Unit 11
... • Developed to provide security in several layers of the traditional TCP/IP stack • Secure Sockets Layer (SSL) – common extension to http ...
... • Developed to provide security in several layers of the traditional TCP/IP stack • Secure Sockets Layer (SSL) – common extension to http ...
IEEE 802.11 based WLANs
... microwave oven, and Bluetooth. Modulation and MAC design challenge Security ...
... microwave oven, and Bluetooth. Modulation and MAC design challenge Security ...
LanDisk FTP Help
... input user password Access decide user’s access right Click “Add/Modify” after user information input. Then Folder list will be able to Add to or Delete from Allowed share list. Add folders you allow this user to access. Click “Back to account list” when you are done with this user ...
... input user password Access decide user’s access right Click “Add/Modify” after user information input. Then Folder list will be able to Add to or Delete from Allowed share list. Add folders you allow this user to access. Click “Back to account list” when you are done with this user ...
HWR54G Rev R Hawking Technologies, Inc. P 0
... Hawking recommends that you enable wireless security within your network. Note that implementing wireless security may have an impact on your network’s performance, but if you are transmitting sensitive data, enabling wireless security should give you peace of mind that your network is safe from int ...
... Hawking recommends that you enable wireless security within your network. Note that implementing wireless security may have an impact on your network’s performance, but if you are transmitting sensitive data, enabling wireless security should give you peace of mind that your network is safe from int ...
Survey - HP Labs
... • Sony HAVi - short for Home Audio Video interoperability • Vendor-neutral audio-video standard • Aimed specifically at home entertainment environment: VCR, TV, stereo, security system, video monitors • Home entertainment & communication devices can be networked and controlled from a device (eg PC o ...
... • Sony HAVi - short for Home Audio Video interoperability • Vendor-neutral audio-video standard • Aimed specifically at home entertainment environment: VCR, TV, stereo, security system, video monitors • Home entertainment & communication devices can be networked and controlled from a device (eg PC o ...
HUNTING-AS-A-SERVICE By Accenture, Powered by Endgame
... of a breach before security analysts take action. This approach is failing. The most dangerous hackers are — with minimal cost and effort — compromising victims at will by leveraging new techniques as their weapons of choice. These approaches include single-use rotating attack patterns that don’t le ...
... of a breach before security analysts take action. This approach is failing. The most dangerous hackers are — with minimal cost and effort — compromising victims at will by leveraging new techniques as their weapons of choice. These approaches include single-use rotating attack patterns that don’t le ...
CPIT 201 6
... carry a bit stream over a physical medium. •Although the data link layer is responsible for moving a frame from one node to another, the physical layer is responsible for moving the individual bits that make up the frame to the next node. •In other words, the unit of transfer in the data link layer ...
... carry a bit stream over a physical medium. •Although the data link layer is responsible for moving a frame from one node to another, the physical layer is responsible for moving the individual bits that make up the frame to the next node. •In other words, the unit of transfer in the data link layer ...
MAC layer
... more robust against disasters • e.g., earthquakes, fire - or users pulling a plug... ...
... more robust against disasters • e.g., earthquakes, fire - or users pulling a plug... ...
[edit] Methods of attack
... other problems to consider. For instance, there is a brief moment where the connection is opened on the server side before the signature itself comes through. Only once the connection is opened to the server can the identifying signature be sent and detected, and the connection torn down. Even teari ...
... other problems to consider. For instance, there is a brief moment where the connection is opened on the server side before the signature itself comes through. Only once the connection is opened to the server can the identifying signature be sent and detected, and the connection torn down. Even teari ...
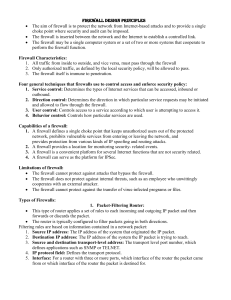
File
... The screened host firewall, dual-homed bastion configuration physically prevents such a security breach if the packer filtering router is completely compromised. 3. Screened subnet firewall system The screened subnet firewall configuration is the most secure among all. In this configuration, t ...
... The screened host firewall, dual-homed bastion configuration physically prevents such a security breach if the packer filtering router is completely compromised. 3. Screened subnet firewall system The screened subnet firewall configuration is the most secure among all. In this configuration, t ...
Wireless Card Adapter Settings and their purpose
... Within a frequency range like 2.4 GHz or 5 GHz, 20 MHz stands for a single channel while 40 MHz will take multiple neighboring channels. As this again can be configured in the router, you can leave this to the default as you most likely don't want to restrict the compatibility of your card. ...
... Within a frequency range like 2.4 GHz or 5 GHz, 20 MHz stands for a single channel while 40 MHz will take multiple neighboring channels. As this again can be configured in the router, you can leave this to the default as you most likely don't want to restrict the compatibility of your card. ...
(Download as PDF)
... Can my SmartNode do Enterprise Class IP Routing? In the landscape of VoIP gateways, the SmartNode is a venerable leader with a proven track record of deployments across the world. So you already bought a SmartNode. With your IP telephony needs planned, you ask yourself, do I really need another rout ...
