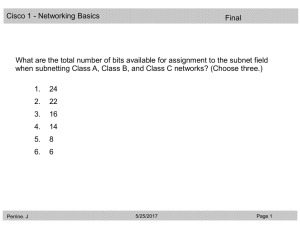
Q1 on FINAL
... The upper layer protocols will reconstruct the data from the damaged frame since most of the frame was transmitted before the collision and only the padding was damaged. ...
... The upper layer protocols will reconstruct the data from the damaged frame since most of the frame was transmitted before the collision and only the padding was damaged. ...
Optical link module
... Siemens provides products and solutions with industrial security functions that support the secure operation of plants, solutions, machines, equipment and/or networks. They are important components in a holistic industrial security concept. With this in mind, Siemens’ products and solutions undergo ...
... Siemens provides products and solutions with industrial security functions that support the secure operation of plants, solutions, machines, equipment and/or networks. They are important components in a holistic industrial security concept. With this in mind, Siemens’ products and solutions undergo ...
Lecture PowerPoint Chapter 2
... Example 2.4 Figure 2.21 shows two computers communicating via the Internet. The sending computer is running three processes at this time with port addresses a, b, and c. The receiving computer is running two processes at this time with port addresses j and k. Process a in the sending computer needs ...
... Example 2.4 Figure 2.21 shows two computers communicating via the Internet. The sending computer is running three processes at this time with port addresses a, b, and c. The receiving computer is running two processes at this time with port addresses j and k. Process a in the sending computer needs ...
Data Link Layer Switching
... Resource allocation too rigid (possibly waste of resources) Once connection is established it cannot be blocked anymore Possibly only reservation of average bandwidth (static reservation) Possibility of congestion High utilization of resources ...
... Resource allocation too rigid (possibly waste of resources) Once connection is established it cannot be blocked anymore Possibly only reservation of average bandwidth (static reservation) Possibility of congestion High utilization of resources ...
CLOUDBAND WITH OPENSTACK AS NFV PLATFORM
... for assuring low signal latencies and disaster resiliency; this infrastructure must, however, also be manageable as a single distributed cloud with global views, statistics and policies • The ability to set up and manage the local and WAN structures required for carrier applications in a programmab ...
... for assuring low signal latencies and disaster resiliency; this infrastructure must, however, also be manageable as a single distributed cloud with global views, statistics and policies • The ability to set up and manage the local and WAN structures required for carrier applications in a programmab ...
Topological Detection on Wormholes in Wireless Ad Hoc and
... make relatively strong assumptions on the networks. For example, some approaches employ specialized hardware devices, such as GPS [3], [6], directional antennas [4], or special radio transceiver modules [10], which introduce significant amounts of extra hardware costs for the systems. Other types of ...
... make relatively strong assumptions on the networks. For example, some approaches employ specialized hardware devices, such as GPS [3], [6], directional antennas [4], or special radio transceiver modules [10], which introduce significant amounts of extra hardware costs for the systems. Other types of ...
Networking on z/OS
... A basic understanding of z/OS job control, library structure, and system libraries is assumed. It is strongly recommended that you have already completed an introductory course on z/OS, such as one that uses Introduction to the New Mainframe: z/OS Basics or a comparable text. This information does n ...
... A basic understanding of z/OS job control, library structure, and system libraries is assumed. It is strongly recommended that you have already completed an introductory course on z/OS, such as one that uses Introduction to the New Mainframe: z/OS Basics or a comparable text. This information does n ...
This chapter covers the following topics: • Characteristics of roaming
... The mechanism to determine when to roam is not defined by the IEEE 802.11 specification and is, therefore, left to vendors to implement. Although this issue posed an interoperability challenge early on with the first 802.11 products, vendors work together today to ensure basic interoperability. The fac ...
... The mechanism to determine when to roam is not defined by the IEEE 802.11 specification and is, therefore, left to vendors to implement. Although this issue posed an interoperability challenge early on with the first 802.11 products, vendors work together today to ensure basic interoperability. The fac ...
ip-shiv2004-routing-I
... Bridges therefore have “L2 forwarding tables,” and use dynamic learning algorithms to build it locally. Even this allows LANs to scale, by limiting broadcasts and collisions to collision domains, and using bridges to interconnect collision domains. The learning algorithm is purely local, oppor ...
... Bridges therefore have “L2 forwarding tables,” and use dynamic learning algorithms to build it locally. Even this allows LANs to scale, by limiting broadcasts and collisions to collision domains, and using bridges to interconnect collision domains. The learning algorithm is purely local, oppor ...
Business Roles and Architecture to realize MUSE
... In a central CAC system, the policies are stored centrally hence for each connection the central CAC system makes the admission decision and signals the access nodes to either allow or block the connection and enforce the policy for the duration of the connection. QoS policy is thus pushed from the ...
... In a central CAC system, the policies are stored centrally hence for each connection the central CAC system makes the admission decision and signals the access nodes to either allow or block the connection and enforce the policy for the duration of the connection. QoS policy is thus pushed from the ...
