application data is involved. On the other hand, there are services like anonymity which are best ...
... which are best supplied by application layer security solutions – since true non-repudiation requires that the user knows what is signed when it is signed – something that is easier to ensure when only application data is involved. On the other hand, there are services like anonymity which are best ...
Security services at various protocol levels
... which are best supplied by application layer security solutions – since true non-repudiation requires that the user knows what is signed when it is signed – something that is easier to ensure when only application data is involved. On the other hand, there are services like anonymity which are best ...
... which are best supplied by application layer security solutions – since true non-repudiation requires that the user knows what is signed when it is signed – something that is easier to ensure when only application data is involved. On the other hand, there are services like anonymity which are best ...
EV24924929
... even more severe traffic conditions. However, they are used only for very severe wireless CIMM system failures. In such cases, however, the main objective for the CIMM system operation is to recover the normal operating conditions as fast as possible and any optimisation of the transmission conditio ...
... even more severe traffic conditions. However, they are used only for very severe wireless CIMM system failures. In such cases, however, the main objective for the CIMM system operation is to recover the normal operating conditions as fast as possible and any optimisation of the transmission conditio ...
October 1, 2003
... • All designs must fit into the IP security architecture ?? • Authentication and confidentiality are the responsibility of end users, not the network • Security protocols should allow different cryptographic algorithms. • Choose a well-known/studied cryptographic algorithm, do NOT invent a new one u ...
... • All designs must fit into the IP security architecture ?? • Authentication and confidentiality are the responsibility of end users, not the network • Security protocols should allow different cryptographic algorithms. • Choose a well-known/studied cryptographic algorithm, do NOT invent a new one u ...
Chapter 6 Review
... the problem of frequency limitation (or spectral congestion) and user capacity - Replace a single high power base station with several lower power base stations, each covering a smaller geographical area, a ‘cell’. - Each of the base stations is allocated a number of channels (portion of the overall ...
... the problem of frequency limitation (or spectral congestion) and user capacity - Replace a single high power base station with several lower power base stations, each covering a smaller geographical area, a ‘cell’. - Each of the base stations is allocated a number of channels (portion of the overall ...
KEYSCAN • PRoDUCt GUIDe - Johnston Communications
... Relying on standard 802.11b/g protocols this device may be configured as an Adhoc wireless network or added to a more comprehensive wireless LAN environment. Also available with AES Rijndael encryption, part number NETCOM6WH. ...
... Relying on standard 802.11b/g protocols this device may be configured as an Adhoc wireless network or added to a more comprehensive wireless LAN environment. Also available with AES Rijndael encryption, part number NETCOM6WH. ...
HG556a INSTALLATION GUIDE AND USER MANUAL
... Procedure for enabling the Wi-Fi connection The initial configuration for the Wi-Fi radio interface of the HG556a is Disabled. To enable the Wi-Fi connection, do as follows: 1. Press the Wi-Fi button on the side panel of HG556a. 2. Once the button is pressed and held, the Wi-Fi indicator turns red i ...
... Procedure for enabling the Wi-Fi connection The initial configuration for the Wi-Fi radio interface of the HG556a is Disabled. To enable the Wi-Fi connection, do as follows: 1. Press the Wi-Fi button on the side panel of HG556a. 2. Once the button is pressed and held, the Wi-Fi indicator turns red i ...
Next Generation Networks
... There are more than 200 million wireless subscribers in the world today; an additional 700 million more will be added over the next 15-20 years There are more than 200 million Cable TV subscribers in the world today; an additional 300 million more will be added over the next 15-20 years More t ...
... There are more than 200 million wireless subscribers in the world today; an additional 700 million more will be added over the next 15-20 years There are more than 200 million Cable TV subscribers in the world today; an additional 300 million more will be added over the next 15-20 years More t ...
Automation of Batch Vacuum Pans At D.R.B.C Sugar Factory
... Definition of Ad hoc network Ad hoc network is a collection of two or more devices equipped with wireless communication and networking capability. An Ad hoc network is infrastructureless as it does not rely on any fixed network entities, i.e, there is no need for any fixed radio base stations, wire ...
... Definition of Ad hoc network Ad hoc network is a collection of two or more devices equipped with wireless communication and networking capability. An Ad hoc network is infrastructureless as it does not rely on any fixed network entities, i.e, there is no need for any fixed radio base stations, wire ...
document
... • Act as middlemen between hosts inside and outside the firewall – Internal hosts communicate with the application gateway program running on the proxy gateway – Application gateway program relays request to the external host – The external host’s reply is sent to the application gateway ...
