Stacks - Courses
... http://www.cs.dartmouth.edu/~farid/teaching/cs15/cs5/lectures/0519/0519.html ...
... http://www.cs.dartmouth.edu/~farid/teaching/cs15/cs5/lectures/0519/0519.html ...
Data structures and performance analysis
... possible locations in the hash table for each key. Suppose we have a hash table T and a pair of hash functions f1 and f2 . Insertion of an element x works as follows. First, compute f1 (x), which is the location to store x. If T [ f1 (x)] is initially empty, the insertion is complete. Otherwise, x m ...
... possible locations in the hash table for each key. Suppose we have a hash table T and a pair of hash functions f1 and f2 . Insertion of an element x works as follows. First, compute f1 (x), which is the location to store x. If T [ f1 (x)] is initially empty, the insertion is complete. Otherwise, x m ...
1 Running Time of Priority Queue Operations
... 1. Sequence containers: These are data structures in which items are accessed by the position they are stored at, like arrays. Our example from class was called List.
2. Associative containers: Here, items are accessed via their “identity” or key. The user does not
know which index an element is ...
... 1. Sequence containers: These are data structures in which items are accessed by the position they are stored at, like arrays. Our example from class was called List
Strings - E
... Vectors (the java.util.Vector class) are commonly used instead of arrays, because they expand automatically when new data is added to them. The Java 2 Collections API introduced the similar ArrayList data structure. ArrayLists are unsynchronized and therefore faster than Vectors, but less secure in ...
... Vectors (the java.util.Vector class) are commonly used instead of arrays, because they expand automatically when new data is added to them. The Java 2 Collections API introduced the similar ArrayList data structure. ArrayLists are unsynchronized and therefore faster than Vectors, but less secure in ...
CS 2110 Object-Oriented Programming and Data Structures Spring
... work into parts, do the parts independently, and then merge. Programming Proficiency A CS 2110 student should be able to write simple programs in some programming language. They should have fluency with strings, arrays, two-dimensional arrays, simple conditional tests, loops, and functions and proce ...
... work into parts, do the parts independently, and then merge. Programming Proficiency A CS 2110 student should be able to write simple programs in some programming language. They should have fluency with strings, arrays, two-dimensional arrays, simple conditional tests, loops, and functions and proce ...
Course: CS 2110 —also ENGRD 2210
... work into parts, do the parts independently, and then merge. Programming Proficiency A CS 2110 student should be able to write simple programs in some programming language. They should have fluency with strings, arrays, two-dimensional arrays, simple conditional tests, loops, and functions and proce ...
... work into parts, do the parts independently, and then merge. Programming Proficiency A CS 2110 student should be able to write simple programs in some programming language. They should have fluency with strings, arrays, two-dimensional arrays, simple conditional tests, loops, and functions and proce ...
Computer Science Homework 1
... Step 3: Testing your installation by starting BlueJ (click on the BlueJ Desktop Icon). You might (but probably not) be asked which “Java Virtual Machine” to use. If you do get that question, pick the one with the highest version number (should be 1.5.0). Soon you will see the BlueJ desktop: ...
... Step 3: Testing your installation by starting BlueJ (click on the BlueJ Desktop Icon). You might (but probably not) be asked which “Java Virtual Machine” to use. If you do get that question, pick the one with the highest version number (should be 1.5.0). Soon you will see the BlueJ desktop: ...
Interactive online environments
... Lots of information to distribute online changes frequently and is gathered from multiple sources Information needs to be organized and managed for other purposes not just for web distribution Information needs to made available using current/common technologies One solution: Content providers send ...
... Lots of information to distribute online changes frequently and is gathered from multiple sources Information needs to be organized and managed for other purposes not just for web distribution Information needs to made available using current/common technologies One solution: Content providers send ...
Chapter 1 Background
... Generation 1 (Late 1940s to Early 1950s)Machine Languages: Programs were coded in machine language, whose only symbols are binary digits. Coding was tedious, slow, and error-prone. It was difficult to modify programs. Each type had its own machine language so programs were not portable. ...
... Generation 1 (Late 1940s to Early 1950s)Machine Languages: Programs were coded in machine language, whose only symbols are binary digits. Coding was tedious, slow, and error-prone. It was difficult to modify programs. Each type had its own machine language so programs were not portable. ...
Thread Synchronization
... Having been crashed The document you're seeking Must now be retyped. ...
... Having been crashed The document you're seeking Must now be retyped. ...
Search Algorithms
... different hash addresses with high probability, even if some of the characters are the same ...
... different hash addresses with high probability, even if some of the characters are the same ...
01-ch01-1-println - University of Washington
... executed together to perform a particular action. ...
... executed together to perform a particular action. ...
Deadlock Conditions
... A thread is the entity within a process that can be scheduled for execution. All threads of a process share its virtual address space and system resources. In addition, each thread maintains exception handlers, a scheduling priority, thread local storage, a unique thread identifier, and a set of str ...
