Document
... TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) exist at the next layer up; these are the protocols by which data is transmitted TCP makes a virtual 'connection', which gives some level of guarantee of reliability. UDP is a best-effort, connectionless transport, in which dat ...
... TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) exist at the next layer up; these are the protocols by which data is transmitted TCP makes a virtual 'connection', which gives some level of guarantee of reliability. UDP is a best-effort, connectionless transport, in which dat ...
No Slide Title - Institute of Technology Sligo
... Data traffic flows up the hierarchy only as far as it needs to find the destination host. This conserves bandwidth on other WAN links. A workgroup server is placed at the access layer of the site where the largest concentration of users is located, and traffic crossing the WAN link to access this se ...
... Data traffic flows up the hierarchy only as far as it needs to find the destination host. This conserves bandwidth on other WAN links. A workgroup server is placed at the access layer of the site where the largest concentration of users is located, and traffic crossing the WAN link to access this se ...
Should SIP be modified for per call billing?
... need to mimic the POTS behavior. Billing network resource is better handled by network protocols, RSVP. ...
... need to mimic the POTS behavior. Billing network resource is better handled by network protocols, RSVP. ...
Operating System Security Fundamentals
... reading and writing actions • Data resides in files; protecting files protects data • Read, write, and execute privileges ...
... reading and writing actions • Data resides in files; protecting files protects data • Read, write, and execute privileges ...
Wireless Networks and Mobile Communication Systems NET 332D
... › Governed by a single organization, Example: Home Network › Size: Home devices versus a class devices versus a small corporation › Small network administered by a single organization or individual who have a common goal interest and set of resources: Example class meets to discuss 332D so this clas ...
... › Governed by a single organization, Example: Home Network › Size: Home devices versus a class devices versus a small corporation › Small network administered by a single organization or individual who have a common goal interest and set of resources: Example class meets to discuss 332D so this clas ...
How to configure the HL2170W to print wireless
... verify your security information and go to STEP II. If the IP Address is a 169.254.x.x number and the Wireless Link Status in LINK OK, please check your router for MAC filtering. If MAC filtering is enabled, please enter the MAC address to the list. If MAC filtering is not enable, please reset the r ...
... verify your security information and go to STEP II. If the IP Address is a 169.254.x.x number and the Wireless Link Status in LINK OK, please check your router for MAC filtering. If MAC filtering is enabled, please enter the MAC address to the list. If MAC filtering is not enable, please reset the r ...
IP : Internet Protocol
... and reassembly packet • TTL : Time to Live, maximum number of routers through with the datagrams may pass (hop count) – decrease at each router to prevent forever looping – normally set to 30 – if TTL == 0 discard and send ICMP TTL exceeded to source IP ...
... and reassembly packet • TTL : Time to Live, maximum number of routers through with the datagrams may pass (hop count) – decrease at each router to prevent forever looping – normally set to 30 – if TTL == 0 discard and send ICMP TTL exceeded to source IP ...
Network Layer
... device interfaces with same subnet part of IP address can physically reach each other without intervening router ...
... device interfaces with same subnet part of IP address can physically reach each other without intervening router ...
70-680_Lesson01
... managed switches, and any other device that has a network card or interface. • An Internet Protocol (IP) address is a logical address and numerical label that is assigned to a device that is connected to a computer network. – While you have to follow certain guidelines based on the TCP/IP protocol s ...
... managed switches, and any other device that has a network card or interface. • An Internet Protocol (IP) address is a logical address and numerical label that is assigned to a device that is connected to a computer network. – While you have to follow certain guidelines based on the TCP/IP protocol s ...
Lecture 8
... • Important nuggets : Hardware type specified type of physical network -- Ethernet/FDDI •Protocol Type -- typically IP (higher layer) •Operation -- specified whether query or response. ...
... • Important nuggets : Hardware type specified type of physical network -- Ethernet/FDDI •Protocol Type -- typically IP (higher layer) •Operation -- specified whether query or response. ...
