Exceptions
... When a problem occurs, Java attempts to transfer control to a method that can deal with the problem. Such methods are called exception handlers. An exception handler can either correct the problem (fault handlers), gracefully terminate the program (trap handlers), or simply ignore the problem. Java ...
... When a problem occurs, Java attempts to transfer control to a method that can deal with the problem. Such methods are called exception handlers. An exception handler can either correct the problem (fault handlers), gracefully terminate the program (trap handlers), or simply ignore the problem. Java ...
Midterm Solutions
... (b) (iii) and (v) only (c) It can result in a separate-chaining hash table having some very long chains and a linearprobing hash table having some very large clusters. Either of these situations can lead to poor (e.g., linear-time) performance for insert, search hit, and search miss. A linear-probin ...
... (b) (iii) and (v) only (c) It can result in a separate-chaining hash table having some very long chains and a linearprobing hash table having some very large clusters. Either of these situations can lead to poor (e.g., linear-time) performance for insert, search hit, and search miss. A linear-probin ...
Dictionaries-Hash-Tables-and-Sets
... HashTable. Keep the data in array of lists of keyvalue pairs (LinkedList>[]) with
initial capacity of 16. When the hash table load runs
over 75%, perform resizing to 2 times larger capacity.
Implement the following methods and properties:
Add(key, value), Find(key)value, Remo ...
... HashTable
Algorithms
... ・Combine each significant field using the 31x + y rule. ・If field is a primitive type, use wrapper type hashCode(). ・If field is null, return 0. ・If field is a reference type, use hashCode(). ・If field is an array, apply to each entry. ...
... ・Combine each significant field using the 31x + y rule. ・If field is a primitive type, use wrapper type hashCode(). ・If field is null, return 0. ・If field is a reference type, use hashCode(). ・If field is an array, apply to each entry. ...
Efficient Memory Management for Lock
... In this paper we propose to deviate from traditional methods in a novel manner by letting the program execute optimistically, allowing the threads to sometimes access an object that has been previously reclaimed. Various forms of optimistic execution have become common in the computing world (both ...
... In this paper we propose to deviate from traditional methods in a novel manner by letting the program execute optimistically, allowing the threads to sometimes access an object that has been previously reclaimed. Various forms of optimistic execution have become common in the computing world (both ...
Chapter 3 - Arrays
... remaining part of the program will become a user of the structure. Secondly, we’ll improve the communication between the storage structure and its user. ...
... remaining part of the program will become a user of the structure. Secondly, we’ll improve the communication between the storage structure and its user. ...
Mutable Linked Lists - Rice University Campus Wiki
... asymptotically speed-up some operations on lists, but others (such as deleting the last element of a list) take O(n) time in the absence of double-linking. Furthermore, formulating nodes as objects adds weight (a two word header in each node) to a linked-list implementation so double-linking adds on ...
... asymptotically speed-up some operations on lists, but others (such as deleting the last element of a list) take O(n) time in the absence of double-linking. Furthermore, formulating nodes as objects adds weight (a two word header in each node) to a linked-list implementation so double-linking adds on ...
EE553: Exam Solution 2006 to 2007
... 1(a ii) Destructors are used to tidy up objects on their destruction. For example in the case of a Bank Account object the destructor could print a paper copy of the account object before it is destroyed. Typically destructors are used in C++ to deallocate memory that was allocated by an object. Imp ...
... 1(a ii) Destructors are used to tidy up objects on their destruction. For example in the case of a Bank Account object the destructor could print a paper copy of the account object before it is destroyed. Typically destructors are used in C++ to deallocate memory that was allocated by an object. Imp ...
Ans 1(a) refer page number 7 -8 from book Ans 1(b) Ans 3(a) Rate
... transaction becomes ready (that is, concurrently along with other transactions already under execution), rather than executing them one after the other. Concurrent transactions at any time are those which are active (i.e., started but not yet complete). The concurrent transactions can operate either ...
... transaction becomes ready (that is, concurrently along with other transactions already under execution), rather than executing them one after the other. Concurrent transactions at any time are those which are active (i.e., started but not yet complete). The concurrent transactions can operate either ...
Decision Patient Therapy - Tutorial
... We provided a detailed description of how to create the proper executable decision with OpenRules® using only Excel. The patient and visit information was defined in Excel data tables. This decision is available as a part of the standard OpenRules® installation as the project “DecisionPatientTherapy ...
... We provided a detailed description of how to create the proper executable decision with OpenRules® using only Excel. The patient and visit information was defined in Excel data tables. This decision is available as a part of the standard OpenRules® installation as the project “DecisionPatientTherapy ...
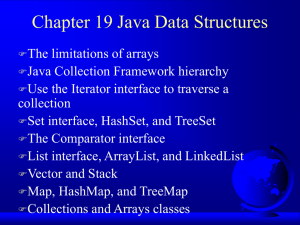
JavaHTP6e_19
... To use collections framework algorithms to manipulate (such as search, sort and fill) collections. To use the collections framework interfaces to program with collections polymorphically. To use iterators to “walk through” a collection. To use persistent hash tables manipulated with objects ...
... To use collections framework algorithms to manipulate (such as search, sort and fill) collections. To use the collections framework interfaces to program with collections polymorphically. To use iterators to “walk through” a collection. To use persistent hash tables manipulated with objects ...
ppt
... • The second algorithm we discuss is concerned with the problem of sorting signed permutations by reversals. Algorithms for sorting by reversals represent one of the most important tools in analyzing rearrangements in the mouse vs. human genome. We point out some shortcomings of the current approach ...
