statement
... • How much data will there be? • How should data be accepted? • Is there a specific output format required? ...
... • How much data will there be? • How should data be accepted? • Is there a specific output format required? ...
Stacks and Queues
... Stacks (continued) Stacks are also called Last Input First Output (LIFO) data structures Operations performed on stacks Push: adds an element to the stack Pop: removes an element from the stack Peek: looks at the top element of the stack ...
... Stacks (continued) Stacks are also called Last Input First Output (LIFO) data structures Operations performed on stacks Push: adds an element to the stack Pop: removes an element from the stack Peek: looks at the top element of the stack ...
The SprayList: A Scalable Relaxed Priority Queue
... Sundell and Tsigas [28] proposed a lock-free SkipList-based implementation which ensures linearizability by preventing threads from moving past a list element that has not been fully removed. Instead, concurrent threads help with the cleanup process. Unfortunately, all the above implementations suff ...
... Sundell and Tsigas [28] proposed a lock-free SkipList-based implementation which ensures linearizability by preventing threads from moving past a list element that has not been fully removed. Instead, concurrent threads help with the cleanup process. Unfortunately, all the above implementations suff ...
12. Parallel computing on Grids - Department of Computer Science
... • High-level & efficient programming support for distributed supercomputing on heterogeneous grids • Use Java-centric approach + JVM technology – Inherently more portable than native compilation • “Write once, run anywhere ” – Requires entire system to be written in pure Java • Optimized special-cas ...
... • High-level & efficient programming support for distributed supercomputing on heterogeneous grids • Use Java-centric approach + JVM technology – Inherently more portable than native compilation • “Write once, run anywhere ” – Requires entire system to be written in pure Java • Optimized special-cas ...
Java Classes
... a search that begins at the root • Maximum number of comparisons is directly proportional to the height, h of the tree • These operations are O(h) • Thus we desire the shortest binary search tree we can create from the data Carrano, Data Structures and Abstractions with Java, Second Edition, (c) 200 ...
... a search that begins at the root • Maximum number of comparisons is directly proportional to the height, h of the tree • These operations are O(h) • Thus we desire the shortest binary search tree we can create from the data Carrano, Data Structures and Abstractions with Java, Second Edition, (c) 200 ...
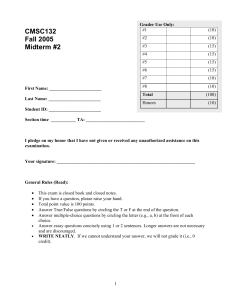
CMSC132 Fall 2005 Midterm #2
... a. What is a hash function? A function to generate a number from a key b. What is a desirable property of hash functions? Numbers generated from keys are spread out uniformly in a range c. What is a perfect hash function? Every key is assigned a unique number d. What is a collision? Identical number ...
... a. What is a hash function? A function to generate a number from a key b. What is a desirable property of hash functions? Numbers generated from keys are spread out uniformly in a range c. What is a perfect hash function? Every key is assigned a unique number d. What is a collision? Identical number ...
Hashing hash functions collision resolution
... no effective alternative for unordered keys faster for simple keys (a few arithmetic ops versus lg N compares) (Java) better system support for strings [cached hashcode] does your hash function produce random values for your key type?? ...
... no effective alternative for unordered keys faster for simple keys (a few arithmetic ops versus lg N compares) (Java) better system support for strings [cached hashcode] does your hash function produce random values for your key type?? ...
Boolean expressions, part 2: Logical operators
... Because 10 <= a <= 20 is evaluated as follows: Expression: Operators: Evaluated as: ...
... Because 10 <= a <= 20 is evaluated as follows: Expression: Operators: Evaluated as: ...
public static final int SIZE = 4
... for (int line = 1; line <= 4; line++) { System.out.print("|"); for (int space = 1; space <= (line * -2 + 8); space++) { System.out.print(" "); ...
... for (int line = 1; line <= 4; line++) { System.out.print("|"); for (int space = 1; space <= (line * -2 + 8); space++) { System.out.print(" "); ...
Generics Collections
... associating these integer keys with objects to store them is impractical, so we develop a scheme for using arbitrary keys. When an application needs to store something, the scheme could convert the application key rapidly to an index. Once the application has a key for which it wants to retrieve ...
... associating these integer keys with objects to store them is impractical, so we develop a scheme for using arbitrary keys. When an application needs to store something, the scheme could convert the application key rapidly to an index. Once the application has a key for which it wants to retrieve ...
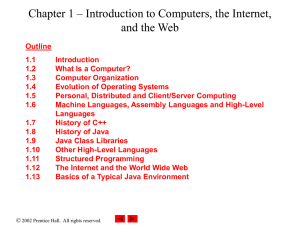
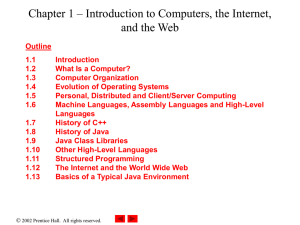
Chapter 1 – Introduction to Computers, the Internet, and the Web
... – Models real-world objects – Models communication among objects – Encapsulates data (attributes) and functions (behaviors) • Information hiding • Communication through well-defined interfaces ...
... – Models real-world objects – Models communication among objects – Encapsulates data (attributes) and functions (behaviors) • Information hiding • Communication through well-defined interfaces ...