... Can my SmartNode do Enterprise Class IP Routing? In the landscape of VoIP gateways, the SmartNode is a venerable leader with a proven track record of deployments across the world. So you already bought a SmartNode. With your IP telephony needs planned, you ask yourself, do I really need another rout ...
CPSC 6126 Computer Security
... Why Hide Internal IP Addresses? • The first step in an attack usually is to find potential victim hosts • Sniffer programs read IP packet streams for IP addresses of potential target hosts • With proxy server, sniffers will not learn IP addresses of internal hosts Sniffer Host IP Address ...
... Why Hide Internal IP Addresses? • The first step in an attack usually is to find potential victim hosts • Sniffer programs read IP packet streams for IP addresses of potential target hosts • With proxy server, sniffers will not learn IP addresses of internal hosts Sniffer Host IP Address ...
Electron Solution Datasheet
... to a wired network while APs with internal high-gain directional antennas can point back to it. This gives IT managers the ability to leverage the longer range that the APs with internal directional antennas have because of their more focused signal beam. Many of the Electron Series dual-band Access ...
... to a wired network while APs with internal high-gain directional antennas can point back to it. This gives IT managers the ability to leverage the longer range that the APs with internal directional antennas have because of their more focused signal beam. Many of the Electron Series dual-band Access ...
SEMESTER 1 MODULE 1
... The number of users connected The number and types of services available individual network usually spans a single geographical area, providing services and applications to people within a common organizational structure networks that connect LANs in geographically separated locations A global mesh ...
... The number of users connected The number and types of services available individual network usually spans a single geographical area, providing services and applications to people within a common organizational structure networks that connect LANs in geographically separated locations A global mesh ...
Comparison of Routing Metrics for a Static Multi
... Subsequently, handled and routed like any other packet, with the exception that its contents are encrypted with the session key ...
... Subsequently, handled and routed like any other packet, with the exception that its contents are encrypted with the session key ...
MYDIGIPASS for Healthcare
... permit patient access to patient portals via username and password plus knowledge-based attributes or emerging technologies in lieu of passwords to reduce vulnerabilities in identity theft. HHS’s 2018-2020 milestone is to have at least 50% of health care organizations have implemented identity proof ...
... permit patient access to patient portals via username and password plus knowledge-based attributes or emerging technologies in lieu of passwords to reduce vulnerabilities in identity theft. HHS’s 2018-2020 milestone is to have at least 50% of health care organizations have implemented identity proof ...
PDF
... required for carrying out the test. The MIB can be configured so that when triggers are activated (fired) either an SNMP Set is performed, a notification is sent out to the interested host, or both. ...
... required for carrying out the test. The MIB can be configured so that when triggers are activated (fired) either an SNMP Set is performed, a notification is sent out to the interested host, or both. ...
interface-based forwarding
... of domains. • When the mobile host first enters into a foreign domain, we revert to traditional Mobile IP mechanisms and the mobile host is assigned a colocated care-of address using DHCP. • If the foreign domain is also based on HAWAII, then for subsequent movements within the foreign domain, the m ...
... of domains. • When the mobile host first enters into a foreign domain, we revert to traditional Mobile IP mechanisms and the mobile host is assigned a colocated care-of address using DHCP. • If the foreign domain is also based on HAWAII, then for subsequent movements within the foreign domain, the m ...
MSc – CD4040 – Internet and Web Research Topics
... Ring). TCP/IP shares the LAN with other users. One device provides the TCP/IP connection between the LAN and the rest of the World. ...
... Ring). TCP/IP shares the LAN with other users. One device provides the TCP/IP connection between the LAN and the rest of the World. ...
WiFi-b Card
... digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate radio frequency energy and, if not installed and used in accordance with manufac ...
... digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate radio frequency energy and, if not installed and used in accordance with manufac ...
Before You Begin: Assign Information Classification
... The two most common types of logical topologies are broadcast and token passing. In a broadcast topology, there is no order that the hosts must follow to use the network – it is first come, first served for transmitting data on the network. Token passing controls network access by passing an ele ...
... The two most common types of logical topologies are broadcast and token passing. In a broadcast topology, there is no order that the hosts must follow to use the network – it is first come, first served for transmitting data on the network. Token passing controls network access by passing an ele ...
Aalborg Universitet On traffic modelling in GPRS networks Martin
... Packet Radio Service (GPRS) was an important step in converging wired and wireless communication. GPRS provides a packet-switched access service for IP traffic, integrated into the GSM architecture [1]. The performance analysis of new wireless data technologies, their optimization and network planni ...
... Packet Radio Service (GPRS) was an important step in converging wired and wireless communication. GPRS provides a packet-switched access service for IP traffic, integrated into the GSM architecture [1]. The performance analysis of new wireless data technologies, their optimization and network planni ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.





![[edit] Methods of attack](http://s1.studyres.com/store/data/021898195_1-cd36b3b46913bad45bc8311de7b00618-300x300.png)