Lecture 10
... Public – Key Cryptosystems Current implementations of public-key cryptosystems works slow Public-key methods are mostly use for key exchange or key agreement protocols p and q should be at least 155 decimal digits each ...
... Public – Key Cryptosystems Current implementations of public-key cryptosystems works slow Public-key methods are mostly use for key exchange or key agreement protocols p and q should be at least 155 decimal digits each ...
Rivest-Shamir
... Cryptographic workhorse; secrecy Key exchange, authentication and integrity of datasingle characters to blocks of data, messages, files ...
... Cryptographic workhorse; secrecy Key exchange, authentication and integrity of datasingle characters to blocks of data, messages, files ...
WHAT IS EC SECURITY? - Joseph H. Schuessler, PhD
... The process of scrambling (encrypting) a message in such a way that it is difficult, expensive, or time-consuming for an unauthorized person to unscramble (decrypt) it plaintext An unencrypted message in human-readable form ciphertext A plaintext message after it has been encrypted into a machin ...
... The process of scrambling (encrypting) a message in such a way that it is difficult, expensive, or time-consuming for an unauthorized person to unscramble (decrypt) it plaintext An unencrypted message in human-readable form ciphertext A plaintext message after it has been encrypted into a machin ...
PowerPoint-10b - Community College of Rhode Island
... – Ensure only authorized parties can view it ...
... – Ensure only authorized parties can view it ...
Slides
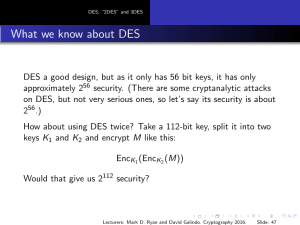
... attacks, and has proved very resilient. So far, there are only very small “erosions” of AES: There is a meet-in-the-middle key recovery attack for AES-128. It requires 2126 operations, so it is only about four times faster than brute-force. There is a “related key” attack on AES-192 and AES-256. Thi ...
... attacks, and has proved very resilient. So far, there are only very small “erosions” of AES: There is a meet-in-the-middle key recovery attack for AES-128. It requires 2126 operations, so it is only about four times faster than brute-force. There is a “related key” attack on AES-192 and AES-256. Thi ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... A Review Paper ON Cryptography Based Secured Advanced ON Demand Routing Protocol … 4. Authentication: The process of verifying that users are who they assert to be when logging onto a system.(the sender and receiver can confirm each others identity and the origin /destination of the information). 5 ...
... A Review Paper ON Cryptography Based Secured Advanced ON Demand Routing Protocol … 4. Authentication: The process of verifying that users are who they assert to be when logging onto a system.(the sender and receiver can confirm each others identity and the origin /destination of the information). 5 ...
Final bits of OS - Department of Computer Science
... • Result: a transport allowing hosts to send IP event notification messages to syslog servers – provides a very general message format – allowing processes and applications to use suitable conventions for ...
... • Result: a transport allowing hosts to send IP event notification messages to syslog servers – provides a very general message format – allowing processes and applications to use suitable conventions for ...
Secure Email
... – The two basic features of Email security are privacy (only the intended recipient can read the message) and authentication (the recipient can be assured of the identity of the sender). The technical capabilities for these functions has been known for many years, but they have only been applied to ...
... – The two basic features of Email security are privacy (only the intended recipient can read the message) and authentication (the recipient can be assured of the identity of the sender). The technical capabilities for these functions has been known for many years, but they have only been applied to ...
ECSP – EC-Council Certified Secure Programmer
... File Input and Output Serialization Input Validation Error Handling and Logging Authorization and Authentication JAAS - Java Authentication and Authorization Service Java Concurrency and Managing Sessions Cryptography and Java Vulnerabilities in Java Applications ...
... File Input and Output Serialization Input Validation Error Handling and Logging Authorization and Authentication JAAS - Java Authentication and Authorization Service Java Concurrency and Managing Sessions Cryptography and Java Vulnerabilities in Java Applications ...