Chapter 1 – Introduction to Computers, the Internet, and the Web
... – Models real-world objects – Models communication among objects – Encapsulates data (attributes) and functions (behaviors) • Information hiding • Communication through well-defined interfaces ...
... – Models real-world objects – Models communication among objects – Encapsulates data (attributes) and functions (behaviors) • Information hiding • Communication through well-defined interfaces ...
Slide 1
... – it possesses excellent cross-platform capabilities – it is supported by many international companies operating in various fields. – plenty of Open Source software Development Tools available ...
... – it possesses excellent cross-platform capabilities – it is supported by many international companies operating in various fields. – plenty of Open Source software Development Tools available ...
[PDF]
... [10, 11, 12, 13] that facilitate the development process from analysis through coding. There are two major approaches used for object-oriented model based code generation, namely structural and behavioral. The structural approach is based on using models of object structure (static relationships). I ...
... [10, 11, 12, 13] that facilitate the development process from analysis through coding. There are two major approaches used for object-oriented model based code generation, namely structural and behavioral. The structural approach is based on using models of object structure (static relationships). I ...
SampleExam10(Ch21-25..
... LinkedList e. Map 20. Which of the data type below could be used to store elements in their natural order based on the compareTo method. a. HashSet b. TreeSet c. LinkedHashSet d. Collection e. Set 21. If you want to store non-duplicated objects in the order in which they are inserted, you should use ...
... LinkedList e. Map 20. Which of the data type below could be used to store elements in their natural order based on the compareTo method. a. HashSet b. TreeSet c. LinkedHashSet d. Collection e. Set 21. If you want to store non-duplicated objects in the order in which they are inserted, you should use ...
Stacks, Queues, and Deques
... happen (unless you exhaust memory, which is another kind of problem) Underflow can happen, and should be handled the same way as for an array implementation When a node is popped from a list, and the node references an object, the reference (the pointer in the node) does not need to be set to null ...
... happen (unless you exhaust memory, which is another kind of problem) Underflow can happen, and should be handled the same way as for an array implementation When a node is popped from a list, and the node references an object, the reference (the pointer in the node) does not need to be set to null ...
Stacks, Queues, and Deques
... happen (unless you exhaust memory, which is another kind of problem) Underflow can happen, and should be handled the same way as for an array implementation When a node is popped from a list, and the node references an object, the reference (the pointer in the node) does not need to be set to null ...
... happen (unless you exhaust memory, which is another kind of problem) Underflow can happen, and should be handled the same way as for an array implementation When a node is popped from a list, and the node references an object, the reference (the pointer in the node) does not need to be set to null ...
ICOM4015-lec18
... Adding an element has no effect if the element is already in the set • Removing an element Attempting to remove an element that isn't in the set is silently ignored • Containment testing (does the set contain a given object?) • Listing all elements (in arbitrary order) ...
... Adding an element has no effect if the element is already in the set • Removing an element Attempting to remove an element that isn't in the set is silently ignored • Containment testing (does the set contain a given object?) • Listing all elements (in arbitrary order) ...
HashTables - University of Arizona
... to store the table as an array of linked lists and to keep at each array index the list of values that yield that hash value known as separate chaining Most often the data stored in a hash table includes both a key field and a data field (e.g., ...
... to store the table as an array of linked lists and to keep at each array index the list of values that yield that hash value known as separate chaining Most often the data stored in a hash table includes both a key field and a data field (e.g., ...
Chapter 6 Slides
... We walk down the list looking for either the ith node or the node containing target. Problem: Once we find the offending node, we've forgotten the previous node. ...
... We walk down the list looking for either the ith node or the node containing target. Problem: Once we find the offending node, we've forgotten the previous node. ...
Applets
... • Uses an init method that performs the same operations as a constructor. • An applet does not have a window of its own so it does NOT require calls to these methods. ...
... • Uses an init method that performs the same operations as a constructor. • An applet does not have a window of its own so it does NOT require calls to these methods. ...
Locks and Concurrency
... o Unrepeatable reads – when a transaction reads a record twice in the same transaction, and the data is altered in the interim. o Phantoms – when a transaction makes an update, but another transaction inserts a record at the same time that would meet the WHERE criteria of that update o Lost updates ...
... o Unrepeatable reads – when a transaction reads a record twice in the same transaction, and the data is altered in the interim. o Phantoms – when a transaction makes an update, but another transaction inserts a record at the same time that would meet the WHERE criteria of that update o Lost updates ...
Slides
... ax + b, where a and b are chosen at random) • With high probability, it will be just as good as any custom-‐designed hash funcLon you can come up with • Guarantees a low number of collisio ...
... ax + b, where a and b are chosen at random) • With high probability, it will be just as good as any custom-‐designed hash funcLon you can come up with • Guarantees a low number of collisio ...
printer-friendly
... If Only We Had A Perfect Hash... • two different objects never have the same hash code • Would just test whether value at the hash location index was ...
... If Only We Had A Perfect Hash... • two different objects never have the same hash code • Would just test whether value at the hash location index was ...
Data structures and web filtering
... allowed to (and even expected to) come up with your own classes for portions of the assignment. An example from HW2 of a simple class that is nice to have is FactorResult. ...
... allowed to (and even expected to) come up with your own classes for portions of the assignment. An example from HW2 of a simple class that is nice to have is FactorResult. ...





![[PDF]](http://s1.studyres.com/store/data/008804302_1-ea1badad5407649bdcfcefcf2161ea31-300x300.png)