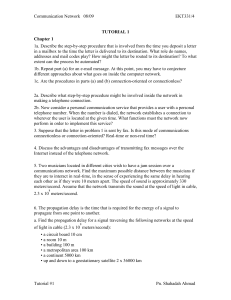
tutorial 1 - UniMAP Portal
... 9. What difference does it make to the network layer if the underlying data link layer provides a connection-oriented service versus a connectionless service? 10. Which OSI layer is responsible for the following? (a) Determining the best path to route packets. (b) Providing end-to-end communications ...
... 9. What difference does it make to the network layer if the underlying data link layer provides a connection-oriented service versus a connectionless service? 10. Which OSI layer is responsible for the following? (a) Determining the best path to route packets. (b) Providing end-to-end communications ...
Chap 3
... The primary purpose of DoS attacks is to steal vital information. (T/F) Name three types of DoS attack. The ping of death works based on using very large ICMP packets that must be fragmented to send and when reassembled are too large for the receiver’s buffer. (T/F) How can a router stop packets fro ...
... The primary purpose of DoS attacks is to steal vital information. (T/F) Name three types of DoS attack. The ping of death works based on using very large ICMP packets that must be fragmented to send and when reassembled are too large for the receiver’s buffer. (T/F) How can a router stop packets fro ...
UNIT 5. Instruction to Computer Networks
... memory and hard disk space than clients • Run Network Operating System that can manage not only data, but also users, groups, security, and applications on the network • Servers often have a more stringent requirement on its performance and reliability ...
... memory and hard disk space than clients • Run Network Operating System that can manage not only data, but also users, groups, security, and applications on the network • Servers often have a more stringent requirement on its performance and reliability ...
pptx
... • Concurrent development at three groups • Leonard Kleinrock (MIT): queueing-theoretic analysis of packet switching in Ph.D. thesis (1961-63) demonstrated value of statistical multiplexing • Paul Baran (RAND) – Reliability of Packet-Switched Links ...
... • Concurrent development at three groups • Leonard Kleinrock (MIT): queueing-theoretic analysis of packet switching in Ph.D. thesis (1961-63) demonstrated value of statistical multiplexing • Paul Baran (RAND) – Reliability of Packet-Switched Links ...
See the dedicated slideshow - VCE IT Lecture Notes by Mark Kelly
... Connections – Wireless Data sent as radio signals between NICs and base stations (WAP=wireless access ...
... Connections – Wireless Data sent as radio signals between NICs and base stations (WAP=wireless access ...
Lecture 2 Digital Data Representation (1)
... Bus networks: All devices connect to a central cable Ring networks: Devices connect to one another in a ring Mesh networks: Multiple connections between devices Some networks use a combination of topologies ...
... Bus networks: All devices connect to a central cable Ring networks: Devices connect to one another in a ring Mesh networks: Multiple connections between devices Some networks use a combination of topologies ...
Networks - PEGSnet
... server computer that is used to access websites on behalf of other computers; hence it acts as a proxy for the actual Internet. When a computer wants a website, it is retrieved by the proxy server and then sent to the requesting computer after it has passed the firewall program. ...
... server computer that is used to access websites on behalf of other computers; hence it acts as a proxy for the actual Internet. When a computer wants a website, it is retrieved by the proxy server and then sent to the requesting computer after it has passed the firewall program. ...
Network Hardware File
... Connections – Wireless Data sent as radio signals between NICs and base stations (WAP=wireless access ...
... Connections – Wireless Data sent as radio signals between NICs and base stations (WAP=wireless access ...
Introduction to Mobile Computing CNT 5517-5564
... Limited communication bandwidth exacerbates the limitation of battery lifetime. ...
... Limited communication bandwidth exacerbates the limitation of battery lifetime. ...
IP addresses
... from the frame header and decides which partition the frame should be relayed to. Once switched on the bridge learns which computer is connected in each collision domain. The learning process occurs as the bridge encounters traffic. The bridge extracts the source MAC address from received frames to ...
... from the frame header and decides which partition the frame should be relayed to. Once switched on the bridge learns which computer is connected in each collision domain. The learning process occurs as the bridge encounters traffic. The bridge extracts the source MAC address from received frames to ...
Fragmentation and IP Forwarding
... List of network names and next hop routers Local networks have entries specifying which interface Link-local hosts can be delivered with Layer-2 forwarding Longest prefix matching ...
... List of network names and next hop routers Local networks have entries specifying which interface Link-local hosts can be delivered with Layer-2 forwarding Longest prefix matching ...
Web Development - Murray School District
... via the internet Each computer must have a separate and unique IP address TCP is what the router uses to attach the IP address to packets being sent ...
... via the internet Each computer must have a separate and unique IP address TCP is what the router uses to attach the IP address to packets being sent ...
Data communication and Networking
... After reading this chapter, the reader should be able to: Understand the rationale for the existence of networks. Distinguish between the three types of networks: LANs, MANs, and WANs. Understand the OSI model and TCP/IP. List different connecting devices and the OSI layers in which each device oper ...
... After reading this chapter, the reader should be able to: Understand the rationale for the existence of networks. Distinguish between the three types of networks: LANs, MANs, and WANs. Understand the OSI model and TCP/IP. List different connecting devices and the OSI layers in which each device oper ...
Network Fundamentals
... – Establish a point-to-point connection to ISP – Use PPTP (etc.) to establish an internet connection – Private link ...
... – Establish a point-to-point connection to ISP – Use PPTP (etc.) to establish an internet connection – Private link ...
iPod-Touch
... The final step in the network configuration is the proxy setting. There are two DOE proxy methods available to you. One is manual and the other is an automatic script. For the manual method, you will follow the steps above. Choose enter
in the server space and enter <8002> in
the po ...
... The final step in the network configuration is the proxy setting. There are two DOE proxy methods available to you. One is manual and the other is an automatic script. For the manual method, you will follow the steps above. Choose
click here
... cheaply, and quickly implemented when overall network security and user authentication strategies are not taken into consideration Wireless access points are cheap and can be used to provide access to areas that would remain otherwise unserved ...
... cheaply, and quickly implemented when overall network security and user authentication strategies are not taken into consideration Wireless access points are cheap and can be used to provide access to areas that would remain otherwise unserved ...