Introduction to System Maintenance
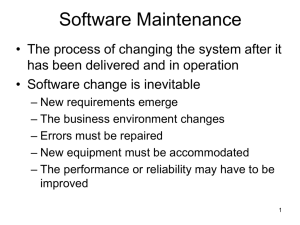
... • Maintenance to adapt software to a different operating environment (Adaptive) – Changing a system so that it operates in a different environment (computer, OS, etc.) from its initial implementation ...
... • Maintenance to adapt software to a different operating environment (Adaptive) – Changing a system so that it operates in a different environment (computer, OS, etc.) from its initial implementation ...
VMS-Spr-2001-sect-1-group
... Process State Structure • The process state structure for VMS involves a process priority queue where processes are ranked in priority from 0 to 31 • 16-31 is a high priority real-time process • 0-15 is a normal process • Normal processes are moved up in the queue if they are critical to the operat ...
... Process State Structure • The process state structure for VMS involves a process priority queue where processes are ranked in priority from 0 to 31 • 16-31 is a high priority real-time process • 0-15 is a normal process • Normal processes are moved up in the queue if they are critical to the operat ...
Sai Uday Kiran Ravi`s presentation on Application Security on
... Sometimes it is possible to securely authenticate a local connection simply by verifying that both endpoints are in the same secure compartment. ...
... Sometimes it is possible to securely authenticate a local connection simply by verifying that both endpoints are in the same secure compartment. ...
PPT
... Enforce “fair” allocation of hardware resources among applications Policies that say what is “fair” and mechanisms to enforce it ...
... Enforce “fair” allocation of hardware resources among applications Policies that say what is “fair” and mechanisms to enforce it ...
Charles Haiber`s presentation on Exokernels
... applications to run on the system, tend to have a very high cost in system resources • Hurts the performance of applications • Hides information from applications • Limits the functionality of applications ...
... applications to run on the system, tend to have a very high cost in system resources • Hurts the performance of applications • Hides information from applications • Limits the functionality of applications ...
Lab 1: C Primer - CS-People by full name
... ➢ To submit your code run the steps below, a status message will be returned upon success: ○ mkdir lab0_test ○ cp hello.c lab0_test ○ gsubmit cs201 -cp lab0_test More examples Look over all 3 codes below, read the comments, compile and run them and try to understand how they work. There are some ‘O ...
... ➢ To submit your code run the steps below, a status message will be returned upon success: ○ mkdir lab0_test ○ cp hello.c lab0_test ○ gsubmit cs201 -cp lab0_test More examples Look over all 3 codes below, read the comments, compile and run them and try to understand how they work. There are some ‘O ...
How to Write, Compile, and Run a Simple Java Program
... If the disk portion of the path (the drive letter) that is shown in the command prompt window is not the same as the drive where the code file is saved then change the disk by typing the correct letter, a colon, and pressing the ‘Enter’ key. For example, suppose that I saved my code file on the H: d ...
... If the disk portion of the path (the drive letter) that is shown in the command prompt window is not the same as the drive where the code file is saved then change the disk by typing the correct letter, a colon, and pressing the ‘Enter’ key. For example, suppose that I saved my code file on the H: d ...
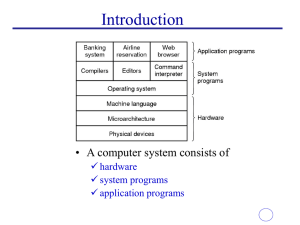
os-1
... Performs the interface task with the hardware (file operations, memory paging, etc.) which should have been done by the user if the OS did not exist High-level interface (GUI, command line a.k.a. CUI) The O/S’s capability for multiuser and multitasking utilize the hardware efficiently Makes visible ...
... Performs the interface task with the hardware (file operations, memory paging, etc.) which should have been done by the user if the OS did not exist High-level interface (GUI, command line a.k.a. CUI) The O/S’s capability for multiuser and multitasking utilize the hardware efficiently Makes visible ...
document
... designed for Intel’s new 16 bit microprocessor the 8086. While similar to CP/M it added features such as: – memory and timer management, – interrupt support, and a more sophisticated file system including a FAT table. – With more available memory, more commands could be built in to the command line ...
