appendix a: wlan-related terminology - University of Houston
... networks. However a lot of concerns were raised later regarding the usefulness of WEP. Some of them are as following: a. Manual Key Management: Keys need to be entered manually on all the clients and Access Points. Such key management overhead may result in WEP keys that are not changed frequently. ...
... networks. However a lot of concerns were raised later regarding the usefulness of WEP. Some of them are as following: a. Manual Key Management: Keys need to be entered manually on all the clients and Access Points. Such key management overhead may result in WEP keys that are not changed frequently. ...
Chapter 2 Protocols and Architecture
... Each layer relies on the next lower layer to perform certain functions Each layer provides services through primitives (operations) to the next higher layer Changes in one layer should not require changes in other layers (modular, info hiding) ...
... Each layer relies on the next lower layer to perform certain functions Each layer provides services through primitives (operations) to the next higher layer Changes in one layer should not require changes in other layers (modular, info hiding) ...
ICN lecture1 - OSI & TCP_IP
... Agreed rules form the basis of harmonious data exchange between network nodes. These rules are referred to as protocols in the telecoms world. All telecommunications technologies are underpinned by protocols that should be recognised internationally managed by established standards bodies. A protoco ...
... Agreed rules form the basis of harmonious data exchange between network nodes. These rules are referred to as protocols in the telecoms world. All telecommunications technologies are underpinned by protocols that should be recognised internationally managed by established standards bodies. A protoco ...
PLM & Digital Manufacturing - Industrial Engineering 2011
... has been made. In other words, devices 1 and 2 can talk to each other through "protocol A" and devices 3 and 4 can talk to each other through "protocol B". It is then also possible that device 3 can talk to device 1 through "protocol A". This has merits in manufacturing where it is not always practi ...
... has been made. In other words, devices 1 and 2 can talk to each other through "protocol A" and devices 3 and 4 can talk to each other through "protocol B". It is then also possible that device 3 can talk to device 1 through "protocol A". This has merits in manufacturing where it is not always practi ...
S-38.310 Thesis Seminar on Networking Technology
... HIPERLAN & HIPERLAN/2 • Developed by ETSI BRAN • The purpose is to allow flexible wireless data networks without the need for an existing wired infrastrcture • HIPERLAN type 1 provide 20Mbit/s with 5GHz range, multimedia application are possible • HIPERLAN/2 is specified for short range radio acces ...
... HIPERLAN & HIPERLAN/2 • Developed by ETSI BRAN • The purpose is to allow flexible wireless data networks without the need for an existing wired infrastrcture • HIPERLAN type 1 provide 20Mbit/s with 5GHz range, multimedia application are possible • HIPERLAN/2 is specified for short range radio acces ...
802.11ag The - Silex Technology
... sustained wire-like speeds. At the same time, applications such as VoIP and video webcasting are much less forgiving of collisions with best-effort traffic and other network anomalies. Unlike the home, where a single access point (AP) serves the entire coverage area, enterprises deploy multiple APs ...
... sustained wire-like speeds. At the same time, applications such as VoIP and video webcasting are much less forgiving of collisions with best-effort traffic and other network anomalies. Unlike the home, where a single access point (AP) serves the entire coverage area, enterprises deploy multiple APs ...
Chapter 1 Lecture Presentation
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
What is a communication network?
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
Chapter 1 Communication Networks and Services
... To implement new services such as caller ID, voice mail, . . . To enable mobility and roaming in cellular networks ...
... To implement new services such as caller ID, voice mail, . . . To enable mobility and roaming in cellular networks ...
Chapter 1 - UniMAP Portal
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
Digital Communication System
... WWAN (Wireless Wide Area Network ) – operates over a large geographical area, mobile phone, ...
... WWAN (Wireless Wide Area Network ) – operates over a large geographical area, mobile phone, ...
File - Learning@NDGTA
... computers exercising LAN control • In turn these may be part of a network with a larger mainframe company computer controlling all ...
... computers exercising LAN control • In turn these may be part of a network with a larger mainframe company computer controlling all ...
For ML MIMO detectors case
... This document does not represent the agreed views of the IEEE 802.16 Working Group or any of its subgroups. It represents only the views of the participants listed in the “Source(s)” field above. It is offered as a basis for discussion. It is not binding on the contributor(s), who reserve(s) the rig ...
... This document does not represent the agreed views of the IEEE 802.16 Working Group or any of its subgroups. It represents only the views of the participants listed in the “Source(s)” field above. It is offered as a basis for discussion. It is not binding on the contributor(s), who reserve(s) the rig ...
