Slides About Systems - Duke Database Devils
... Heap: dynamic memory The “heap” is an ADT in a runtime library: the code to maintain the heap is a heap manager. It allocates a contiguous slab of virtual memory from the OS kernel, then “carves it up” as needed. It enables the programming language environment, to store dynamic objects. E.g., with ...
... Heap: dynamic memory The “heap” is an ADT in a runtime library: the code to maintain the heap is a heap manager. It allocates a contiguous slab of virtual memory from the OS kernel, then “carves it up” as needed. It enables the programming language environment, to store dynamic objects. E.g., with ...
Exercises
... are easy to modify. No two system installations are the same, so each installation may want to tune the operating system to suit its needs. With mechanism and policy separate, the policy may be changed at will while the mechanism stays unchanged. This arrangement provides a more flexible system. 2.2 ...
... are easy to modify. No two system installations are the same, so each installation may want to tune the operating system to suit its needs. With mechanism and policy separate, the policy may be changed at will while the mechanism stays unchanged. This arrangement provides a more flexible system. 2.2 ...
Operating systems
... In the early 1950s, a computer could execute only one program at a time. Each user had sole use of the computer for a limited period of time and would arrive at a scheduled time with program and data on punched paper cards or punched tape. The program would be loaded into the machine, and the machin ...
... In the early 1950s, a computer could execute only one program at a time. Each user had sole use of the computer for a limited period of time and would arrive at a scheduled time with program and data on punched paper cards or punched tape. The program would be loaded into the machine, and the machin ...
Introduction to Computer Science
... 3. Explain the client-server model on the Internet. In which layer of the TCP/IP protocol suite is the model implemented? (10%) In the client-server architecture, each application is made of two separate but related programs: a client program and a server program. The server program must be running ...
... 3. Explain the client-server model on the Internet. In which layer of the TCP/IP protocol suite is the model implemented? (10%) In the client-server architecture, each application is made of two separate but related programs: a client program and a server program. The server program must be running ...
Document
... Operating system kernel serves an intermediary between the application and hardware. ...
... Operating system kernel serves an intermediary between the application and hardware. ...
Document
... – access to metadata of resources (that can be used further for discovery semantics, or whatever) – a simple web interface to access the resources – event manager reporting on the access, etc. ...
... – access to metadata of resources (that can be used further for discovery semantics, or whatever) – a simple web interface to access the resources – event manager reporting on the access, etc. ...
Operating systems Architecture
... System calls are provided by the system and are executed in the system kernel. ...
... System calls are provided by the system and are executed in the system kernel. ...
Introduction - University of Pennsylvania
... O.S. issues -- network communication protocols, data encryption, security, reliability, consistency of distributed data Real-Time Systems – timing constraints, deadlines, QoS (quality of service) ...
... O.S. issues -- network communication protocols, data encryption, security, reliability, consistency of distributed data Real-Time Systems – timing constraints, deadlines, QoS (quality of service) ...
EECE 432– Operating Systems
... Students will work in teams to finish three projects. The first and second project will consist on modifying the kernel of an operating system to customize a specific behavior. The third project is to examine a case study or build a module from scratch where students get exposed and focus on one sp ...
... Students will work in teams to finish three projects. The first and second project will consist on modifying the kernel of an operating system to customize a specific behavior. The third project is to examine a case study or build a module from scratch where students get exposed and focus on one sp ...
Basic Development on UNIX
... • Even simple programs are not self contained – You can call routines like “sin,” “printf”, or “write;” but you don’t have to include code for these functions in your program ...
... • Even simple programs are not self contained – You can call routines like “sin,” “printf”, or “write;” but you don’t have to include code for these functions in your program ...
7.3.3. Computer System Structures
... The Android runtime environment includes a core set of libraries as well as the Dalvik virtual machine. Google has designed a separate Android API for Java development. The Java class files are first compiled to Java bytecode and then translated into an executable file that runs on the Dalvik ...
... The Android runtime environment includes a core set of libraries as well as the Dalvik virtual machine. Google has designed a separate Android API for Java development. The Java class files are first compiled to Java bytecode and then translated into an executable file that runs on the Dalvik ...
99_Introduction
... The device that performs all calculations and data manipulation in a computer ...
... The device that performs all calculations and data manipulation in a computer ...
