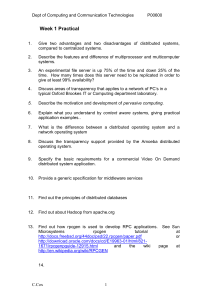
Intro. to Computer - web page for staff
... sometimes used to increase the speed of processing by making current programs and data available to the CPU at a rapid rate. The cache memory is employed in computer systems to compensate for the speed differential between main memory access time, with the result that processing speed is limited pri ...
... sometimes used to increase the speed of processing by making current programs and data available to the CPU at a rapid rate. The cache memory is employed in computer systems to compensate for the speed differential between main memory access time, with the result that processing speed is limited pri ...
Operating System
... operating-systems research and development. System development is done on the virtual machine, instead of on a physical machine and so does not disrupt normal system operation. The virtual machine concept is difficult to implement due to the effort required to provide an exact duplicate to the und ...
... operating-systems research and development. System development is done on the virtual machine, instead of on a physical machine and so does not disrupt normal system operation. The virtual machine concept is difficult to implement due to the effort required to provide an exact duplicate to the und ...
PPT - Duke Database Devils
... all of its memory, etc. •Performance isolation. The OS manages resources (“metal and glass”: computing power, memory, disk space, I/O throughput capacity, network capacity, etc.). Each instance needs the “right amount” of resources to run properly. The OS prevents apps from impacting the performance ...
... all of its memory, etc. •Performance isolation. The OS manages resources (“metal and glass”: computing power, memory, disk space, I/O throughput capacity, network capacity, etc.). Each instance needs the “right amount” of resources to run properly. The OS prevents apps from impacting the performance ...
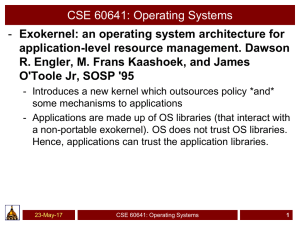
PPT - Surendar Chandra
... designed to be portable. Hence, they define interfaces (e.g. system calls). Abstractions add overhead and so the OS is general purpose but not optimized for a specific scenario – Data bases - need access to hard drive – Movie player – need access to display, DVD drive, CPU – Games – need access to C ...
... designed to be portable. Hence, they define interfaces (e.g. system calls). Abstractions add overhead and so the OS is general purpose but not optimized for a specific scenario – Data bases - need access to hard drive – Movie player – need access to display, DVD drive, CPU – Games – need access to C ...
Introduction to operating systems
... A consistent interface between the user and the operating system. ...
... A consistent interface between the user and the operating system. ...
Config OS - UNM Computer Science
... • Namespace semantics and management towards single system image and virtualization • Resource allocation for memory objects (static versus dynamic) • Intrinsic model of execution • What to do when the application flatlines – exceptions and ...
... • Namespace semantics and management towards single system image and virtualization • Resource allocation for memory objects (static versus dynamic) • Intrinsic model of execution • What to do when the application flatlines – exceptions and ...
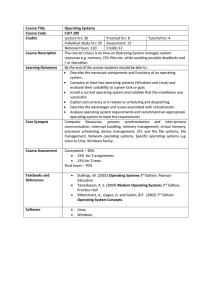
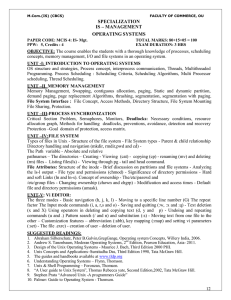
Course Title Operating Systems Course Code CUIT 109 Credits
... Individual Study hrs: 59 Assessment: 13 Notional Hours: 120 Credits 12 The course’s focus is on how an Operating System manages system resources e.g. memory, CPU files etc, while avoiding possible deadlocks and / or starvation. By the end of the course students should be able to : Describe the nec ...
... Individual Study hrs: 59 Assessment: 13 Notional Hours: 120 Credits 12 The course’s focus is on how an Operating System manages system resources e.g. memory, CPU files etc, while avoiding possible deadlocks and / or starvation. By the end of the course students should be able to : Describe the nec ...