CHAPTER FIVE
... The notion of one- way function is central to public key cryptography .One way function are easy to compute , but it is significantly hard (computationally) to reverse. That is given x , it is easy to compute f(x) , but given f(x), it is hard to compute x .Breaking plate is a good example of a one-w ...
... The notion of one- way function is central to public key cryptography .One way function are easy to compute , but it is significantly hard (computationally) to reverse. That is given x , it is easy to compute f(x) , but given f(x), it is hard to compute x .Breaking plate is a good example of a one-w ...
Lecture on Security
... Some sort of overhaul is required – So what can we do to avoid shared secret? ...
... Some sort of overhaul is required – So what can we do to avoid shared secret? ...
Practice Questions with Solutions
... employee leaked several sensitive documents to the news media. To prevent this, the organization should have: a. Reviewed access logs b. Restricted the employee’s access to sensitive information c. Obtained a signed non-disclosure statement d. Performed a background verification prior to hiring the ...
... employee leaked several sensitive documents to the news media. To prevent this, the organization should have: a. Reviewed access logs b. Restricted the employee’s access to sensitive information c. Obtained a signed non-disclosure statement d. Performed a background verification prior to hiring the ...
VPNs, PKIs, ISSs, SSLs with narration
... • A PKI automates most aspects of using public key encryption and authentication • Uses a PKI Server ...
... • A PKI automates most aspects of using public key encryption and authentication • Uses a PKI Server ...
Still Image Compression
... She chooses a number e such that e is relatively prime to (n) and computes d, the inverse of e in Z (n ) (i.e., ed =1 mod \phi(n)) She publicizes the pair (e,n) as her public key.(e is called RSA exponent, n is called RSA modulus)She keeps d secret and destroys p, q, and (n) Plaintext and ciph ...
... She chooses a number e such that e is relatively prime to (n) and computes d, the inverse of e in Z (n ) (i.e., ed =1 mod \phi(n)) She publicizes the pair (e,n) as her public key.(e is called RSA exponent, n is called RSA modulus)She keeps d secret and destroys p, q, and (n) Plaintext and ciph ...
Lecture1
... that use trivially related, often identical, cryptographic keys for both decryption and encryption. 0 The encryption key is trivially related to the decryption key, in that ...
... that use trivially related, often identical, cryptographic keys for both decryption and encryption. 0 The encryption key is trivially related to the decryption key, in that ...
Securing Distribution Automation
... local authentication solution is still required. To fulfill this requirement, some vendors provide an innovative mechanism where a remote access server grants the user a limited duration “security ticket” that can be used to access a field device. However, to manage revocation within 24 hours, the s ...
... local authentication solution is still required. To fulfill this requirement, some vendors provide an innovative mechanism where a remote access server grants the user a limited duration “security ticket” that can be used to access a field device. However, to manage revocation within 24 hours, the s ...
Net+ Chapter 1
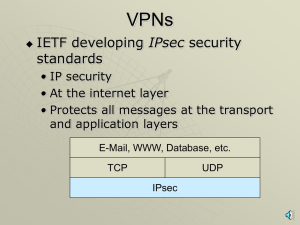
... Internet Protocol Security (IPSec) • IPSec is an IETF standard designed to provide secure communications across both public and private networks. • IPSec can deter several types of threats, including denial-of-service, identity spoofing, and packet sniffing. ...
... Internet Protocol Security (IPSec) • IPSec is an IETF standard designed to provide secure communications across both public and private networks. • IPSec can deter several types of threats, including denial-of-service, identity spoofing, and packet sniffing. ...
Here - IJPAM
... From a defense perspective, nowadays encryption algorithms are being replaced with open, standards-based algorithms that are less cumbersome to manage in terms of physical controls. We need more advanced encryption techniques so that out data and security are guarded. This paper concentrates on encr ...
... From a defense perspective, nowadays encryption algorithms are being replaced with open, standards-based algorithms that are less cumbersome to manage in terms of physical controls. We need more advanced encryption techniques so that out data and security are guarded. This paper concentrates on encr ...
