IDT Press Contact: Dean Solov Public Relations Manager Phone
... Ultra-High Linearity and Glitch-Free Performance to Support Increased Data Rates SAN JOSE, Calif., March 2, 2016— Integrated Device Technology, Inc.® (IDT®) (NASDAQ: IDTI) today expanded its RF portfolio with the addition of a new family of digital step attenuators (DSAs) optimized for the demanding ...
... Ultra-High Linearity and Glitch-Free Performance to Support Increased Data Rates SAN JOSE, Calif., March 2, 2016— Integrated Device Technology, Inc.® (IDT®) (NASDAQ: IDTI) today expanded its RF portfolio with the addition of a new family of digital step attenuators (DSAs) optimized for the demanding ...
CORD Fabric, Overlay Virtualization, and Service Composition
... The fact that we use MPLS labels to achieve this edgecore (leafspine) separation is immaterial. We could have just as well used VLAN tags. However in our experience with current ASICs, it is easier to use labels instead of tags, as they are treated differently in current ASIC pipelines and ther ...
... The fact that we use MPLS labels to achieve this edgecore (leafspine) separation is immaterial. We could have just as well used VLAN tags. However in our experience with current ASICs, it is easier to use labels instead of tags, as they are treated differently in current ASIC pipelines and ther ...
Document
... A network protocol used on Internet or LAN connections Developed in 1969 beginning with RFC 15 Standardized as IETF STD 8 ...
... A network protocol used on Internet or LAN connections Developed in 1969 beginning with RFC 15 Standardized as IETF STD 8 ...
ISO Layer and TCP Fundamentals
... • Destination host is responsible for reassembling all fragments into original packet • Performance impact on modern (ASIC based) routers ...
... • Destination host is responsible for reassembling all fragments into original packet • Performance impact on modern (ASIC based) routers ...
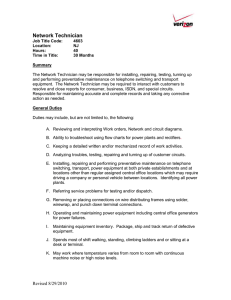
Net Tech Job Description
... Responsible for maintaining accurate and complete records and taking any corrective action as needed. General Duties Duties may include, but are not limited to, the following: A. Reviewing and interpreting Work orders, Network and circuit diagrams. B. Ability to troubleshoot using flow charts for po ...
... Responsible for maintaining accurate and complete records and taking any corrective action as needed. General Duties Duties may include, but are not limited to, the following: A. Reviewing and interpreting Work orders, Network and circuit diagrams. B. Ability to troubleshoot using flow charts for po ...
《Electromagnetic Field and Microwave Technology》 Course syllabus
... generation, transmission, reception theory and method; 2. Familiar with the basic features and uses of high frequency electronic devices; 3. Master circuit working principles of high frequency electronic circuit module and export of basic circuits. 4. Learn basic analysis method for high frequency e ...
... generation, transmission, reception theory and method; 2. Familiar with the basic features and uses of high frequency electronic devices; 3. Master circuit working principles of high frequency electronic circuit module and export of basic circuits. 4. Learn basic analysis method for high frequency e ...
Ethernet - Binus Repository
... cable) is an Ethernet network that typically uses unshielded twisted-pair (UTP) to connect computers. While 10BaseT normally uses UTP, shielded twisted-pair (STP) will also work without changing any of the 10BaseT parameters. Most networks of this type are configured in a star pattern but internally ...
... cable) is an Ethernet network that typically uses unshielded twisted-pair (UTP) to connect computers. While 10BaseT normally uses UTP, shielded twisted-pair (STP) will also work without changing any of the 10BaseT parameters. Most networks of this type are configured in a star pattern but internally ...
Network Reference Model for cdma2000 Spread Spectrum
... Mobile Equipment (ME) The ME is the MS without a UIM. The ME is only capable of accessing the network per locally defined service configuration e.g. emergency services, service center, etc. Mobile Position Center (MPC) The MPC selects a PDE to determine the position of a mobile station. The MPC may ...
... Mobile Equipment (ME) The ME is the MS without a UIM. The ME is only capable of accessing the network per locally defined service configuration e.g. emergency services, service center, etc. Mobile Position Center (MPC) The MPC selects a PDE to determine the position of a mobile station. The MPC may ...
Functional Policy: Design & Implementation
... Network administrator should take into account interoperability between wireless LAN security solution before making purchases. for example many EAP types are proprietary, and not supported by all vendors PPTP is widely used in small and medium-sized wireless networks for its authentication and encr ...
... Network administrator should take into account interoperability between wireless LAN security solution before making purchases. for example many EAP types are proprietary, and not supported by all vendors PPTP is widely used in small and medium-sized wireless networks for its authentication and encr ...
3GPP TSG-SA2 Meeting #30
... and which operators it holds roaming agreements with so that the UE can decide whether to attach to the network or not. TS 23.234 [1] suggests using the SSID (Service Set ID) in the beacon signal for 802.11. It is unclear exactly how this would work and by being specific to the individual standards ...
... and which operators it holds roaming agreements with so that the UE can decide whether to attach to the network or not. TS 23.234 [1] suggests using the SSID (Service Set ID) in the beacon signal for 802.11. It is unclear exactly how this would work and by being specific to the individual standards ...
ppt - Courses
... as circuit switching could have been considered, but the applications being supported, such as remote login, were naturally served by the packet switching paradigm” ...
... as circuit switching could have been considered, but the applications being supported, such as remote login, were naturally served by the packet switching paradigm” ...