... • The second algorithm we discuss is concerned with the problem of sorting signed permutations by reversals. Algorithms for sorting by reversals represent one of the most important tools in analyzing rearrangements in the mouse vs. human genome. We point out some shortcomings of the current approach ...
BIT 115: Introduction To Programming - Canvas
... public static void main(String[ ] args) The method is public because it is accessible to the JVM (Java Virtual Machine) to begin execution of the program, and can be accessed by any other class or method. The static keyword signifies the fact that this method can be invoked without creating an insta ...
... public static void main(String[ ] args) The method is public because it is accessible to the JVM (Java Virtual Machine) to begin execution of the program, and can be accessed by any other class or method. The static keyword signifies the fact that this method can be invoked without creating an insta ...
A Decision Procedure for Concurrent Skiplists
... Logics like those in [LQ08, YRS+ 06, BDES09] are very powerful to describe pointer structures, but they require the use of quantifiers to reach their expressive power. Hence, these logics preclude a combination a-la Nelson-Oppen or BAPA [KNR05] with other aspects of the program state. Instead, our s ...
... Logics like those in [LQ08, YRS+ 06, BDES09] are very powerful to describe pointer structures, but they require the use of quantifiers to reach their expressive power. Hence, these logics preclude a combination a-la Nelson-Oppen or BAPA [KNR05] with other aspects of the program state. Instead, our s ...
MapADT_HashTables
... Time to construct an empty hashtable: 0.161 seconds Time to build table of 50000 entries: 0.65 seconds Time to lookup each table entry once: 0.19 seconds 8000 arrays of Linked lists Time to construct an empty hashtable: 0.04 seconds Time to build table of 50000 entries: 0.741 seconds Time to looku ...
... Time to construct an empty hashtable: 0.161 seconds Time to build table of 50000 entries: 0.65 seconds Time to lookup each table entry once: 0.19 seconds 8000 arrays of Linked lists Time to construct an empty hashtable: 0.04 seconds Time to build table of 50000 entries: 0.741 seconds Time to looku ...
The Map ADT and Hash Tables
... Time to construct an empty hashtable: 0.161 seconds Time to build table of 50000 entries: 0.65 seconds Time to lookup each table entry once: 0.19 seconds ´ 8000 arrays of Linked lists Time to construct an empty hashtable: 0.04 seconds Time to build table of 50000 entries: 0.741 seconds Time to loo ...
... Time to construct an empty hashtable: 0.161 seconds Time to build table of 50000 entries: 0.65 seconds Time to lookup each table entry once: 0.19 seconds ´ 8000 arrays of Linked lists Time to construct an empty hashtable: 0.04 seconds Time to build table of 50000 entries: 0.741 seconds Time to loo ...
typedef struct
... logical contents of a set of locations when it executes without interference from concurrent commit operations. A Commit operation contains 3 stages: a) acquires exclusive ownership of the locations being updated. b) read-check phase ensures that locations that have been read but not updated hold th ...
... logical contents of a set of locations when it executes without interference from concurrent commit operations. A Commit operation contains 3 stages: a) acquires exclusive ownership of the locations being updated. b) read-check phase ensures that locations that have been read but not updated hold th ...
Web Servlets and JSP
... course dealing with Servlets and JSP. We begin with a quick overview of Web basics and server side programming, followed by an introduction to J2EE Web Applications and Java Servlets. We then deal with the technology’s pros and cons and explore its commonly used features, including request manipulat ...
... course dealing with Servlets and JSP. We begin with a quick overview of Web basics and server side programming, followed by an introduction to J2EE Web Applications and Java Servlets. We then deal with the technology’s pros and cons and explore its commonly used features, including request manipulat ...
Chapter 19 Implementing Trees and Priority Queues
... General trees: Trees with no restrictions on number of children Binary trees: Each node has at most two children: left child and right child. ...
... General trees: Trees with no restrictions on number of children Binary trees: Each node has at most two children: left child and right child. ...
java.util.LinkedList
... processing. Besides basic Collection operations, queues provide additional insertion, extraction, and inspection operations. Queues typically, but do not necessarily, order elements in a FIFO (First-In-First-Out) manner. 交通大學資訊工程學系 蔡文能 ...
... processing. Besides basic Collection operations, queues provide additional insertion, extraction, and inspection operations. Queues typically, but do not necessarily, order elements in a FIFO (First-In-First-Out) manner. 交通大學資訊工程學系 蔡文能 ...
Digital television
... • DVB-HTML services are very often called as supertext-tv services. • It will replace the normal teletext services. • New services possible but already launched applications are the same as in normal teletext but with pictures • Perhaps ’cause the feedback channel is not yet implemented in on the ma ...
... • DVB-HTML services are very often called as supertext-tv services. • It will replace the normal teletext services. • New services possible but already launched applications are the same as in normal teletext but with pictures • Perhaps ’cause the feedback channel is not yet implemented in on the ma ...
ch10ppt - Learn District 196
... • Example: a dictionary is a map that maps words to definitions ...
... • Example: a dictionary is a map that maps words to definitions ...
Linked Lists
... • In a circular linked list with more than one node, it is convenient to make the reference variable first point to the last node of the list ...
... • In a circular linked list with more than one node, it is convenient to make the reference variable first point to the last node of the list ...
19slide
... +previousIndex() : int +previous() : Object +previousIndex() : int +set(element: Object) : void ...
... +previousIndex() : int +previous() : Object +previousIndex() : int +set(element: Object) : void ...