DwB Standard Presentation
... • Access points rules : Jara and Kamel use the same thin client (DwB SDBox) DESTATIS allows access for resident as well as non resident, however only from accredited point of access in Germany. Humboldt University is accredited. France allows access from researchers own office in France as wel ...
... • Access points rules : Jara and Kamel use the same thin client (DwB SDBox) DESTATIS allows access for resident as well as non resident, however only from accredited point of access in Germany. Humboldt University is accredited. France allows access from researchers own office in France as wel ...
Wireless/Cellular Technologies
... • mobile telephony offering the traditional bandwidth of 3.1 kHz • Emergency number common number throughout Europe (112); mandatory for all service providers; free of charge; connection with the highest priority (preemption of other connections possible) ...
... • mobile telephony offering the traditional bandwidth of 3.1 kHz • Emergency number common number throughout Europe (112); mandatory for all service providers; free of charge; connection with the highest priority (preemption of other connections possible) ...
MP49 Music Transmission and reception with high S/N ratio using
... glass or plastic. An optical fiber acts as a waveguide, or "light pipe", to transmit light between ...
... glass or plastic. An optical fiber acts as a waveguide, or "light pipe", to transmit light between ...
OSI Data Link Layer
... • Terminates connection at end of session (up/down) • Three-way handshake ...
... • Terminates connection at end of session (up/down) • Three-way handshake ...
William Stallings Data and Computer Communications
... Aggregating or bonding ISDN lines to gain bandwidth ...
... Aggregating or bonding ISDN lines to gain bandwidth ...
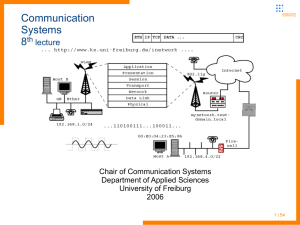
Communication Systems 8th lecture - Electures
... telephony networks work, we give an introduction to ISDN, GSM and UMTS First traditional telephony networks its history and their concepts in general Digitization of voice - PCM Then introduction to ISDN – a completely digitalized communication infrastructure ...
... telephony networks work, we give an introduction to ISDN, GSM and UMTS First traditional telephony networks its history and their concepts in general Digitization of voice - PCM Then introduction to ISDN – a completely digitalized communication infrastructure ...
Understanding Sociograms
... Sociograms and network analysis data are important organizational tools because they can provide a framework for clarifying other available data within the context of organizational capacity. Maps and network data illustrate the capacity of an organization to achieve goals. They can provide a diagno ...
... Sociograms and network analysis data are important organizational tools because they can provide a framework for clarifying other available data within the context of organizational capacity. Maps and network data illustrate the capacity of an organization to achieve goals. They can provide a diagno ...
Tech Team Policy
... 1.3.2: All projects are brought to tech team, approved, purchased by the house, then funded through the finance office. 1.3.3: No funding is provided for individual consumable supplies, including, but not limited to paper, ink/toner, or data storage media 1.4 Equipment Loans 1.4.1: Tech Team may len ...
... 1.3.2: All projects are brought to tech team, approved, purchased by the house, then funded through the finance office. 1.3.3: No funding is provided for individual consumable supplies, including, but not limited to paper, ink/toner, or data storage media 1.4 Equipment Loans 1.4.1: Tech Team may len ...
CMPE 150 – Spring 06
... • If octet of all zeros and last voltage pulse preceding was negative encode as 000-+0+• Causes two violations of AMI code • Unlikely to occur as a result of noise • Receiver detects and interprets as octet of all ...
... • If octet of all zeros and last voltage pulse preceding was negative encode as 000-+0+• Causes two violations of AMI code • Unlikely to occur as a result of noise • Receiver detects and interprets as octet of all ...
William Stallings Data and Computer Communications
... • Protocol specification • Operates between the same layer on two systems • May involve different operating system • Protocol specification must be precise • Format of data units • Semantics of all fields • allowable sequence of PCUs ...
... • Protocol specification • Operates between the same layer on two systems • May involve different operating system • Protocol specification must be precise • Format of data units • Semantics of all fields • allowable sequence of PCUs ...
CIS 1140 Network Fundamentals
... points between the wire-bound LAN and wireless clients to cover the same distance that 802.11b networks cover • More expensive than either 802.11b or 802.11g • Not compatible with either 802.11b and 802.11g 802.11a Demo ...
... points between the wire-bound LAN and wireless clients to cover the same distance that 802.11b networks cover • More expensive than either 802.11b or 802.11g • Not compatible with either 802.11b and 802.11g 802.11a Demo ...