6 Multi-layer Recovery Strategy in Resilient Packet
... token bucket shaper (Shape A on Figure 48) is provided to ensure that the client traffic does not exceed the allocated rate. Each node/station advertises the amount of bandwidth it needs for its Class A service. This allows calculating how much bandwidth is reserved for Class A in the ring and how m ...
... token bucket shaper (Shape A on Figure 48) is provided to ensure that the client traffic does not exceed the allocated rate. Each node/station advertises the amount of bandwidth it needs for its Class A service. This allows calculating how much bandwidth is reserved for Class A in the ring and how m ...
Computer Networking : Principles, Protocols and Practice Release
... These physical media can be used to exchange information once this information has been converted into a suitable electrical signal. Entire telecommunication courses and textbooks are devoted to the problem of converting analog or digital information into an electrical signal so that it can be trans ...
... These physical media can be used to exchange information once this information has been converted into a suitable electrical signal. Entire telecommunication courses and textbooks are devoted to the problem of converting analog or digital information into an electrical signal so that it can be trans ...
Advanced Routing Mechanisms in ASON/GMPLS Networks by Fernando Agraz Bujan
... the scheduler, NPOT processing, Q-Tool computation and backup path signaling time contributions have been considered. . . . . . . . . . . . . . 5.30 Relative FPGA QoT estimation time improvement as a function of the number of active lightpaths in the network compared to the case where a software-bas ...
... the scheduler, NPOT processing, Q-Tool computation and backup path signaling time contributions have been considered. . . . . . . . . . . . . . 5.30 Relative FPGA QoT estimation time improvement as a function of the number of active lightpaths in the network compared to the case where a software-bas ...
GMPLS-based provisioning of Ethernet connections over WSON with Quality of Service Ph.D. Thesis
... link timer, which postpones the release of created FA TE link when there are no more upper-layer connections over such a link, rather than releasing it immediately. By doing so, we do reduce the signaling overhead due to consecutive triggering of FA TE links between the same pair of nodes. As a seco ...
... link timer, which postpones the release of created FA TE link when there are no more upper-layer connections over such a link, rather than releasing it immediately. By doing so, we do reduce the signaling overhead due to consecutive triggering of FA TE links between the same pair of nodes. As a seco ...
OpenFlow1.3 GUI Manual
... grey lines, as shown in the diagram below. In addition, the data plane can be formed by connecting OpenFlow switches to other network devices, such as other OpenFlow switches or hosts. Data plane connections are represented in the GUI as black lines (see below diagram). We call this structure OUTBAN ...
... grey lines, as shown in the diagram below. In addition, the data plane can be formed by connecting OpenFlow switches to other network devices, such as other OpenFlow switches or hosts. Data plane connections are represented in the GUI as black lines (see below diagram). We call this structure OUTBAN ...
ss7 structure - Home - KSU Faculty Member websites
... The communications network for communications equipment: Control and signaling information between switches Saad Haj Bakry ...
... The communications network for communications equipment: Control and signaling information between switches Saad Haj Bakry ...
Routing - La Salle University
... scalability arise. For a network to “scale” – One should be able to add nodes easily. – The network’s functionality should remain relatively constant when nodes are added. ...
... scalability arise. For a network to “scale” – One should be able to add nodes easily. – The network’s functionality should remain relatively constant when nodes are added. ...
Professional control led lighting
... OverledBUS node, it is a slave module of OverledBUS, this can be connected in the network as overledBUS driver,but not integrated in the fixture.This module have a cable lock and connectors for harness and holes for electrical housing or wall mounting. OverledBUS node can drive constant current led ...
... OverledBUS node, it is a slave module of OverledBUS, this can be connected in the network as overledBUS driver,but not integrated in the fixture.This module have a cable lock and connectors for harness and holes for electrical housing or wall mounting. OverledBUS node can drive constant current led ...
ElastiCon: An Elastic Distributed SDN Controller
... multi-threaded design [21, 2, 4, 8] in recent years. Despite the significant performance improvement over time, the single-controller systems still have limits on scalability and vulnerability. Some research papers have also explored the implementation of distributed controllers across multiple host ...
... multi-threaded design [21, 2, 4, 8] in recent years. Despite the significant performance improvement over time, the single-controller systems still have limits on scalability and vulnerability. Some research papers have also explored the implementation of distributed controllers across multiple host ...
On the Effectiveness of Traffic Analysis Against
... reveal variation in network and system operation parameters. These correlated patterns are used to link network peers which are part of an anonymous communication session. For example, previous work [9], [30] demonstrated how variation in anonymous traffic leads to variation in CPU temperature and, ...
... reveal variation in network and system operation parameters. These correlated patterns are used to link network peers which are part of an anonymous communication session. For example, previous work [9], [30] demonstrated how variation in anonymous traffic leads to variation in CPU temperature and, ...