... A thread is the entity within a process that can be scheduled for execution. All threads of a process share its virtual address space and system resources. In addition, each thread maintains exception handlers, a scheduling priority, thread local storage, a unique thread identifier, and a set of str ...
ArrayList
... The List Interface and ArrayList Class • So far, all we have is an array for storing a collection of elements. • An array is an indexed structure: can select its elements in arbitrary order using a subscript value • Elements may be accessed in sequence using a loop that increments the subscript • Y ...
... The List Interface and ArrayList Class • So far, all we have is an array for storing a collection of elements. • An array is an indexed structure: can select its elements in arbitrary order using a subscript value • Elements may be accessed in sequence using a loop that increments the subscript • Y ...
12~Chapter 12_Concur.. - Programming Assignment 0
... – They're pretty low-level. • When using them for mutual exclusion, for example (the most common usage), it's easy to forget a P or a V, especially when they don't occur in strictly matched pairs (because you do a V inside an if statement, for example, as in the use of the spin lock in the implement ...
... – They're pretty low-level. • When using them for mutual exclusion, for example (the most common usage), it's easy to forget a P or a V, especially when they don't occur in strictly matched pairs (because you do a V inside an if statement, for example, as in the use of the spin lock in the implement ...
Week 1 - Intro to Object Oriented Programming
... – Models real-world objects – Models communication among objects – Encapsulates data (attributes) and functions (behaviors) • Information hiding • Communication through well-defined interfaces ...
... – Models real-world objects – Models communication among objects – Encapsulates data (attributes) and functions (behaviors) • Information hiding • Communication through well-defined interfaces ...
JDBC - Webcourse
... In SQL, NULL means the field is empty Not the same as 0 or “”! In JDBC, you must explicitly ask if the last read field was null ...
... In SQL, NULL means the field is empty Not the same as 0 or “”! In JDBC, you must explicitly ask if the last read field was null ...
Java Review
... else System.out.println(“Negative value not allowed”); An else clause gets paired with the nearest previous if clause that doesn’t already have an else. ...
... else System.out.println(“Negative value not allowed”); An else clause gets paired with the nearest previous if clause that doesn’t already have an else. ...
Bhupesh_Java-hadoop_8Years_resume
... Develop business layer components using spring, Strut, JDBC and Hibernate and GUI using JQuery, AJAX, JavaScript, JSON, XML, XSLT and XHTML. Design and develop solutions that are highly reliable, scalable and meet business-defined services. Conducted the SQL performance analysis on Oracle data ...
... Develop business layer components using spring, Strut, JDBC and Hibernate and GUI using JQuery, AJAX, JavaScript, JSON, XML, XSLT and XHTML. Design and develop solutions that are highly reliable, scalable and meet business-defined services. Conducted the SQL performance analysis on Oracle data ...
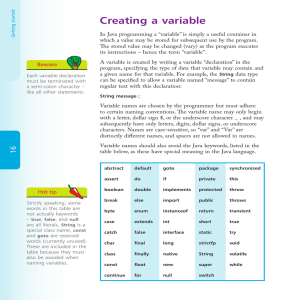
Creating a variable
... words (currently unused). These are included in the table because they must also be avoided when naming variables. ...
... words (currently unused). These are included in the table because they must also be avoided when naming variables. ...
hash function
... the other implementations of the Set & Map interfaces, HashSet & HashMap, use a "magic" data structure to provide O(1) operations* *legal disclaimer: performance can degrade to O(N) under bad/unlikely conditions however, careful setup and maintenance can ensure O(1) in practice ...
... the other implementations of the Set & Map interfaces, HashSet & HashMap, use a "magic" data structure to provide O(1) operations* *legal disclaimer: performance can degrade to O(N) under bad/unlikely conditions however, careful setup and maintenance can ensure O(1) in practice ...
Problem
... This approach is called speculative, or optimistic because, rather than preventing interference by completely serializing the read-compute-update steps, interference is allowed to happen. If interference does happen, it must be detected, and if necessary, the entire operation retried. One way of imp ...
... This approach is called speculative, or optimistic because, rather than preventing interference by completely serializing the read-compute-update steps, interference is allowed to happen. If interference does happen, it must be detected, and if necessary, the entire operation retried. One way of imp ...
Networking with URLs and sockets in Java
... InputStreamReader constructor translates bytes into Unicode characters BufferedReader constructor buffers characters, reading one line at a time, with readline() ...
... InputStreamReader constructor translates bytes into Unicode characters BufferedReader constructor buffers characters, reading one line at a time, with readline() ...
slides
... A key is stored in either of the tables Conflict resolution: relocate existing keys to leave empty slot for the new key. ...
... A key is stored in either of the tables Conflict resolution: relocate existing keys to leave empty slot for the new key. ...