Programming 101
... It allows you the freedom to do other things if you simply your life by having computers do the work faster It’s fun It’s profitable If your competitors are doing programming to achieve greater efficiencies and you and your company are not – they will beat you and your company. ...
... It allows you the freedom to do other things if you simply your life by having computers do the work faster It’s fun It’s profitable If your competitors are doing programming to achieve greater efficiencies and you and your company are not – they will beat you and your company. ...
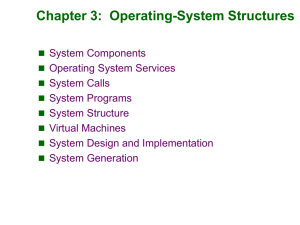
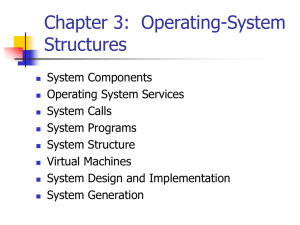
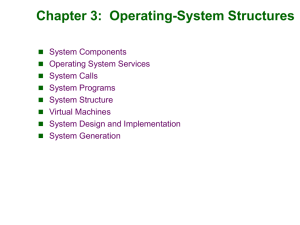
Module 3: Operating-System Structures
... • Protection refers to a mechanism for controlling access by programs, processes, or users to both system and user resources. • The protection mechanism must: – distinguish between authorized and unauthorized usage. – specify the controls to be imposed. – provide a means of enforcement. ...
... • Protection refers to a mechanism for controlling access by programs, processes, or users to both system and user resources. • The protection mechanism must: – distinguish between authorized and unauthorized usage. – specify the controls to be imposed. – provide a means of enforcement. ...
Introduction
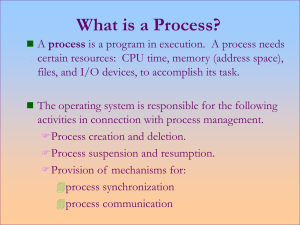
... that is currently executing. • The actual contents of all programs are initially stored in persistent storage, such as a hard drive. • In order to be executed, a program must be loaded into random-access memory (RAM) and uniquely identified as a process. • In this way, multiple copies of the same pr ...
... that is currently executing. • The actual contents of all programs are initially stored in persistent storage, such as a hard drive. • In order to be executed, a program must be loaded into random-access memory (RAM) and uniquely identified as a process. • In this way, multiple copies of the same pr ...
here
... 5. Enumerate, explain, and differentiate between different mechanisms of interprocess communication and synchronisation 6. Analyse the architecture of a computer system and understand the significance of different architectural features and their affect on system administration. 7. Perform basic and ...
... 5. Enumerate, explain, and differentiate between different mechanisms of interprocess communication and synchronisation 6. Analyse the architecture of a computer system and understand the significance of different architectural features and their affect on system administration. 7. Perform basic and ...
Abstract View of System Components
... OS Airlines – Windows xx • Planes are remarkably similar to ones used by Windows 3.1 OS • Environment is even nicer, but the plane takes 5 times as long to get started – or to stop • Plane flies well enough, smooth and quite fast • Then the plane blows up for no explainable reason ...
... OS Airlines – Windows xx • Planes are remarkably similar to ones used by Windows 3.1 OS • Environment is even nicer, but the plane takes 5 times as long to get started – or to stop • Plane flies well enough, smooth and quite fast • Then the plane blows up for no explainable reason ...
Six Different Phase for Executing C program
... groups of programmers working on a particular project. • A linker links the object code with the code for the missing functions to produce an executable image (with no missing pieces). ...
... groups of programmers working on a particular project. • A linker links the object code with the code for the missing functions to produce an executable image (with no missing pieces). ...
Lecture 4: September 11 4.1 Processes 4.2 Memory and Secondary
... data processing and preparation which does not need to be done in privileged mode. Ideally, this reduces the coupling between the operating system and the application, and increases portability. On Unix-based and POSIX-based systems, popular system calls are open, read, write, close, wait, exec, for ...
... data processing and preparation which does not need to be done in privileged mode. Ideally, this reduces the coupling between the operating system and the application, and increases portability. On Unix-based and POSIX-based systems, popular system calls are open, read, write, close, wait, exec, for ...
doc, 33kb
... depend on these inputs. We have implemented a PLAN-P interpreter which is written in C to be portable on all routers. However, our interpreter is specialised with respect to a PLAN-P program in order to eliminate the interpretive overhead. Because the program is not available until run time, a run-t ...