... designed for Intel’s new 16 bit microprocessor the 8086. While similar to CP/M it added features such as: – memory and timer management, – interrupt support, and a more sophisticated file system including a FAT table. – With more available memory, more commands could be built in to the command line ...
History of Operating Systems
... Jobs running in a modern OS can start processes that run in the memory of the OS, using drivers or other functions available through system calls ...
... Jobs running in a modern OS can start processes that run in the memory of the OS, using drivers or other functions available through system calls ...
Lecture Overview Operating System Components
... possible to separate these two functions • A virtual machine provides multiprogramming only by providing an exact virtual copies of the bare hardware • The operating system creates the illusion of multiple processes, each executing on its own processor with its own (virtual) memory • Each virtual ma ...
... possible to separate these two functions • A virtual machine provides multiprogramming only by providing an exact virtual copies of the bare hardware • The operating system creates the illusion of multiple processes, each executing on its own processor with its own (virtual) memory • Each virtual ma ...
operating system
... following activities in connections with memory management: – Keep track of which parts of memory are currently being used and by whom. – Decide which processes to load when memory space becomes available. – Allocate and de-allocate memory space as needed. ...
... following activities in connections with memory management: – Keep track of which parts of memory are currently being used and by whom. – Decide which processes to load when memory space becomes available. – Allocate and de-allocate memory space as needed. ...
OS Components and Structure
... process that handles interpretation of user input commands from keyboard (or script files) on some systems, command interpreter is a standard part of the OS on others, it’s simply a non-privileged process that interfaces to the user, permitting replacement of interpreter with others on others, there ...
... process that handles interpretation of user input commands from keyboard (or script files) on some systems, command interpreter is a standard part of the OS on others, it’s simply a non-privileged process that interfaces to the user, permitting replacement of interpreter with others on others, there ...
OS Services System calls and their types
... Often, more information is required than simply identity of desired system call – Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS – Simplest: pass the parameters in registers • In some cases, may be more parameters than regis ...
... Often, more information is required than simply identity of desired system call – Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS – Simplest: pass the parameters in registers • In some cases, may be more parameters than regis ...
System
... memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code. Accounting – To keep track of which users use how much and what kinds of computer resources ( billing) Protection and security – Concurrent processes should not in ...
... memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code. Accounting – To keep track of which users use how much and what kinds of computer resources ( billing) Protection and security – Concurrent processes should not in ...
Traditional UNIX kernels
... UNIX was taken to University of California Berkley leading to the foundation of the Berkeley Standard Distribution UNIX then opened up the computer industry to many other UNIX type operating systems and more To date, Apple MAC OS X is the most widely used desktop version of UNIX ...
... UNIX was taken to University of California Berkley leading to the foundation of the Berkeley Standard Distribution UNIX then opened up the computer industry to many other UNIX type operating systems and more To date, Apple MAC OS X is the most widely used desktop version of UNIX ...
Object Oriented Programming
... If you compile and there are errors, Java will not create a new .class file So if you click on execute after you have errors, Java might run an older version of your file ...
... If you compile and there are errors, Java will not create a new .class file So if you click on execute after you have errors, Java might run an older version of your file ...
Chapter 2 Operating System Overview
... • Process isolation • Automatic allocation and management • Protection and access control ...
... • Process isolation • Automatic allocation and management • Protection and access control ...
Executable code
... are powerful computers or processes dedicated to managing disk drives (file servers), printers (print servers), or network traffic (network servers ). Clients are PCs or workstations on which users run applications. Clients rely on servers for resources, such as files, devices, and even processing p ...
... are powerful computers or processes dedicated to managing disk drives (file servers), printers (print servers), or network traffic (network servers ). Clients are PCs or workstations on which users run applications. Clients rely on servers for resources, such as files, devices, and even processing p ...
