Efficient Way of iSCSI based Remote Storage Service for
... Target can become overlong than SCSI cable or fiber channel. ...
... Target can become overlong than SCSI cable or fiber channel. ...
re-feedback - Bob Briscoe
... • recall: permissive rate response to congestion ≡ QoS • traditional QoS: routers give certain packets priority during congestion • allowing an app to maintain its rate during pre-congestion is equivalent • zero rate response to congestion ≡ QoS reservation ...
... • recall: permissive rate response to congestion ≡ QoS • traditional QoS: routers give certain packets priority during congestion • allowing an app to maintain its rate during pre-congestion is equivalent • zero rate response to congestion ≡ QoS reservation ...
PDF
... you can configure the proxy by outbound interface. For example, if there were 100 set-top boxes downstream from the proxy router, you had to configure 100 proxies. With this enhancement, you configure only the outbound interface(s). In addition, the receiver proxy is guaranteed to terminate the rese ...
... you can configure the proxy by outbound interface. For example, if there were 100 set-top boxes downstream from the proxy router, you had to configure 100 proxies. With this enhancement, you configure only the outbound interface(s). In addition, the receiver proxy is guaranteed to terminate the rese ...
Chapter 4
... government. “Com” stands for commercial, so many businesses have .com as their domain name. Top-level domains are registered by Internet Assigned Numbers Authority (IANA); http://www.iana.org/. In order for network traffic to travel across routers all over the world, the domain name needs to be regi ...
... government. “Com” stands for commercial, so many businesses have .com as their domain name. Top-level domains are registered by Internet Assigned Numbers Authority (IANA); http://www.iana.org/. In order for network traffic to travel across routers all over the world, the domain name needs to be regi ...
Implementing CAIA Delay
... the layer above it, and utilizes the layer below it to do so. Internet hosts have no strict requirements such as size, speed or function, but communication with other hosts needs at least one protocol for each layer in the TCP/IP model [12]. Routers, switches and other devices between hosts will typ ...
... the layer above it, and utilizes the layer below it to do so. Internet hosts have no strict requirements such as size, speed or function, but communication with other hosts needs at least one protocol for each layer in the TCP/IP model [12]. Routers, switches and other devices between hosts will typ ...
OSPF - fog.ccsf.edu
... Basic OSPF Configuration Modifying the Cost of a link Both sides of a serial link should be configured with the same bandwidth – Commands used to modify bandwidth value • Bandwidth command – Example: Router(config-if)#bandwidthbandwidth-kbps • ip ospf cost command – allows you to directly speci ...
... Basic OSPF Configuration Modifying the Cost of a link Both sides of a serial link should be configured with the same bandwidth – Commands used to modify bandwidth value • Bandwidth command – Example: Router(config-if)#bandwidthbandwidth-kbps • ip ospf cost command – allows you to directly speci ...
Good Control/Good Proxy Server Installation
... deployment configuration and is suitable for proof-of-concept or demonstration but is not suitable for production use. For an overview of the common deployment configurations, see Variations on deployment configurations . The following are the minimum requirements to successfully install the BlackBe ...
... deployment configuration and is suitable for proof-of-concept or demonstration but is not suitable for production use. For an overview of the common deployment configurations, see Variations on deployment configurations . The following are the minimum requirements to successfully install the BlackBe ...
II. bicc overview
... outgoing BICC set-up or after there are two different ways of bearer connection set-up: Forward and Backward. It depends as well on outgoing CSF route characteristics and originating BIWF. The choice between Fast (Forward or Backward) and Delayed Forward/Backward set-up, respectively, is made by the ...
... outgoing BICC set-up or after there are two different ways of bearer connection set-up: Forward and Backward. It depends as well on outgoing CSF route characteristics and originating BIWF. The choice between Fast (Forward or Backward) and Delayed Forward/Backward set-up, respectively, is made by the ...
Seahorse XFp Analyzer User Guide
... To see the conditions defined for a Group, touch the group name and look at the header information, as shown. ...
... To see the conditions defined for a Group, touch the group name and look at the header information, as shown. ...
