FinalReview.pdf
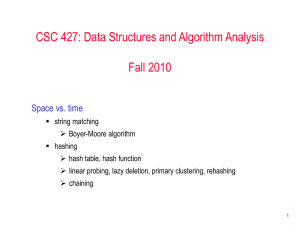
... Lower bound for comparison sorts. Abstract data types (ADTs). An ADT is just a set of values together with (primitive, or predefined) operations on them and the idea that we may expect the primitive operations to have certain properties, e.g. O(1) cost and O(n) space. How we can define an ADT in Jav ...
... Lower bound for comparison sorts. Abstract data types (ADTs). An ADT is just a set of values together with (primitive, or predefined) operations on them and the idea that we may expect the primitive operations to have certain properties, e.g. O(1) cost and O(n) space. How we can define an ADT in Jav ...
Lock-Free Resizeable Concurrent Tries
... locks induce a performance degradation if a thread holding a lock gets delayed (e.g. by being preempted by the operating system). All other threads competing for the lock are prevented from making progress until the lock is released. More fundamentally, mutual exclusion locks are not fault tolerant ...
... locks induce a performance degradation if a thread holding a lock gets delayed (e.g. by being preempted by the operating system). All other threads competing for the lock are prevented from making progress until the lock is released. More fundamentally, mutual exclusion locks are not fault tolerant ...
Notes
... Java Code: Implementing an Interface public class name implements InterfaceName { public void method1() { } public Object method2() { return new Object(); } public void method3(Object obj) { } //Note that each method must have a method body, but //that method body could be empty. ...
... Java Code: Implementing an Interface public class name implements InterfaceName { public void method1() { } public Object method2() { return new Object(); } public void method3(Object obj) { } //Note that each method must have a method body, but //that method body could be empty. ...
pptx
... isEmpty: initially true, later have there been same number of pops as pushes push: takes an item pop: raises an error if isEmpty, else returns most-recently pushed item not yet returned by a pop … (Often some more operations) ...
... isEmpty: initially true, later have there been same number of pops as pushes push: takes an item pop: raises an error if isEmpty, else returns most-recently pushed item not yet returned by a pop … (Often some more operations) ...
stack - CENG METU
... • Several interfaces are used to define operations on the collections, such as List, Set, SortedSet, Map, and SortedMap ...
... • Several interfaces are used to define operations on the collections, such as List, Set, SortedSet, Map, and SortedMap ...
Data Structures So Far
... Comparator ADT A comparator encapsulates the action of comparing two objects according to a given total order relation A generic priority queue uses an auxiliary comparator The comparator is external to the keys being compared When the priority queue needs to compare two keys, it ...
... Comparator ADT A comparator encapsulates the action of comparing two objects according to a given total order relation A generic priority queue uses an auxiliary comparator The comparator is external to the keys being compared When the priority queue needs to compare two keys, it ...
ch6
... • Many systems provide hardware support for critical section code • Uniprocessors – could disable interrupts – Currently running code would execute without preemption – Generally too inefficient on multiprocessor systems • Operating systems using this not broadly scalable ...
... • Many systems provide hardware support for critical section code • Uniprocessors – could disable interrupts – Currently running code would execute without preemption – Generally too inefficient on multiprocessor systems • Operating systems using this not broadly scalable ...
thread
... support designed to provide flexibility in exploiting processor resources. Processes include the user’s address space, stack, and process control block ...
... support designed to provide flexibility in exploiting processor resources. Processes include the user’s address space, stack, and process control block ...
The Lock-Free k-LSM Relaxed Priority Queue
... queue, the parameter k has a significant impact on both scalability and absolute performance. The larger k, the less we need to rely on the shared LSM. Performance and scalability furthermore improves with smaller prefill values, since this also reduces the reliance on the shared LSM priority queue. ...
... queue, the parameter k has a significant impact on both scalability and absolute performance. The larger k, the less we need to rely on the shared LSM. Performance and scalability furthermore improves with smaller prefill values, since this also reduces the reliance on the shared LSM priority queue. ...
Lecture for Chapter 12, Software Life Cycle
... In XP, planning is driven by requirements and their relative priorities. Requirements are elicited by writing stories with the client. Stories are high-level use cases that encompass a set of coherent features. Developers then decompose each story in terms of development tasks that are needed ...
... In XP, planning is driven by requirements and their relative priorities. Requirements are elicited by writing stories with the client. Stories are high-level use cases that encompass a set of coherent features. Developers then decompose each story in terms of development tasks that are needed ...
COS 126 Written Exam 2, Spring 2008
... shaded). In the blank provided, mark each as correct (with a check mark) or wrong (with an X). For those marked wrong, give a reason (for example an input for which the machine does not produce the desired result). ...
... shaded). In the blank provided, mark each as correct (with a check mark) or wrong (with an X). For those marked wrong, give a reason (for example an input for which the machine does not produce the desired result). ...
Advanced Object Oriented Systems
... • A method is said to be maximally specific for a method invocation if it is applicable and accessible and there is no other applicable and accessible method that is more specific. • If there is only one maximally specific method for a given method invocation, it is called the most specific method • ...