POSITION DESCRIPTION
... Required Knowledge and Abilities Thorough knowledge of computer network configuration, installation and maintenance; Thorough knowledge of computer capabilities and associated networking equipment; Thorough knowledge of routers and hubs; Thorough knowledge of structured wiring systems; Good knowled ...
... Required Knowledge and Abilities Thorough knowledge of computer network configuration, installation and maintenance; Thorough knowledge of computer capabilities and associated networking equipment; Thorough knowledge of routers and hubs; Thorough knowledge of structured wiring systems; Good knowled ...
Chapter 1 PowerPoint
... The Internet is the largest computer network in the world. The word “Internet” comes from “Inter-connected networks” because the TCP/IP protocol allows for everyone’s own network to connect to others. ...
... The Internet is the largest computer network in the world. The word “Internet” comes from “Inter-connected networks” because the TCP/IP protocol allows for everyone’s own network to connect to others. ...
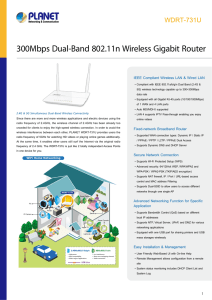
300Mbps Dual-Band 802.11n Wireless Gigabit Router
... At the same time, it enables other users still surf the Internet via the original radio frequency of 2.4 GHz. The WDRT-731U is just like 2 totally independent Access Points in one device for you. ...
... At the same time, it enables other users still surf the Internet via the original radio frequency of 2.4 GHz. The WDRT-731U is just like 2 totally independent Access Points in one device for you. ...
SDN evolution - FSU Computer Science
... • Advantage: Offload routing from routers without additional support. The system can be deployed in the current networks • Limitations: Control is limited by what existing protocols can do. ...
... • Advantage: Offload routing from routers without additional support. The system can be deployed in the current networks • Limitations: Control is limited by what existing protocols can do. ...
Security for (Wireless) LANs
... • No client software (DHCP ubiquitous) • No access control • Network is open (sniffing easy, every client and server on LAN is available) ...
... • No client software (DHCP ubiquitous) • No access control • Network is open (sniffing easy, every client and server on LAN is available) ...
Interconnection Networks
... the buffer, the packet is discarded, SW detects and resends – Flow control: between pairs of receivers and senders; use feedback to tell the sender when it is allowed to send the next packet » Back-pressure: separate wires to tell to stop » Window: give the original sender the right to send N packet ...
... the buffer, the packet is discarded, SW detects and resends – Flow control: between pairs of receivers and senders; use feedback to tell the sender when it is allowed to send the next packet » Back-pressure: separate wires to tell to stop » Window: give the original sender the right to send N packet ...
TCP/IP Networking
... IP addresses were grouped into “classes” Class A,B and C denote regular IP addresses. Class D and E are used for multicasting and research purpose. Part of the host portion of an address is “borrowed” to extend the network portion. ...
... IP addresses were grouped into “classes” Class A,B and C denote regular IP addresses. Class D and E are used for multicasting and research purpose. Part of the host portion of an address is “borrowed” to extend the network portion. ...
DIVISION: Technology BUSINESS UNIT: Henley TV Facilities
... redundancy for on air operational broadcasts 24 hours a day. May need to supervise other network support and client server specialists and plan, coordinate, and implement network security measures. KEY ACCOUNTABILITIES Perform, plan and control the efficient preventative and corrective maintenance ...
... redundancy for on air operational broadcasts 24 hours a day. May need to supervise other network support and client server specialists and plan, coordinate, and implement network security measures. KEY ACCOUNTABILITIES Perform, plan and control the efficient preventative and corrective maintenance ...
Presentation Title
... Trunking allows multiple Linking trunks provides increased VLANs over a single network link Bandwidth and resiliency ...
... Trunking allows multiple Linking trunks provides increased VLANs over a single network link Bandwidth and resiliency ...