Wi-Fi Technology
... • Service Set Identifier (SSID) - Uniquely identifies the wireless LAN with a configured alphanumeric label. • Wired Equivalency Protocol (WEP) - A widely available data encryption. It does have the chance of being cracked by a motivated attacker. • Wi-Fi Protocol Access (WPA) - An upgrade over WEP ...
... • Service Set Identifier (SSID) - Uniquely identifies the wireless LAN with a configured alphanumeric label. • Wired Equivalency Protocol (WEP) - A widely available data encryption. It does have the chance of being cracked by a motivated attacker. • Wi-Fi Protocol Access (WPA) - An upgrade over WEP ...
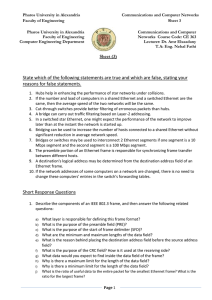
TIA Test 2
... Data transfer rate is always greater than bandwidth Data transfer rate is the maximum speed at which data can be transmitted between two nodes of a network Each node on a network needs a network adapter Home networks are P2P networks In a client-server network each node is connected on the network c ...
... Data transfer rate is always greater than bandwidth Data transfer rate is the maximum speed at which data can be transmitted between two nodes of a network Each node on a network needs a network adapter Home networks are P2P networks In a client-server network each node is connected on the network c ...
$doc.title
... • But, performance definitely is affected – TCP treats packet loss as a sign of congesVon – TCP tries to esVmate the RTT to drive retransmissions – TCP does not perform well under out-‐of-‐order packets ...
... • But, performance definitely is affected – TCP treats packet loss as a sign of congesVon – TCP tries to esVmate the RTT to drive retransmissions – TCP does not perform well under out-‐of-‐order packets ...
Higher Computing Unit 1 – Peripherals and Interfaces
... A local council sets up an intranet within their headquarters. Internet access is made available through a web server on the intranet. Apart from allowing shared Internet access, state two functions that the web server is likely to provide the local council. ...
... A local council sets up an intranet within their headquarters. Internet access is made available through a web server on the intranet. Apart from allowing shared Internet access, state two functions that the web server is likely to provide the local council. ...
Powerpoint - Chapter 3
... Routers strip away the data-link layer frame of incoming packets and build a new frame using the data-link layer protocol of the outgoing network. Routing tables can be created manually by a network administrator or automatically by a routing protocol. ...
... Routers strip away the data-link layer frame of incoming packets and build a new frame using the data-link layer protocol of the outgoing network. Routing tables can be created manually by a network administrator or automatically by a routing protocol. ...
Question 1
... 2. If the number and load of computers in a shared Ethernet and a switched Ethernet are the same, then the average speed of the two networks will be the same. 3. Cut-through switches provide better filtering of erroneous packets than hubs. 4. A bridge can carry out traffic filtering based on Layer-2 ...
... 2. If the number and load of computers in a shared Ethernet and a switched Ethernet are the same, then the average speed of the two networks will be the same. 3. Cut-through switches provide better filtering of erroneous packets than hubs. 4. A bridge can carry out traffic filtering based on Layer-2 ...
Ethernet - wmmhicks.com
... Routers learn routes from each other and put them in their routing tables. A routing protocol is the set of rules they use to swap information. ...
... Routers learn routes from each other and put them in their routing tables. A routing protocol is the set of rules they use to swap information. ...
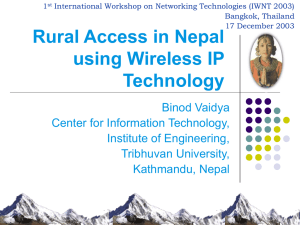
rural access in Nepal
... LSCs that serve as wireless backhaul connection. On wireless backhaul link, access points to line can be used as hot spots Distribution node could be established to provide access to local community. With backbone nodes, distribution nodes are connected All wireless ISPs can be connected to MLSC to ...
... LSCs that serve as wireless backhaul connection. On wireless backhaul link, access points to line can be used as hot spots Distribution node could be established to provide access to local community. With backbone nodes, distribution nodes are connected All wireless ISPs can be connected to MLSC to ...
NetworkingReview
... LAN, WAN, bridge, repeater, switch, router, gateway, backbone. 6. Explain the hidden terminal problem for wireless networks. What is a solution? 7. At what layer in the TCP/IP protocol hierarchy would a firewall be placed to filter messages based on a. Message content b. Source address c. Type of ap ...
... LAN, WAN, bridge, repeater, switch, router, gateway, backbone. 6. Explain the hidden terminal problem for wireless networks. What is a solution? 7. At what layer in the TCP/IP protocol hierarchy would a firewall be placed to filter messages based on a. Message content b. Source address c. Type of ap ...
Middleboxes
and
Tunneling
Reading:
Sect
8.5,
9.4.1,
4.5
COS
461:
Computer
Networks
Spring
2011
... – MulGple machines w/ private addrs behind a single public addr ...
... – MulGple machines w/ private addrs behind a single public addr ...
