Powerpoint Slides
... NullPointerException is not an exception that has to be caught or declared. » Usually indicates you need to fix your code, not add a catch block. » Just check if objectName == null before you use the object! In some cases, it is useful to set objects to null – such as in linked lists, where a null l ...
... NullPointerException is not an exception that has to be caught or declared. » Usually indicates you need to fix your code, not add a catch block. » Just check if objectName == null before you use the object! In some cases, it is useful to set objects to null – such as in linked lists, where a null l ...
Ch 6 Notes
... directly to the implementation of the array. If the data structure above (array) changes, then we will have to change the iteration. When we use the Iterator Pattern, we program against an interface. Thus, the underlying data structure change without affecting the code. 3. So, what does it mean for ...
... directly to the implementation of the array. If the data structure above (array) changes, then we will have to change the iteration. When we use the Iterator Pattern, we program against an interface. Thus, the underlying data structure change without affecting the code. 3. So, what does it mean for ...
Collection
... commonly reusable collection data structures. • Designed and developed primarily by Joshua Bloch (currently Chief Java Architect at Google). ...
... commonly reusable collection data structures. • Designed and developed primarily by Joshua Bloch (currently Chief Java Architect at Google). ...
chap09 - MCST-CS
... • Trace execution of comparison-based algorithm by using graph called comparison tree • Let L be a list of n distinct elements, where n > 0. For any j and k, where 1 = j, k = n, either L[j] < L[k] or L[j] > L[k] • Each comparison of the keys has two outcomes; comparison tree is a binary tree • Each ...
... • Trace execution of comparison-based algorithm by using graph called comparison tree • Let L be a list of n distinct elements, where n > 0. For any j and k, where 1 = j, k = n, either L[j] < L[k] or L[j] > L[k] • Each comparison of the keys has two outcomes; comparison tree is a binary tree • Each ...
CS 340 Data Structures
... algorithm will be used. You choose bubble sort. After all, it has a cool name! ...
... algorithm will be used. You choose bubble sort. After all, it has a cool name! ...
The ArrayList Class and File IO
... Arrays are weak where linked lists are strong, and vice versa. Is there ...
... Arrays are weak where linked lists are strong, and vice versa. Is there ...
pptx
... One of the problems need to be solved: ◦ Evaluate the probability of an observation sequence on a given HMM (Evaluation) ◦ The solution of above is the key to choose the best matched models among the HMMs ...
... One of the problems need to be solved: ◦ Evaluate the probability of an observation sequence on a given HMM (Evaluation) ◦ The solution of above is the key to choose the best matched models among the HMMs ...
COS 333: Advanced Programming Techniques Robert M. Dondero, Ph.D.
... Client-side web programming AJAX programming ...
... Client-side web programming AJAX programming ...
Slides_12
... • Open the ICE_12.java. Note that the main method is always a static method: It can be called on a class without instantiating an object first – Can only call static methods or make objects and call their non-static methods – Useful for instantiating objects including those of it’s own class, often ...
... • Open the ICE_12.java. Note that the main method is always a static method: It can be called on a class without instantiating an object first – Can only call static methods or make objects and call their non-static methods – Useful for instantiating objects including those of it’s own class, often ...
Public or Private -
... they’ll get a compile-time error. “Friendly” has to do with something called a “package,” which is Java’s way of making libraries. If something is “friendly” it’s available only within the package. (Thus this access level is sometimes referred to as “package access.”) protected acts just like privat ...
... they’ll get a compile-time error. “Friendly” has to do with something called a “package,” which is Java’s way of making libraries. If something is “friendly” it’s available only within the package. (Thus this access level is sometimes referred to as “package access.”) protected acts just like privat ...
投影片 1 - CSIE -NCKU
... flow state monitoring, and malware detection often require large data storage resources, fast queries, and frequent updates. Hash tables are traditional data structures that allow large amounts of data to be stored, queried, and updated in a spaceand time-efficient manner on average. ...
... flow state monitoring, and malware detection often require large data storage resources, fast queries, and frequent updates. Hash tables are traditional data structures that allow large amounts of data to be stored, queried, and updated in a spaceand time-efficient manner on average. ...
Week 3: Java Buttons - Pitt Computer Science
... Indicate the mouse has been pressed Get the current location of the mouse If it's within the shape, select the shape If not, change the background color (and unselect the shape, if it had been selected) ...