Homework: OS Organization
... Submit: In lab 4 you completed building the core of an exokernel-based operating system. In class you studied xv6, a monolithic operating systems. Both are intend to support the UNIX API, but their internal organizations are different. A good example is the virtual memory implementation: JOS impleme ...
... Submit: In lab 4 you completed building the core of an exokernel-based operating system. In class you studied xv6, a monolithic operating systems. Both are intend to support the UNIX API, but their internal organizations are different. A good example is the virtual memory implementation: JOS impleme ...
Part IV: Longer Answer: Use your knowledge of operating systems to
... installation and configuration of device drivers after a hardware device has been installed. 4. _______________ is a multi-user time-sharing operating system; most versions are based on AT&T System 5 and Berkeley Software Distribution 5. _______________ is a situation where one or more processes is ...
... installation and configuration of device drivers after a hardware device has been installed. 4. _______________ is a multi-user time-sharing operating system; most versions are based on AT&T System 5 and Berkeley Software Distribution 5. _______________ is a situation where one or more processes is ...
Slides. - Department of Computer Science and Information Systems
... 4. Memory management 5. Input/output 6. File systems 7. Multimedia operating systems 8. Multiple processor systems 9. Security UNIX and Windows are to be used as running case studies. ...
... 4. Memory management 5. Input/output 6. File systems 7. Multimedia operating systems 8. Multiple processor systems 9. Security UNIX and Windows are to be used as running case studies. ...
batch systems
... Yet More Issues in OS • scale and growth - what happens as demands or resources increase? • persistence - how to make data last longer than programs • compatibility - can we ever do anything new? • distribution - can the components of the system be geographically separated? • accounting - who pays ...
... Yet More Issues in OS • scale and growth - what happens as demands or resources increase? • persistence - how to make data last longer than programs • compatibility - can we ever do anything new? • distribution - can the components of the system be geographically separated? • accounting - who pays ...
Slide 1
... Loading/Executing Object Programs • Loader invoked when user types command or clicks on icon in graphical user interface • User input identifies object file on disk • Object file has information on starting location in memory and length of program • Loader transfers object program from disk to memo ...
... Loading/Executing Object Programs • Loader invoked when user types command or clicks on icon in graphical user interface • User input identifies object file on disk • Object file has information on starting location in memory and length of program • Loader transfers object program from disk to memo ...
Operating System
... When Operating Systems didn’t Exist • technological capabilities • Individual Programs • One person used the computer at a time • “Job Scheduling” • Libraries 1st procedure ...
... When Operating Systems didn’t Exist • technological capabilities • Individual Programs • One person used the computer at a time • “Job Scheduling” • Libraries 1st procedure ...
Document
... for program loading and execution. Communications – provide mechanism for creating virtual connections among processes, users, and different computer systems which allows message passing, browse web pages, send e-mail messages, log-in remotely, transfer files from one machine to another. Application ...
... for program loading and execution. Communications – provide mechanism for creating virtual connections among processes, users, and different computer systems which allows message passing, browse web pages, send e-mail messages, log-in remotely, transfer files from one machine to another. Application ...
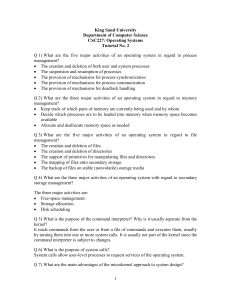
tutorial-02-with
... only limited sections of the system rather than touching all sections of the operating system. Information is kept only where it is needed and is accessible only within a defined and restricted area, so any bugs affecting that data must be limited to a specific module or layer. Q 11) List five servi ...
... only limited sections of the system rather than touching all sections of the operating system. Information is kept only where it is needed and is accessible only within a defined and restricted area, so any bugs affecting that data must be limited to a specific module or layer. Q 11) List five servi ...
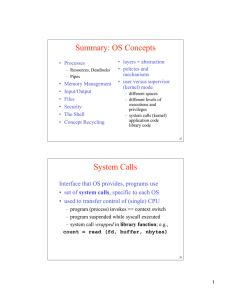
Summary: OS Concepts System Calls
... /* display prompt */ read_command (command, parameters) /* input from terminal */ if (fork() != 0) { /* fork off child process */ /* Parent code */ waitpid( -1, &status, 0);/* wait for child to exit */ } else { /* Child code */ execve (command, parameters, 0);/* execute command */ ...
... /* display prompt */ read_command (command, parameters) /* input from terminal */ if (fork() != 0) { /* fork off child process */ /* Parent code */ waitpid( -1, &status, 0);/* wait for child to exit */ } else { /* Child code */ execve (command, parameters, 0);/* execute command */ ...