1 - Erode Sengunthar Engineering College
... Instead of improvements in distributed computing , most systems do not offer general purpose distributed file systems .therefore , most clusters do not allow shared access to data on the disk. For this , distributed file systems , must provide access control and locking to the files to ensure no con ...
... Instead of improvements in distributed computing , most systems do not offer general purpose distributed file systems .therefore , most clusters do not allow shared access to data on the disk. For this , distributed file systems , must provide access control and locking to the files to ensure no con ...
Operating System
... • a collection of one or more threads and associated system resources • programmer has greater control over the modularity of the application and the timing of application related events ...
... • a collection of one or more threads and associated system resources • programmer has greater control over the modularity of the application and the timing of application related events ...
Operating Systems - inst.eecs.berkeley.edu
... • Abstractions and Primitives – Set of constructs and well‐defined interfaces to simplify application development: “all the code you didn’t write” in order to implement your application • Because hardware changes faster than applications! • Because some concepts are useful across applications ...
... • Abstractions and Primitives – Set of constructs and well‐defined interfaces to simplify application development: “all the code you didn’t write” in order to implement your application • Because hardware changes faster than applications! • Because some concepts are useful across applications ...
Chapter 3.1
... that is currently executing. • The actual contents of all programs are initially stored in persistent storage, such as a hard drive. • In order to be executed, a program must be loaded into random-access memory (RAM) and uniquely identified as a process. • In this way, multiple copies of the same pr ...
... that is currently executing. • The actual contents of all programs are initially stored in persistent storage, such as a hard drive. • In order to be executed, a program must be loaded into random-access memory (RAM) and uniquely identified as a process. • In this way, multiple copies of the same pr ...
Lecture 3
... System call causes a TRAP to switch from user to kernel mode and starts execution at interrupt vector location for TRAP instruction. Operating system looks at requested operation and any parameters passed by the application. Dispatches the correct system call handler through a table of pointers to s ...
... System call causes a TRAP to switch from user to kernel mode and starts execution at interrupt vector location for TRAP instruction. Operating system looks at requested operation and any parameters passed by the application. Dispatches the correct system call handler through a table of pointers to s ...
Operating systems
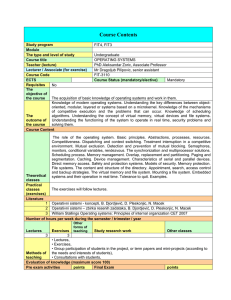
... The acquisition of basic knowledge of operating systems and work in them. Knowledge of modern operating systems. Understanding the key differences between objectoriented, modular, layered or systems based on a microkernel. Knowledge of the mechanisms of competitive execution and the problems that ca ...
... The acquisition of basic knowledge of operating systems and work in them. Knowledge of modern operating systems. Understanding the key differences between objectoriented, modular, layered or systems based on a microkernel. Knowledge of the mechanisms of competitive execution and the problems that ca ...
Advanced Operating Systems (CS 202) OS Evolution
... hierarchical file systems, devices as files, … ...
... hierarchical file systems, devices as files, … ...
Course number and name CSC 345 – Operating Systems Credits
... Brief description of the content of the course (catalog description) An introduction to operating systems concepts. Topics include processor management, storage management, device management, performance, security, and case studies of common operating systems. Prerequisites or co-requisites CSC 222 ...
... Brief description of the content of the course (catalog description) An introduction to operating systems concepts. Topics include processor management, storage management, device management, performance, security, and case studies of common operating systems. Prerequisites or co-requisites CSC 222 ...
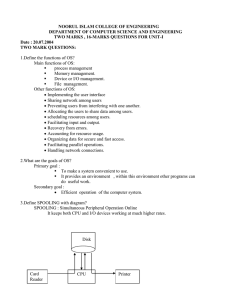
Functions of the operating systems
... 1. allows the user to organize their data on secondary storage into files & folders 2. also manages the use of main memory by splitting main memory into two parts (user area, system area). 3. Time sharing: operating system can allow more than one user to work on the same computer, and run more than ...