... depend on these inputs. We have implemented a PLAN-P interpreter which is written in C to be portable on all routers. However, our interpreter is specialised with respect to a PLAN-P program in order to eliminate the interpretive overhead. Because the program is not available until run time, a run-t ...
Operating System Objectives and Functions
... 4. Characteristics of Modern Operating Systems Microkernel architecture-assigns only a few essential functions to the kernel, including address spaces, interprocess communication, and basic scheduling. Multithreading- the process is divided into threads that can run simultaneously Thread- dispatcha ...
... 4. Characteristics of Modern Operating Systems Microkernel architecture-assigns only a few essential functions to the kernel, including address spaces, interprocess communication, and basic scheduling. Multithreading- the process is divided into threads that can run simultaneously Thread- dispatcha ...
Java Concepts Ch1
... fetch data from storage and input/output devices send data back to devices ...
... fetch data from storage and input/output devices send data back to devices ...
Operating Systems - Villanova Computer Science
... Installing a new device: • A physical connection must be made to the peripheral. • The proper software drivers must be added to the operating system – Device Driver: A program that will allow communication between the operating system and another part of the computer, usually a peripheral device lik ...
... Installing a new device: • A physical connection must be made to the peripheral. • The proper software drivers must be added to the operating system – Device Driver: A program that will allow communication between the operating system and another part of the computer, usually a peripheral device lik ...
Creating Your First Computer Program in Java ()
... - estimated 1.5 billion Internet users (~ 5 x U.S. Population) - 14.3 billion searches by Americans in May 09 - Microsoft: the world’s largest software company - company worth $36 billion (2008) - over 400 million copies of Windows XP sold - the largest social networking site - company worth $3.75 – ...
... - estimated 1.5 billion Internet users (~ 5 x U.S. Population) - 14.3 billion searches by Americans in May 09 - Microsoft: the world’s largest software company - company worth $36 billion (2008) - over 400 million copies of Windows XP sold - the largest social networking site - company worth $3.75 – ...
ppt
... • Programmer time wasted! “Sigh. In the good old days….” – Time-sharing – Multics (sorta) – New problems ...
... • Programmer time wasted! “Sigh. In the good old days….” – Time-sharing – Multics (sorta) – New problems ...
Principles of Program Design
... granted such as “substituting equals for equals”. If a method uses mutation, it can potentially modify any accessible object. Hence, it is difficult to determine if calling such a method can break a given program invariant. In the absence of mutation, objects can safely be shared (rather than copied ...
... granted such as “substituting equals for equals”. If a method uses mutation, it can potentially modify any accessible object. Hence, it is difficult to determine if calling such a method can break a given program invariant. In the absence of mutation, objects can safely be shared (rather than copied ...
Module 3: Operating
... programs permanently, the computer system must provide secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk ma ...
... programs permanently, the computer system must provide secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk ma ...
Module 3: Operating-System Structures
... permanently, the computer system must provide secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: ...
... permanently, the computer system must provide secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: ...
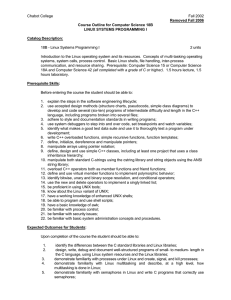
Linux Systems Programming I
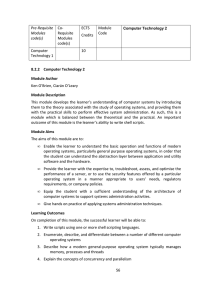
... Before entering the course the student should be able to: 1. explain the steps in the software engineering lifecycle; 2. use accepted design methods (structure charts, pseudocode, simple class diagrams) to develop and code several (six-ten) programs of intermediate difficulty and length in the C++ l ...
... Before entering the course the student should be able to: 1. explain the steps in the software engineering lifecycle; 2. use accepted design methods (structure charts, pseudocode, simple class diagrams) to develop and code several (six-ten) programs of intermediate difficulty and length in the C++ l ...
Course Syllabus
... This course will cover the basic principles of operating system design and implementation. Concurrent processes, inter-process communication, job and process scheduling; deadlock. Issues in memory management (virtual memory, segmentation, and paging) and auxiliary storage management (file systems, d ...
