Protection Mechanisms
... network are routed into—and then out of—a routing firewall to the separate network segment known as the DMZ – Connections into the trusted internal network are allowed only from the DMZ bastion host servers Management of Information Security ...
... network are routed into—and then out of—a routing firewall to the separate network segment known as the DMZ – Connections into the trusted internal network are allowed only from the DMZ bastion host servers Management of Information Security ...
Jensen3
... • In Sec. 1 Par. 7, “Traitor tracing has unique properties that makes it simpler than fingerprinting for detection of copyright violators.” – Isn’t Traitor Tracing accomplished by fingerprinting? ...
... • In Sec. 1 Par. 7, “Traitor tracing has unique properties that makes it simpler than fingerprinting for detection of copyright violators.” – Isn’t Traitor Tracing accomplished by fingerprinting? ...
CATAPAN Global Brochure
... The CATAPAN Global Key Management System (KMS) is a unique off-the-shelf solution for full sovereign key generation and management. The KMS allows customers to control their own cryptographic keys for the CATAPAN Global devices. Full control of this process guarantees the sovereign capability of the ...
... The CATAPAN Global Key Management System (KMS) is a unique off-the-shelf solution for full sovereign key generation and management. The KMS allows customers to control their own cryptographic keys for the CATAPAN Global devices. Full control of this process guarantees the sovereign capability of the ...
pdf
... master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by using the Guillou-Quisquater (GQ) signature scheme (this was the scheme from Hom ...
... master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by using the Guillou-Quisquater (GQ) signature scheme (this was the scheme from Hom ...
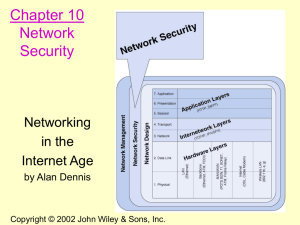
CHAPTER 1 Networking Concepts
... A. Conventional Encryption Also referred to as symmetry encryption or single-key encryption A form of cryptosystem in which encryption and decryption are performed using the same key This encryption scheme has five ingredients Plaintext: Readable message or data Encryption Algorithm: Performs ...
... A. Conventional Encryption Also referred to as symmetry encryption or single-key encryption A form of cryptosystem in which encryption and decryption are performed using the same key This encryption scheme has five ingredients Plaintext: Readable message or data Encryption Algorithm: Performs ...
COS 338_day17
... Each added character increases the brute force search time by a factor of up to 75 ...
... Each added character increases the brute force search time by a factor of up to 75 ...
Important Concepts.
... Intended to counter security attacks. Using one or more security mechanisms. Often replicates functions normally associated with physical documents which, for example, have signatures, dates; need protection ...
... Intended to counter security attacks. Using one or more security mechanisms. Often replicates functions normally associated with physical documents which, for example, have signatures, dates; need protection ...
Hidden Markov Model Cryptanalysis
... Introduce random computations Example: randomized projective coordinates in Elliptic Curve computations Projective coordinates (X,Y,Z) of P = (x,y) are given by: ...
... Introduce random computations Example: randomized projective coordinates in Elliptic Curve computations Projective coordinates (X,Y,Z) of P = (x,y) are given by: ...
Security - The University of Texas at Dallas
... • You hear them murmur, "Let's see you use that VISA card now, Professor "I-Don't-Give-A's-To Any MBA Candidate!" ...
... • You hear them murmur, "Let's see you use that VISA card now, Professor "I-Don't-Give-A's-To Any MBA Candidate!" ...
CSCI6268L37
... Foundations of Network and Computer Security John Black Lecture #36 Dec 11th 2009 ...
... Foundations of Network and Computer Security John Black Lecture #36 Dec 11th 2009 ...
Hardware Building Blocks and Encoding
... the header, two types of information are included: MIME type and subtype. The MIME type describes the general file type of the transmitted content type such as image, text, audio, application, and others. The subtype carries the specific file type such as jpeg or gif, tiff, and so on. S/MIME w ...
... the header, two types of information are included: MIME type and subtype. The MIME type describes the general file type of the transmitted content type such as image, text, audio, application, and others. The subtype carries the specific file type such as jpeg or gif, tiff, and so on. S/MIME w ...
Lecture 13
... key” function have one, but significant disadvantage: it is necessary to distribute a key among all users and all of them must take care of keeping the key unavailable to others. • The alternative is an “open key” encryption, which became very popular during last 15-20 years. In this method, which i ...
... key” function have one, but significant disadvantage: it is necessary to distribute a key among all users and all of them must take care of keeping the key unavailable to others. • The alternative is an “open key” encryption, which became very popular during last 15-20 years. In this method, which i ...
Competency: Defend and Attack (virus, spam, spyware - FBLA-PBL
... 7. Identify and analyze environmental hazards (e.g., fire, flood, moisture, temperature, electricity,) and establish environmental security controls to protect and restore. 8. Perform a physical configuration audit. 9. Train and test employees in area of physical security awareness. 10. Describe the ...
... 7. Identify and analyze environmental hazards (e.g., fire, flood, moisture, temperature, electricity,) and establish environmental security controls to protect and restore. 8. Perform a physical configuration audit. 9. Train and test employees in area of physical security awareness. 10. Describe the ...
Untersuchungen zur MAC Address Translation (MAT)
... In the datapath the packet classification is done by finding classification rules for incoming frames with the help of the hash functions The evolution module changes the hash function depending on the existing key to increase lookup performance ...