Secure Full-Duplex Spectrum-Sharing Wiretap Networks with
... LB . Moreover, we find that RSC/ZFB achieves a similar performance to that of GSC/ZFB as LB approaches NB , and the secrecy performance of both schemes is not always improved with the increase of LB under a given NB . Finally, the optimal antenna allocation at Bob for the two proposed schemes is als ...
... LB . Moreover, we find that RSC/ZFB achieves a similar performance to that of GSC/ZFB as LB approaches NB , and the secrecy performance of both schemes is not always improved with the increase of LB under a given NB . Finally, the optimal antenna allocation at Bob for the two proposed schemes is als ...
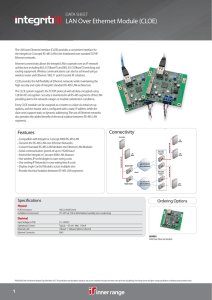
LAN Over Ethernet Module (CLOE)
... architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also be achieved using a wireless router and Ethernet / 802.11 point to point RF solutions. CLOE provides the full flexibility of Ethernet networks while maintaining the high se ...
... architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also be achieved using a wireless router and Ethernet / 802.11 point to point RF solutions. CLOE provides the full flexibility of Ethernet networks while maintaining the high se ...
ready to `software define` your Wide area network?
... out to the main Internet connection. Now we can send it out to multiple routes.” While SD-WAN may be sufficient for guest Wi-Fi or processes that can be completed offline, the public Internet cannot be counted on as a completely reliable medium for critical services, cautions ipSpace.net’s Pepelnjak ...
... out to the main Internet connection. Now we can send it out to multiple routes.” While SD-WAN may be sufficient for guest Wi-Fi or processes that can be completed offline, the public Internet cannot be counted on as a completely reliable medium for critical services, cautions ipSpace.net’s Pepelnjak ...
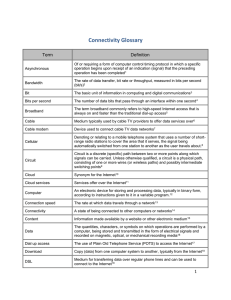
Connectivity Glossary
... The rate of data transfer, bit rate or throughput, measured in bits per second ...
... The rate of data transfer, bit rate or throughput, measured in bits per second ...
Chapter 9.doc
... 3. With the necessary software, a printer with Internet printing capability can receive print instructions from desktop computers, mobile computers, or mobile devices. 4. A voice mail system seldom provides individual voice mailboxes. 5. In a networked environment, no authorized computer user can ac ...
... 3. With the necessary software, a printer with Internet printing capability can receive print instructions from desktop computers, mobile computers, or mobile devices. 4. A voice mail system seldom provides individual voice mailboxes. 5. In a networked environment, no authorized computer user can ac ...
ADSL Network - Binus Repository
... • Fiber node: optical - RF conversion •Head end: • Signals from multiple sources multiplexed • Frequency conversion for local signal • Network interface device (NID) / unit (NIU) Demarcation point between customer network and service provider networks • Cable modem: RF Ethernet, analog telephony, an ...
... • Fiber node: optical - RF conversion •Head end: • Signals from multiple sources multiplexed • Frequency conversion for local signal • Network interface device (NID) / unit (NIU) Demarcation point between customer network and service provider networks • Cable modem: RF Ethernet, analog telephony, an ...
- IEEE Mentor
... operators it holds roaming agreements with so that the UE can decide whether to attach to the network or not. TS 23.234 [1] suggests using the SSID (Service Set ID) in the beacon signal for 802.11. It is unclear exactly how this would work and by being specific to the individual standards (e.g. 802. ...
... operators it holds roaming agreements with so that the UE can decide whether to attach to the network or not. TS 23.234 [1] suggests using the SSID (Service Set ID) in the beacon signal for 802.11. It is unclear exactly how this would work and by being specific to the individual standards (e.g. 802. ...
Total Conversation through ITU
... multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
... multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
Total Conversation through ITU-T Standards
... multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
... multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
Chapter 11
... Transmission bit rate Modulation type Operating frequency range Frequency hop channel sequence ...
... Transmission bit rate Modulation type Operating frequency range Frequency hop channel sequence ...
1 - City of San Carlos
... The City of San Carlos is currently supported by a re-furbished telephone system that was purchased in 1987, upgraded in 1992. It is approximately three (3) generations removed from today’s state of the art technology. The system is, and will continue to be, costly to maintain. Replacements parts ha ...
... The City of San Carlos is currently supported by a re-furbished telephone system that was purchased in 1987, upgraded in 1992. It is approximately three (3) generations removed from today’s state of the art technology. The system is, and will continue to be, costly to maintain. Replacements parts ha ...
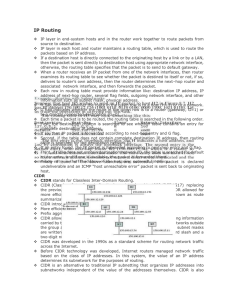
IP Routing
... It is also used for IP over other LAN technologies, such as Token Ring, FDDI, or IEEE 802.11 , and for IP over ATM. ARP is a Link Layer protocol because it only operates on the local area network or point-to-point link that a host is connected to. The hardware address is also known as the Medi ...
... It is also used for IP over other LAN technologies, such as Token Ring, FDDI, or IEEE 802.11 , and for IP over ATM. ARP is a Link Layer protocol because it only operates on the local area network or point-to-point link that a host is connected to. The hardware address is also known as the Medi ...
Lecture 25: Introduction to Network Security
... …but with Public Key Encryption anyone can get the public key, so you don’t know if the message really came from Alice, even it is says it did. i.e. can’t do authentication ...
... …but with Public Key Encryption anyone can get the public key, so you don’t know if the message really came from Alice, even it is says it did. i.e. can’t do authentication ...