System Security - Wright State engineering
... Let us assume that Mallory, a cracker, not only can listen to the traffic between Alice and Bob, but also can modify, delete, and substitute Alice's and Bob's messages, as well as introduce new ones. Mallory can impersonate Alice when talking to Bob and impersonate Bob when talking to Alice. Here is ...
... Let us assume that Mallory, a cracker, not only can listen to the traffic between Alice and Bob, but also can modify, delete, and substitute Alice's and Bob's messages, as well as introduce new ones. Mallory can impersonate Alice when talking to Bob and impersonate Bob when talking to Alice. Here is ...
lesson-4modular-arithmetric1
... the two communicating parties to have a secure prior agreement on the keys to be used in the cipher. This means that the two parties must trust each other in the handling of the keys, and keep the keys private, i.e., private key cryptography, as the decryption keys can be easily obtained from the en ...
... the two communicating parties to have a secure prior agreement on the keys to be used in the cipher. This means that the two parties must trust each other in the handling of the keys, and keep the keys private, i.e., private key cryptography, as the decryption keys can be easily obtained from the en ...
Slide 1
... Instead, IPSec provides a set of security algorithms plus a general framework that allows a pair of communicating entities to use whichever algorithms provide security appropriate for the communication. ...
... Instead, IPSec provides a set of security algorithms plus a general framework that allows a pair of communicating entities to use whichever algorithms provide security appropriate for the communication. ...
answer-sheet-7540-040-7630-345-b_
... Motion detector: Just like CCTV you could use motion detection, this is there to detect movement in a room and can be used the same as CCTV meaning in after a certain time if motion is detected it will set of an alarm notifying surrounding people and the owner and police. This protects ICT systems f ...
... Motion detector: Just like CCTV you could use motion detection, this is there to detect movement in a room and can be used the same as CCTV meaning in after a certain time if motion is detected it will set of an alarm notifying surrounding people and the owner and police. This protects ICT systems f ...
Course Name : INFORMATION SECURITY
... Mention the essential characteristics of information security. How are they used in the study of computer security? Briefly explain the components of an information system and their security. How will you balance security and access? ...
... Mention the essential characteristics of information security. How are they used in the study of computer security? Briefly explain the components of an information system and their security. How will you balance security and access? ...
Cryptography

Cryptography or cryptology; from Greek κρυπτός kryptós, ""hidden, secret""; and γράφειν graphein, ""writing"", or -λογία -logia, ""study"", respectively is the practice and study of techniques for secure communication in the presence of third parties (called adversaries). More generally, it is about constructing and analyzing protocols that block adversaries; various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, and electrical engineering. Applications of cryptography include ATM cards, computer passwords, and electronic commerce.Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense. The originator of an encrypted message shared the decoding technique needed to recover the original information only with intended recipients, thereby precluding unwanted persons from doing the same. Since World War I and the advent of the computer, the methods used to carry out cryptology have become increasingly complex and its application more widespread.Modern cryptography is heavily based on mathematical theory and computer science practice; cryptographic algorithms are designed around computational hardness assumptions, making such algorithms hard to break in practice by any adversary. It is theoretically possible to break such a system, but it is infeasible to do so by any known practical means. These schemes are therefore termed computationally secure; theoretical advances, e.g., improvements in integer factorization algorithms, and faster computing technology require these solutions to be continually adapted. There exist information-theoretically secure schemes that provably cannot be broken even with unlimited computing power—an example is the one-time pad—but these schemes are more difficult to implement than the best theoretically breakable but computationally secure mechanisms.The growth of cryptographic technology has raised a number of legal issues in the information age. Cryptography's potential for use as a tool for espionage and sedition has led many governments to classify it as a weapon and to limit or even prohibit its use and export. In some jurisdictions where the use of cryptography is legal, laws permit investigators to compel the disclosure of encryption keys for documents relevant to an investigation. Cryptography also plays a major role in digital rights management and piracy of digital media.