... In the datapath the packet classification is done by finding classification rules for incoming frames with the help of the hash functions The evolution module changes the hash function depending on the existing key to increase lookup performance ...
Introduction - Computer Science
... – A service provided by a protocol layer of communicating open systems, which ensures adequate security of the systems or of data transfers ...
... – A service provided by a protocol layer of communicating open systems, which ensures adequate security of the systems or of data transfers ...
RSA - people.vcu.edu - Virginia Commonwealth University
... Myth: More Secure than conventional encryption Reality: Security of any encryption depends on key length and computational effort required in breaking a cipher Myth: General purpose technique that has made conventional encryption obsolete Reality: Public-key cryptography has lot of computational ove ...
... Myth: More Secure than conventional encryption Reality: Security of any encryption depends on key length and computational effort required in breaking a cipher Myth: General purpose technique that has made conventional encryption obsolete Reality: Public-key cryptography has lot of computational ove ...
Principles of Public Key Cryptography Applications of
... a.) by choosing e at random and test if it is relatively prime to (p - 1) · (q - 1) b.) by choosing e first and then determine matching p and q → RSA is not less secure if always the same e is chosen → If e is small or its binary representation has few '1's, the operations for encryption and signatu ...
... a.) by choosing e at random and test if it is relatively prime to (p - 1) · (q - 1) b.) by choosing e first and then determine matching p and q → RSA is not less secure if always the same e is chosen → If e is small or its binary representation has few '1's, the operations for encryption and signatu ...
VI-I Computing Euler`s function
... The problem is that given an RSA modulus n and a random z C Zn and for finding r>1 and y C Zn such that y^r = z and the choice of r may be restricted in some cases that allows to occur the flexible RSA problem, so the strong RSA assumption is the assumption that this problem is hard to solve. The r ...
... The problem is that given an RSA modulus n and a random z C Zn and for finding r>1 and y C Zn such that y^r = z and the choice of r may be restricted in some cases that allows to occur the flexible RSA problem, so the strong RSA assumption is the assumption that this problem is hard to solve. The r ...
Power point
... Redirection Attack • Suppose we can guess destination IP in encrypted packet • Flip bits to change IP to Evil 2, send it to AP – Tricks to adjust IP checksum (in paper) ...
... Redirection Attack • Suppose we can guess destination IP in encrypted packet • Flip bits to change IP to Evil 2, send it to AP – Tricks to adjust IP checksum (in paper) ...
IPSec
... Update OS network stack Adding software that’s binds to network stack can cause software conflicts ...
... Update OS network stack Adding software that’s binds to network stack can cause software conflicts ...
VPN in the spotlight of IT- Security
... The more challenging threat of data exchange is an active attacker. Such an attacker has the ability to intrude into the communication channel. So the packets between both parties could be modified, deleted or replaced. In this case the whole data stream is corrupted and the destination gateway is g ...
... The more challenging threat of data exchange is an active attacker. Such an attacker has the ability to intrude into the communication channel. So the packets between both parties could be modified, deleted or replaced. In this case the whole data stream is corrupted and the destination gateway is g ...
Chapter 1. Introduction to Data Communications
... User Profiles and Forms of Access • The limits of what users have access to on a network are determined by user profiles assigned to each user account by the net manager. • The profile specifies access details such as what data and network resources a user can access and the type of access (e.g., r ...
... User Profiles and Forms of Access • The limits of what users have access to on a network are determined by user profiles assigned to each user account by the net manager. • The profile specifies access details such as what data and network resources a user can access and the type of access (e.g., r ...
PK b
... assuming the PEKS is semantically secure against an adaptive chosen message attack.(once can send a bit?) Building non-interactive public-key searchable encryption is at least as hard as building an IBE system. ...
... assuming the PEKS is semantically secure against an adaptive chosen message attack.(once can send a bit?) Building non-interactive public-key searchable encryption is at least as hard as building an IBE system. ...
Cryptography

Cryptography or cryptology; from Greek κρυπτός kryptós, ""hidden, secret""; and γράφειν graphein, ""writing"", or -λογία -logia, ""study"", respectively is the practice and study of techniques for secure communication in the presence of third parties (called adversaries). More generally, it is about constructing and analyzing protocols that block adversaries; various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, and electrical engineering. Applications of cryptography include ATM cards, computer passwords, and electronic commerce.Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense. The originator of an encrypted message shared the decoding technique needed to recover the original information only with intended recipients, thereby precluding unwanted persons from doing the same. Since World War I and the advent of the computer, the methods used to carry out cryptology have become increasingly complex and its application more widespread.Modern cryptography is heavily based on mathematical theory and computer science practice; cryptographic algorithms are designed around computational hardness assumptions, making such algorithms hard to break in practice by any adversary. It is theoretically possible to break such a system, but it is infeasible to do so by any known practical means. These schemes are therefore termed computationally secure; theoretical advances, e.g., improvements in integer factorization algorithms, and faster computing technology require these solutions to be continually adapted. There exist information-theoretically secure schemes that provably cannot be broken even with unlimited computing power—an example is the one-time pad—but these schemes are more difficult to implement than the best theoretically breakable but computationally secure mechanisms.The growth of cryptographic technology has raised a number of legal issues in the information age. Cryptography's potential for use as a tool for espionage and sedition has led many governments to classify it as a weapon and to limit or even prohibit its use and export. In some jurisdictions where the use of cryptography is legal, laws permit investigators to compel the disclosure of encryption keys for documents relevant to an investigation. Cryptography also plays a major role in digital rights management and piracy of digital media.