CSS307-System Programming
... Linux borrows heavily from the UNIX operating system, with which its creators were well versed. ...
... Linux borrows heavily from the UNIX operating system, with which its creators were well versed. ...
Operating System Concepts
... POSIX: POSIX (Portable Operating System Interface) represents a set of standards implemented primarily for UNIX-based operating systems. POSIX-compliant systems must implement the POSIX core standard (POSIX .1)--Linux, Solaris, and Mac OS X. POSIX also defines several extensions to the standards, in ...
... POSIX: POSIX (Portable Operating System Interface) represents a set of standards implemented primarily for UNIX-based operating systems. POSIX-compliant systems must implement the POSIX core standard (POSIX .1)--Linux, Solaris, and Mac OS X. POSIX also defines several extensions to the standards, in ...
your Reading document for this topic
... network share will be based on the permissions available in file system being used on the drive. For example, a network share of a FAT32 drive will not have as many file security permission options as the same file on an NTFS drive. Some Operating systems also provide enhanced data sharing facilitie ...
... network share will be based on the permissions available in file system being used on the drive. For example, a network share of a FAT32 drive will not have as many file security permission options as the same file on an NTFS drive. Some Operating systems also provide enhanced data sharing facilitie ...
LINUX Virtualization
... Hardware vendors have recognized this shortcoming (and others), and have produced new designs that support and accelerate virtualization. Intel’s new virtualization technology supports hypervisors for both the x86 32-bit (VT-x) and Itanium® (VT-I) 64-bit architectures. The VT-x supports two new form ...
... Hardware vendors have recognized this shortcoming (and others), and have produced new designs that support and accelerate virtualization. Intel’s new virtualization technology supports hypervisors for both the x86 32-bit (VT-x) and Itanium® (VT-I) 64-bit architectures. The VT-x supports two new form ...
I. Ch 5 System Software
... resources, provides a user interface, and runs applications. Computer Resources include memory, processing, storage, input & output devices. The OS also monitors system performance, schedules jobs, and provides some security for the computer. User Interface: on older systems, a character based inter ...
... resources, provides a user interface, and runs applications. Computer Resources include memory, processing, storage, input & output devices. The OS also monitors system performance, schedules jobs, and provides some security for the computer. User Interface: on older systems, a character based inter ...
Document
... The UNIX filesystem is heirarchical (resembling a tree structure). The tree is anchored at a place called the root, designated by a slash "/". Every item in the UNIX filesystem tree is either a file, or a directory. A directory is like a file folder. A directory can contain files, and other director ...
... The UNIX filesystem is heirarchical (resembling a tree structure). The tree is anchored at a place called the root, designated by a slash "/". Every item in the UNIX filesystem tree is either a file, or a directory. A directory is like a file folder. A directory can contain files, and other director ...
The Essence of UNIX and Linux
... – Bourne shell, developed by S. Bourne (AT&T Bell Labs), was the first UNIX command processor – Another Bell employee developed the Korn shell • History feature ...
... – Bourne shell, developed by S. Bourne (AT&T Bell Labs), was the first UNIX command processor – Another Bell employee developed the Korn shell • History feature ...
Linux-Spr-2001-sect-1-group
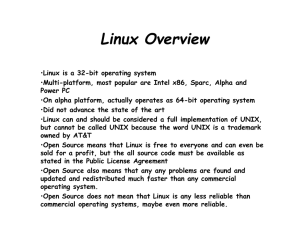
... •Linux can and should be considered a full implementation of UNIX, but cannot be called UNIX because the word UNIX is a trademark owned by AT&T •Open Source means that Linux is free to everyone and can even be sold for a profit, but the all source code must be available as stated in the Public Licen ...
... •Linux can and should be considered a full implementation of UNIX, but cannot be called UNIX because the word UNIX is a trademark owned by AT&T •Open Source means that Linux is free to everyone and can even be sold for a profit, but the all source code must be available as stated in the Public Licen ...
CS311 - NUS School of Computing
... “The low-level software which schedules tasks, allocates storage, handles the interface to peripheral hardware and presents a default interface to the user when no application program is running.” “The OS may be split into a kernel which is always present and various system programs which use facili ...
... “The low-level software which schedules tasks, allocates storage, handles the interface to peripheral hardware and presents a default interface to the user when no application program is running.” “The OS may be split into a kernel which is always present and various system programs which use facili ...
system programs
... Processes • Recall: a process is not just a program – it is a dynamic entity. • A given program (e.g. emacs) could be executing many times on a given machine – the machine must represent each execution as a separate process. ...
... Processes • Recall: a process is not just a program – it is a dynamic entity. • A given program (e.g. emacs) could be executing many times on a given machine – the machine must represent each execution as a separate process. ...
Network operating system comparison
... infrastructure. A single-purpose operating system may provide higher performance for file and print services but may require companies to support another operating system as a platform for application services. A general-purpose operating system can support multifunction servers that can minimize ma ...
... infrastructure. A single-purpose operating system may provide higher performance for file and print services but may require companies to support another operating system as a platform for application services. A general-purpose operating system can support multifunction servers that can minimize ma ...