... 1. allows the user to organize their data on secondary storage into files & folders 2. also manages the use of main memory by splitting main memory into two parts (user area, system area). 3. Time sharing: operating system can allow more than one user to work on the same computer, and run more than ...
Benchmarked Performance and Introduction to
... source code. • Linker - tool that binds or links separate object files and completes any missing details. • This tool outputs a file in executable format for the native operating system. • That is, the file may be loaded into memory and executed. • Programs may be self contained (statically linked) ...
... source code. • Linker - tool that binds or links separate object files and completes any missing details. • This tool outputs a file in executable format for the native operating system. • That is, the file may be loaded into memory and executed. • Programs may be self contained (statically linked) ...
CSCI 3753 Operating Systems Spring 2005
... – assembler doesn’t generate absolute addresses, because • don’t know to what other object files you’ll be linked with • the binary executable could be loaded anywhere in RAM ...
... – assembler doesn’t generate absolute addresses, because • don’t know to what other object files you’ll be linked with • the binary executable could be loaded anywhere in RAM ...
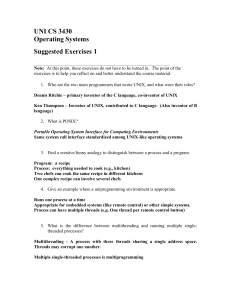
Answers
... Note: At this point, these exercises do not have to be turned in. The point of the exercises is to help you reflect on and better understand the course material. 1. Who are the two main programmers that wrote UNIX, and what were their roles? Dennis Ritchie – primary inventor of the C language, co-in ...
... Note: At this point, these exercises do not have to be turned in. The point of the exercises is to help you reflect on and better understand the course material. 1. Who are the two main programmers that wrote UNIX, and what were their roles? Dennis Ritchie – primary inventor of the C language, co-in ...
Library (computing)
In computer science, a library is a collection of non-volatile resources used by computer programs, often to develop software. These may include configuration data, documentation, help data, message templates, pre-written code and subroutines, classes, values or type specifications. In IBM's OS/360 and its successors they are referred to as partitioned data sets.In computer science, a library is a collection of implementations of behavior, written in terms of a language, that has a well-defined interface by which the behavior is invoked. This means that as long as a higher level program uses a library to make system calls, it does not need to be re-written to implement those system calls over and over again. In addition, the behavior is provided for reuse by multiple independent programs. A program invokes the library-provided behavior via a mechanism of the language. For example, in a simple imperative language such as C, the behavior in a library is invoked by using C's normal function-call. What distinguishes the call as being to a library, versus being to another function in the same program, is the way that the code is organized in the system. Library code is organized in such a way that it can be used by multiple programs that have no connection to each other, while code that is part of a program is organized to only be used within that one program. This distinction can gain a hierarchical notion when a program grows large, such as a multi-million-line program. In that case, there may be internal libraries that are reused by independent sub-portions of the large program. The distinguishing feature is that a library is organized for the purposes of being reused by independent programs or sub-programs, and the user only needs to know the interface, and not the internal details of the library.The value of a library is the reuse of the behavior. When a program invokes a library, it gains the behavior implemented inside that library without having to implement that behavior itself. Libraries encourage the sharing of code in a modular fashion, and ease the distribution of the code. The behavior implemented by a library can be connected to the invoking program at different program lifecycle phases. If the code of the library is accessed during the build of the invoking program, then the library is called a static library. An alternative is to build the executable of the invoking program and distribute that, independently from the library implementation. The library behavior is connected after the executable has been invoked to be executed, either as part of the process of starting the execution, or in the middle of execution. In this case the library is called a dynamic library. A dynamic library can be loaded and linked as part of preparing a program for execution, by the linker. Alternatively, in the middle of execution, an application may explicitly request that a module be loaded.Most compiled languages have a standard library although programmers can also create their own custom libraries. Most modern software systems provide libraries that implement the majority of system services. Such libraries have commoditized the services which a modern application requires. As such, most code used by modern applications is provided in these system libraries.