Routing and Switching (CCNA).
... The Routing and Switching Fundamentals Part 1 and 2 brought to you by Pitman Training is the course for you if you are looking to pass the Cisco CCNA exam and build a career in network management or support in a Cisco environment. This course provides knowledge and skills to make connections ...
... The Routing and Switching Fundamentals Part 1 and 2 brought to you by Pitman Training is the course for you if you are looking to pass the Cisco CCNA exam and build a career in network management or support in a Cisco environment. This course provides knowledge and skills to make connections ...
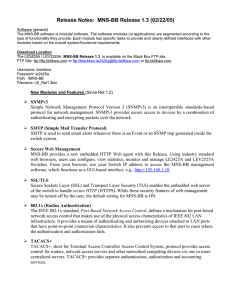
Release notes_1.3
... Switches. From your browser, use your Switch IP address to access the MNS-BB management software, which functions as a GUI-based interface. e.g., http://192.168.1.10. SSL/TLS Secure Sockets Layer (SSL) and Transport Layer Security (TLS) enables the embedded web server of the switch to handle secur ...
... Switches. From your browser, use your Switch IP address to access the MNS-BB management software, which functions as a GUI-based interface. e.g., http://192.168.1.10. SSL/TLS Secure Sockets Layer (SSL) and Transport Layer Security (TLS) enables the embedded web server of the switch to handle secur ...
The Application Layers :On Demand Lecture (Part I)
... Uses ARP format. New opcodes: “Request reverse”, “reply reverse” Send query: Request-reverse [ether addr], server responds with IP ...
... Uses ARP format. New opcodes: “Request reverse”, “reply reverse” Send query: Request-reverse [ether addr], server responds with IP ...
Equipment: IP Networking Tech Gear
... • Subnet Mask Address – Divides IP address (192.168.1.50) into 2 numbers, eg. Network ID (192.168.1) and Host ID (50) – Tells devices which numbers to care about – Same for every device on a network – Always starts with 255 – Looks like 255.255.255.0 or 255.255.248.0 ...
... • Subnet Mask Address – Divides IP address (192.168.1.50) into 2 numbers, eg. Network ID (192.168.1) and Host ID (50) – Tells devices which numbers to care about – Same for every device on a network – Always starts with 255 – Looks like 255.255.255.0 or 255.255.248.0 ...
Assignment Group A1
... going on inside an electric cable (but at a higher level, of course).In the past, such tools were either very expensive, proprietary, or both. However, with the advent of Wireshark, all that has changed.Wireshark is perhaps one of the best open source packet analyzers available today. 2. TCPDUMP: TC ...
... going on inside an electric cable (but at a higher level, of course).In the past, such tools were either very expensive, proprietary, or both. However, with the advent of Wireshark, all that has changed.Wireshark is perhaps one of the best open source packet analyzers available today. 2. TCPDUMP: TC ...
VoIP and Desktop Video Teleconferencing
... Introduction to Cisco Routers and Switches Willis Kim 8 October 2005 ...
... Introduction to Cisco Routers and Switches Willis Kim 8 October 2005 ...
Slides
... A file server stands at the heart of most networks. It is a very fast computer with a large amount of RAM and storage space, along with a fast network interface card. The network operating system software resides on this computer, along with any software applications and data files that need to be s ...
... A file server stands at the heart of most networks. It is a very fast computer with a large amount of RAM and storage space, along with a fast network interface card. The network operating system software resides on this computer, along with any software applications and data files that need to be s ...
lecture10 - Computer and Information Sciences
... Tutorial is available All required tools on a Linux ...
... Tutorial is available All required tools on a Linux ...
ppt
... Infrastructure vs. Ad Hoc • Infrastructure mode – Wireless hosts are associated with a base station – Traditional services provided by the connected network – E.g., address assignment, routing, and DNS resolution ...
... Infrastructure vs. Ad Hoc • Infrastructure mode – Wireless hosts are associated with a base station – Traditional services provided by the connected network – E.g., address assignment, routing, and DNS resolution ...
Lesson 11
... Identifies end system originated packet • Source and destination address • Protocol layer generating data (e.g. TCP) • Identification supplied by IP layer ...
... Identifies end system originated packet • Source and destination address • Protocol layer generating data (e.g. TCP) • Identification supplied by IP layer ...
Wireless LAN and IEEE 802.11
... MAC PDU Formats : It is the data unit exchanged between the MAC layers of the BS and its SSs. ...
... MAC PDU Formats : It is the data unit exchanged between the MAC layers of the BS and its SSs. ...
Protocols - Computing Sciences
... TCP/IP Application Layer Protocols Tomsho, Tittel, Johnson (2007) • DHCP – Detailed configuration of devices, keeping track of assigned addresses and to which machine they were assigned, etc., is difficult in large networks ...
... TCP/IP Application Layer Protocols Tomsho, Tittel, Johnson (2007) • DHCP – Detailed configuration of devices, keeping track of assigned addresses and to which machine they were assigned, etc., is difficult in large networks ...