Introduction to Operating Systems (continued)
... about details • Implementer of abstraction does not need to worry about how user will use it (within limits) CS-2301 B-term 2008 ...
... about details • Implementer of abstraction does not need to worry about how user will use it (within limits) CS-2301 B-term 2008 ...
Ch01 - Mathematics and Computer Science
... computer science and enhances personal development. Software is distributed for free along with the source code; should one person change that source code, that person must redistribute that source code so that others can benefit from the changes or give appropriate feedback (for example, fix bugs). ...
... computer science and enhances personal development. Software is distributed for free along with the source code; should one person change that source code, that person must redistribute that source code so that others can benefit from the changes or give appropriate feedback (for example, fix bugs). ...
Ceng 334 - Operating Systems
... • Anytime you add a new device you must – get a device driver for the device – recompile the kernel with the new device driver – reboot the machine so the new kernel will be used ...
... • Anytime you add a new device you must – get a device driver for the device – recompile the kernel with the new device driver – reboot the machine so the new kernel will be used ...
Windows Server 2008 - Dr. Edward E. Boas, Jr., Professor
... Optimizing Software Installation • Consider the following when installing network server software: – Make sure there are enough licenses to match the number of users – Determine the network load created by software – Consider purchasing management software that can automatically update system-wide ...
... Optimizing Software Installation • Consider the following when installing network server software: – Make sure there are enough licenses to match the number of users – Determine the network load created by software – Consider purchasing management software that can automatically update system-wide ...
Introduction to the Solaris Operating Environment
... The root account and password are set up during the UNIX Operating Environment installation process. This login account is used by the system administrator to perform specific administration tasks on the system. ...
... The root account and password are set up during the UNIX Operating Environment installation process. This login account is used by the system administrator to perform specific administration tasks on the system. ...
Delimited continuations in operating systems
... operating-system research, continuations are poorly known and seldom used explicitly. In this paper, we cross the boundary between operating systems and programming languages to argue by examples that continuations, especially delimited ones, pervade operating systems—if only implicitly. We contend ...
... operating-system research, continuations are poorly known and seldom used explicitly. In this paper, we cross the boundary between operating systems and programming languages to argue by examples that continuations, especially delimited ones, pervade operating systems—if only implicitly. We contend ...
PowerPoint 簡報
... Kernel data and Kernel functions and each process’s kernel-level stack are stored in the kernel address space and could be accessed only when a process (thread) is in kernel mode. The contents of the user address space of different processes maybe are different; however, the contents of all processe ...
... Kernel data and Kernel functions and each process’s kernel-level stack are stored in the kernel address space and could be accessed only when a process (thread) is in kernel mode. The contents of the user address space of different processes maybe are different; however, the contents of all processe ...
slides
... Applications cannot modify the interrupt vector because it lives in the kernel address space. Any attempt to modify the interrupt vector raises a kernel exception, which is safely handled. ...
... Applications cannot modify the interrupt vector because it lives in the kernel address space. Any attempt to modify the interrupt vector raises a kernel exception, which is safely handled. ...
ppt - Computer Science
... MIT Exokernel Operating System http://pdos.csail.mit.edu/exo.html Wikipedia: Exokernel http://en.wikipedia.org/wiki/Exokernel Wikipedia: Kernel (computer science) http://en.wikipedia.org/wiki/Kernel_%28computer_science%29 Wikipedia: MicroKernel http://en.wikipedia.org/wiki/Microkernel Wikipe ...
... MIT Exokernel Operating System http://pdos.csail.mit.edu/exo.html Wikipedia: Exokernel http://en.wikipedia.org/wiki/Exokernel Wikipedia: Kernel (computer science) http://en.wikipedia.org/wiki/Kernel_%28computer_science%29 Wikipedia: MicroKernel http://en.wikipedia.org/wiki/Microkernel Wikipe ...
PowerPoint Format
... Linux uses two techniques to protect critical sections: 1. Normal kernel code is nonpreemptible – when a time interrupt is received while a process is executing a kernel system service routine, the kernel’s need_resched flag is set so that the scheduler will run once the system call has completed an ...
... Linux uses two techniques to protect critical sections: 1. Normal kernel code is nonpreemptible – when a time interrupt is received while a process is executing a kernel system service routine, the kernel’s need_resched flag is set so that the scheduler will run once the system call has completed an ...
Network Operating Systems - Partha Dasgupta`s Workstation!
... system consists of an interconnected group of machines that are loosely connected. By loosely connected, we mean that such computers possess no hardware connections at the CPU – memory bus level, but are connected by external interfaces that run under the control of software. Each computer in this g ...
... system consists of an interconnected group of machines that are loosely connected. By loosely connected, we mean that such computers possess no hardware connections at the CPU – memory bus level, but are connected by external interfaces that run under the control of software. Each computer in this g ...
01-intro
... environment than the CLS You are expected to attend labs and lectures to get full value for your tuition money. If you have to miss a lab, let your lab instructor ...
... environment than the CLS You are expected to attend labs and lectures to get full value for your tuition money. If you have to miss a lab, let your lab instructor ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.