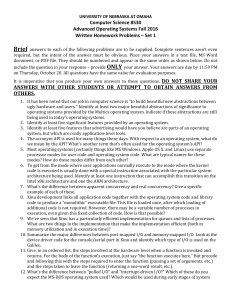
Computer Science 8530 Advanced Operating Systems Fall 2016
... code is executed is usually done with a special instruction associated with the particular system architecture being used. Identify at least one instruction that can accomplish this transition on the Intel x86 architecture and one the ARM architecture. 7. What’s the difference between apparent co ...
... code is executed is usually done with a special instruction associated with the particular system architecture being used. Identify at least one instruction that can accomplish this transition on the Intel x86 architecture and one the ARM architecture. 7. What’s the difference between apparent co ...
powerpoint
... Yet More Issues in OS • scale and growth - what happens as demands or resources increase? • persistence - how to make data last longer than programs • compatibility - can we ever do anything new? • distribution - can the components of the system be geographically separated? • accounting - who pays ...
... Yet More Issues in OS • scale and growth - what happens as demands or resources increase? • persistence - how to make data last longer than programs • compatibility - can we ever do anything new? • distribution - can the components of the system be geographically separated? • accounting - who pays ...
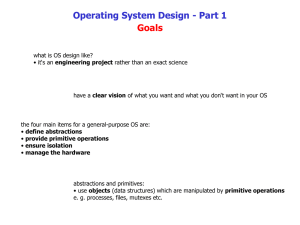
Operating System Design
... what is OS design like? • it‘s an engineering project rather than an exact science ...
... what is OS design like? • it‘s an engineering project rather than an exact science ...
CompOrgEclipseIntro
... Two levels Operating System and Application Operating system manages computer's resources; typically runs as soon as computer is turned on. Typical responsibilities: • Process management Determines when, how programs will run on • Memory management • I/O, window system • Security ...
... Two levels Operating System and Application Operating system manages computer's resources; typically runs as soon as computer is turned on. Typical responsibilities: • Process management Determines when, how programs will run on • Memory management • I/O, window system • Security ...
Library (computing)
In computer science, a library is a collection of non-volatile resources used by computer programs, often to develop software. These may include configuration data, documentation, help data, message templates, pre-written code and subroutines, classes, values or type specifications. In IBM's OS/360 and its successors they are referred to as partitioned data sets.In computer science, a library is a collection of implementations of behavior, written in terms of a language, that has a well-defined interface by which the behavior is invoked. This means that as long as a higher level program uses a library to make system calls, it does not need to be re-written to implement those system calls over and over again. In addition, the behavior is provided for reuse by multiple independent programs. A program invokes the library-provided behavior via a mechanism of the language. For example, in a simple imperative language such as C, the behavior in a library is invoked by using C's normal function-call. What distinguishes the call as being to a library, versus being to another function in the same program, is the way that the code is organized in the system. Library code is organized in such a way that it can be used by multiple programs that have no connection to each other, while code that is part of a program is organized to only be used within that one program. This distinction can gain a hierarchical notion when a program grows large, such as a multi-million-line program. In that case, there may be internal libraries that are reused by independent sub-portions of the large program. The distinguishing feature is that a library is organized for the purposes of being reused by independent programs or sub-programs, and the user only needs to know the interface, and not the internal details of the library.The value of a library is the reuse of the behavior. When a program invokes a library, it gains the behavior implemented inside that library without having to implement that behavior itself. Libraries encourage the sharing of code in a modular fashion, and ease the distribution of the code. The behavior implemented by a library can be connected to the invoking program at different program lifecycle phases. If the code of the library is accessed during the build of the invoking program, then the library is called a static library. An alternative is to build the executable of the invoking program and distribute that, independently from the library implementation. The library behavior is connected after the executable has been invoked to be executed, either as part of the process of starting the execution, or in the middle of execution. In this case the library is called a dynamic library. A dynamic library can be loaded and linked as part of preparing a program for execution, by the linker. Alternatively, in the middle of execution, an application may explicitly request that a module be loaded.Most compiled languages have a standard library although programmers can also create their own custom libraries. Most modern software systems provide libraries that implement the majority of system services. Such libraries have commoditized the services which a modern application requires. As such, most code used by modern applications is provided in these system libraries.