... • A method is said to be maximally specific for a method invocation if it is applicable and accessible and there is no other applicable and accessible method that is more specific. • If there is only one maximally specific method for a given method invocation, it is called the most specific method • ...
Data Structures and Text Editing
... possible locations in the hash table for each key. Suppose we have a hash table T and a pair of hash functions f1 and f2 . Insertion of an element x works as follows. First, compute f1 (x), which is the location to store x. If T [ f1 (x)] is initially empty, the insertion is complete. Otherwise, x m ...
... possible locations in the hash table for each key. Suppose we have a hash table T and a pair of hash functions f1 and f2 . Insertion of an element x works as follows. First, compute f1 (x), which is the location to store x. If T [ f1 (x)] is initially empty, the insertion is complete. Otherwise, x m ...
Chapter 2: Using Objects
... As long as the ADT accurately fulfills the promises of the interface, it doesn't really matter how the ADT is implemented Objects are a perfect programming mechanism to create ADTs because their internal details are encapsulated ...
... As long as the ADT accurately fulfills the promises of the interface, it doesn't really matter how the ADT is implemented Objects are a perfect programming mechanism to create ADTs because their internal details are encapsulated ...
GUI and event-driven programming
... Adding objects to the frame • There are two approaches to placing GUI objects on a frame’s content pane. • One approach uses a layout manager, an object that controls the placement of the objects. • The other approach uses absolute positioning to explicitly specify the position and size of objects ...
... Adding objects to the frame • There are two approaches to placing GUI objects on a frame’s content pane. • One approach uses a layout manager, an object that controls the placement of the objects. • The other approach uses absolute positioning to explicitly specify the position and size of objects ...
Server-Side Processing Overview
... • The servlet is responsible for loading and executing the Java classes that generate the HTML content. • To the client, this looks like standard HTML processing, except faster. • The servlet then need not shut down. Instead, it can handle subsequent requests without restarting. ...
... • The servlet is responsible for loading and executing the Java classes that generate the HTML content. • To the client, this looks like standard HTML processing, except faster. • The servlet then need not shut down. Instead, it can handle subsequent requests without restarting. ...
hash function
... cost of insertion is O(1) – simply map to index and add to list cost of search is proportional to number of items already mapped to same index e.g., using naïve "first letter" hash function, searching for "APPLE" might requires traversing a list of all words beginning with 'A' if hash function i ...
... cost of insertion is O(1) – simply map to index and add to list cost of search is proportional to number of items already mapped to same index e.g., using naïve "first letter" hash function, searching for "APPLE" might requires traversing a list of all words beginning with 'A' if hash function i ...
ppt version - University of Pittsburgh
... throughout computer science We should understand these from a user's point of view: ...
... throughout computer science We should understand these from a user's point of view: ...
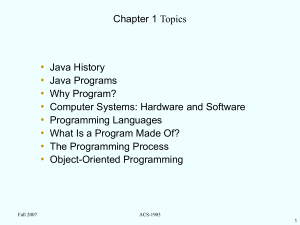
Intro to Java and Classes
... a class includes abstract methods, then the class must be declared abstract, example: public abstract class Shape { // declare fields // declare nonabstract methods abstract void draw(); ...
... a class includes abstract methods, then the class must be declared abstract, example: public abstract class Shape { // declare fields // declare nonabstract methods abstract void draw(); ...
ppt
... • The CPU performs the fetch, decode, execute cycle in order to process program information. The CPU’s control unit fetches, from main memory, the next instruction in the sequence of program instructions. ...
... • The CPU performs the fetch, decode, execute cycle in order to process program information. The CPU’s control unit fetches, from main memory, the next instruction in the sequence of program instructions. ...
Concurrent Access Algorithms for Different Data Structures: A
... infinitely often some method finishes in a finite number of steps. This definition implies that no deadlock is possible for lock-free calls. On the other hand, the guarantee that some call finishes in a finite number of steps is not enough to guarantee that all of them eventually finish. In other wo ...
... infinitely often some method finishes in a finite number of steps. This definition implies that no deadlock is possible for lock-free calls. On the other hand, the guarantee that some call finishes in a finite number of steps is not enough to guarantee that all of them eventually finish. In other wo ...
Solutions
... a. What is a hash function? A function to generate a number from a key b. What is a desirable property of hash functions? Numbers generated from keys are spread out uniformly in a range c. What is a perfect hash function? Every key is assigned a unique number d. What is a collision? Identical numbe ...
... a. What is a hash function? A function to generate a number from a key b. What is a desirable property of hash functions? Numbers generated from keys are spread out uniformly in a range c. What is a perfect hash function? Every key is assigned a unique number d. What is a collision? Identical numbe ...
Design Considerations when Developing Applications using SAS
... framework consists of hundreds of classes that are all residing at the same level as the Operating System (OS) layer. Above this layer, A Common Language Runtime layer is provided where VB and other supported languages are compiled into byte code at runtime. These programs can utilise all the classe ...
... framework consists of hundreds of classes that are all residing at the same level as the Operating System (OS) layer. Above this layer, A Common Language Runtime layer is provided where VB and other supported languages are compiled into byte code at runtime. These programs can utilise all the classe ...