Chapter 3- Flow Control
... – To run the program, we then give the byte-code to the Java byte-code interpreter to run the code. – This allows us to run our program on any OS that a Java byte-code interpreter has been created for (currently Windows, Linux, and Solaris) without having to recompile. ...
... – To run the program, we then give the byte-code to the Java byte-code interpreter to run the code. – This allows us to run our program on any OS that a Java byte-code interpreter has been created for (currently Windows, Linux, and Solaris) without having to recompile. ...
Lecture 1: Operating System Services What is an Operating System?
... Interrupt handling: Operating systems are event driven programs. If there are no programs to execute, no I/O devices to service, and no user to respond to, an O.S. will sit quietly, waiting for something to happen. Events are almost always signaled by the occurrence of an interrupt or trap. When an ...
... Interrupt handling: Operating systems are event driven programs. If there are no programs to execute, no I/O devices to service, and no user to respond to, an O.S. will sit quietly, waiting for something to happen. Events are almost always signaled by the occurrence of an interrupt or trap. When an ...
2.01 - Fordham University
... Some of them are simply user interfaces to system calls; others are considerably more complex File management - Create, delete, copy, rename, print, dump, list, and generally manipulate files and directories Status information Some ask the system for info - date, time, amount of available memory ...
... Some of them are simply user interfaces to system calls; others are considerably more complex File management - Create, delete, copy, rename, print, dump, list, and generally manipulate files and directories Status information Some ask the system for info - date, time, amount of available memory ...
Underlying computer system = hardware + software
... Everything is an object. Objects perform computations by making requests of each other through the passing of messages. Every object has its own memory, which consists of other objects. Every object is an instance of a class. A class groups similar objects. The class is the repository for behavior a ...
... Everything is an object. Objects perform computations by making requests of each other through the passing of messages. Every object has its own memory, which consists of other objects. Every object is an instance of a class. A class groups similar objects. The class is the repository for behavior a ...
Library (computing)
In computer science, a library is a collection of non-volatile resources used by computer programs, often to develop software. These may include configuration data, documentation, help data, message templates, pre-written code and subroutines, classes, values or type specifications. In IBM's OS/360 and its successors they are referred to as partitioned data sets.In computer science, a library is a collection of implementations of behavior, written in terms of a language, that has a well-defined interface by which the behavior is invoked. This means that as long as a higher level program uses a library to make system calls, it does not need to be re-written to implement those system calls over and over again. In addition, the behavior is provided for reuse by multiple independent programs. A program invokes the library-provided behavior via a mechanism of the language. For example, in a simple imperative language such as C, the behavior in a library is invoked by using C's normal function-call. What distinguishes the call as being to a library, versus being to another function in the same program, is the way that the code is organized in the system. Library code is organized in such a way that it can be used by multiple programs that have no connection to each other, while code that is part of a program is organized to only be used within that one program. This distinction can gain a hierarchical notion when a program grows large, such as a multi-million-line program. In that case, there may be internal libraries that are reused by independent sub-portions of the large program. The distinguishing feature is that a library is organized for the purposes of being reused by independent programs or sub-programs, and the user only needs to know the interface, and not the internal details of the library.The value of a library is the reuse of the behavior. When a program invokes a library, it gains the behavior implemented inside that library without having to implement that behavior itself. Libraries encourage the sharing of code in a modular fashion, and ease the distribution of the code. The behavior implemented by a library can be connected to the invoking program at different program lifecycle phases. If the code of the library is accessed during the build of the invoking program, then the library is called a static library. An alternative is to build the executable of the invoking program and distribute that, independently from the library implementation. The library behavior is connected after the executable has been invoked to be executed, either as part of the process of starting the execution, or in the middle of execution. In this case the library is called a dynamic library. A dynamic library can be loaded and linked as part of preparing a program for execution, by the linker. Alternatively, in the middle of execution, an application may explicitly request that a module be loaded.Most compiled languages have a standard library although programmers can also create their own custom libraries. Most modern software systems provide libraries that implement the majority of system services. Such libraries have commoditized the services which a modern application requires. As such, most code used by modern applications is provided in these system libraries.