... Indicate the mouse has been pressed Get the current location of the mouse If it's within the shape, select the shape If not, change the background color (and unselect the shape, if it had been selected) ...
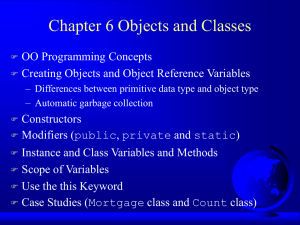
Chapter 6 Objects and Classes
... Constructors are invoked using the new operator when an object is created. Constructors play the ...
... Constructors are invoked using the new operator when an object is created. Constructors play the ...
JavaServer Faces: The Fundamentals
... Advantages of Facelets for large-scale development projects include the following: Support for code reuse through templating and composite components Functional extensibility of components and other server-side objects through customization Faster compilation time Compile-time EL validatio ...
... Advantages of Facelets for large-scale development projects include the following: Support for code reuse through templating and composite components Functional extensibility of components and other server-side objects through customization Faster compilation time Compile-time EL validatio ...
Introduction
... //Project number //Student's name Date project is due //Course number //Purpose of the program cosc236/intro ...
... //Project number //Student's name Date project is due //Course number //Purpose of the program cosc236/intro ...
Data structures and performance analysis
... has excellent Eclipse integration that makes it easy to use. We have included a small example to demonstrate how to write JUnit tests, and we have scheduled a lab about using JUnit. You should not only test whether the program works correctly from the command line interface, but also should write te ...
... has excellent Eclipse integration that makes it easy to use. We have included a small example to demonstrate how to write JUnit tests, and we have scheduled a lab about using JUnit. You should not only test whether the program works correctly from the command line interface, but also should write te ...
posted
... concurrent processing adds to an operating system. Answer: (1) A method of time sharing must be implemented to allow each of several processes to have access to the system. This method involves the preemption of processes that do not voluntarily give up the CPU (by using a system call, for instance) ...
... concurrent processing adds to an operating system. Answer: (1) A method of time sharing must be implemented to allow each of several processes to have access to the system. This method involves the preemption of processes that do not voluntarily give up the CPU (by using a system call, for instance) ...
Mining District user guide
... County and state boundaries and records are turned off by default; however, these layers are still searchable from within the Enhanced Search Widget. PLSS data is also available for this map. However, since the layers are fairly large they are turned off by default. The user may turn on PLSS layers ...
... County and state boundaries and records are turned off by default; however, these layers are still searchable from within the Enhanced Search Widget. PLSS data is also available for this map. However, since the layers are fairly large they are turned off by default. The user may turn on PLSS layers ...
Java, Java, Java
... else if (name.compareTo(nam)< 0){// name < nam if (right == null) return true; else return right.contains(name,pho); }else { // name > nam if (left == null) return true; else return left.contains(name,pho); } //else ...
... else if (name.compareTo(nam)< 0){// name < nam if (right == null) return true; else return right.contains(name,pho); }else { // name > nam if (left == null) return true; else return left.contains(name,pho); } //else ...
HashingFinal
... • Requires: unique key (unless multiple items allowed). Key must be protected from change (use abstract class that provides only a constructor). • Keys must be “comparable”. ...
... • Requires: unique key (unless multiple items allowed). Key must be protected from change (use abstract class that provides only a constructor). • Keys must be “comparable”. ...
CS410J: Advanced Java Programming Inner Classes Example of an
... • A Class’s getDeclaredField and getDeclaredMethod methods return a field or method declared by that class ...
... • A Class’s getDeclaredField and getDeclaredMethod methods return a field or method declared by that class ...
Grid - Department of Computer Science
... • High-level & efficient programming support for distributed supercomputing on heterogeneous grids • Use Java-centric approach + JVM technology – Inherently more portable than native compilation • “Write once, run anywhere ” – Requires entire system to be written in pure Java • Optimized special-cas ...
... • High-level & efficient programming support for distributed supercomputing on heterogeneous grids • Use Java-centric approach + JVM technology – Inherently more portable than native compilation • “Write once, run anywhere ” – Requires entire system to be written in pure Java • Optimized special-cas ...
Chapter 6 Objects and Classes
... Constructors are invoked using the new operator when an object is created. Constructors play the ...
... Constructors are invoked using the new operator when an object is created. Constructors play the ...