... This course will cover the basic principles of operating system design and implementation. Concurrent processes, inter-process communication, job and process scheduling; deadlock. Issues in memory management (virtual memory, segmentation, and paging) and auxiliary storage management (file systems, d ...
Operating-System Structures - Stanford Computer Graphics
... Secondary-Storage Management Since main memory (primary storage) is volatile and too ...
... Secondary-Storage Management Since main memory (primary storage) is volatile and too ...
ppt
... • Programmer time wasted! “Sigh. In the good old days….” – Time-sharing – Multics (sorta) – New problems ...
... • Programmer time wasted! “Sigh. In the good old days….” – Time-sharing – Multics (sorta) – New problems ...
Lecture 3 - The College of New Jersey
... memory and to run it. I/O operations – since user programs cannot execute I/O operations directly, the operating system must provide some means to perform I/O. File-system manipulation – program capability to read, write, create, and delete files. Communications – exchange of information between pro ...
... memory and to run it. I/O operations – since user programs cannot execute I/O operations directly, the operating system must provide some means to perform I/O. File-system manipulation – program capability to read, write, create, and delete files. Communications – exchange of information between pro ...
C | 4. Evolution of Programming Languages
... mistakes. Second-generation programming languages are a way of describing Assembly code which uses mnemonic codes like ADD,SUB,MUL,Div,MOV etc. •By using codes resembling English programming becomes much easier. The use of these mnemonic codes such as LDA for load and STA for store means the code is ...
... mistakes. Second-generation programming languages are a way of describing Assembly code which uses mnemonic codes like ADD,SUB,MUL,Div,MOV etc. •By using codes resembling English programming becomes much easier. The use of these mnemonic codes such as LDA for load and STA for store means the code is ...
Operating Systems
... example of real time processing. • Real time systems are used for tasks such as navigation, in which the computer must react to a steady flow of new information ...
... example of real time processing. • Real time systems are used for tasks such as navigation, in which the computer must react to a steady flow of new information ...
ppt
... • Programmer time wasted! “Sigh. In the good old days….” – Time-sharing – Multics (sorta) – New problems ...
... • Programmer time wasted! “Sigh. In the good old days….” – Time-sharing – Multics (sorta) – New problems ...
Library (computing)
In computer science, a library is a collection of non-volatile resources used by computer programs, often to develop software. These may include configuration data, documentation, help data, message templates, pre-written code and subroutines, classes, values or type specifications. In IBM's OS/360 and its successors they are referred to as partitioned data sets.In computer science, a library is a collection of implementations of behavior, written in terms of a language, that has a well-defined interface by which the behavior is invoked. This means that as long as a higher level program uses a library to make system calls, it does not need to be re-written to implement those system calls over and over again. In addition, the behavior is provided for reuse by multiple independent programs. A program invokes the library-provided behavior via a mechanism of the language. For example, in a simple imperative language such as C, the behavior in a library is invoked by using C's normal function-call. What distinguishes the call as being to a library, versus being to another function in the same program, is the way that the code is organized in the system. Library code is organized in such a way that it can be used by multiple programs that have no connection to each other, while code that is part of a program is organized to only be used within that one program. This distinction can gain a hierarchical notion when a program grows large, such as a multi-million-line program. In that case, there may be internal libraries that are reused by independent sub-portions of the large program. The distinguishing feature is that a library is organized for the purposes of being reused by independent programs or sub-programs, and the user only needs to know the interface, and not the internal details of the library.The value of a library is the reuse of the behavior. When a program invokes a library, it gains the behavior implemented inside that library without having to implement that behavior itself. Libraries encourage the sharing of code in a modular fashion, and ease the distribution of the code. The behavior implemented by a library can be connected to the invoking program at different program lifecycle phases. If the code of the library is accessed during the build of the invoking program, then the library is called a static library. An alternative is to build the executable of the invoking program and distribute that, independently from the library implementation. The library behavior is connected after the executable has been invoked to be executed, either as part of the process of starting the execution, or in the middle of execution. In this case the library is called a dynamic library. A dynamic library can be loaded and linked as part of preparing a program for execution, by the linker. Alternatively, in the middle of execution, an application may explicitly request that a module be loaded.Most compiled languages have a standard library although programmers can also create their own custom libraries. Most modern software systems provide libraries that implement the majority of system services. Such libraries have commoditized the services which a modern application requires. As such, most code used by modern applications is provided in these system libraries.