... • Act as middlemen between hosts inside and outside the firewall – Internal hosts communicate with the application gateway program running on the proxy gateway – Application gateway program relays request to the external host – The external host’s reply is sent to the application gateway ...
Certification Scheme in Information Security 1
... 1. About Information Security Education and Awareness (ISEA) Project Keeping in view the pervasive nature and impact of cyber security on all walks of life - economic and social, Government of India has identified Information Security as one of the major thrust area for launching various development ...
... 1. About Information Security Education and Awareness (ISEA) Project Keeping in view the pervasive nature and impact of cyber security on all walks of life - economic and social, Government of India has identified Information Security as one of the major thrust area for launching various development ...
... D-Link wireless products are based on industry standards to provide high-speed wireless connectivity that is easy to use within your home, business or public access wireless networks. D-Link wireless products provides you with access to the data you want, whenever and wherever you want it. Enjoy the ...
ppt
... Scenarios and Roadmap • Point to point wireless networks • Example: Your laptop to CMU wireless • Challenges: • Poor and variable link quality (makes TCP unhappy) • Many people can hear when you talk • Pretty well defined. • Ad hoc networks (wireless++) • Rooftop networks (multi-hop, fixed position ...
... Scenarios and Roadmap • Point to point wireless networks • Example: Your laptop to CMU wireless • Challenges: • Poor and variable link quality (makes TCP unhappy) • Many people can hear when you talk • Pretty well defined. • Ad hoc networks (wireless++) • Rooftop networks (multi-hop, fixed position ...
The need for an information policy
... an obvious use is to place a firewall between organisation and Internet can also be used to guard separate components of a LAN can deny certain protocols between departments example: University of Glamorgan could install firewalls between ...
... an obvious use is to place a firewall between organisation and Internet can also be used to guard separate components of a LAN can deny certain protocols between departments example: University of Glamorgan could install firewalls between ...
Firewall - theodoros christophides site
... Software-Only Packages • Many free firewall tools on the Internet – Some also run on a free operating system ...
... Software-Only Packages • Many free firewall tools on the Internet – Some also run on a free operating system ...
Network Security: Intrusion Detection and Protection
... Every connection to a host outside of the internal network is made through an application program called a proxy. Stateful Inspection Firewalls. Track the state of communication sessions and dynamically open and close ports based on access policies. ...
... Every connection to a host outside of the internal network is made through an application program called a proxy. Stateful Inspection Firewalls. Track the state of communication sessions and dynamically open and close ports based on access policies. ...
Product Key Features - D-Link
... The multi-protocol print server makes network connection easy through the use of a NWay connection which allows the print server to be used with either Ethernet or Fast Ethernet LAN. The multi-protocol print server is equipped with high-speed parallel port , and a NWay port, transmitting at either 1 ...
... The multi-protocol print server makes network connection easy through the use of a NWay connection which allows the print server to be used with either Ethernet or Fast Ethernet LAN. The multi-protocol print server is equipped with high-speed parallel port , and a NWay port, transmitting at either 1 ...
A CARMEN mesh experience: deployment and results
... All the 195 CoNEXT attendees were provided with instructions to connect to the Internet through the regular WiFi access. Out of these 195, we randomly selected 75 and provided them also with instructions to use the Mesh access. In this paper we present the results for the second day of the conferenc ...
... All the 195 CoNEXT attendees were provided with instructions to connect to the Internet through the regular WiFi access. Out of these 195, we randomly selected 75 and provided them also with instructions to use the Mesh access. In this paper we present the results for the second day of the conferenc ...
Sample pages 2 PDF
... any other device or host within that network. Although extremely robust, in general mesh topologies are very expensive, as they involve a high level of redundancy. This makes them less used for wired connectivity. However, mesh topologies are most popular for wireless networks, as wireless links can ...
... any other device or host within that network. Although extremely robust, in general mesh topologies are very expensive, as they involve a high level of redundancy. This makes them less used for wired connectivity. However, mesh topologies are most popular for wireless networks, as wireless links can ...
chapterw4
... and are transmitted at 64 kbps. Assume propagation delays over the links are negligible. As a packet travels along the route, it encounters an average of 5 packets when it arrives at each node. How long does it take for the packet to get to the receiver if the nodes transmit on a ...
... and are transmitted at 64 kbps. Assume propagation delays over the links are negligible. As a packet travels along the route, it encounters an average of 5 packets when it arrives at each node. How long does it take for the packet to get to the receiver if the nodes transmit on a ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.