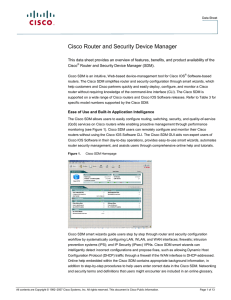
Cloud and Network Services
... features—Network Address Translation (NAT), access control lists (ACLs), firewalls, intrusion prevention system (IPS), and IPsec VPNs—and integrates these security features into existing router configuration and network architectures. Smart wizards in the Cisco SDM understand the interaction of rout ...
... features—Network Address Translation (NAT), access control lists (ACLs), firewalls, intrusion prevention system (IPS), and IPsec VPNs—and integrates these security features into existing router configuration and network architectures. Smart wizards in the Cisco SDM understand the interaction of rout ...
XP Utilites
... Is printer Plug and Play compatible? Is the printer local or on the network? To which port will the printer be connected? What is the make and model of the printer? What do you want the printer to be named? Do you want the printer to be the default for all print jobs? Should printer be shared with t ...
... Is printer Plug and Play compatible? Is the printer local or on the network? To which port will the printer be connected? What is the make and model of the printer? What do you want the printer to be named? Do you want the printer to be the default for all print jobs? Should printer be shared with t ...
BROCADE DCX BACKBONE FAMILY
... (MAPS): Simplifies fabric-wide threshold configuration and monitoring. By leveraging pre-built rule/policy-based templates, applying thresholds and alerts to ports is a simple two-step process. Organizations can configure the entire fabric (or multiple fabrics) at one time using common rules and pol ...
... (MAPS): Simplifies fabric-wide threshold configuration and monitoring. By leveraging pre-built rule/policy-based templates, applying thresholds and alerts to ports is a simple two-step process. Organizations can configure the entire fabric (or multiple fabrics) at one time using common rules and pol ...
Gnutella2: A Better Gnutella?
... malicious users from sending out queries for the purpose of flooding the network with spoofed requests. ...
... malicious users from sending out queries for the purpose of flooding the network with spoofed requests. ...
Powerpoint Slides - Suraj @ LUMS
... First prune all links not fulfilling constrains Now find shortest path on the rest of the topology ...
... First prune all links not fulfilling constrains Now find shortest path on the rest of the topology ...
PDF - ZTE Deutschland GmbH
... have promised. Another point is that they are able to take risk and manage it. We had one common game to win and done it together. It is a huge thing to have a partner who is taking your journey as his own one. Our promise that we will not cause any negative impact on our five million customers was ...
... have promised. Another point is that they are able to take risk and manage it. We had one common game to win and done it together. It is a huge thing to have a partner who is taking your journey as his own one. Our promise that we will not cause any negative impact on our five million customers was ...
AMHS IP Interoperability Trials
... 1.The short term proposal is to implement, as minimum, the current CIDIN routing/topology. 2.According with the current PENs implementation, a fully meshed topology will be possible in the Eur Region in medium term. As consequence, the topology among some members of the AEFMP will be “theoretically” ...
... 1.The short term proposal is to implement, as minimum, the current CIDIN routing/topology. 2.According with the current PENs implementation, a fully meshed topology will be possible in the Eur Region in medium term. As consequence, the topology among some members of the AEFMP will be “theoretically” ...
Core of the network
... • You have to use both mechanisms in real network – DHCPv6 server, Advertises on router – Secure either of them – Failure any of them leads to a network connectivity failure • Different platforms support different techniques – Windows XP - SLAAC ...
... • You have to use both mechanisms in real network – DHCPv6 server, Advertises on router – Secure either of them – Failure any of them leads to a network connectivity failure • Different platforms support different techniques – Windows XP - SLAAC ...
Introduction to Dynamic Routing Protocol
... Cisco developed Interior Gateway Routing Protocol (IGRP) and Enhanced IGRP (EIGRP), which also scales well in larger network implementations. Additionally, there was the need to interconnect different internetworks and provide routing among them. Border Gateway Routing (BGP) protocol is now used ...
... Cisco developed Interior Gateway Routing Protocol (IGRP) and Enhanced IGRP (EIGRP), which also scales well in larger network implementations. Additionally, there was the need to interconnect different internetworks and provide routing among them. Border Gateway Routing (BGP) protocol is now used ...
Apricot 2000 Traffice Engineering with MPLS
... Needs configuration on each router Do not re-route when a link fails ...
... Needs configuration on each router Do not re-route when a link fails ...